Blogs




India has been leveraging technology to drive its economic transformation, enhancing its capacity to outpace other major economies in growth. The integration of technology has positively influenced society, contributing to reductions in emissions and transforming capital markets by introducing new opportunities.
With the proliferation of the internet, mobile devices, and social media, technology has become deeply embedded in our daily lives. While it has undeniably delivered numerous benefits, it has also significantly impacted Indian culture, particularly through the emergence of a new generation of digital natives. Sectors such as banking, financial services, and insurance (BFSI), healthcare, pharmaceuticals, e-commerce, retail, and manufacturing are increasingly adopting advanced technologies.
Technologies such as Industry 4.0, digital supply chains, and digital assistance are expected to drive economic development by 2025. Organisations within these sectors are taking on transformative journeys, with forward-thinking entities capitalising on the extensive capabilities of emerging technologies to gain competitive advantages. Let us understand how technology has changed the world in depth today:
The term “SMART” stands for “self-monitoring, analysis, and reporting technology.” This technology integrates artificial intelligence, machine learning, and big data analysis to give cognitive awareness to objects that were once considered inanimate.
These devices form a network that uses sensors, chips, software, online connectivity, and analytics to bring physical objects to life. IoT devices are futuristic, scalable, and automated, providing significant value. Examples include smart cities, smart homes, and smart factories.
Connected via the internet or Bluetooth and controlled remotely, smart connected devices offer a customised experience but require manual handling. Examples include smart security cameras, smart bulbs, and smartphones.
These devices offer limited automation and don’t require internet connectivity. They are programmable to provide specific services, such as smart coffee makers that deliver personalised services at designated times.
This technology allows for multitasking with minimal effort, often through simple voice commands. Whether adjusting lighting, securing your home, or ordering food, it brings a new level of convenience. The latest SMART technologies can analyse your preferences to offer automated, personalised services and consider external factors like traffic to guide you safely.
SMART technology aids in energy conservation, helping both industrial and domestic sectors reduce energy waste. By automating the control of appliances like lights and heating systems, it conserves energy and saves money, contributing to a more sustainable future.
Offering more reliable protection than traditional security systems, this technology includes gadgets like door sensors, alarm systems, and security cameras. These devices alert property owners and law enforcement to potential threats, while also enabling real-time preventive actions, such as locking doors or detecting hazards like smoke or gas leaks.
SMART technology uses data to optimise processes and systems, making them more efficient. By tracking and analysing activities, it enhances productivity, helping you start your day smoothly with everything ready and distractions minimised.
Devices like smart thermostats, lighting, and appliances optimise energy usage, leading to lower energy bills. Additionally, by automating repetitive tasks, SMART technology saves time, reducing lost or wasted efforts.
As emerging technologies reshape global industries, nations have adopted varying approaches to govern these innovations, reflecting diverse priorities and philosophies. In Europe, the precautionary principle leads to anticipatory regulation, where risks are addressed even before technologies are fully developed. For instance, the European Union's General Data Protection Regulation (GDPR) places strict responsibilities on data controllers and processors, ensuring individuals have access to their data and understand its usage. This regulation not only tackles current security and privacy threats but also prepares for future challenges, such as the implications of artificial intelligence and automated decision-making.
International and nongovernmental organisations like the International Organisation for Standardisation (ISO) and the International Telecommunication Union (ITU) also play crucial roles in setting standards and norms for new technologies. These organisations help define the appropriate boundaries for government use of technologies, particularly when such technologies could be used as tools of state control.
In India, the approach to technology governance is evolving rapidly, influenced by both global trends and unique national considerations. The Indian government has taken steps to regulate data privacy through the Personal Data Protection Bill, which aims to establish a legal framework for data protection similar to the GDPR. However, the bill is still under development, and the debate around balancing innovation with privacy and security continues. The interplay between politics, privacy, and engineering in India, as in the rest of the world, underscores the importance of thoughtful governance and responsible design in shaping the future of technology.
Corporate giants and big tech companies significantly influence the development and impact of technological innovations. Often, these firms are either unprepared or unwilling to tackle the social problems their technologies may worsen. Governments face challenges in regulating this fast-paced sector due to the complexity of setting standards, enforcing rules, and managing the vast resources and influence of tech companies.
The immense power of tech companies is a growing concern. These entities often surpass governments in their ability to affect millions of people globally, controlling information access and platform usage. Their vast scale complicates efforts to identify and address potential regulatory violations, particularly since many offer free services, making antitrust issues challenging to pinpoint.
As tech firms operate internationally, they can implement global changes that individual states struggle to manage. The emergence of private-public partnerships in sectors like energy and cybersecurity blurs the lines between public and private responsibilities, raising critical questions about governance and regulatory influence.
In the 21st century, technology has become a fundamental aspect of daily life, fundamentally altering the ways in which we live, work, and engage with the world. The accelerated pace of technological advancement has ushered in a digital revolution that affects every dimension of society. Its transformative influence is evident in diverse sectors such as communication, healthcare, business, and education. Let us explore some of the best ways in which technology is changing the world:
Technology has revolutionised global connectivity, creating an interconnected world through the internet and advanced telecommunications. Social media platforms, instant messaging, and video conferencing tools enable seamless communication across the globe, enhancing personal interactions and fostering international collaboration in various fields.
Businesses are undergoing a digital transformation driven by the best technology existing in this world. Automation, artificial intelligence, and data analytics are streamlining operations, increasing efficiency, and offering competitive advantages. E-commerce and digital marketing have redefined retail and consumer engagement, signalling a shift from traditional business models to innovative, technology-driven approaches.
Technology is transforming healthcare by improving diagnosis, treatment, and patient care. Telemedicine provides access to healthcare in remote areas, while wearable devices and health apps empower individuals to monitor their health. Artificial intelligence aids in diagnostics, predicting disease outcomes, and advancing drug discovery, driving improvements in patient care and medical research.
The education sector is being transformed by the best technology through online learning platforms, interactive apps, and virtual classrooms. Virtual and augmented reality enhance learning experiences with immersive simulations. Technology breaks down geographic barriers, providing global access to quality educational resources and fostering lifelong learning.
Smart cities are emerging as we are integrating the best technology with urban planning to create efficient and sustainable environments. IoT devices optimise traffic flow, manage energy use, and enhance public safety. Smart infrastructure, including connected transportation and energy-efficient buildings, improves urban living conditions and supports environmental sustainability.
Technology plays a crucial role in environmental conservation by advancing renewable energy, energy efficiency, and waste reduction. Monitoring systems and data analytics track and address issues like deforestation, climate change, and pollution, contributing to a more sustainable and eco-friendly future.
Artificial intelligence and automation are reshaping industries by enhancing human capabilities and optimising processes. Machine learning enables predictive analytics and data-driven decision-making, while automation improves efficiency in manufacturing, logistics, and supply chain management. These advancements offer new opportunities for innovation and collaboration between humans and AI.
India's integration of technology has been a transformative force, driving economic growth, societal change, and industrial innovation. As the nation continues to embrace advancements like Industry 4.0 and smart technologies, it is poised to enhance its global standing and sustain its post-COVID recovery. However, the journey ahead requires balancing technological progress with thoughtful governance to address privacy and regulatory challenges. The role of corporate giants and big tech in shaping technological impact underscores the need for thoughtful governance and clear policies to address the complex interplay between technology, politics, and privacy. India's future success will depend on its ability to harness these technologies responsibly, ensuring that the benefits of innovation are widely shared while mitigating potential risks.
Engineering and education intersect in fascinating ways, offering numerous opportunities in academia. Here’s an overview of how these fields interact and the potential avenues for exploration:
Exploring these opportunities with JAIN Faculty of Engineering and Technology can lead to a rewarding career that not only advances the field of engineering but also enhances the quality and accessibility of education.
We recognise this decade as one of development and innovation, with engineers leading the charge in driving innovative progress. Engineers are regarded as the brains behind developments happening across the globe. An engineering degree is seen as a valuable investment that can open numerous career paths. Unlike other educational backgrounds that might limit individuals to a single profession, an engineering degree offers opportunities in various fields, including music, sports, conservation, and construction. Engineers are not confined to traditional roles; they are sought after in a wide range of industries, allowing them to apply their skills in areas that match their personal interests. Here are some unconventional jobs for engineers, unique jobs after engineering, software engineer jobs, and job options for engineers after Bachelor of Technology (BTech) or Master of Technology (MTech):
Data science is considered an unconventional field for engineers because traditional engineering disciplines (such as civil, mechanical, electrical, or electronics engineering) are generally focused on tangible products, systems, and infrastructure. In contrast, data science is more abstract, focusing on extracting meaningful insights from large datasets using statistical methods, machine learning, and computational techniques. Data science skills are in high demand across various industries, including finance, healthcare, technology, manufacturing, and retail. Companies are increasingly relying on data to make informed decisions, optimise operations, and innovate products and services. Engineers transitioning into data science can explore various roles such as Data Scientist, Data Analyst, Machine Learning Engineer, Artificial Intelligence (AI) Specialist, and Business Intelligence Analyst. Engineers can also pursue software engineer jobs that involve designing, developing, testing, and maintaining software applications and systems.
Digital marketing is essential for businesses across all sectors, from small startups to large corporations. With the rise of online platforms, companies are investing heavily in digital marketing to reach and engage their target audiences. Digital marketing offers a wide range of roles, including Digital Marketing Manager, SEO Specialist, Content Strategist, Social Media Manager, PPC Specialist, and Email Marketing Specialist. Each role focuses on different aspects of online marketing, such as search engine optimisation (SEO), content creation, social media management, and paid advertising. To transition into digital marketing, engineers need to acquire new skills in areas like content creation, social media management, SEO, and digital advertising. Online courses, certifications (such as Google Analytics, Google Ads, and HubSpot), and hands-on experience through internships or freelance work can help engineers build the necessary expertise. For engineers considering jobs after engineering, digital marketing presents a promising option that leverages their analytical skills and technical background.
With the increasing importance of user experience in digital products, the demand for UX (User Experience)/User Interface (UI) designers is on the rise. Companies across industries—from tech startups to large enterprises—are prioritising user-centred design to enhance product usability, customer satisfaction, and brand loyalty. UX/UI design offers a variety of career paths, including roles such as UX Designer, UI Designer, Interaction Designer, UX Researcher, and Product Designer. These roles involve different aspects of the design process, from researching user needs to creating visually appealing and functional interfaces. Engineers bring forth strong problem-solving abilities, analytical thinking, and technical knowledge to the table. These skills are valuable in UX/UI design, where understanding user problems and creating functional solutions are essential. Engineers should become proficient in design tools like Adobe XD, Sketch, Figma, and InVision. Familiarity with front-end development (HTML, CSS, JavaScript) can also be advantageous. Jobs for engineers in UX/UI design are growing as more companies recognise the value of their engineering skill set in creating user-focused designs.
Engineers can pursue a career in technical writing as they possess a deep understanding of complex technical concepts, strong analytical skills, and the ability to communicate clearly. Technical writing involves creating documents such as user manuals, product specifications, white papers, and technical reports, which require a solid grasp of the subject matter and the ability to explain it in a way that is understandable to the intended audience. The demand for technical writers is high in technology-driven industries such as software development, telecommunications, manufacturing, and engineering. Engineers can find opportunities in various roles within technical writing, including creating user manuals, software documentation, API documentation, technical reports, and instructional materials. There are also specialised roles, such as medical writers, scientific writers, and proposal writers, where engineers can apply their specific knowledge. Considering jobs for engineers in technical writing, engineers can leverage their expertise to excel in this field.
Marketing automation is becoming a hot topic these days as companies seek to streamline their marketing efforts, improve customer engagement, and boost ROI. The demand for professionals skilled in marketing automation is growing across industries, including e-commerce, technology, finance, and healthcare. The field of marketing automation offers various roles, such as Marketing Automation Specialist, CRM (Customer Relationship Management) Manager, Email Marketing Manager, and Marketing Operations Manager. Engineers with a deep understanding of data analytics, programming, and software integration can bring a unique perspective to marketing automation, making them valuable assets to companies looking to enhance their marketing strategies. Marketing automation offers engineers the opportunity to diversify their career by combining technical skills with marketing knowledge. This dual expertise can open doors to job options for engineers in marketing automation, data-driven marketing, and strategic planning.
Investment banking requires a strong understanding of financial modelling, valuation, and market analysis, all of which can be approached with the methodical and structured mindset typical of engineers. The skills developed in engineering—such as analytical thinking, problem-solving, and quantitative analysis—are highly transferable to investment banking. Engineers in investment banking can explore various roles, including M&A advisory, equity research, debt financing, and trading. They can also work in specialised areas such as infrastructure finance, energy banking, or technology banking, where their engineering background is particularly valuable. Engineers need to build a solid foundation in finance, which can be achieved through formal education, such as a Master’s in Business Administration (MBA) with a focus on finance, or through self-study and certifications like the Chartered Financial Analyst (CFA) designation. For those considering jobs after engineering, investment banking represents a lucrative and challenging career path.
Entrepreneurship can be an excellent, albeit unconventional, career path for engineers, particularly those with a passion for innovation and a desire to bring their ideas to life. Engineers possess essential skills like problem-solving, critical thinking, and attention to detail, which are crucial for overcoming the challenges of starting and managing a business. While the path of entrepreneurship involves risks such as financial uncertainty and a steep learning curve, it offers the potential for immense rewards, including the freedom to be one's own boss and the opportunity to pursue personal passions. By attending networking events, seeking mentorship from successful entrepreneurs, and embracing the challenges ahead, engineers can successfully transition into entrepreneurship, making it a fulfilling and profitable career choice. Job options for engineers in entrepreneurship include launching startups or consulting, where they can apply their technical expertise to innovate and create new ventures.
As industries develop, the demand for engineers continues to grow, not only in traditional sectors but also in emerging areas where their skills are increasingly valued. From software engineer jobs that involve designing cutting-edge software to automating marketing processes, engineers have the opportunity to apply their problem-solving abilities and technical knowledge in varied ways. Their ability to adapt, innovate, and apply their expertise across diverse industries underscores the value of an engineering degree. From traditional job options for engineers to emerging fields like data science, digital marketing, and investment banking, engineers have the flexibility to forge their own paths and make significant contributions to society. Whether it's developing innovative solutions, leading projects, or launching new ventures, engineers are well-equipped to thrive in a variety of roles, making their contributions essential to the continued progress of society.
Engineering as a course has been present for decades. In India, having this degree is a matter of prestige and accomplishment. But, as technology evolves constantly, engineering degrees have also grown their branches across different types of engineering to adapt and grow in academics and industry.
Being an in-demand job with attractive salary packages and the versatile nature of professions after this course, one wonders how does all types of engineering offer exceptional courses that meet today’s industry expectations. We take you as a guide to show how various types of engineering degrees have evolved to suit students' interests today.
Engineering means building, creating, or designing instruments, buildings, and systems that make lives convenient. This course has been since ancient times and has become popular in the recent ages. Until recently, there were five different types of engineering.
As the name implies, mechanical engineering is a branch that deals with mechanical systems and sets devices in motion. It involves principles of mathematics and physics to transform parts of an object into ships, firearms, appliances, turbines, vehicles, and more. Core components from years remain the same, but their functionalities change over time with this branch of engineering.
Considered one of the most prominent and oldest disciplines, civil engineering works closely with constructing, designing, and maintaining public structures such as bridges, tunnels, and water supply lines. Engineers from this course are involved in urban planning, transportation, and building projects.
In a broad sense, chemical engineering deals with chemicals and manipulating their properties to design and manufacture materials and products. Engineers in this course work closely with chemistry and biology. Their industry collaborators include microbiology, food, pharmaceuticals, fuels, and more. They innovate processes that use and transform energy.
Industrial engineering comes close to helping businesses reduce costs, managing inventories, overseeing personnel assignments, increase efficiency, and workplace safety. Graduates from this stream of engineering are often within the entertainment, service, and healthcare sectors.
With the invention of electricity, electrical engineering branched out and has been introduced in the 19th century. It focuses on electrical equipment and electronics. They design, test, and maintain electrical devices and gadgets. The field of work of these electrical engineers includes maintaining microchips, satellites, power station generators, and more. Industries that work with high-volume electricity include electrical engineers.
With time, all types of engineering have evolved with the growth in technology. As a field that uses math, natural science, and design, it helps in processes that solve technical issues and increase efficiency and productivity.
This branching out has led to the creation of diverse engineering degrees today. Let us explore the most recent types of engineering degrees, with each that focus on different aspects of technology and business.
As the name suggests, this degree focuses on computer science and entails designing and developing software and hardware. This course includes subcategories such as programming, algorithms, computer architecture, and more. An individual with this specialization can enter the workforce as a data scientist, system analyst, software architect, database and network administrator, and more.
The communication industry is growing. With it, the demand for engineers who work with devices that streamline communication is growing rapidly. And introduction of 5G networks by mobile network companies, and electronics and communication engineers’ role has become critical in the industry. Engineers, in this course work with smart grids, infrastructure of electric vehicles, and more. Job roles one can explore are electrical design engineer, power plant engineer, control system engineer, and more.
There is new information every day on the internet and within companies. With a degree in information technology and engineering, an individual will work with web technologies, data management systems, algorithms, coding, and more. The IT industry is their target market. As the demand for an IT engineer never decreases, this course is a best fit if your career goals are similar to web developers, database administrators, IT consultants, software developers, and more.
Healthcare cannot function alone by its industry. Collaboration with the engineering industry enables healthcare work with efficiency and increases productivity. With a biomedical engineering degree, one can work by designing medical tools, diagnostic equipment, prosthetics, and more. Since COVID-19 surged, this industry and career have gained significant traction.
In the era of artificial intelligence, industries are adapting to the new technology. By acquiring a degree in robotics and automation engineering, a student can drive the integration of robots and automation across diverse industries such as agriculture, healthcare, manufacturing, and more. Job roles to explore with this specialization include control system engineer, embedded systems engineer, robot programmer, tester, and more.
Taking flight and reaching new goals is the new normal. In aerospace engineering, cutting-edge aircraft, space crafts, and satellites are created for defense and public use. As one of the up-and-coming industries and a branch of engineering, research is encouraged and experimentation is supported for advancement in technology. Some popular job positions an engineer can pursue with this degree include aerodynamics engineer, flight tester, stress engineer, and more.
Choosing an engineering specialization can be challenging for a student. We have a few tips that can help you making your decision among these top choices.
JAIN (Deemed-to-be University) - Faculty of Engineering and Technology comes with various specializations that you require in the market. With experienced faculty and a university that believes in the overall development of the student, JU-FET can be your perfect companion for future endeavors.
School of Engineering and Technology at JAIN (Deemed-to-be University) places strong emphasis on practical, peer and research learning that prepares students for industry-standard projects. High-quality and state-of-the-art labs and classrooms help us impart an education that moves along with the student.
To ensure students get placed in top companies and industries, our collaboration with major companies helps us attract internships and company placements.
Why wait longer? Begin your journey by choosing a stream that takes you above and beyond. Choose JAIN (Deemed-to-be University) as your helping hand towards reaching your career goals. Enter the industry with exciting opportunities and contribute to innovations that matter.
Selecting the right engineering college is one of the most important decisions that can influence your career trajectory. With numerous institutions offering diverse programs, finding the best fit for your goals involves careful consideration of several factors. Here’s a comprehensive guide to help you navigate this important choice and simplify your process:
Before diving into college options, take some time to clarify your career objectives. No matter if you are interested in mechanical, civil or computer engineering, it is necessary for a student to identify their career goals and make informed decisions.
Engineering is a broad field with many specializations so it is necessary to look for colleges that offer strong programs in your area of interest. Research the curriculum to see if it aligns with your career goal and if it includes practical experience through internships, labs, and projects.
The quality of faculty can greatly impact your engineering career. Review the qualifications and research interests of the professors in your field of interest. Faculty with significant industry experience or research credentials can provide valuable insights and connections that enhance your learning experience.
For those interested in research, select colleges with robust research programs and facilities. Investigate the ongoing research projects and the potential for undergraduate involvementResearch experience can be crucial for careers in academia or specialized industry roles.
Modern engineering programs often require state-of-the-art labs, equipment, and software. Ensure the colleges you’re considering have up-to-date facilities that support hands-on learning and experimentation. Good facilities can make a significant difference in your educational experience.
A college with strong industry connections can facilitate internships and job placements. Research the college’s placement record and its relationships with industry partners. Colleges with robust career services and strong ties to the industry can help bridge the gap between education and employment.
The college’s location can impact your overall experience. Consider whether you prefer an urban or rural setting and think about how the location might affect your internship opportunities and lifestyle. Campus life, including extracurricular activities and support services, also plays a role in your overall college experience.
Tuition costs and availability of financial aid are critical factors. Compare the costs of different colleges and explore scholarships, grants, and other funding opportunities. Consider not just the immediate costs but also the potential return on investment based on the college’s reputation and employment outcomes.
Talk to current students and alumni to gain insights into the culture and academic environment of engineering college. They can provide firsthand accounts of their experiences, helping you understand what to expect and how well the program aligns with your goals.
This will give you a sense of the environment, facilities, and campus culture. You can also meet with faculty and students, attend classes, and explore the surrounding area to see if it feels like the right fit.
Choosing the right engineering college involves evaluating how well each institution aligns with your engineering career, academic interests, and personal preferences.
By thoroughly researching programs, faculty, facilities, and financial aspects, you can choose JAIN Faculty of Engineering and Technology to make an informed decision that sets the foundation for a successful engineering career. Remember, this choice is a significant step, but with careful consideration, you can find a college that will help you achieve your professional aspirations and personal growth.
Innovation and progress are two terms that pop up in our minds when we discuss engineers. Are you wondering about what the world be like with no engineers? Imagine a world of chaos – no houses, no pipelines, no electricity, and of course no electronic devices from which you are reading this article.
While we appreciate their contribution to the world, let us take a moment and go back to learning about those engineers who have impacted the engineering world and continue to do so with their ground-breaking research.
Moshkagundam Visvesvaraya, born in Mysore, British India is renowned for his contributions to Automatic Sluice Gates and Block irrigation systems. His inventions are up to be engineering marvels in the world of engineering. His interest in nation-building and engineering has won him prestigious awards, including India’s highest honour, Bharat Ratna.
To honour his eternal achievements that have turned around lives with dams and electricity in each home, India celebrates Engineers Day every 15th September. May his glorious inventions enable more discoveries and inventions by Indian engineers.
Alan Mathison Turing, also considered the father of theoretical computer science and artificial intelligence is known for his significant contributions to engineering. This includes his joint contributions to mathematics, cryptanalysis, logic, philosophy, and mathematical biology.
Mr. Turing, who developed and invented machines during World War II, is best known for solving the mystery of the 'enigma machine' Germans used to communicate in confidence. During his extensive work in computers, his catchphrase was - Among those problems that can be solved by a computer, which ones can be solved efficiently?
Making Paris known for its famous Eiffel Tower, Gustave Eiffel is a French civil engineer renowned for his work on one of the most travelled tourist spots in the world. His contributions do not limit themselves to the Eiffel Tower.
He is also known to have worked closely on the Statue of Liberty, another tourist attraction in the United States. His work also resounds in the Porto viaduct over the river Douro, the Garabit viaduct, the Pest railway station in Hungary, the dome of the Nice observatory, and more.
Known as the ‘Indian Rocket Man’ through his expertise and involvement in developing ballistic missiles and rocket technology, Dr. A P J Abdul Kalam contributed over and beyond as he served as the 11th President of India (2002-2007). His vast contributions to the aerospace engineering world include the infamous Pokhran II nuclear test, the Rohini satellite, and SLV-III.
Dr. Kalam was not just a project leader. He led India and its youth towards developing the country via science and research. In his time as the President of India, he has pushed projects in the areas of science and culture helping make India as it is today.
One of the few women engineers in the world in the 19th century, Babbitt was concerned with the waste generated by chopping wood. To promote sustainability, resource preservation, and timely delivery of wood for various projects, Babbitt built equipment that became famous as the two-person whipsaw.
With time, she invented the circular saw powered by a water-powered device. This may be a smaller invention among the engineers in this blog. Yet, it is an invention in an era where women were confined within homes is a revolutionary step towards helping women enter the world of engineering.
Alice Parker's concept could be accepted with gratitude by electrical engineers and by homes that use central heating throughout the winter. This African American inventor laid the groundwork for the ultimate creation of the contemporary central heating system. Her gas-powered home heating system was complex and challenging to put into action. This offered those in the next-gen the inspiration to create a new model that generates heat during the cold.
She may be long forgotten due to the complexities in her system, but her patent in 1919 has proved that women in engineering can make a huge impact in the lives of common people. Her invention has enabled millions of homes to be warm and ward off the cold in regions with heavy snow and freezing temperatures.
Kurien, originally a mechanical engineer, pursued a degree in dairy engineering. The engineering community now recognizes Verghese Kurien’s '1 Billion Litre Idea' and revolution in the dairy industry. India now boasts the largest self-sufficient industry in the world for primary rural employment sectors thanks to the White Revolution's Operation Flood, which transformed the dairy product market.
The Anand model created with the cooperation of the Gujarat government gave birth to the dairy cooperative ‘Amul’ and has supported millions of Indians, especially women in becoming independent via dairy farming. Numerous recognitions and honours have been received by Mr. Kurien such as the Ramon Magsaysay Award for Community Leadership (1963) and the World Food Prize (1989).
The father of the Pentium microprocessor chip, Vinod Dham is associated as a co-inventor of flash memory technology. The technology is known as SD cards and is widely utilized in USB drives and digital cameras. His other inventions include AMD K, and Intel’s Flash Memory technology (ETOX). His contribution to computer science and engineering has helped him to be promoted to Vice President of the Microprocessor Group at Intel Co.
Bringing Metro services to India with projects such as the Delhi Metro and Kolkata Metro makes E Sreedharan one of the top Indian engineers who deserves a mention on Engineers Day in India.
His contribution to the public transport system helped him bag the Padma Shri Medal in 2001 and the Padma Viboushan Award in 2008. International acclaim for this work in this sector motivated France to award Mr. Sreedharan with France’s highest folk decoration, the Medal of Honour.
A huge contributor to Apple’s success, Wozniak, fondly known as Woz, was integral in bringing out the world’s first successful personal computer in the 1970s. His business skills alongside engineering helped Apple raise a whopping $1.77 Billion in investment when the company went public in 1980.
His ground-breaking work in computer engineering ensured that every home had a personal computer. His achievements have grown the computer industry multi-fold and inspired companies to take a step towards providing accessible and budget-friendly connectivity to the global world.
If you are on the way to being an engineer, you must be aware that we cannot end the blog without Elon Musk. Co-founded six companies including Tesla, SpaceX, and Boring Company, Musk has worked towards improving space technology with his team.
The world is filled with engineers with great work and achievements, but we had space for the top 11 engineers in our blog. Engineering is not just precision components, it is the idea that sparks in your mind and the result you create with those components.
Remember that inventing incredible inventions requires dedication and practical experience. If our blog inspired you to pursue a career in engineering and your goals line up with famous engineers in this blog, we're confident we can help you get the expertise you require to succeed.
By being a part of JAIN (Deemed-to-be University) - Faculty of Engineering and Technology, you can rest assured that knowledge and opportunities come hand in hand with your growth. Why wait longer to be a part of the engineering world? Start your journey towards a better tomorrow. We await to hear innovative ideas from you!
Employment for mechanical engineers is expected to grow by 10% from 2022 to 2032, significantly faster than the average for all occupations. In India, the construction industry is projected to expand at an average annual growth rate of 6% from 2023 to 2026, creating a high demand for skilled mechanical engineers. Mechanical engineering remains a strong career choice in India due to its broad scope and opportunities across various sectors such as automotive, aerospace, energy, and construction. The field offers good job prospects and competitive salaries, bolstered by substantial government investment in infrastructure projects. On the other hand, thermal engineering is highly sought after in sectors like aerospace, automotive, electronics, and energy. The drive for cleaner energy solutions and more efficient electronic devices has increased the demand for professionals skilled in designing cooling systems, managing heat dissipation, and enhancing product sustainability. In aerospace, for example, thermal engineers are essential for developing systems that protect equipment and passengers from extreme temperatures. Advances in cooling systems and thermal management solutions further drive the need for these specialists across technology-driven industries. Let us learn about mechanical and thermal engineering in depth:
In mechanical and thermal engineering, heat and energy principles play a crucial role in the design, analysis, and optimisation of systems that involve the transfer and conversion of energy. Here's an overview of how these principles are applied:
In mechanical and thermal engineering, the first law is applied to analyse energy balance in systems like engines, compressors, turbines, and heat exchangers. This law asserts that the total energy of an isolated system remains constant, highlighting the need to account for all forms of energy—heat, work, and internal energy—in system design and analysis.
This law is crucial for understanding the efficiency limits of thermal systems. It states that energy conversions increase the entropy of a system, meaning that no process is entirely efficient. Engineers use this principle to assess the performance of engines and refrigeration cycles, determining how to minimise energy losses.
Conduction is the transfer of heat through a solid material without the movement of the material itself. This principle is essential in the design of insulation, heat exchangers, and thermal barriers, where Fourier’s Law helps calculate the rate of heat transfer.
Convection involves the transfer of heat between a surface and a moving fluid. It's critical in designing systems like radiators and cooling systems, where engineers use Newton’s Law of Cooling to calculate heat transfer rates based on fluid motion and temperature differences.
Radiation occurs without the need for a medium, making it significant in high-temperature applications such as furnaces and solar energy systems. The Stefan-Boltzmann Law helps engineers calculate heat transfer by radiation, especially in environments where other forms of heat transfer are minimal.
Cycles like the Carnot, Rankine, and Brayton are fundamental in converting heat energy into mechanical work. These cycles are used in power plants, jet engines, and other systems, providing a framework for maximising efficiency and performance.
Mechanical engineering is a broad field that involves the design, development, and building of machinery using engineering principles. Within this discipline, students can choose to specialise in specific areas, allowing them to focus their studies and career on a niche aspect of mechanical engineering. Some of the common areas of specialisation in mechanical engineering are described below:
This specialisation focuses on optimising robotics, such as autonomous vehicles, biomedical devices, and drones. Engineers in this field work on advanced mechanical systems and artificial intelligence, often in aerospace, military, defence, or automotive industries. Key topics include probability, statistical methods, algorithms, and the automation of aerospace vehicles.
Automotive design combines engineering and creativity, emphasising the analysis and optimisation of mechanical systems in vehicles. Students learn about material handling, sensor systems, and quality control to improve vehicle design. This specialisation is ideal for the students aiming to work in the automotive industry.
This specialisation can be academic or practical. Academically, it involves studying control systems that manage and regulate device behaviours. Practically, it applies to designing motion control systems, computer storage devices, and biomedical systems in the business sector. Engineers in automation and control systems may also design intelligent systems for robotics and automated vehicles, enabling advanced autonomous operations across various industries.
Ocean engineering deals with designing and analysing systems that operate offshore or in coastal environments. It focuses on the interaction between fluid and solid elements in the ocean, relevant to industries such as oil, energy, conservation, and natural sciences. Ocean engineers may also work on the design of underwater vehicles, offshore wind turbines, and marine renewable energy systems, contributing to advancements in sustainable ocean technology.
This specialisation explores technologies that harness energy from natural sources like the atmosphere, ocean, and groundwater. Students learn about energy flows, climate data, and sustainable energy systems. Careers in this field often involve working with energy companies or environmental organisations.
Combining chemistry and physics, this specialisation addresses issues in nanotechnology, biotechnology, and energy. Students study material selection, fabrication, and thermodynamics, preparing them for roles in healthcare, chemical engineering, and related fields. Engineers in materials science and engineering may also develop cutting-edge materials for aerospace, electronics, and renewable energy applications, driving innovation across multiple high-tech industries.
Thermal engineering involves the study of heat transfer, fluid mechanics, and the design of heating and cooling systems used in industries like electric power, automotive, and HVAC. Thermal engineers create systems that convert thermal energy into chemical, mechanical, or electrical energy, relying on principles of thermodynamics, fluid mechanics, and heat and mass transfer. This expertise is essential for operating a wide range of machinery. Mechanical and chemical engineers often specialise in thermal engineering to deepen their understanding of thermal sciences. The key specialisation areas in thermal engineering are as follows:
This area of thermal engineering is dedicated to the generation, use, and exchange of heat between physical systems. It covers all methods of heat transfer, including conduction, convection, radiation, and phase change energy transfer. Engineers specialising in this field may work on projects related to automotive engineering, thermal management of electronic devices, climate control, insulation, materials processing, and power station engineering.
Thermal system design is an interdisciplinary specialisation that combines thermodynamics, fluid mechanics, and heat transfer to find effective solutions for real-world systems. Engineers working in this field are responsible for the design and optimisation of fluid flow systems, pumps, turbines, heat exchangers, and other energy conversion systems. They must manage all aspects of thermal energy to ensure systems operate efficiently and meet performance standards, making this a key area in thermal engineering.
Combustion engineering is focused on the application of combustion science to industrial systems. Engineers in this specialisation design, test, and implement combustion equipment and energy-burning systems, with an emphasis on developing new technologies for environmentally sustainable fuel consumption. This field plays a vital role in supplying steam power for electricity generation in the United States, as well as in other industries that rely on combustion processes.
This specialisation is focused on the study of heat and mass transfer, fluid flow, and the development of new technologies in the energy sector. Engineers in this field work on a wide range of projects, from studying new energy materials to converting waste into energy, improving energy storage technologies, and ensuring the sustainability of energy systems. They may also focus on low-carbon environmental protection, climate change mitigation, and sustainable development goals.
Engineers specialising in refrigeration and air conditioning tackle the challenges of designing and installing more efficient cooling systems. The focus is on reducing energy consumption and minimising the heat released into the environment. Projects in this area may include the development of water-based cooling technologies, improvements to heat-driven cooling systems, and the creation of hybrid models that incorporate conduction, convection, and radiation.
Turbomachinery is a branch of thermal engineering that deals with systems that transfer energy between a rotor and a fluid, such as turbines and compressors. Engineers specialising in this field work on designing and optimising turbomachines used in power generation, including hydroelectric turbines, steam turbines, gas turbines, and windmills. In the aerospace industry, thermal engineers work on gas turbines and turbopumps, ensuring these systems operate efficiently and reliably across a range of applications.
Mechanical engineers, known for their ability to create cost-effective designs, have a wide range of lucrative career opportunities available to them. Their problem-solving skills and technical expertise make them valuable across various sectors. In the aerospace sector, they work on designing and testing aircraft and spacecraft. The automobile sector offers opportunities in vehicle design and manufacturing. Energy utility firms utilise their skills to enhance power generation and distribution systems. Engineering consultancies and government agencies seek their expertise for project management and policy development. The armed forces and biomedical industries provide roles in developing advanced technologies and medical devices. Additionally, the marine industry offers positions in ship design and offshore engineering. Some of the promising career avenues after completing graduation are as follows:
Thermal engineers, experts in heat transfer and energy systems, find diverse career opportunities across various industries due to their specialised skill-set and knowledge. In the renewable energy sector, they work on designing and optimising solar thermal systems and geothermal energy solutions. The chemical processing industry relies on them for managing heat in chemical reactions and refining processes. In the pharmaceutical industry, thermal engineers focus on temperature control for drug production and storage. The food and beverage industry employs them to design and maintain systems for temperature regulation in processing and preservation. They can also pursue career roles in the textile industry, where they can work on thermal management for manufacturing processes. Additionally, thermal engineers are crucial in the development of advanced thermal systems for electronics cooling and telecommunications. Some of the promising career avenues after completing graduation are as follows:
Mechanical engineers benefit from a broad spectrum of career opportunities, ranging from designing and developing mechanical systems to engaging in specialised fields such as automotive design, robotics, and renewable energy. The field’s enduring appeal is further enhanced by competitive salaries and substantial government investments in infrastructure projects, which continue to drive demand for mechanical engineering expertise. In contrast, thermal engineering is gaining prominence due to the increasing need for efficient thermal management and cleaner energy solutions. The growing focus on advanced cooling systems and energy-efficient technologies has increased demand for thermal engineers across multiple sectors, including aerospace, automotive, electronics, and energy. These professionals play a crucial role in designing systems that manage heat dissipation, enhance product sustainability, and contribute to environmental sustainability. Both mechanical and thermal engineering offer robust career prospects and opportunities for impact. The continued evolution of these fields, driven by innovation and global challenges, ensures that professionals in these areas will remain at the forefront of engineering solutions.
Engineers and innovators worldwide are dedicated to developing ground-breaking technologies that contribute to a greener and more sustainable future. These advancements, from solar-powered aircraft to self-healing materials, highlight human ingenuity in addressing urgent environmental challenges. Innovation in engineering involves thinking beyond traditional boundaries and devising creative solutions for complex problems. Engineers continually push the limits of possibility, applying their expertise to create new technologies and enhance existing ones. As a result, they are at the forefront of innovation in various fields, such as designing more efficient engines and developing cutting-edge medical devices. Innovation is crucial for engineering as it drives progress and helps solve intricate problems. By constantly exploring new ideas and approaches, engineers can develop more efficient, effective, and sustainable systems and technologies that benefit society. This blog will explore the latest trends and best practices in engineering innovation, offering insights into the dynamic world of engineering and innovation:
Innovation is essential for fostering progress and addressing complex challenges in the field of engineering. Here are some key reasons why engineering and innovation go hand in hand:
New technologies drive progress in engineering by enhancing the efficiency and effectiveness of projects. For instance, the development of advanced computer-aided design (CAD) software allows engineers to create more precise and efficient designs. Innovations such as 3D printing have revolutionised manufacturing processes, enabling rapid prototyping and customised production.
Innovations and novel techniques in engineering can lower the costs associated with materials, labour, and maintenance, making projects more affordable and accessible. For example, the use of modular construction techniques allows for the prefabrication of building components, which can reduce construction time and labour costs. Innovations in materials, such as the development of high-strength, lightweight composites, can lower material costs and extend the lifespan of structures. Additionally
Engineering and innovation work together to develop creative solutions that contribute to environmental protection, ensuring a healthier planet for future generations. For example, advancements in renewable energy technologies such as solar panels and wind turbines help reduce reliance on fossil fuels. Innovations in waste management and recycling processes contribute to minimising environmental pollution.
Advances in engineering and innovation lead to the creation of safer infrastructure, including buildings, roads, and bridges, by refining design and construction practices. Innovations such as smart sensors and monitoring systems can detect structural weaknesses or hazardous conditions in real-time, allowing for timely interventions.
Innovation has significantly transformed engineering, continuously introducing new technologies and methods that enhance both processes and products. Here’s how innovation has influenced the field of engineering:
Advances in materials science have enabled engineers to create materials that are stronger, lighter, and more durable. These innovative materials are used across various sectors, including construction and transportation, to improve the performance and longevity of structures and products. For instance, the development of high-strength composites and advanced alloys has led to more resilient and efficient designs, from skyscrapers to spacecraft.
The advent of automation has dramatically changed manufacturing processes. Automated systems and robotics increase production efficiency by performing repetitive tasks with high precision and speed. This shift not only boosts productivity but also reduces human error and improves product quality. Automation is widely used in industries such as automotive manufacturing, where it enhances the consistency and accuracy of assembly lines.
Digital technology has revolutionised the design and simulation of engineering systems. Engineers now use sophisticated software tools to create detailed models and simulations, allowing them to test and optimise designs virtually before actual construction. This digital approach helps in identifying potential issues early in the design process, leading to more efficient and effective engineering solutions.
Innovations in sustainable engineering focus on developing products and processes that have a minimal environmental impact. By incorporating eco-friendly materials and energy-efficient technologies, engineers contribute to reducing waste, conserving resources, and lowering carbon footprints. Examples include green building practices, renewable energy solutions, and advancements in recycling technologies that promote environmental stewardship.
The last few years have marked a significant milestone in engineering and technology, with ground-breaking innovations across various fields. From clean energy solutions to advanced prosthetics, the contributions of start-ups, researchers, scientists, and engineers worldwide have led to remarkable advancements. Here are some of the new technology inventions in the field of engineering that have made a huge impact on the world:
Ukrainian-founded biotech start up Esper Bionics has pioneered the future of prosthetics with its AI-powered Esper Hand. This advanced prosthetic arm, a testament to engineering and innovation, mimics the movements and dexterity of a natural hand using a non-invasive brain-computer interface. The arm’s AI capabilities enable it to learn and adapt to the user’s unique movement patterns over time, making its use more intuitive and effortless.
Germany introduced the world’s first hydrogen-powered passenger trains in 2022. The Coradia iLint fleet operates in Lower Saxony, replacing diesel trains with environmentally friendly alternatives. Hydrogen fuel cells offer a scalable solution for green transportation, emitting zero greenhouse gases and reducing noise pollution. This innovation promises cleaner air and a quieter, more enjoyable travel experience.
Launched in December 2021, the James Webb Space Telescope (JWST) represents a pinnacle of engineering and innovation in space exploration. As the most powerful telescope ever sent to orbit, the JWST provides unprecedented images and data on distant galaxies and exoplanets. Its advanced sensors enable detailed observations of planets outside our solar system and offer insights into the universe’s formation by looking back millions of years in time.
In May 2022, researchers at MIT unveiled the world’s first lab-grown wood. This cell-cultured wood, derived from Zinnia plant cells, can be 3D printed into various shapes without requiring live trees. This innovation presents a major leap towards sustainable manufacturing by reducing the need for deforestation. MIT’s ongoing research with Foray Bioscience aims to integrate cell-cultured wood into supply chains, offering an eco-friendlier alternative to traditional timber.
The Oscilla Power Triton energy system is a breakthrough in engineering and innovation for harnessing wave energy. This device captures kinetic energy from ocean waves and converts it into electricity with an impressive 75% efficiency rate. The Triton’s design allows it to operate during extreme weather conditions and be manufactured affordably on a large scale. As a promising source of renewable energy, wave power could significantly contribute to global climate goals and complement other clean energy technologies like wind and solar power.
The innovation process in engineering is a dynamic journey that involves creativity, problem-solving, and collaboration. To successfully innovate in engineering, individuals should follow these essential steps:
The journey begins with identifying a problem or opportunity that needs to be addressed. Recognising the right challenge is crucial for setting the direction of the innovation efforts.
Once the problem is identified, the next step is to conduct thorough research. This involves gathering information through market analysis, data examination, and consultations with experts to gain a comprehensive understanding of the issue.
With the gathered information, the next stage is brainstorming potential solutions. This phase is where creativity comes into play, generating a range of ideas to tackle the identified problem.
Transforming ideas into a tangible form is crucial, and this is achieved by developing a prototype or proof of concept. This could be a physical model, a digital simulation, or any preliminary version of the solution.
Evaluating the prototype through rigorous testing is essential. The prototype should be refined and adjusted based on feedback and test results to ensure it meets specifications and effectively addresses the issue.
Once the solution is refined and ready, it is time to implement it and market it to the intended audience. This final step involves bringing the engineering innovation to the real world and promoting it effectively.
The relentless pursuit of innovation in engineering underscores a profound commitment to advancing both technology and sustainability. As engineers and innovators tackle complex problems with inventive solutions, they not only address immediate needs but also lay the groundwork for long-term progress. The integration of cutting-edge technologies such as AI-driven prosthetics, hydrogen-powered trains, and cell-cultured wood exemplifies how engineering is evolving to meet global challenges with creativity and precision. Looking ahead, the ongoing exploration of emerging trends and best practices in engineering will be crucial in shaping a future where technological progress aligns with environmental stewardship and societal well-being. The dynamic nature of engineering innovation promises exciting developments, and staying abreast of these changes will be essential for harnessing their full potential.

Artificial intelligence has been in our lives for a while and has been taken up by a storm. Today, as individuals are webbed into technology and devices, artificial intelligence comes to the rescue to make our lives easier. It helps in impeccable creations that go above and beyond human imagination.
As it takes over our lives for the better, we see it support us via self-driving cars, humanoid robots, and reusable robots and put itself to use when it comes to technical assistance in education, healthcare, business, and industries.
As people from the era of computers and robots, it is essential to move towards open AI with a positive mind, introduce it into our lives, and incorporate it as a support system. For this to be successful and fruitful, we must understand various advantages of artificial intelligence.
Did you know? The education system is improvising its curriculum and assignments to support the growth of students as a research by McKinsey points out that student retention has improved by 30% after AI-powered personalized learning platforms were introduced to students.
When a simple artificial intelligence powered software holds this power, let us explore what it holds to help us better our standard of living.
Algorithms powered by AI have been developed to help detect various diseases in patients showing symptoms of distress. It provides stability and efficiency with drug discovery and surgeries. Various equipments in operation theaters have reduced the rate of error and improving the process of healing.
For example - A study has discovered that AI algorithms can help detect breast cancer as efficiently as radiologists.
Personalized learning is taking over the education industry. With videos, presentations, animations, and simplified explanations of topics, open ai has relieved the stress on educators by lending them a helping hand in classrooms. By automating grading systems, teachers are encouraged to spend more time with students and understand their requirements in terms of interpersonal skills and academics.
Did you know? Around 10 million students globally use AI-based tutoring systems. This helps in bridging the gap with teacher-student ratio.
Large-scale and small-scale industries use advanced technology of AI as a system that reduced the burden of report making and instant replies via customer care. A research by Gartner shares that businesses will be adopting AI chatbots into customer service and over 80% of customers are prepared to overlook errors by chatbots until the service remind excellent. Companies are looking forward to automate certain functions and reduced budget allocation and increase productivity and profits.
Finance and entertainment industries are required to beyond audience and stakeholder expectations with each step. With the help of AI, they bring out nw features and enhance technologies that monitor transactions and fraud. AI has also supported in enhancing images and videos that help to visually please the audience. In the finance sector, about 50-70% of fraud transactions have been monitored via real time transaction monitoring. And by recommendations of AI, 80% of the content viewed on OTT platforms have been according to audience preferences and liking.
Imagining a day without Google Assistant, Alexa, and Siri may not be as we expect it to be. With smartphones gaining popularity and accessible features, over 3.25 Billion voice-activated AI assistants are in use on smartphones worldwide. Artificial intelligence today runs the smartphone market with various app and content recommendations, navigation, and purchasing.
As advanced technology has taken over our lives in various forms, the demand for engineers who work with diverse technologies and open ai are increasing in the industry. If you are interested in working closely with a team that innovate everyday with algorithms and devices, our courses on artificial intelligence, machine learning, data engineering, and more at JAIN (Deemed-to-be University) holds the potential to support your entry into the industry.
As we see diverse advantages of artificial intelligence, we come to realize how much of technology is imbibed into our day to day life. AI has proven to be revolutionary not only in science but also in an ordinary man’s life. Let us take a moment and appreciate the development we see everyday with technology. To be part of this movement, enroll into our B. Tech and M. Tech courses and contribute your ideas and skills into making the world a sustainable and better place to experience the true essence of life.
The Indian job market for Electronics and Communication Engineers is projected to grow at a steady rate of 7% annually. By 2026, more than 345,800 positions are expected to be available, with overall employment in the field anticipated to grow 5% from 2022 to 2032, outpacing the average for all occupations. Electronics Engineering and Communication Engineering are two highly sought-after disciplines within the broader engineering sector, offering abundant opportunities for innovation and professional advancement. Several engineering students also opt for a combined course of electronics and communication engineering. These two fields of engineering emphasise the analysis of electronic systems, communication devices, and related technologies, encompassing areas like embedded systems, signal processing, communication systems, and both analogue and digital electronics. Pursuing Electronics Engineering and Communication Engineering open doors to a variety of careers, including wireless communication, hardware engineering, telecom engineering, software analysis, and robotics engineering, with numerous opportunities for specialisation and career growth. Let us explore each discipline in detail:
Signal processing, transmission, and reception are key concepts in electronics and communication engineering, focusing on the manipulation and management of signals to transmit information effectively. Let us understand each one of the functions:
Signal processing involves the analysis, modification, and synthesis of signals to enhance their quality, extract useful information, or prepare them for transmission. This can include operations such as filtering, modulation, amplification, and encoding. Signal processing can be performed on analogue signals, digital signals, or a combination of both.
Signal transmission refers to the process of sending a signal from one location to another through a medium, such as air, cables, or fibre optics. The key goal is to ensure the signal reaches the destination with minimal loss of quality and information.
Signal reception is a critical stage in the communication process, where the transmitted signal is captured, processed, and converted back into its original form or a form suitable for further processing. This stage involves several key components and techniques to ensure the signal is accurately received and interpreted.
Electronics is a branch of engineering that focuses on the design and application of electronic circuits, devices, integrated circuits, and systems using components like semiconductors, transistors, and diodes. The Bachelor of Engineering (BE) or Bachelor of Technology (BTech) in Electronics Engineering is a 4-year programme, divided into 8 semesters. The Master of Engineering (ME) or Master of Technology (MTech) in Electronics Engineering spans 2 years, divided into 4 semesters. This field covers a wide range of areas, including analogue and digital electronics, consumer electronics, embedded systems, and power electronics. Electronics Engineering also intersects with various related fields such as solid-state physics, radio engineering, telecommunications, control systems, signal processing, systems engineering, computer engineering, instrumentation engineering, electric power control, photonics, and robotics. The key topics covered in the curriculum are as follows:
Electronics Engineering offers a variety of specialisations that allow engineers to focus on specific areas of interest. Here are some common specialisations:
Communications Engineering is a branch of engineering that focuses on the transmission, reception, and processing of information across various channels such as radio, optical fibres, and satellite links. It deals with the design, development, and maintenance of communication systems that enable voice, data, and video transmission over short and long distances. The BE or BTech in Communications Engineering is typically a 4-year programme whereas the ME or MTech in Communications Engineering is a postgraduate degree that spans 2 years. This field covers a wide range of areas, including wireless communication, data communication, optical communication, satellite communication, and network engineering. Communications engineering also intersects with various related fields such as signal processing, computer networks, digital communication, microwave engineering, and information theory. The key topics covered in the curriculum are as follows:
The different types of specialisation areas available in Communication Engineering are listed down below:
Electronics Engineering students have a wide range of career opportunities across various industries. In aerospace and defence, they can contribute to designing avionics and communication systems for aircraft and spacecraft with leading organisations like ISRO and DRDO. In the consumer electronics sector, they can develop innovative features for products such as smartphones and TVs, working with companies like Samsung India and LG Electronics India. Additionally, the semiconductor industry offers roles in chip manufacturing and testing with firms like Intel India and Texas Instruments India. Electronics engineers can also find employment in diverse fields, including aviation, consumer electronics, power plants, manufacturing, transportation, computer applications, radio and television, diagnostic equipment production, and offshore companies. Some of the potential career avenues in this field are as follows:
In the telecommunications sector, students can work on designing and maintaining communication networks, including mobile, broadband, and satellite systems, with companies like Bharti Airtel, Reliance Jio, and Vodafone Idea. In the broadcasting industry, Communication Engineering students can contribute to the development of transmission systems and content distribution networks for radio and television with organisations like Doordarshan and All India Radio. The defence sector also offers roles in secure communication systems and radar technology, working with agencies like DRDO and Bharat Electronics Limited (BEL). Communications engineering students can also pursue careers in wireless communication, network engineering, optical fibre technology, satellite communication, IT and networking companies, broadcasting, and even emerging fields like IoT (Internet of Things) and 5G technology. Some of the potential career avenues in this field are as follows:
The fields of Electronics Engineering and Communication Engineering are poised for significant growth in India, offering promising career opportunities in various sectors. With a steady demand for skilled professionals, these disciplines are integral to technological innovation and advancement. Whether you specialise in signal processing, embedded systems, wireless communication, or any other related area, the diverse curriculum and specialisations in both fields provide a strong foundation for a successful and dynamic career. The continuous evolution of technology, including the rise of 5G, IoT, and AI, further amplifies the relevance and demand for professionals in these fields. As the industry continues to evolve, engineers in these fields will be at the forefront of driving technological progress, making substantial contributions to a wide range of industries.
The Internet of Things (IoT) is a rapidly expanding network of connected devices, with over 50 billion IoT devices in use today. This vast network generates and communicates data between devices and systems. The core value of IoT lies in this data exchange, which allows consumers and businesses to access raw information, derive insights, and make informed decisions based on the data. IoT offers numerous benefits, prompting more companies to explore IoT technology, and its business applications. However, it also presents challenges, particularly concerning security and standards. Currently, most IoT devices are consumer-oriented, including smart TVs, vehicles, wearable exercise monitors, and refrigerators. Businesses, too, are leveraging IoT through security cameras, smart building infrastructure, connected electric metres, industrial control systems, GPS systems, and RFID chips, among other use cases. With the affordability of processors and the proliferation of wireless networks, it is now possible to connect almost any device, making it "smart." These smart devices, equipped with data-generating sensors, create a new intersection between the digital and physical worlds. Let us learn more about what is IoT (internet of things):
The full form of IoT stands for Internet of Things. The Internet of Things (IoT) refers to the vast network of billions of physical objects connected to the internet, enabling them to collect and exchange data. The proliferation of affordable computer chips and wireless networks has allowed a wide range of items, from pills to aeroplanes, to become part of the IoT ecosystem. This technology connects everyday objects such as home appliances, cars, thermostats, and baby monitors to the internet through embedded electronics. As one of the most transformative technologies of the 21st century, IoT facilitates continuous communication among people, processes, and things. Let us learn more about what is IoT internet of things that is significantly enhancing efficiency and connectivity around us:
The Internet of Things (IoT) is a network of interconnected devices that communicate and exchange data with each other and the cloud. But what is IoT technology? It involves devices embedded with sensors and software that can include both mechanical and digital machines, as well as consumer objects. IoT devices range from everyday household items to complex industrial tools. Increasingly, organisations across various industries are using IoT to enhance operational efficiency, deliver better customer service, improve decision-making, and increase business value.
A key feature of IoT is its ability to transfer data over a network without requiring human-to-human or human-to-computer interactions. These smart objects include simple devices like smart thermostats and smartwatches, RFID-enabled clothing, and sophisticated industrial machinery and transportation systems. Technologists are even envisioning entire "smart cities" built on IoT technologies. The essence of what is IoT lies in its capability to enable these smart devices to communicate with each other and other internet-enabled devices, such as smartphones and gateways. This creates a vast network of interconnected devices that can autonomously exchange data and perform various tasks. Examples include monitoring environmental conditions on farms, managing traffic patterns with smart cars, controlling machinery and processes in factories, and tracking inventory and shipments in warehouses.
IoT systems operate by collecting data from sensors embedded in IoT devices. This data is then transmitted through an IoT gateway to be analysed by an application or back-end system. The IoT ecosystem comprises the following:
An IoT ecosystem is composed of web-enabled smart devices equipped with processors, sensors, and communication hardware. These components allow the devices to collect, transmit, and act on data from their environments.
IoT devices communicate over the internet via a network. They connect to an IoT gateway, which serves as a central hub for data transmission. Before reaching the gateway, data may be analysed locally by an edge device, which helps reduce the volume of data sent to the cloud and minimises bandwidth use.
Data analysis involves filtering out irrelevant information to identify patterns, provide recommendations, and detect potential issues early. Analysing data locally helps decrease cloud data usage and bandwidth consumption.
A graphical user interface (UI) is commonly used to manage IoT devices. This can be a website or a mobile app that allows users to control, manage, and register smart devices. An easy-to-use interface helps professionals identify and react to the data in real time.
The Internet of Things (IoT) enhances both personal and business experiences by connecting and automating various devices. For individuals, IoT-embedded devices such as smartwatches, thermostats, and vehicles streamline daily routines. For instance, a car can automatically open a garage door upon arrival, while a thermostat adjusts the temperature and lighting settings to adapt to a preferred ambiance. By automating tasks and reducing human intervention, IoT enables companies to lower labour costs, minimise waste, and improve service delivery, ultimately making manufacturing and delivery processes more cost-effective and transparent. Modern factories use smart, internet-enabled machines that provide real-time sensory data. This data enables predictive maintenance, reducing downtime, and increasing efficiency.
The vast amount of data generated by IoT devices offers profound insights for decision-making. Effective data retrieval and analysis are crucial for leveraging this information. While consumer applications often integrate data analysis through paired apps, businesses are developing strategies to manage and use this data effectively. IoT also supports high levels of personalisation, allowing services to be dynamically adjusted based on real-time data and individual preferences. Furthermore, IoT can dramatically reduce overhead and lower expenses for businesses. For example, it enables precise inventory management, which improves food freshness and tracking in retail environments. By offering better visibility into inventory needs and consumption patterns, the IoT helps organisations streamline operations and enhance efficiency. Now that we know what is IoT internet of things is and its benefits, let us look at its applications across industries:
The Internet of Things (IoT) offers significant benefits, but it also presents several challenges that enterprises must address to fully leverage its potential.
As IoT technology advances, it introduces new security concerns. The proliferation of connected devices increases the risk of security breaches. With a larger number of devices, the potential attack surface expands, making it more difficult to ensure comprehensive security. Vulnerabilities in one device could potentially compromise others, leading to severe consequences such as unauthorised access to smart cars, wireless routers, or even critical medical devices like pacemakers.
The rapid growth of IoT devices highlights the need for uniform standards to ensure device security and accountability. Currently, the absence of standardised policies and guidelines poses a challenge for securing IoT environments. There is a call for manufacturers and providers to enhance their liability and collaborate on information sharing to mitigate security risks. As IoT continues to develop, establishing and adhering to these standards will be crucial for securing devices and systems.
According to Forbes, the IoT healthcare market is projected to reach approximately $150 billion in 2024, with an anticipated valuation of $289 billion by 2028. This growth is driven by the increasing use of wearables and in-home sensors for remote health monitoring. By 2035, revenue from autonomous cars is expected to range between $300 billion and $400 billion. As IoT technology progresses, there is a shift from single-device models to modular, microservice approaches. Enhanced connectivity technologies, including 5G, Wi-Fi 6, LPWAN, and satellites, are facilitating IoT adoption. Additionally, wearable devices such as smartwatches, earbuds, and AR/VR headsets are rapidly evolving.
The future of IoT in enterprises is promising, with the potential for significant business advantages. For example, logistics companies can use IoT data to optimise routes, reduce costs, and improve operational efficiency. However, the challenges associated with IoT, such as managing and securing devices and data, will need to be addressed. Companies must develop effective strategies for connection, integration, and maintenance to make meaningful use of IoT data. The success of IoT will depend on how well organisations can address these issues and leverage the technology to drive innovation and efficiency.
With its capacity to connect billions of devices, IoT offers unparalleled opportunities for innovation, efficiency, and customisation. From enhancing daily life through smart home devices to driving operational improvements in varied industries, the impact of IoT is far-reaching. However, as we embrace these advancements, it's crucial to remain vigilant about the associated challenges. The growing complexity of IoT networks underscores the need for robust security measures and standardised protocols to safeguard against potential risks. The future of IoT will depend not only on technological advancements but also on our ability to address these challenges effectively. As we continue to integrate IoT into various aspects of our lives and businesses, understanding what is IoT and creating a secure and standardised framework will be essential to supporting its growth and maximising its benefits. By doing so, we can harness the full potential of the IoT, driving progress while ensuring a safe and connected future.
ECE is a branch in engineering that deals specifically with electronic equipments and troubleshooting equipments. If you are a student who dreams to work in advanced networking services such as video conferencing technology, televisions, telephones, and connect people across the globe, this course is your calling. Looking to pursue your goals in the field of ECE after this? This blog is made for you to understand ECE full form in engineering.
ECE engineering full form is Electronics and Communication Engineering. This branch of engineering focuses on research, design, and developing new communication devices. It also helps deal with troubleshooting equipments for bugs and fixing them for usage.
This degree is presented in both undergraduate and postgraduate level in the form of B. Tech and M. Tech from various universities - central, state, private, as well as, deemed-to-be universities such as JAIN (Deemed-to-be University).
Few areas of study under ECE include signal processing, solid state devices, satellite communications, analogue transmission, basic electronics, microwave engineering, aviation electronic or telecommunication engineering, control engineering, and more.
The minimum qualification required by institutions in India for B. Tech in this field include to qualify the 10+2 examination in Science. This qualification can be from PUC/ ISC/ CBSE, or an equivalent board. The criteria can vary from institution to institution.
Electronics and Communications Engineering holds opportunities that can help you grow as an individual in the industry. Here are some of the career paths you can opt for after understanding the ECE full form in engineering -
As a student longing to pursue your studies in engineering after understanding ECE full form in engineering, let us explore various entrance examinations that help you get selected within reputed institutions for higher education.
JAIN (Deemed-to-be University) - Faculty of Engineering and Technology AKA JU-FET offers a B. Tech and M. Tech program in Electronics and Communications Engineering. This course offers specialization in VLSI design and technology and Robotics.
With a dynamic OBE syllabus, the university works towards upskilling students and support research across various specializations. Vibrant research activities enables students to experiment and derive diverse solutions that keep up with the need of the hour and industry standard.
To sum up the points discussed above about ECE degree, we have understood ECE full form in engineering, the eligibility criteria to fulfill the admission requirements, scope of employment, and how JU-FET can help you complete your degree in Electronics and Communications Engineering.
This engineering degree holds the power to help you move across verticals in the area of ECE. If your focus is to work with electronic gadgets, networking, and drives new technologies, this path in your graduate and postgraduate studies can help you move above and beyond towards your career goals and success. Join the spirit of researching new technologies with ECE degree and discover sustainable solutions that can make a huge difference in remote areas, rural areas, as well as urban cities.
Are you seeking a course that enables you to work within the technical field? Does your career goals include being an engineer with diverse skills? A BE degree can assist you in reaching this objective.
BE is a branch of engineering that assists in gaining the technical know-how required to work in the energy, manufacturing, petroleum, and artificial intelligence sectors, among other areas. This degree holds the power to push you within sectors with knowledge and experience. Before we take a step towards understanding BE in details, let us understand the full form of BE degree.
BE degree full form is Bachelor in Engineering. By its name, we can understand the area of expertise it offers to individuals interested in this course. Having this degree will make it easier for employers to recognize your interest in working in the engineering field with machines and software.
The BE full form in engineering explains us the various courses that you can join and grow within. Some of the courses include Electrical Engineering, Mechanical Engineering, Aerospace Engineering, Computer Science and Engineering, Electronics and Telecommunication Engineering, Chemical Engineering, Mining Engineering, Civil Engineering, Textiles Engineering, Automotive Engineering, Information Technology, Biochemical Engineering, and Biomedical Engineering.
BE and its specializations are offered in many countries such as India, UK, US, Canada, Australia, New Zealand, and more. Since it is a popular subject in India, many universities such as IITs, NITs, state universities, central universities, private and deemed universities such as JAIN (Deemed-to-be University) offer this course with customized program schedules and curriculums.
As we now understand BE full form in engineering, what exams must be attended to get an admission to this course?
After you are acquainted with the BE degree full form, let us discover the different entrance exams you may have to appear to depending on the institute you want to join for this course.
Some entrance exams for Bachelor in Engineering include IIT-JEE (Indian Institute of Technology - Joint Entrance Exam) , AIEEE (All India Engineering Entrance Examination, currently known as JEE (Main)), and KCET (Karnataka Common Entrance Test) in Karnataka.
The course of this programme is for 4 years in India, however depending on the requirements and industry standards, it can last anywhere from 3 to 5 years in other countries.
It is not enough to just understand BE full form in engineering. This course comes with a criteria list that needs to be fulfilled to join.
Criteria include that the student must have passed 10+2 from a recognized board of the university with subjects Physics, Chemistry and Mathematics. The requirement of the percentage scored can vary from university to university.
JAIN (Deemed-to-be University) offers a diverse portfolio of engineering degrees in bachelors and masters level. The University builds its own curriculum and collaborates with multiple industry experts and companies to offer a one-of-a-kind course that helps students keep up with the expectations of the industry.
The criteria for admission at JAIN (Deemed-to-be University) is to have passed the 10+2 from PUC, ISC, CBSE or equivalent board with Physics and Mathematics as major with Chemistry, Electronics, Computer Science or Biology. The student is required to have passed the exam with 45% (40% for SC/ST).
For IB students, a minimum of 26 credits is required to qualify for this course.
Cambridge students must have Physics, Chemistry, and Mathematics as their three subject in ‘A’ level (Advanced level).
Final year students of class XII or its equivalent, awaiting examination results may also apply
NIOS candidates are eligible to apply.
Entrance Score Accepted - UNIGAUGE / JEE / ComedK
Candidates can join the course via JET (JAIN Entrance Test) Examination.
Bachelor in Engineering brings with a multitude of careers you can choose from. Some of them include -
Understanding the full form of a BE degree can help you make a decision on whether you want to continue your studies in the field of engineering. If you are looking for a course for tech enthusiasts like yourself, Bachelor of Engineering is your go-to-course for the future. Together with us, take this step today and unlock a whole new world of cutting-edge technology at your fingertips.

The Indian Electrical Equipment industry is projected to grow at a compound annual growth rate (CAGR) of 12%, reaching over $70 billion by 2025. This growth presents promising opportunities, particularly for students pursuing Electrical and Electronics Engineering. In the current era, marked by a significant demand for electronic devices, components, and innovative designs, the range of career options in Electrical and Electronics Engineering, or EEE full form in engineering continues to expand. After graduation, students can find lucrative job opportunities in the fields of power generation, distribution, transmission, energy storage, renewable energy, and energy management. Moreover, as a Research and Development (R&D) engineer, students can also work across diverse industries, including technology, manufacturing, aerospace, consumer goods, energy, chemicals, and healthcare. Let us learn more about EEE in depth:
EEE engineering full form, stands for Electrical and Electronics Engineering. EEE is a specialised branch of engineering that focuses on the study, design, development, and application of electrical systems, devices, and technologies. This field encompasses a wide range of areas, including electrical circuits, power systems, electronics, telecommunications, control systems, and signal processing. Electrical and Electronics Engineering, or EEE full form, focuses on the fundamental principles of electricity, electromagnetism, and electronics. Key details about EEE are summarised below:
|
EEE full form in engineering |
Electrical and Electronics Engineering |
|
Level of Study |
Undergraduate (UG): Bachelor of Technology (BTech) in EEE Postgraduate (PG): Master of Technology (MTech) in EEE) |
|
Duration |
UG: 4 years PG: 2 years |
|
Admission Process |
Admission Examination/ Direct Admission |
In an EEE course, students learn to design and analyse electrical systems, ranging from small-scale integrated circuits to large power distribution networks. The Electrical and Electronics Engineering, or EEE full form in engineering curriculum typically covers subjects such as circuit theory, digital electronics, electromagnetic fields, power electronics, microprocessors, and control systems. This discipline also prepares students to tackle real-world challenges in energy generation, transmission, and utilisation through internships and industrial visits. In this course, students learn about a wide array of topics, including semiconductors, analogue electronics, and power systems. The curriculum also emphasises big transmission lines, digital electronics, electrical machines (both AC and DC), and control systems. A BTech in Electrical and Electronics Engineering, or BTech EEE full form, enables students to apply electrical and electronic principles to circuits, machines, power systems, and control systems. This knowledge will enable them to develop solutions for industrial automation, green energy systems, and smart grids effectively.
Electrical and Electronics Engineering, or EEE full form in engineering offers a variety of specialisations, each focusing on different aspects of the field. Here are some common EEE specialisations:
To enrol for a BTech in Electrical and Electronics Engineering, or BTech EEE full form, students must have passed the Class 12th or Pre-University Course (PUC) or an equivalent qualification from a recognised board. Additionally, students must have secured a minimum of 45% aggregate marks in physics and mathematics, along with chemistry, biotechnology, biology, electronics, or computers. Additionally, candidates must qualify for one of the following entrance exams: the Common Entrance Test (CET), the Consortium of Medical, Engineering, and Dental Colleges of Karnataka (COMED-K), the Joint Entrance Examination (JEE), or the All India Engineering Entrance Examination (AIEEE). For postgraduate admission, the candidate must hold a Bachelor of Technology (BTech) degree in Electrical Engineering with a minimum of 55% aggregate marks from a recognised university. Furthermore, students must qualify for the Graduate Aptitude Test in Engineering (GATE) entrance exam to enrol in a Master's programme.
Electrical and electronics engineering offers extensive career opportunities across various high-paying and rapidly growing industries. Prominent sectors include research and development, automotive, telecommunications, aerospace, and the medical industry. Students pursuing a BTech in Electrical and Electronics Engineering, or BTech EEE full form, are also in demand in the field of robotics. Industries such as manufacturing, education and research, defence, automotive, agriculture, and healthcare offer lucrative and expanding opportunities for skilled robotics engineers. Let us look at some of the potential career prospects in Electrical and Electronics Engineering, or EEE engineering full form:
Electrical and Electronics Engineering presents abundant career opportunities across various industries, driven by the growing demand for skilled professionals adept in power systems, control engineering, and embedded systems. Students pursuing Electrical and Electronics Engineering, or EEE engineering full form, are well-positioned to contribute to sectors ranging from telecommunications to aerospace, leveraging their expertise to advance technologies in renewable energy, automation, and beyond. With structured curricula and rigorous eligibility criteria, EEE programmes prepare students to meet industry challenges and drive innovation in the 21st century. As the global reliance on electronic solutions intensifies, EEE remains at the forefront of technological innovation, offering rewarding career paths and opportunities for impactful contributions to society.

The importance of cybersecurity in the 21st century reached its peak, and it will continue to grow as data theft and cybercrime become more prevalent. Cybersecurity is crucial in ensuring that you are safeguarded from cyberattacks that gain personal information and plant malware into your network.
The Faculty of Engineering and Technology at JAIN (Deemed-to-be University) is mindful of the challenges associated with the computer science and engineering domain. With our M. Tech Cyber Security in Flexible Mode, we have set the groundwork for working towards a safer network in response to industry requests to professionals who are well-trained and equipped with solutions against cybercrime. This unique course from the Faculty of Engineering and Technology gives you the chance to achieve your upskilling goals without interfering with your demanding work and professional commitments.
JU-FET's M. Tech Cyber Security program is an effort to assist students with hectic work schedules efficiently pursue their career goals. Our curriculum is structured to broaden your perspective of cyber security and network security while delving deeply into disciplines like information security principles, risk assessment, policies and procedures, security controls and countermeasures, architecture, and security management.
One among the top cyber security courses in Bangalore, M. Tech in Cyber Security at JAIN (Deemed-to-be University) offers you with one-on-one experience and insights from your peers, experienced guest lecturers, and instructors. It enables you to engage and exchange experiences, learn new concepts, and resolve challenges based on insights, all of whom help you succeed in real-world cybersecurity. While we place an immense portion of emphasis on providing our students with customized learning experiences. Our program additionally believes and emphasizes on continuing your education while advancing your career.
Enrolling in our program grants you swift and exclusive access to the University's collaborative cyber security certifications, which include CompTIA Security+, EC-Council (ECH), EICT, and IIT Kanpur. As a result, you will possess practical understanding of modern network security guidelines and procedures related to cybersecurity as a professional.
The M. Tech in Cybersecurity offers career choices that could assist you advance professionally. Ethical hacker, network security analyst, network security engineer, threat intelligence analyst/engineer, penetration tester, cyber forensic specialist, anti-virus developer, and more represent a few of the roles and cutting-edge cybersecurity vocations it supports. Possessing an M. Tech in Cybersecurity empowers you to apply conceptual knowledge from the top industry specialists to your career. This promotes your advancement in the discipline.
A qualified B.E., B. Tech., or AMIE in Computer Science Engineering, Information Science, Electrical and Electronics, Medical Electronics, Electronics and Telecommunication, Electronics and Instrumentation, or Instrumentation and Control Engineering is a prerequisite to enrol in this course at JAIN (Deemed-to-be University). The candidate must have completed the qualifying exam with at least 50% of the marks45% marks in case of candidates belonging to reserved category).
Professionals employed by MSMEs within a 50 kilometre radius of the Institute, as well as those employed by Central or State organizations, private or public limited companies, and registered industries, are also eligible for the course.
Our eligibility criteria include a minimum of one year of experience in full-time or regular working experience.
We have a dedicated office for inquiries and admissions. Kindly visit the JGI Knowledge Campus, # 44/4, District Fund Road, Jayanagar 9th Block Campus, Bangalore - 560069. For additional information, please contact us at +91 80 46650130 or visit our website at https://set.jainuniversity.ac.in/academics/computer-science-engineering/mtech-cyber-security-flexible-mode.

As digital presence becomes ubiquitous across all organisations and businesses, the IT sector emerges as one of the fastest-growing fields among all sectors. This surge in demand has directly led to an increased need for computer science engineers and programmers. According to the Bureau of Labour Statistics (BLS), job opportunities in software development, a key field within applied computer science, are projected to grow by 22% by 2030. This growth rate far surpasses the national average for all professions, which stands at 8%. Besides this, the Indian IT industry is projected to achieve a market size of $300 billion by 2025, resulting in a significant demand for skilled Computer Science Engineering (CSE) professionals in the coming years. Government initiatives such as Digital India are further fuelling job growth in this sector. Moreover, the growing demand in areas like artificial intelligence and machine learning has opened up specialised career opportunities in areas like block chain, data engineering, and cyber security, among others. Let us learn more about Computer Science Engineering, in depth:
The full form of CSE is Computer Science Engineering. Computer Science Engineering encompasses a curriculum dedicated to designing, developing, and managing technology and hardware-centric data systems. This discipline of engineering focuses on topics related to computation, such as programming languages, algorithm analysis, software development, hardware design, and programme design. Both undergraduate and postgraduate programmes in Computer Science Engineering are offered in this branch of engineering. A Bachelor of Technology (BTech) in Computer Science or CSE full form in engineering is generally offered at the undergraduate level, while a Master of Technology (MTech) programme is offered at the post-graduate level. Key details about CSE are summarised below:
|
Full Form of CSE |
Computer Science Engineering |
|
Courses offered |
|
|
Duration |
|
|
CSE Entrance Exam |
JEE Main, JEE Advanced and COMEDK |
Computer Science Engineering, or CSE full form in engineering, encompasses the theory of computation and the development of computational systems. In this programme, students learn to design and implement hardware and software for computers, along with gaining knowledge of communication systems and related devices. A BTech in Computer Science Engineering, or BTech CSE full form, typically spans four years, further divided into eight semesters. This undergraduate degree covers essential topics such as programming languages, software design, and computer hardware. These subjects provide students with deep insights into technology and its practical applications in engineering. Throughout the BTech in Computer Science Engineering, or BTech CSE full form course, students are encouraged to innovate and develop their skills independently. Successful completion of the programme requires students to achieve a minimum credit score and undertake a significant project in their final year. The core topics covered in this curriculum are:
The programme teaches essential technical skills, such as proficiency in programming languages such as C++, Java, Python, and others. This exposure in Computer Science Engineering, or CSE full form in engineering, can enable students to develop robust software solutions and adapt to industry-specific needs. Data analysis capabilities are crucial for interpreting complex datasets and deriving actionable insights, while expertise in technical writing ensures effective communication of project details and documentation within IT teams. Software development skills encompass the entire lifecycle of application creation, from coding to testing and troubleshooting, ensuring reliable and efficient software performance. Moreover, the curriculum also hones students’ proficiency in cloud computing skills—spanning security, data migration, and API integration. On the soft skills front, students master the art of effective time management that helps them meet project deadlines and deliver quality results consistently. Students also develop collaboration skills that are critical for teamwork and fostering a productive environment where innovative ideas can flourish. Lastly, excellent communication skills are taught in the BTech in Computer Science Engineering, or BTech CSE full form course, for articulating technical concepts, facilitating smooth project execution, and aligning with business goals.
The eligibility criteria for CSE courses differ based on the level of the study. We have listed the basic eligibility criteria required to pursue the CSE programme:
|
Level of Study |
Eligibility Criteria |
Entrance Exam |
|
Diploma in CSE |
Candidates must have passed the Class 10th exam from a recognised board with at least 55% marks. |
Diploma Entrance Exam |
|
BTech in CSE |
Candidates must have completed the Class 12 exam from a recognised board with Physics, Chemistry, and Mathematics as core subjects. Additionally, candidates should have achieved a minimum aggregate of 60% in these subjects combined.
|
|
|
MTech in CSE |
Candidates should hold a BTech degree in the same specialisation with a minimum 50% percentage. |
Graduate Aptitude Test in Engineering (GATE) in Computer Science and Information Technology (CS) |
|
PhD in CSE |
Candidates must have a Master’s degree in the field of Computer Science or related discipline with valid aggregate marks as specified by the institute. |
|
Computer Science Engineering, or CSE full form in engineering, presents a myriad of career opportunities across diverse sectors. Students in this field can specialise in areas such as information security, cyber security and forensics, and robotics process automation. Another burgeoning field is cloud technology, which involves managing server networks for online data storage and maintenance. Here are some potential career paths that students can pursue after graduation in Computer Science Engineering, or CSE full form in engineering:
The field of CSE is experiencing unprecedented growth, driven by the increasing reliance on technology across industries worldwide. CSE programmes equip students with essential skills in programming languages, software engineering, hardware design, and data analysis, preparing them for roles that span from software developers to AI engineers. By combining technical expertise with innovation and adaptability, CSE students are well-positioned to lead and innovate in the growing field of technology. Their ability to navigate evolving technologies ensures a rewarding and impactful career journey ahead in fields such as cloud computing, cybersecurity, and machine learning. Overall, pursuing a career in Computer Science Engineering not only promises professional growth but also offers opportunities to shape the future of technology-driven societies globally.

The recent 2024 Engineering Job Market Report by the IET highlights a 20% year-over-year increase in engineering jobs, outpacing other sectors. This growth is driven by technological innovations and the need for infrastructure modernisation across industries such as renewable energy and advanced robotics. Engineers play a crucial role in today's world, not just filling jobs but leading significant innovations and enhancing operational efficiency. Their contributions support both new and established companies, promoting growth and stability in an interconnected digital era.
The demand for skilled engineering professionals is more competitive than ever, with organisations worldwide vying to attract and retain these experts due to their critical role in key projects. According to the Global Engineering Services Outlook, engineering salaries have seen an average increase of 15% in the past year, reflecting the high value of specialised skills. Engineering careers are also noted for their resilience. Data from the National Bureau of Economic Research shows that engineering positions are 35% less likely to be affected by economic downturns compared to other jobs. This stability, combined with significant career advancement opportunities, makes engineering a highly attractive field. Pursuing a Mtech degree full form; Master of Technology allows students to maximise their engineering knowledge and specialise in a specific field. Prestigious private engineering institutes emphasise developing advanced skills, enabling students to become specialists. Multinational companies and startups often prefer candidates with a Master of Technology, or MTech full-form degree, for varied career roles. Reputable industries, including international giants like Microsoft and Google, favour job candidates with an MTech degree. Let us learn more about MTech in depth:
The full form of MTech is Master of Technology. It is a postgraduate degree programme that enhances and deepens the technical knowledge and skills acquired during a Bachelor of Technology (B.Tech.) or Bachelor of Engineering (B.E.) degree. This programme allows students to specialise in specific engineering or technology fields, such as computer science, electrical engineering, mechanical engineering, or civil engineering.
There is no requirement for work experience to pursue a full-time Master of Technology, or MTech full form course, as admission is typically based on entrance exams or BTech degree marks. However, for part-time MTech courses, some universities require candidates to have relevant full-time work experience. This requirement varies, with some colleges allowing fresh BTech graduates to enrol in MTech programmes designed for working professionals. Key details are summarised below:
|
Full Form of MTech |
Master of Technology |
|
Level of Education |
Postgraduate |
|
Duration |
4 years |
|
Admission Process |
Merit-based and entrance examinations |
Pursuing an MTech degree offers numerous benefits that can significantly enhance your career prospects and earning potential.
The Master of Technology, or MTech degree full form curriculum typically consists of a mix of core and elective courses. Core courses provide a strong foundation in engineering fundamentals, covering topics like engineering mathematics, engineering mechanics, thermodynamics, fluid mechanics, heat transfer, and machine design. Elective courses enable students to specialise in areas of interest such as computer-aided engineering, robotics, control systems, signal processing, data structures and algorithms, software engineering, and information security. In the first year, students focus on core subjects related to their specialisation, forming the basis of their expertise. Students can also select elective subjects aligned with their interests and career goals, along with practical sessions and laboratory work that offer hands-on experience. The second year emphasises specialised subjects that dive deeper into the chosen area of expertise, equipping students with advanced skills for industry roles. Additionally, many MTech programmes require a research project or thesis in the final year, allowing students to contribute to their field and develop research competencies. Some popular specialisations offered in the field of Master of Technology, or MTech degree full form, are as follows:
Computer Science and Engineering
Electronics and Communication Engineering
To be eligible for MTech programmes, candidates must have a bachelor's degree in engineering or technology (B.E. or B.Tech.) with a minimum aggregate score of 55% to 60% from a recognised university or institution. Many universities also require candidates to qualify for national-level entrance exams such as the GATE (Graduate Aptitude Test in Engineering), JEST (Joint Entrance Screening Test), NET (National Eligibility Test), or institution-specific entrance exams. Additionally, candidates who have completed a 5-year programme in science or applied sciences are eligible for MTech courses. Admission is generally based on the rank obtained in the entrance test conducted for MTech programmes.
Engineering has long been a popular and widely chosen career path. Students with a MTech degree find employment across various industries, such as IT, automotive, aerospace, manufacturing, energy, and healthcare, based on their area of specialisation. Many MTech programmes also provide research opportunities, equipping students for careers in R&D laboratories, government institutions, and academic research. Some of the promising career avenues in the field of a Master of Technology, or MTech degree full form are as follows:
Beyond the traditional MTech programme, engineers have several upskilling opportunities to enhance their knowledge and skills. These programmes are shorter in duration and focus on emerging technologies such as artificial intelligence, big data analytics, cloud computing, and the Internet of Things (IoT). After completing an MTech degree, students can consider various certifications to boost their skills and career prospects. Some notable certifications include:
The competitive demand for engineering talent underscores the sector's resilience and offers abundant prospects for career advancement. Pursuing a Master of Technology (MTech) not only deepens technical expertise but also positions students for diverse and rewarding career paths in leading global industries. MTech programmes provide a structured pathway for students to augment their engineering acumen, preparing them for leadership roles and interdisciplinary careers in emerging fields such as artificial intelligence, data science, and cybersecurity. The emphasis on practical skills and research initiatives equips students to address complex challenges and drive innovation in the 21st century economy. In essence, investing in an MTech not only enhances career prospects but also cultivates a mindset of continuous learning and adaptability. As the demand for skilled engineers continues to rise, pursuing an MTech emerges as a strategic choice to excel in today's competitive engineering environment.
India boasts over 7,000 engineering colleges, solidifying its position as a global leader in engineering education. According to The Hindu, the country anticipates 12 million engineering job openings within the next five years, marking a 300% increase in hiring in the next decade. Nationally, engineering opportunities are projected to grow by 7% by 2026, as reported by the Bureau of Labour Statistics. The surge in demand for engineers can be largely attributed to rapid technological advancements in recent years. As new technologies and industries emerge, the future of engineering is continually evolving. Fields such as renewable energy, artificial intelligence, and biotechnology are expected to grow in the coming years. Additionally, traditional fields like civil and mechanical engineering are experiencing a resurgence with a focus on sustainability and efficiency. Engineers of the future will need to be adaptable, innovative, and collaborative to address the complex challenges of the 21st century.
Pursuing a BTech degree full form; Bachelor of Technology is highly sought-after due to the competitive salaries and opportunities offered across various sectors. BTech programmes emphasise practical learning through internships, industrial projects, and lab work, providing students with valuable industry experience. Students with a BTech degree are poised to drive creativity and innovation in the dynamic technology sector. They can leverage their skills and technical knowledge to develop groundbreaking technologies and solve real-world problems. Let us learn more about BTech programmes in detail:
The full form of BTech stands for Bachelor of Technology. BTech is a comprehensive undergraduate programme offered by recognised universities and colleges. It focuses on engineering and technology disciplines, making it highly sought-after across numerous educational institutions in India. This professional degree equips students with practical knowledge of engineering principles applicable across various specialties within the technology sector. Students have the flexibility to choose specialised streams aligned with their interests and career goals. BTech emphasises skill development, offered by both private and public institutions. Key details about the BTech degree are summarised below:
|
Full Form of BTech |
Bachelor of Technology |
|
Level of Education |
Undergraduate degree |
|
Introduced by |
University of Mysore in 1957 |
|
Duration |
Four Years |
Candidates aspiring to pursue a Bachelor of Technology, or B.Tech full form must meet specific eligibility criteria, as outlined below:
Additionally, individual universities or colleges may have specific admission rules that students must fulfill. Admission to most BTech programmes is primarily based on performance in entrance exams. National-level exams like the Joint Entrance Examination (JEE) Mains are crucial for securing admission to government colleges nationwide. Similarly, private universities conduct similar structured exams to select eligible candidates. Aspiring students typically take these entrance tests after completing their Class 12 examinations. Moreover, students who have pursued a B.Sc. or Diploma in Engineering may qualify for lateral entry directly into the second year of the BTech programme.
In India, Bachelor of Technology, or BTech full form admissions are determined through various national and state-level entrance tests. These tests are open to students who have completed their higher secondary education with Physics, Chemistry, and Mathematics as core subjects. While some universities compile their merit lists based on the Joint Entrance Examination (JEE), others conduct separate institutional exams to select candidates. Popular entrance exams like West Bengal Joint Entrance Examination (WBJEE), Vellore Institute of Technology Engineering Entrance Examination (VITEEE), Birla Institute of Technology and Science Admission Test (BITSAT), Consortium of Medical, Engineering and Dental Colleges of Karnataka (ComedK), and others play a crucial role in admission to different universities and colleges. It is advisable for Bachelor of Technology, or BTech degree full form aspirants to thoroughly prepare for these entrance exams in advance.
BTech programmes cover a wide range of engineering disciplines, from traditional fields such as Computer Science Engineering (CSE), Civil Engineering, and Mechanical Engineering to emerging disciplines like Artificial Intelligence (AI), Machine Learning (ML), and Robotics. Recently, BTech programmes have been integrating advanced technologies like AI and machine learning into their curriculum to better equip students for today's dynamic job market. As a result, students now have the option to specialise in emerging fields such as AI and CSE within their Bachelor of Technology, or BTech degree full form courses. Over the past few years, BTech programmes in India have seen a consistent Compound Annual Growth Rate (CAGR) of approximately 5%. Many of these programmes are accredited by the National Board of Accreditation (NBA) and the All India Council for Technical Education (AICTE), ensuring they maintain high-quality standards in their curriculum and teaching methodologies. The different types of specialisations offered in the Bachelor of Technology, or BTech degree full form courses are as follows:
A proficient engineer needs a blend of both technical expertise and interpersonal skills to excel in their role. Technical skills are acquired through theoretical knowledge gained during a four-year BTech programme and practical experience gained through internships in various industries. Here are some essential skills taught in a BTech degree:
The BTech degree offers a wide array of career opportunities both in India and abroad. With the economy soaring up over recent decades, there has been a consistent growth in technology industries and various other sectors, providing students with diverse career options. A BTech degree not only exposes students to valuable experiences but also equips them with skills and knowledge essential for various professional fields. Students have opportunities to work for multinational corporations like Microsoft, Google, and Intel, as well as emerging startups. Here are some promising career pathways that students can pursue after graduating with a Bachelor of Technology, or BTech degree, in full form:
The Bachelor of Technology (BTech) degree is highly esteemed for its competitive salaries and diverse career prospects across sectors. With specialisations ranging from Computer Science Engineering to Robotics and beyond, B.Tech prepares students to tackle the complex challenges of the 21st century. Accredited by bodies like the National Board of Accreditation (NBA) and the All India Council for Technical Education (AICTE), these programmes ensure high-quality education aligned with industry standards. Skills such as problem-solving, information technology, attention to detail, and effective communication are crucial in preparing engineers to navigate and excel in their professional fields. The future of engineering in India looks promising, with BTech students poised to lead the charge in shaping a sustainable and technologically advanced economy.

The term "software engineer" is broad and encompasses various technical roles, including web development, cloud computing, mobile application creation, and video game development. While both web development and software engineering involve creating software, they require different skill sets, education levels, and work responsibilities. Web developers specialise in websites, while software engineers work on a wider range of software products across various platforms. Although these fields share similarities, they are distinct disciplines with unique objectives. Web developers create programmes and websites visible only on browsers, while software engineers develop cross-platform tools. Thus, web development specifically refers to creating websites and web applications, whereas software engineering covers a broader range of software development tasks. Let us try to understand the key differences between these two disciplines:
Software engineering course requires a unique blend of technical expertise and soft skills to excel. On the technical side, mastering coding languages like Python, Java, and C/C++, along with understanding data structures and algorithms, is crucial. Additionally, proficiency in software testing and debugging is essential, as it ensures the reliability and functionality of software products. Object-oriented design principles, emphasising flexibility and reusability, further enhance a software engineer's skill set. Additionally, soft skills are equally vital for success in this field. Effective communication skills enable software engineers to collaborate with diverse teams and stakeholders, facilitating clear and concise exchanges of ideas. Being a team player is essential, as software development often involves working collaboratively towards common goals. Problem-solving abilities are invaluable for identifying and addressing challenges throughout the development process, while attention to detail ensures the accuracy and quality of software solutions.
Web development necessitates a diverse skill set, combining technical expertise with soft skills to craft effective and user-friendly websites. A proficient web developer should be adept at front-end coding, mastering HTML, CSS, and JavaScript to construct the user interface of websites and ensure compatibility across various devices. Additionally, familiarity with version control systems like Git facilitates efficient collaboration and code management within development teams. Understanding responsive design principles is essential for creating websites that seamlessly adapt to different screen sizes and devices, thereby enhancing the user experience and search engine optimisation (SEO) performance. Moreover, proficiency in back-end web programming languages such as PHP, Java, Ruby, C#, and Python enables developers to build server-side applications and integrate databases effectively. Effective communication skills are crucial for articulating technical concepts to non-technical stakeholders, fostering collaboration, and problem-solving. Additionally, creativity enables developers to devise innovative solutions and enhance the functionality and design of web applications.
Software engineering projects encompass a wide array of types, each tailored to meet specific objectives and requirements. One prevalent type is web development projects, involving the creation of websites, web applications, and online platforms. These projects utilise languages like HTML, CSS, JavaScript, and frameworks such as React or Angular. Another common type is mobile app development projects, which focus on creating applications for smartphones and tablets using languages like Swift or Kotlin. Enterprise software projects are also significant, involving the development of solutions for businesses to streamline processes, such as CRM systems or ERP software. Game development projects, embedded systems projects, and machine learning and AI projects are further examples, each requiring specialised knowledge and skills. Open-source projects, research and development projects, quality assurance and testing projects, and legacy system modernisation projects round out the diverse landscape of software engineering endeavours, each offering unique challenges and opportunities for innovation.
Web development projects encompass a variety of tasks, ranging from crafting basic static pages to developing intricate web applications such as social networking services. One prevalent type is e-commerce website development, focused on creating online platforms for buying and selling goods or services. Content Management System (CMS) development is another common type, involving the creation of platforms like WordPress or Joomla for managing digital content. Additionally, there are web application development projects that involve building dynamic and interactive applications accessible through web browsers. Portfolio website development focuses on creating websites to showcase individuals' or businesses' work and accomplishments. Moreover, there are Blogging Platform Development projects that aim to create platforms like Medium or Blogger for publishing and sharing written content. Custom Web Solutions Development involves building bespoke web applications tailored to specific client needs. Landing page development projects focus on creating single-page websites designed to capture leads or promote specific products or services.
Software engineering careers entail designing, developing, testing, and maintaining software by applying engineering principles and practices. Responsibilities encompass a wide range of activities, from gathering requirements and system design to ensuring quality assurance. The scope of software engineering spans across various domains, including operating systems, video games, middleware, and more. Here are some promising career options in the field of software engineering:
Conversely, web developers design and build websites and web-based applications for clients. As businesses increasingly digitise and seek an online presence, the demand for skilled web developers is rising. Careers in web development span numerous industries, including healthcare, business, and education. Opportunities exist in diverse fields such as graphic design, database administration, and cybersecurity. Here are some promising career options in the field of web development:
While both software engineering and web development involve creating software, they are distinct disciplines with unique objectives, skill sets, and responsibilities. Software engineers work on a wide range of software products across various platforms, applying engineering principles to design, develop, test, and maintain complex systems such as operating systems, middleware, and video games. On the other hand, web developers focus specifically on building and maintaining websites and web applications, utilising skills in front-end and back-end development, responsive design, and SEO. Understanding these differences is crucial for anyone pursuing a career in one of these fields. Software engineers require a broader range of technical skills, including proficiency in multiple programming languages and software testing, as well as strong problem-solving and communication abilities. Web developers, while also needing technical expertise, particularly in front-end technologies like HTML, CSS, and JavaScript, must focus on creating user-friendly and responsive designs. Ultimately, both careers offer diverse opportunities across various industries, and the choice between them depends on one's interests, skills, and career goals.

The global civil engineering market is projected to grow at a compound annual growth rate (CAGR) of 5.9% from 2023 to 2030. This growth is driven by the increasing number of infrastructure and capital projects, supported by rising disposable incomes in emerging economies. Despite the challenges posed by the COVID-19 pandemic, innovative advancements and expanding investments in construction projects have fuelled the growth of the structural design sector. The planning and design service segment is expected to experience the fastest growth, with a CAGR of 6.2%. Additionally, increasing renovation activities and the installation of energy-efficient products contribute to market expansion.
On the other hand, the global transportation infrastructure market is forecast to grow significantly between 2024 and 2031, driven by strategies adopted by key players. Transport infrastructure, including roads, railways, ports, and airports, plays a crucial role in social and economic development by connecting individuals to opportunities and facilitating the global supply chain. Working in transportation offers an exciting career at the intersection of town planning, civil engineering, and architecture. With increasing demand for engineers and numerous upcoming projects, both civil and transportation engineering provide opportunities for fresh talent to make a meaningful impact on society. Let us explore these two engineering disciplines in depth to help make an informed career choice:
Civil engineering applies physical and scientific principles to design, develop, and maintain both constructed and natural environments. This field covers a wide range of infrastructure, including airports, bridges, buildings, canals, dams, pipelines, power plants, railways, roads, and sewage systems. It is traditionally divided into several sub-disciplines and is recognised as the second-oldest engineering field after military engineering. Civil engineering projects can be found in both the public sector, ranging from municipal public works to federal government agencies, and in the private sector, from small local firms to large global companies.
Transportation engineering, a subset of civil engineering, focuses on the planning, design, operation, and maintenance of transportation systems to create smart, safe, and liveable communities. This field encompasses any system that moves people and goods, including highways, railways, oil pipelines, public transport systems, traffic control systems, automated transport systems, and even space transport systems. Transportation engineers gather data on local populations, travel patterns, socioeconomic factors, laws, ordinances, and financial resources. These professionals use this information along with decision-support tools to develop, design, and implement transportation projects that consider various performance metrics.
Urban planning involves creating frameworks and strategies to guide the sustainable development and growth of cities. Civil engineers play a pivotal role in this process by providing technical expertise and ensuring the feasibility of infrastructure projects. They collaborate with architects, urban planners, and decision-makers to develop infrastructure that meets the current and future needs of urban populations. Access to clean water and proper sanitation facilities is fundamental to public health and well-being. Civil engineers design and implement water supply systems, wastewater treatment plants, stormwater management systems, and sewage networks. They ensure efficient water distribution, proper waste disposal, and environmental protection. In urban areas, buildings and infrastructure must be designed to withstand various environmental factors and ensure occupant safety. Civil engineers specialising in structural engineering analyse material behaviour, design structural systems, and ensure compliance with safety codes and regulations.
Transportation is a cornerstone of functional urban regions. The recent growth of suburban areas is largely due to improved transportation facilities, which have enabled the expansion of built-up areas in cities. Efficient transport networks have restructured urban forms, allowing people in urban areas to travel safely and promptly from one place to another. The interconnection between cities, their hinterlands, and metropolitan areas relies heavily on an efficient transportation system. Such a system facilitates economic and social mobility, accelerating urbanisation and economic growth. Effective transportation networks are vital for the smooth functioning of urban areas. Roads, highways, bridges, and mass transit systems are essential components that transportation engineers design and build. These engineers consider factors such as traffic flow, safety, and sustainability to create efficient transportation networks that connect different parts of the city.
Civil and transportation engineering is essential for infrastructure development, shaping the way our cities and communities function. However, with environmental challenges like climate change and resource depletion, it is crucial for the field to adopt sustainable practices. Sustainability in civil and transportation engineering considers long-term environmental, social, and economic impacts. There are some sustainable solutions that can be incorporated into civil and transportation engineering:
Green building design focuses on energy efficiency, reduced resource consumption, and minimal environmental impact. Features like energy-efficient lighting, renewable energy sources (e.g., solar panels), and natural ventilation systems are incorporated to reduce a building's carbon footprint and operational costs.
Choosing sustainable construction materials is crucial for project sustainability. Civil engineers are increasingly using eco-friendly materials like recycled steel, reclaimed wood, and low-impact concrete. These materials lessen the environmental impact of construction and promote responsible resource management.
Efficient resource management involves minimising waste, optimising resource use, and recycling materials whenever possible. Construction sites are adopting practices like on-site material sorting and recycling to reduce landfill waste. Technologies like Building Information Modelling (BIM) help engineers plan and execute projects with greater precision, reducing material waste.
Transportation engineers are key to creating sustainable transportation solutions. They design and implement public transit systems, pedestrian-friendly urban environments, and cycling infrastructure. By promoting alternatives to private vehicles, such as electric buses and light rail systems, transportation engineers help reduce traffic congestion and greenhouse gas emissions.
Sustainable water management is vital for civil engineering, especially with increasing water scarcity and extreme weather events. Engineers design innovative stormwater management systems to capture and reuse rainwater and upgrade wastewater treatment plants to produce reclaimed water for non-potable uses, conserving freshwater resources.
With climate change causing more frequent and severe weather events, civil engineers focus on building resilient infrastructure. This involves designing structures that can withstand extreme conditions like hurricanes, floods, and earthquakes. Resilient infrastructure protects lives and property and reduces the need for costly repairs and reconstruction after disasters.
The global civil and transportation engineering sectors are experiencing significant growth, driven by increasing infrastructure projects and strategic investments. Despite the challenges posed by the COVID-19 pandemic, both sectors have demonstrated resilience and innovation, leading to sustained development. Civil engineering plays a crucial role in urban development, while transportation engineering focuses on creating efficient and safe transportation systems to support economic and social mobility. As demand for infrastructure continues to rise, there are abundant opportunities for professionals in both civil and transportation engineering fields to contribute to meaningful projects. Moreover, the adoption of sustainable practices is paramount to addressing environmental challenges and ensuring long-term resilience and sustainability in infrastructure development. By incorporating sustainable strategies, civil and transportation engineers can play a pivotal role in creating more liveable, resilient, and environmentally friendly cities for future generations.

India has been home to remarkable astronauts such as Rakesh Sharma and Kalpana Chawla, whose influence extends to millions of young Indians aspiring for careers in aerospace or aeronautical engineering. Their legacies serve as beacons of inspiration for young individuals, fostering a keen interest in astronomy and space exploration. Additionally, ISRO's Chandrayaan mission, credited with the groundbreaking discovery of water on the moon, continues to shatter barriers and establish new benchmarks. Beyond its immediate scientific impact, this mission holds the potential to ignite a new wave of enthusiasm among young minds, propelling them towards careers in space exploration and scientific inquiry.
However, due to a lack of clarity, individuals often find themselves making erroneous decisions or pursuing alternative paths. Many are uncertain about the nuances distinguishing aerospace and aeronautical engineering. While both fields involve the design of aircraft, missiles, and related vehicles, there are distinct differences. Aerospace engineering serves as the overarching discipline, focusing on the design, testing, and production of aircraft, spacecraft, and associated systems. It encompasses both atmospheric and space flight, with astronautical engineering constituting a subset specialising in craft operating within and beyond Earth's atmosphere. Today, we shall learn more about these two engineering disciplines in depth to make an informed career choice.
Aerospace Engineering, a specialised branch of engineering, furnishes students with the expertise to conceptualise, manufacture, and uphold spacecraft, missiles, and weapon systems. The curriculum of a Bachelor of Technology (B.Tech.) in Aerospace Engineering not only imparts foundational engineering theories but also emphasises their practical application. Upon enrolment in the B.Tech degree, students dive deep into disciplines such as engineering mechanics, thermodynamics, fluid mechanics, heat transfer, aerodynamics, kinematics, propulsion, measurements and controls, and design. This B.Tech. programme encompasses the science and engineering of aircraft and spacecraft, encompassing aeroplanes, space shuttles, and other aerial vehicles operating both within and beyond Earth's atmosphere. The syllabus covers a wide array of subjects, including elements of aeronautics, aero-fluid mechanics, mechanics of solids, aircraft component drawing, machines and mechanisms, aircraft systems and instruments, air-breathing propulsion, and others.
Aerospace Research Engineering stands at the forefront of innovation, dedicated to advancing the efficiency, safety, and sustainability of aerospace systems. Within this specialised domain of aeronautical engineering, aerospace research engineers are instrumental in conducting groundbreaking research and development, pushing the boundaries of human flight and space exploration. The key research focus areas are as follows:
Astronautical engineering is a specialised branch of aerospace engineering dedicated to the design, development, and testing of spacecraft and rockets for exploration, communication, and various applications. This field emphasises the structural design and analysis of aircraft and spacecraft components, as well as the materials used in their construction. A B.Tech in Astronautical Engineering imparts a profound understanding of engineering principles, coupled with creative problem-solving skills to innovate solutions for complex engineering challenges. The curriculum provides a robust foundation in engineering, mathematics, and science, empowering students to analyse and design future aircraft and spacecraft. Core subjects in the astronautical engineering programme cover engineering mathematics, physics, chemistry, engineering graphics, mechanical engineering basics, environmental studies, and others to ensure a comprehensive understanding of key concepts and hands-on experience from the outset of the programme.
Astronautical engineering uses novel propulsion methods such as ion propulsion, solar sails, or nuclear propulsion to enhance our ability to explore space efficiently and effectively. Research in this area focuses on developing advanced algorithms and systems for spacecraft attitude control, trajectory optimisation, and autonomous navigation. Exploring these research areas is crucial for precision missions and operations. The key research focus areas are as follows:
Aerospace engineering enables human endeavours such as piloting aeroplanes, launching satellites, and advancing defence technology. Embarking on a career in aerospace engineering necessitates a robust foundation in mathematics and science, equipping students with the requisite knowledge and skills to contribute to aircraft and spacecraft design and operation. Aerospace engineering students play a pivotal role within aerospace companies' research and development divisions, fostering innovation. Collaborating with governmental entities such as NASA, ISRO, ESA, and defence research organisations, aerospace engineering students explore space and aviation technologies. Here are some key career paths that students can pursue after the completion of their degree:
Astronautical engineering is responsible for crafting and refining a wide array of spacefaring technologies, including rockets, satellites, planetary probes, and spacecraft capsules. These professionals work on meticulous analysis and troubleshooting to ensure the efficiency and safety of these designs. The innovative ideas generated within this field have a profound impact on both space and terrestrial travel. Leveraging their technical expertise, these engineers oversee the entire lifecycle of spacecraft, from initial design to testing and ongoing upgrades. Although distinct from astronauts, many astronauts have backgrounds in astronautical engineering. Here are some key career paths that students can pursue after the completion of their degree:
Space exploration yields a plethora of advantages for future generations, both tangible and intangible. Tangible benefits encompass the advancement of scientific understanding, the cultivation of innovative technologies, the emergence of fresh industries and employment avenues, and enhancements to life quality on Earth. For instance, space exploration unravels mysteries like the solar system's origins, confirms the presence of water on Mars, and hints at extraterrestrial life. It has also led to practical breakthroughs like satellite navigation, remote sensing, telemedicine, and renewable energy solutions. Furthermore, space exploration fosters global collaboration, economic prosperity, and educational enrichment. Conversely, some benefits are less quantifiable but no less significant. These intangible merits encompass the nurturing of curiosity, creativity, and ingenuity in young engineers. Space exploration also fosters the cultivation of a planetary perspective, environmental stewardship, and the elevation of human aspirations. Notably, space exploration ignites passion in countless students, propelling them towards careers in STEM fields as well as in the arts, humanities, and social sciences. It also encourages critical thinking, collaboration, and ethical contemplation regarding the challenges and opportunities that lie ahead.
Aerospace engineering encompasses the design and maintenance of aircraft and spacecraft, whereas astronautical engineering focuses specifically on spacecraft for exploration beyond Earth's atmosphere. Both disciplines offer extensive opportunities for research and career advancement. Aerospace engineering explores areas like hypersonic flight, electrification of aircraft, and space tourism, while astronautical engineering explores propulsion systems, spacecraft design, and space colonisation. Ultimately, space exploration offers myriad tangible and intangible benefits, ranging from technological advancements and economic growth to the cultivation of curiosity, creativity, and a global perspective among aspiring engineers. Embracing these opportunities can propel future generations towards fulfilling careers.
Computer Science Engineering (CSE) and Information Technology Engineering (ITE) play crucial roles in developing the modern digital landscape. Although there are similarities between the two fields, their applications, areas of emphasis, and the skill sets they teach prospective engineers are different.
The more expansive of the two is computer science engineering, which includes a thorough grasp of theoretical ideas, programming languages, data structures, and algorithms. It dives deeply into the fundamentals of computers, allowing students to take on challenging issues and come up with creative solutions. Information technology engineering, on the other hand, is more application-focused and emphasises the real-world use of computer technology to solve problems. Effective management, design, and implementation of databases, networks, and information systems are the main concerns of ITE specialists.
The course duration of a degree in computer science engineeringis four years. These four years are divided into eight semesters where different aspects of computers, such as computer programming, operating systems, hardware and software, among other concepts, are covered.
A degree in information technology engineering also takes four years to complete. Over eight semesters cover the complete software development cycle, database system, IT application development, and other technical skills.
Computer science engineering is a diverse field covering many topics, providing a solid foundation in theory and practical applications. Some of the subjects included in CSE are:
Information technology engineering is a specialised domain that applies computer systems for storing, studying and transmitting data. It has a more focused curriculum, emphasising the practical application of technology in a business environment. To meet the demands of the ever-growing IT industry both technically as well as academically, some of the subjects that are covered in this engineering field are:
CSE graduates are well-equipped for diverse roles in cutting-edge technology. Opportunities in artificial intelligence and machine learning allow them to shape the future of technology. Data science roles enable these professionals to analyse and derive insights from vast datasets. CSE opens doors to dynamic fields, fostering creativity and problem-solving skills. Graduates in CSE possess a strong foundation in both theoretical and practical aspects of computing. Here are some career opportunities that await CSE graduates:
Software developersdesign, code, test, and maintain software applications across various platforms. They may specialise in web, mobile app, or system software development.
Data scientistsanalyse large datasets, derive meaningful insights, and contribute to data-driven decision-making processes.
Machine Learning engineersdelve into creating algorithms and models that enable machines to learn and make intelligent decisions.
Cybersecurity analystsplay a crucial role in securing systems and networks by implementing measures to protect against potential breaches and ensure data integrity.
Database administratorsmanage databases, ensuring efficient data storage, retrieval, and organisation. They play a vital role in maintaining data integrity and optimising database performance.
Full-stack developerswork on all aspects of software applications, from user interface design to server-side scripting.
IT engineers play a crucial role in managing and optimising technology for businesses. They contribute significantly to businesses' technological success and resilience. IT professionals deal with the management and implementation of computer systems and networks and ensure the seamless functioning of organisational infrastructure, making them essential contributors to the efficiency and success of businesses. Here are some career opportunities for IT graduates:
Network administratorsimplement, manage, and maintain an organisation's communication infrastructure, including routers, switches, and firewalls.
System administratorsmanage and maintain computer systems, ensuring their smooth operation. They are responsible for software installations, system updates, and troubleshooting.
IT consultantsadvise businesses on utilising technology to meet their goals. They assess existing IT infrastructure, recommend improvements, and help implement solutions.
IT project managersoversee the planning, execution, and completion of technology projects by coordinating with teams, managing budgets, and ensuring that projects align with organisational objectives.
IT support specialistsassist end-users by troubleshooting hardware and software issues. They may work in help desks, responding to user inquiries and resolving technical problems.
Both CSE and IT offer dynamic career paths with ample opportunities for growth and specialisation. Ultimately, the choice between Computer Science Engineering and Information Technology Engineering depends on individual interests, career goals, and preferred skill sets. CSE offers a broader and more theoretical foundation, while ITE provides practical skills for managing and implementing IT solutions. Both fields are integral to the ever-evolving tech industry, ensuring many opportunities for aspiring engineers with diverse interests and aspirations.

Chemical Engineering and Petrochemical Engineering are closely related fields that share fundamental principles but differ in focus and application. Both disciplines play crucial roles in processing and producing chemicals, fuels, and various industrial products.
Chemical engineering is a vast discipline that uses engineering concepts to design, develop, and operate processes and systems for large-scale production. Chemical engineers deal with various materials, such as chemicals, pharmaceutics, food, and materials. They emphasise a broad range of areas where chemical processes are involved, extending beyond the petrochemical industry.
Conversely, petrochemical engineering is a highly specialised branch of chemical engineering that focuses on the manufacturing and handling of petrochemicals. The extraction of crude oil, its refinement into useful products, and the subsequent processing of these products into numerous chemical derivatives are the areas in which petrochemical engineers specialise. It is primarily concerned with producing and processing chemicals from natural gas, petroleum, and their by-products.
The chemical engineering full-time undergraduate programme spans four years, usually about eight semesters. After completing the undergraduate degree, some students may pursue further education through master's or doctoral programmes, which can take an additional two to six years.
The petrochemical engineering undergraduate course is also a four-year commitment that teaches all about crude oil refinement, extracting crude oil using cutting-edge technology, heat transfer operation, and solid-fluid operations, among other things. Advanced degrees, such as master's or doctoral programmes, can add another two to six years of study.
Just like many other engineering disciplines, chemical engineering is also divided into practical, theory and assignments designed to provide a strong foundation in mathematics, physics, chemistry, and engineering principles. Students are taught how to link engineering to chemistry principles to take care of the production and use of chemicals efficiently. The programme acquaints students with a detailed study of different theories, operations and developments carried out in chemical plants, the equipment used in chemical engineering processes, and the management skills needed to be a successful engineer. Some subjects that are taught in chemical engineering include:
Petrochemical engineering, being a specialised branch of chemical engineering, focuses specifically on the processes involved in the production of petrochemicals. The curriculum includes core chemical engineering subjects but places a greater emphasis on topics related to petroleum refining, petrochemical production, and the utilisation of hydrocarbons. There are some specific areas of focus in petrochemical engineering, such as:
The primary responsibility of a chemical engineer is to design, conceive and troubleshoot processes for producing chemicals or fuels, conduct research, ensure safety compliance, design equipment, and monitor production processes. Job profiles suited for this degree are:
Development chemical engineers design, develop, and implement industrial processes that involve chemical reactions. They then make use of these processes for the creation of new products.
Materials engineers research the structure of atoms to design and develop innovative methods to apply in chemical procedures.
Analytical chemists gather, process and analyse data on various substances to learn about chemical pollutants and their reactive properties.
Mining engineers ensure safety while extracting gases, compounds and other elements from down the planet.
Energy managers perform audits to analyse the consumption of energy to ensure appropriate measures are taken to maximise energy conservation.
Since petrochemicals is a more specialised field, these engineers focus and work directly with transforming raw petroleum and natural gas into specific chemical compounds. Here are some lucrative career options for a petrochemical engineer:
Process engineers are responsible for designing and maintaining processes that include extraction and refining of petrochemicals.
Quality control engineers ensure that the products used in petrochemical production are safe and meet the safety standards and regulations. They manage and maintain the quality of the petrochemical elements.
R&D engineers work on studying and developing new processes, technologies and other products used in this industry.
Technical sales engineers offer support on product usage and application. They also provide technical expertise to businesses that use petrochemical products.
The oil and gas sector is ever-growing; therefore, extraction, refining, and processing of chemicals from these will not end. Both chemical engineering and petrochemical engineering are dynamic and essential fields that contribute significantly to industrial processes. Ultimately, the choice between the two depends on individual interests and career goals. Whether you're passionate about designing chemical processes in a broad sense or specialising in the petrochemical industry, both fields offer exciting opportunities for exploration and innovation.
In the field of applied sciences, technology and engineering Agricultural Engineering and Food Engineering are two distinct yet interrelated fields crucial in ensuring an efficient food production system. Both aim to serve the food industry and help improve overall efficiency and sustainability.
Agricultural engineering combines agricultural practices with engineering principles that optimise and enhance the agricultural system. It deals with designing, developing and improving various agricultural improvements, processes, and machines used in farming. Professionals in this field work on enhancing crop cultivation techniques, irrigation systems, and farm machinery, aiming to optimise productivity while minimising environmental impact. On the other hand, food engineering deals with the post-harvest aspects of the food production chain. It involves the application of engineering principles to the processing, preservation, and packaging of food products. Food engineers work to develop innovative methods for food processing, ensuring the safety, quality, and nutritional value of the final products.
The agricultural engineering bachelor’s course spans four years and covers various aspects of engineering, including basics, concepts of crops and soil, and practical knowledge of the course. Students also delve into core engineering principles, agricultural sciences, and specialised courses in farm machinery, irrigation systems, and crop management.
A bachelor’s degree in food engineering also takes four years to complete and provides knowledge about food engineering, food science, food packaging, and food manufacturing. The four-year-round course is valuable and worthwhile for students interested in food science, food chemistry, food processing technologies, quality control, and understanding the food industries.
Agricultural engineering interfaces with agronomy, environmental science, and mechanical engineering. To be responsible for developing and designing new and innovative farm equipment or machinery and to enhance productivity in the agriculture field, one needs knowledge in agricultural engineering domains. Some of the courses in this field are:
Food engineering integrates aspects of chemical engineering, microbiology, and nutrition. Students who wish to pursue food engineering should have scientific knowledge, project management, problem-solving, and communication skills. To cover all of these and more, coursework in food engineering includes:
Agricultural engineering offers diverse and rewarding career opportunities, contributing significantly to different agricultural and food production stages. An agricultural engineer can work in the private and public sectors depending on one's interest. Specifically, in an agrarian economy like India, they are in high demand and play an essential role in economic development. Some of the job profiles that are suited for this course are:
Agronomists study the different practices and have knowledge of crop production principles and soil management for optimising crop yields and soil fertility.
Microbiologists research beneficial and harmful microorganisms in the soil or plants to improve soil health and decrease plant diseases. They work on improving agricultural sustainability via microbiological interventions.
Research analysts conduct experiments to analyse data that assist in developing innovative solutions for agricultural problems and evaluate the efficiency of agricultural methods and practices.
Agricultural inspectors are responsible for ensuring compliance with the standards and regulatory practices related to agriculture, food safety and the environment.
Crop engineers design and develop irrigation systems that improve crop yield and cultivation, along with focusing on engineering principles that increase crop production.
In contrast, a degree in food engineering can open doors to various job profiles. Being a versatile course, it can help those interested in food processing, packaging and distribution or safety and prevention. Professionals in this field are key in enhancing efficiency, sustainability, and safety within the agricultural and food sectors. Some of the career opportunities that one can get with this degree are:
Food engineers oversee and store agriculture-related material in the process of food manufacturing.
Food storage managers take care of the employees, goods storage facility and other day-to-day activities in the food storage business.
Quality assurance specialists help improve food safety and quality by conducting regular inspections and taking care of safety protocols about food processing plants.
The country's ever-growing population is directly proportional to the increase in demand for food. Therefore, the roles of a food engineer and an agriculture engineer are paramount now. They work towards improving crop yield for maximising agriculture output, ensuring food security, promoting sustainability, and addressing the domestic demand for sustainable and secure food systems. These very interesting fields combine engineering and science with technology to better utilise food resources.

Telecommunication Engineering vs. Network Engineering: Connectivity
The fields of telecommunication engineering and network engineering fall under the broader umbrella of information and communication technology, which play crucial roles in the modern world of communication and connectivity. While these two domains might have some similarities, they are distinct in many ways. Both disciplines are essential for the seamless transfer of information, yet they focus on different aspects of the broader communication landscape.
Telecommunication engineering is more focused on mediums and devices that transmit communication information in the form of words, images or even sounds. So, the primary mediums a telecommunication engineer works on and develops are telephone, television or radio. On the other hand, network engineering is about maintaining the connectivity of networks via data, videos, calls and wireless network services. This field looks after the overall network infrastructure and maximises the same, rendering performance and security to end users.
The course duration for pursuing a bachelor’s degree in telecommunication engineering, focusing on electrical and computer engineering, is four years. The four-year structure allows for an in-depth exploration of both theoretical concepts and practical applications.
Similarly, a bachelor's degree in network engineering generally follows a four-year timeline. This duration provides students with a solid foundation in networking principles, protocols, and technologies. The programme is structured to cover various aspects of computer networks, from basic connectivity to advanced network design and management.
The telecommunication engineering curriculum is designed to equip students with a broad understanding of communication systems, encompassing hardware and software. For creating, designing, implementing and maintaining communication systems, the typical course curriculum of a telecommunication engineer includes subjects such as:
Network engineering is a dynamic field with varying needs depending from company to company. The network engineering curriculum is tailored to provide students with a specialised understanding of computer networks and their applications, along with the knowledge of scripting language, network infrastructure, security, firewalls etc. A few of the network engineering courses are:
A degree in telecommunication engineering can lead to various career opportunities in the rapidly expanding fields of 5G and the Internet of Things (IoT). These engineers will ensure that all telecommunication systems, from smaller components to more extensive networks, function efficiently. Here are a few career opportunities after completing telecommunication engineering:
Telecom data analysts create reports and insights to help managers in decision-making by gathering and examining information on customer trends and network performance.
Technical support managers support customers facing difficulties with their telecommunication services and brief them about the business plans and services.
R&D engineers are specialists responsible for designing, developing and innovating new products and solutions for communication networks and systems.
Network security specialists implement and maintain security procedures to protect the overall network infrastructure and monitor the network traffic to avoid security flaws.
Networking engineering is a big industry, and in today’s digital world, where technology is rapidly growing, the demand for this profession is also seeing an upward swing. There are several growth opportunities for an engineer specialising in networking. Equipped with the right skills, talent and knowledge, network engineers can find themselves working in these positions:
Network specialists ensure the network works well while overseeing PCs so that the users get the right network based on their business needs. Removing and installing software or hardware also forms a part of their job.
Network administrators keep the computer network up and ensure smooth functioning. Businesses that use multiple software platforms or PCs often need a network administrator.
Network technicians monitor the everyday operations of a business’s computer systems, installing software or hardware and communicating with the clients to implement safety measures ensuring data protection.
Network solutions architects define the future networking and telecommunication infrastructure standards, offering knowledge on firewalls, Linux/ Unix configurations, and so on.
The fields of telecommunication engineering and network engineering overlap in terms of connectivity; the former revolves more around communication systems and technologies, whereas the latter is more about designing and managing the networking system concerning data exchange. Moving towards a modern interconnected environment, these fields hold immense potential and offer an exciting and rewarding career path for individuals with a passion for engineering, electronics, communications, and mathematics. Both fields are dynamic and continually evolving to meet the ever-growing demands of our interconnected world. As technology advances, professionals in both disciplines will play pivotal roles in shaping the future of communication and connectivity.

Environmental Engineering and Water Resources Engineering are closely related yet distinct fields within civil engineering. While both disciplines share common characteristics and often overlap, they address different aspects of our interaction with the environment, particularly concerning water.
Environmental Engineering is a multidisciplinary field that focuses on applying engineering principles to protect and improve the quality of the environment. Environmental engineers work towards designing and implementing solutions that mitigate the impact of human activities on the environment. This involves considering projects' environmental, social, and economic aspects to achieve a balance that ensures long-term sustainability.
On the other hand, Water Resources Engineering is a specialised branch of civil engineering that deals explicitly with managing and utilising water resources. This field focuses on planning, designing, and implementing systems that control and distribute water for various purposes, including irrigation, urban water supply, flood control, and hydropower generation.
Typically, an undergraduate programme in environmental engineering spans four years, leading to a Bachelor of Technology (Civil Engineering). Postgraduate programmes in environmental engineering typically offer Master of Technology and Doctor of Philosophy (Ph.D.) degrees. A Master's programme generally takes two years to complete, while Ph.D. programmes vary in duration but often take around five years, including coursework, comprehensive exams, and original research.
Undergraduate programmes in water resources engineering also commonly have a duration of four years. Postgraduate programmes in water resources engineering lead to a Master's and eventually a Ph.D. degree. The structure is similar to environmental engineering, with a Master's programme lasting around two years and a Ph.D. programme extending for several years. The emphasis in these programmes is on advanced topics and research.
Environmental engineering is a multidisciplinary field that addresses various environmental issues. The curriculum is designed to provide a comprehensive understanding of the principles and practices necessary to mitigate the impact of human activities on the environment. Core subjects include:
Water resources engineering focuses specifically on the study and management of water-related systems. The curriculum is tailored to equip students with the knowledge and skills to address water quantity, quality, and distribution challenges. Core subjects covered are:
Environmental engineers play a crucial role in developing solutions to address and prevent environmental issues caused by human activities. Their job roles are diverse and often involve working on projects that aim to protect and improve the quality of air, water, and soil. Some key career job roles in environmental engineering include:
Environmental consultants advise businesses and government agencies and assess environmental impact, ensure regulatory compliance, and recommend sustainable practices.
Air quality engineers focus on monitoring and improving air quality. They design systems to control and reduce air pollutants from industrial processes, transportation, and other sources.
Waste management engineers design and implement systems for properly collecting, disposing, and recycling solid and hazardous waste. They focus on minimising the environmental impact of waste disposal.
Environmental health and safety engineers ensure workplaces comply with environmental regulations and safety standards. They develop protocols to minimise environmental risks and protect the health of workers.
Environmental scientists research to understand environmental processes, assess pollution levels, and develop innovative solutions for environmental challenges.
Water resources engineers are specialists in managing and optimising water-related systems. Their job roles revolve around ensuring the sustainable use of water resources, preventing floods, and designing water supply and irrigation infrastructure. Key career job roles in water resources engineering include:
Hydrologists study the distribution and movement of water in the environment. They assess precipitation, evaporation, and runoff to understand water availability and plan for sustainable water resource management.
Hydraulic engineers design hydraulic structures such as dams, channels, and pipelines, thereby ensuring efficient water flow, controlling flooding, and optimising water transport systems.
Irrigation engineers design systems to supply water to crops efficiently. They aim to maximise crop yield while minimising water consumption.
Water quality engineers focus on maintaining and improving water quality. They design systems for water treatment and monitor water quality parameters.
While environmental engineering and water resources engineering have specific areas of emphasis, they are intricately linked and share a common goal of promoting sustainable practices and minimising the environmental impact of human activities. Environmental engineering takes a broader view, tackling issues related to air and water quality, waste management, and sustainable development. On the other hand, water resources engineering narrows down to planning and managing water systems for agriculture, urban supply, flood control, and hydropower. Ultimately, the choice between the two depends on individual interests, career aspirations, and preferred skill sets.
Mechanical Engineering and Mechatronics Engineering are closely related yet distinct fields within the broader engineering domain. Both fields deal with mechanical systems' design, analysis, and manufacturing, but they have unique focuses and applications. Both fields offer excellent prospects, and the decision between the two needs to align with your interests and the direction you envision for your engineering career.
Mechanical engineering is a foundational engineering discipline focusing on designing, analysing, and manufacturing mechanical systems. It forms the backbone of various industries, from automotive and aerospace to energy and manufacturing. It involves working on diverse projects, from designing machinery and thermal systems to developing components for consumer products.
Mechatronics engineering, on the other hand, is a more specialised and interdisciplinary field that integrates mechanical engineering, electronics, computer science, and control engineering. It focuses on creating intelligent systems that merge mechanical components with electronic and software elements. Mechatronics engineers work on projects involving robotics, automation, and control systems.
The duration of mechanical and mechatronics engineering programmes is four years for a bachelor's degree. In both disciplines, the four-year duration is divided into semesters or quarters, covering a range of fundamental and specialised courses. The courses include a combination of theoretical coursework, laboratory work, and possibly internships or cooperative education experiences. The curriculum is designed to provide a strong foundation in both mechanical and electrical engineering principles.
The curriculum for mechanical engineering is diverse, covering a wide range of subjects within the field. Additionally, some elective courses allow students to specialise in areas like automotive engineering, aerospace engineering, energy systems, or robotics. Here are some standard courses that are taught:
Mechatronics engineering is an interdisciplinary field that combines mechanical engineering, electronics, computer science, and control engineering. The unique aspect of mechatronics is the integration of mechanical and electronic systems to create intelligent and automated products. The curriculum includes:
Mechanical engineers have many career opportunities due to their versatile skill set. They are sought after in various industries, including automotive, aerospace, energy, and manufacturing, due to their expertise in designing, analysing, and manufacturing mechanical systems. Some common career paths include:
Automotive engineers design and improve automotive systems, vehicle performance, safety, and fuel efficiency.
Mechanical design engineers focus on creating and improving mechanical systems and products. They collaborate with cross-functional teams to ensure designs meet technical specifications and standards.
Aerospace engineers work on aircraft and spacecraft design.
Manufacturing engineers work on optimising manufacturing processes and systems and implement cost-effective solutions to improve production efficiency. They ensure that products are manufactured with high quality and within budget constraints.
Thermal and fluids engineers specialise in studying heat transfer, fluid dynamics, and thermodynamics. They design systems such as HVAC (Heating, Ventilation, and Air Conditioning) and heat exchangers.
With their combined mechanical and electronic systems knowledge, mechatronics engineers are well-suited for roles involving automation and intelligent technologies. Mechatronics engineers are in demand in the robotics, automation, telecommunications, and healthcare industries. Career options include:
Robotics engineers design and programme robotic systems for automation and various applications. They integrate mechanical components with sensors, actuators, and control systems.
Automation engineers implement automated systems in manufacturing using a combination of hardware and software. They optimise systems for increased efficiency and reduced human intervention.
Embedded systems engineers work on embedded electronics in various devices that involve hardware and software integration. They design and programme microcontrollers and microprocessors for specific applications.
IoT (Internet of Things) engineers design connected systems for IoT applications.
Control systems engineers work on designing and implementing control systems for machines and processes. They utilise feedback mechanisms to ensure the stability and performance of systems and address challenges related to automation and precision control.
While mechanical engineering and mechatronics engineering share common foundational principles, they diverge in focus, course content, and career opportunities. The choice between the two fields depends on individual interests and career goals. If you are passionate about traditional mechanical systems and enjoy the broader spectrum of engineering applications, mechanical engineering might be the right fit. On the other hand, if you are intrigued by the prospect of working with cutting-edge technologies, intelligent systems, and automation, mechatronics engineering could be the path for you.
The field of engineering is all about applying science or mathematics to problems or innovations that scientists come up with. It is a part of STEM education that engages students in science, technology, engineering and mathematics. Engineering applications are used everywhere, from prosthetics and cell membranes to construction and transportation.
Engineering physics is a blend of combined disciplines involving mathematics, engineering, chemistry and physics in multiple ways to develop and design innovative solutions. On the other hand, engineering mathematics is a branch of engineering concerned with mathematical methods and techniques that find their uses in various industries. The mutual relationship between these two fields plays a crucial role in developing innovative solutions and problem-solving in engineering.
Typically, an engineering degree, i.e. a Bachelor of Engineering (B.E.) is an academic degree that takes four years to complete. While studying for a bachelor’s in engineering, a student is offered various subjects spanning multiple disciplines. There can be specialisations or specific concentrations within the engineering field that can be studied, and mathematics and physics are amongst the common subjects that form a part of a B.E. degree. Since these are foundational courses, they usually begin in the initial semesters. They are spread across multiple semesters, going from beginner to advanced level, as they form the fundamental blocks for the engineering degree.
Engineering physics reduces the gap between practical engineering and theoretical science, focusing on design, analysis, research and development. Topics covered may include main areas of engineering such as:
Engineering mathematics is an interdisciplinary subject that answers engineer’s needs for practical and theoretical specialisations and helps solve engineering problems. Topics that engineering mathematics consists of primarily include:
Engineering physics bridges the fundamental laws of physics and their practical implementation in engineering design and technology. It is crucial in developing innovative solutions and advancing technology across various engineering disciplines. If you are interested or passionate about creating and testing systems or mechanical/electrical components of machines, then engineering physics is the path to take. You can find a career in various industries with a degree in engineering physics. Some career options might include:
Engineering mathematics is a multifaceted discipline that provides the analytical tools engineers need to understand, model, and optimise complex systems. An engineering mathematics degree can equip you with skills opening doors for various industry careers. A few potential career opportunities that you can look forward to are:
Both engineering mathematics and physics are unique in their ways, but the choice of moving forward with either of the specialisations depends on your future career goals and objectives. You can take these subjects as standalone or pursue them as a part of the integrated broader specialisation. Mathematics and physics are relevant for various job roles, as stated above. They are proficient in leveraging data-driven decision-making and can be considered good options as you embark on your engineering journey. The future of engineering solutions will undoubtedly be significantly influenced by the joint efforts of mathematicians and physicists within the engineering community as technology continues to progress.
Electrical engineering and Electronics and Communication engineering are closely related disciplines in the vast engineering field. The study, design and use of equipment and appliances that use any form of electricity comes under electrical engineering. In contrast, electronics and communication engineering focuses more on information transmission across different mediums via electronic devices. If you are passionate about developing and applying capacitors, inductors, inverters or other home appliances, electrical engineering is the right choice. On the other hand, if telecommunications, sensors, and microprocessors excite you, then electronics and communication engineering is the path ahead.
Both fields offer promising career opportunities, and the decision should be based on personal passion and the specific area of interest within the vast engineering field. As technology continues to evolve, professionals with a blend of skills from both disciplines may find themselves at an advantage in the ever-changing engineering landscape.
The course duration of these two fields of engineering is similar. To complete an electrical engineering degree, you need four years. It is considered a broader subject and can acquaint you with basic knowledge of electronics and communication as well, along with a wide range of topics related to electrical systems, devices, and networks.
Electronics and communication engineering takes four years to complete as well. It is a specific course designed to equip you with specialised skills relevant to modern communication technologies. The duration is tailored to emphasise electronics, signal processing, and communication systems.
The electrical engineering curriculum encompasses various topics, giving students a holistic understanding of electrical systems. Electrical engineering refers to electricity transmission and the proper and smooth production, functioning and storage of electricity when it travels from point A to point B. Some of the subjects that are taught in this field are:
While many students tend to get confused between the two subjects, electronics and communication deals with the electronics part that covers devices and chips used in electricity transmission. It focuses on the application of electronics to communication systems. The subjects that are dealt with while pursuing electrical and communication engineering are:
Electrical engineers have the necessary knowledge of mathematics and physics and technological know-how for debugging and scrutinising situations from a technical perspective. Some of the career opportunities that are available for an electrical engineer are:
With the continuous development in communication technology and our increasing reliance on electronic systems, graduates with an electronics and communication engineering degree can work in telecommunication, aviation, research and development, automotive, defence and many other industries. Here are a few career opportunities that are available in this discipline:
Electrical engineering and electronics and communication engineering are disciplines that stand out independently and are considered some of the most dynamic and promising engineering fields. The choice between the two is purely out of one’s personal interests and future career goals. Although both fields have substantial overlap, the learning outcomes from these degrees are substantially different, including the particular applications they cater to in the engineering domain. Let your long-term career aspiration and aptitude shape and guide your decision!

Aerospace Engineering and chemical engineering are two streams in the broad spectrum of engineering embarking on the success of scientific innovation. Engineering is regarded as the strongest pillar of technology and scientific advancements. Aerospace Engineering and chemical engineering stand out for their research progress and scientific contributions to the world. Both fields of study are filled with scopes to conquering miraculous accomplishments. Here is everything you need to know about these two streams of professional courses in detail before choosing one.
Aerospace and chemical engineering courses are available at both bachelor’s (B-Tech) and master’s (M-Tech) levels. The course duration for these courses is listed below:
The eligibility criteria for enrolling in engineering bachelor’s programmes for both streams are completion of 12th of equivalent studies with maths and science as primary subjects.
The eligibility criteria for enrolling in for engineering master’s programme for both streams is completing a bachelor’s in the respective programme with an aggregate accepted by the university.
The branch of aerospace engineering and chemical engineering has been popular for a very long time. These streams are popular and celebrated for various reasons ranging from their significant impact on the global economy to the subject challenged. Here is a structural outline of both courses for further clarity.
The aerospace and chemical industry has always been a great contributor to the world’s growing economy. Since the time of the academic evolution of engineering, the course has grown to a career-promising field and below are a few of the several options available in the job market.
Aerospace Engineering and Chemical Engineering are vast with the potential to bring a beneficial change to mankind. After, having a closer look at the core areas of study and career prospects of both the streams of the discussed professional course, it is inferred that both disciplines portray the transformative power of the subject relevance. and human innovations. Both fields are career-promising for the subject potential and the hefty contribution of the respective sectors towards the global economy. Hence, the right choice of stream with passion and enthusiasm can further elevate the ever-evolving landscape of science.
Engineering offers a vast array of specialised branches. Amidst the multitude of options available, it is often a challenging task to choose one specialisation that truly piques interest. However, the decision becomes even more complex when you encounter two closely related engineering disciplines like chemical engineering and bioprocess engineering.
Today, we will explore two such closely intertwined branches: "Chemical Engineering" and "Bioprocess Engineering." Chemical engineering focuses on the design and operation of industrial manufacturing plants, with a primary emphasis on the production of chemicals and various products that undergo chemical processing. Conversely, bioprocess engineering applies chemical engineering principles to focus on industrial processes and biological components, such as living cells and their constituents. Let us study these two engineering domains, the courses available, the curriculum, and their promising career prospects!
Courses, Duration, and Eligibility Criteria
The undergraduate courses available in the fields of chemical and bioprocess engineering comprises a Bachelor of Engineering (B.E) and a Bachelor of Technology (B.Tech). For students interested in higher education, there are post-graduate programmes such as Master of Engineering (M.E) and Master of Technology (M.Tech). Moreover, students have the option to pursue diploma or certification courses to augment their expertise and proficiency in their respective sub-disciplines.
While the duration of UG programmes entails four years, PG programmes are generally two-year courses in India. The duration of the diploma and certification courses can vary, ranging from six months to one year.
The eligibility criteria for UG admissions encompass a successful completion of 10+2 with a minimum score of 50 percent from an accredited institution. The applicants should have pursued mathematics, physics, and chemistry as major subjects during their high school education. Besides this criterion, the selection process for most colleges and universities generally involves entrance examinations and personal interviews. Students interested in pursuing a lateral entry into B.Tech programmes are required to hold a diploma programme from a recognised institution. On the other hand, students applying for PG courses should hold 50% marks in their B.E/B.Tech degree, followed by a valid GATE score. Similarly, candidates who have completed a 5-year programme in science or applied sciences can also apply for M.Tech courses.
Course Curriculum
Chemical engineering courses focus on the study of processes and designs related to chemical plants and production methods. In this engineering field, students gain a robust understanding of various subjects, including chemistry, materials, mechanics, fundamental principles of chemical engineering, petrochemicals, and operational procedures. Students learn about the principles of physics and chemistry, mathematics, biology, economics, and more. Other crucial subjects covered in the curriculum are material science, renewable energy sources, fluid mechanics, and more.
Conversely, bioprocess engineering provides a strong foundation in key aspects of bioprocess research, emphasising its significance and practical applications in relevant industries. The curriculum equips students with the knowledge and skills required to produce biofuels, develop enzymes for nutritious food, and comprehend the conversion of waste materials into energy sources. The core topics addressed in this curriculum include pharmaceuticals, petrochemicals, waste management, pollution control, and metallurgical processing.
Career Opportunities
In contemporary India, chemical engineering stands out as one of the most in-demand career choices. Students can harness their knowledge to pioneer innovative technologies, opening up lucrative prospects in fields such as environmental conservation and ensuring health and safety. Students can work as process engineers, optimising manufacturing processes and designing systems for chemical production. Furthermore, students can venture into research and development, contributing to innovations in pharmaceuticals, materials, and sustainable energy. Environmental engineering offers a pathway to work on critical global challenges like pollution control and sustainable resource management. Students interested in entrepreneurial ventures can explore careers in project management and consulting related to strategic planning, cost analysis, and client collaboration.
After the completion of their degree in bioprocess engineering, students will have plenty of career opportunities in the fields of vaccines, antibiotics, food and agricultural products, pharmaceutical supplements, and others. Students can contribute to research and development in biotechnology companies, advancing breakthroughs in healthcare, agriculture, and renewable energy. Environmental bioprocess engineers are responsible for developing sustainable strategies for waste management and the mitigation of pollution. Furthermore, there are career prospects available in areas like pharmaceutical and biotechnology sectors. Bioprocess engineering students can also explore roles in food and beverage production, responsible for ensuring food safety, quality, and innovation. With the growing importance of sustainable practices, bioprocess engineers play a pivotal role in the fields of bioremediation and bioenergy.
Way Forward
We can understand that prospects are promising in both fields. Both disciplines offer various career paths, from research and development to regulatory affairs. Chemical engineers play a crucial role in designing environmentally friendly technologies. On the other hand, bioprocess engineers work on vaccines, antibiotics, food, pharmaceuticals, and renewable energy. While chemical engineering deals with industrial plant design and chemical production, bioprocess engineering applies chemical principles to biological processes. Both fields offer undergraduate and postgraduate programmes, along with diploma courses. Students can align their interests and career goals before taking the final call!

Over the past few years, notable technological progress has underscored the impact of computers and software in our day-to-day lives. The technology sector has become so pervasive that occupations such as computer engineers and software engineers have achieved widespread recognition across various social levels. Frequently, these terms, 'computer engineers' and ‘software engineers' are used interchangeably. While both career paths share some common features, several distinctions exist between them. Computer engineering, a broader discipline, encompasses software engineering as one of its sub-domains. While computer engineering involves the design and development of various computer systems, software engineering entails the diagnosis of issues in computer system operations. The latter emphasises designing, testing, and implementing computer software with minimal concern for computer hardware. Today, in this blog, we shall explore these two engineering disciplines in detail:
Courses and Duration
The undergraduate (UG) courses available in computer engineering include a Bachelor of Engineering (B.E) and a Bachelor of Technology (B.Tech) in computer engineering. The duration of these specialised UG programmes is four years, further divided into eight semesters. Students can advance their studies in the same field by enrolling in a Master of Engineering (M.E) or a Master of Technology (M.Tech) programme. These postgraduate degrees have a duration of two years, divided into two semesters.
On the other hand, students interested in the field of software engineering can pursue B.E or B.Tech in this specialisation. The duration of these UG programmes is also four years, further split into eight semesters. Options for PG degrees are also available, such as M.E or M.Tech in software engineering, a 2-year engineering course.
Course Curriculum
The computer engineering curriculum provides a comprehensive understanding of coding languages, essential topics in computer architecture, artificial intelligence, and cyber security. Additionally, students learn about core computing subjects, gaining insights into principles and techniques from diverse areas such as digital image processing, digital electronics, VLSI, and basic electrical and electronics engineering. Within this curriculum, students can develop a profound knowledge of both software and hardware methodologies. The curriculum often includes other essential subjects like digital electronics, database systems, and information and network security, among others.
The software engineering curriculum offers an overview of various topics, including computer programming, web development, data structures, and project management. The programme equips students with practical knowledge for software design, development, and testing. Key subjects within the software engineering curriculum include computer science engineering, programming, mathematics, machine learning, and big data. It's worth noting that the software engineering syllabus may differ based on the academic level. For example, the UG courses introduce students to software engineering and foundational concepts in the field. However, the PG courses dive deeper into specialised and advanced topics within the field of software engineering.
Career Opportunities
Computer engineering holds a top spot as a favoured career path for many students. This popularity is primarily due to the broad spectrum of specialisations available within the field, thereby offering numerous career prospects for students. Armed with a versatile skill set, students can venture into roles like software development, hardware design, and systems engineering. Moreover, students can discover their expertise in domains like artificial intelligence, cybersecurity, data science, and network administration. Students can find employment as software developers, network engineers, system administrators, or data analysts. The growing importance of cybersecurity has opened up job roles related to safeguarding digital assets, such as ethical hacking and cybersecurity specialists. Furthermore, there is abundant scope for career progression in sectors like telecommunications, healthcare, and automotive technology.
Conversely, emerging trends suggest that transformative technologies like automation, virtual reality, and cryptocurrency will become the driving factors behind the growing demand for software engineering. Students can leverage their expertise to find employment in product development, data science, marketing, and more. Of these, software developers play a crucial role, given their crucial involvement in developing software solutions for businesses. Students will be responsible for identifying, implementing, and rigorously testing software applications, thus holding a significant position in the technology landscape. Besides this, students can specialise in front-end or back-end development, design user-friendly interfaces, or optimise the efficiency of complex systems. Furthermore, opportunities also extend into areas like mobile app development, web development, and database management.
Summing Up
In an era marked by technological advancement, the significance of computers and software in our daily routines has reached a paramount level. This has led to a growing prominence of computer engineering and software engineering in the tech industry. Computer engineering has a wider scope, involving the design of computer systems and hardware, with software development as one of its components. Conversely, software engineering focuses on the identification and resolution of software-related problems. By examining the courses, curriculum, and career prospects associated with these fields, students can make well-informed decisions regarding their educational and professional paths in these tech-driven domains.
Mechanical and aerospace engineering are two highly coveted specialisations in the field of engineering. Although both the fields use mechanical systems and devices, the end products and systems that these two disciplines deal with are quite different. Mechanical engineering uses devices and systems for domestic or industrial purposes, whereas aerospace engineering focuses on building aircraft, spacecraft, missiles, and weapons systems. The end objective of mechanical engineering is to design, manufacture, and maintain power-producing and power-consuming machines. In contrast, aerospace engineering leverages the principles of physics and navigation to design missiles, helicopters, planes, drones, civil aircraft, satellites, and others. Our blog aims to dive deep into each specialisation and help students make an informed career choice!
Duration and Eligibility
Both mechanical and aerospace engineering offer undergraduate (UG) programmes such as Bachelor of Engineering (B.E) and Bachelor of Technology (B.Tech) respectively. The duration of these UG degrees is four years, divided into eight semesters. Furthermore, students have the option to pursue higher education in both disciplines by enrolling in a Master of Engineering (M.E) or a Master of Technology (M.Tech) programme. These postgraduate engineering programs extend over a period of two years, divided into four semesters.
The eligibility criteria for these two engineering degrees at the UG level require 50% marks in class 10+2 from CBSE/ICSE/State Board, or equivalent. Students who are applying should have studied mathematics, physics, and chemistry (biology, optional) in their higher secondary. However, the qualifying aggregate score is 40% in the case of SC/ST/OBC candidates. Students who possess a diploma in mechanical or allied sciences after the completion of secondary education are also eligible for direct admission. Furthermore, students need to clear national (Joint Entrance Examinations) or state-level entrance examinations (ComedK/WBJEE) to secure admissions to reputed engineering colleges.
Curriculum
A mechanical engineering curriculum covers a diverse range of subjects, viz., mechanics, thermodynamics, and materials science. As semesters advance, students learn specialised topics such as fluid dynamics, heat transfer, and machine design. Other areas of study comprise control systems, manufacturing processes, and structural analysis. Moreover, students have the opportunity to take up elective courses and projects in fields such as robotics, renewable energy, and automotive engineering.
In contrast, the aerospace engineering programme allows students to develop expertise in aerospace-focused subjects. Students gain insights into areas like aerodynamics, design of aircraft and spacecraft, propulsion systems, and structural analysis. The curriculum also covers areas such as flight mechanics and orbital mechanics to gain a comprehensive understanding of flight and space exploration. Furthermore, the curriculum may offer elective courses in areas like avionics, advanced materials, and space systems engineering.
Career Prospects
Mechanical engineering is known for imparting problem-solving and innovation skills through its courses. Students can utilise their knowledge and skills to access a wide range of job opportunities in the evolving business landscape. After graduation, students can work in the automotive industry, designing, manufacturing, and enhancing the performance of vehicles. Furthermore, ample career advancement opportunities lie in the energy sector. Students can leverage their expertise in energy production, renewable energy technologies, and energy-efficient systems. On the other hand, a career in manufacturing involves supervising production processes, ensuring quality control, and implementing automation in manufacturing facilities. Students can also venture into the fields of robotics and automation, where they design robotic systems for diverse applications.
Conversely, aerospace engineering provides promising career prospects, driven by the burgeoning commercialisation of the space industry. Aerospace engineers play a crucial role in the development of aircraft, spacecraft, and propulsion systems. Furthermore, with the emergence of private space enterprises and government investments in space exploration, students can explore various areas, including satellite technology, space tourism, and planetary expeditions. Students can work as aircraft design engineers, focusing on the development of airplanes, helicopters, and unmanned aerial vehicles (UAVs). Alternatively, students can work as propulsion engineers, engaged in the development of engines for spacecraft, such as jet engines and rocket propulsion systems.
Summing Up
Mechanical and aerospace engineering stand as highly sought-after specialisations within the vast field of engineering. Mechanical engineering focuses on machines for domestic and industrial use, while aerospace engineering deals with aircraft, spacecraft, and related technologies. Both mechanical and aerospace engineering offer promising career prospects across various fields. Mechanical engineers find opportunities in the automotive industry, energy sector, manufacturing, and automation, among others. Conversely, aerospace engineers are in high demand due to technological advancements and the flourishing commercial space industry. These engineers play an integral role in the development of aerospace technologies, with promising avenues in satellite technology, space tourism, and others. Both fields present exciting career opportunities for students who are passionate about innovating and solving complex engineering challenges.

A recent university survey reported that automotive and industrial engineering are at the forefront of technological innovations, thereby offering promising career prospects to young professionals. These two disciplines form an integral component of production engineering, and differ from each other. Mechanical engineering emphasises developing a wide range of vehicles and their equipment. On the other hand, industrial engineering collaborates with automotive engineers to translate the ideas into action. Industrial engineering oversees the entire project life cycle, from manufacturing specifications to delivery on time. Distinguishing between these professions is vital for effective project management, spanning from design to completion. Today, we shall explore these two engineering disciplines and understand the differences between them!
Automotive Engineering vs. Industrial Engineering: An Overview
| Parameters |
Automotive Engineering |
Industrial Engineering |
| Subject Focus |
Focuses on the design, development, manufacturing, and maintenance of vehicles, such as cars, trucks, motorcycles, and other transportation vehicles. |
Focuses on optimising processes and systems in various industries, such as, manufacturing, healthcare, logistics, and others. |
| Courses Available | Undergraduate courses (UG):
Post-graduate courses (PG):
|
Undergraduate courses (UG):
Post-graduate courses (PG):
|
| Duration |
UG: 4 years ; PG: 2 years |
UG: 4 years ; PG: 2 years |
| Key Skills |
|
|
Automotive Engineering vs. Industrial Engineering: Syllabus
Automotive engineering courses deal with designing vehicle components, improving fuel efficiency, enhancing safety features, and addressing vehicle-related challenges. Students learn to tackle issues such as engine performance, aerodynamics, and vehicle dynamics. The core subjects covered in this field of engineering are listed below:
On the other hand, the industrial engineering curriculum covers supply chain management, production line efficiency, quality control, and workflow improvements. The main aim of the course is to impart knowledge and skills on reducing costs and increasing productivity across various industries. The core subjects covered in this field of engineering are listed below:
Automotive Engineering vs. Industrial Engineering: Future Scope
As the automotive industry is growing rapidly, the demand for skilled automotive engineers is robust. After graduation, students can work in diverse areas such as vehicle electrification, battery technology, software development, and others. Additionally, the ongoing focus on sustainability has resulted in employers seeking skilled engineers who can innovate and optimise automotive designs. Here is an overview of exciting career opportunities in the field of automotive engineering:
Industrial engineering offers great career advancement scope due to its versatile applications across various industries. Students can leverage their expertise to enhance efficiency, reduce costs, and improve processes in diverse sectors. As industries continuously seek ways to optimise operations and remain competitive, industrial engineers play a pivotal role in streamlining workflows and resource management. Here is an overview of exciting career opportunities in the field of industrial engineering:
Final Thoughts
Automotive and industrial engineering stand as dynamic fields, driving technological innovations and promising career prospects for emerging professionals. While both contribute to production engineering, they offer distinct areas of expertise. Automotive engineering focuses on vehicle design and sustainability; industrial engineering deals with process optimisation and quality control across various industries. Both fields provide undergraduate and postgraduate programmes covering a wide range of subjects and elective specialisations. The future scope of automotive engineering is robust, with career opportunities in design, manufacturing, electrical systems, testing, and validation. Industrial engineering, too, offers versatile career advancement prospects, with roles such as engineering economists, operations research analysts, quality control specialists, inventory control managers, and others. Both fields hold exciting opportunities; therefore, students must carefully align their career goals before making the final call!
Electrical and electronics engineering is often considered to be at the forefront of modern technology. Both electronic and electrical engineering focus on the development of innovative devices using new materials and address the challenges posed by the next generation of technology. Despite their similarities, they are two distinctive branches of engineering. Electrical engineering focuses on the generation and distribution of power, predominantly in the form of electricity. In contrast, electronics engineering can be regarded as a specialised subfield of electrical engineering, focusing on the design, optimisation, and management of electronic devices.
To illustrate the contrast between these engineering disciplines, let us consider the example of an audio amplifier system. An electronics engineer would be responsible for designing the intricate circuitry within the amplifier and selecting and configuring the appropriate electronic components. An electrical engineer, on the other hand, would be involved in the overall power distribution within an audio system, ensuring that the amplifier receives the necessary electrical power for operation. This example implies that while electrical engineering is a broader field, electronics engineering is more specific. Today, we shall understand the key differences between these engineering specialisations in detail:
Industry Focus
Electrical engineering deals with the generation, transmission, and distribution of electrical energy. This engineering discipline involves the design and innovation of electrical machinery and equipment for industrial structures and facilities. Typically, individuals in this field work on extensive systems, including power grids, substations, and power plants.
Conversely, electronics engineering, a subdiscipline of electrical engineering, focusing on smaller-scale electronic devices and systems. In this engineering field, individuals gain expertise in designing, developing, implementing, and maintaining electronic circuits and software. The knowledge acquired in electronics engineering is applicable to a wide range of fields, including automation and control systems, robotics, and biomedical devices, among others.
Courses and duration
The courses in electrical engineering help build a strong foundation in power systems, electromagnetics, control systems, and high-voltage engineering. Conversely, electronic engineering focuses on areas such as analogue and digital electronics, microelectronics, circuit design, and others. Let us see some of the courses covered in both of these disciplines:
| Parameters | Electrical Engineering | Electronics Engineering |
| Undergraduate (UG) Courses | Bachelor of Engineering (B.E) Bachelor of Technology (B.Tech) |
Bachelor of Engineering (B.E) |
| Postgraduate (PG) Courses | Master of Engineering (M.E) Master of Technology (M.Tech) |
Master of Engineering (M.E) |
| Duration | UG: 4 years PG: 2 years |
UG: 4 years |
Course Curriculum
The electrical engineering curriculum focuses on the practical applications of electricity, electronics, and electromagnetism. Students get trained to design electrical circuits and various equipment. The curriculum imparts expertise across a wide spectrum, from managing and optimising large-scale power plants to collaborating with smaller hardware companies. This engineering discipline covers multiple sub-disciplines, such as acoustics, speech, signal processing, automotive and vehicular technology, geoscience, remote sensing, laser and electro-optics, robotics, ultrasonics, ferroelectrics, and frequency control.
Electronics engineering courses deal with electronic circuits, integrated circuits, and systems using electrical components. The curriculum covers areas of telecommunications engineering, embedded systems design, microelectronics, and electromagnetic engineering, among others. This branch of engineering imparts a robust understanding of artificial intelligence (AI), semiconductors, optoelectronics, and image and video processing. Some engineering colleges may also cover areas like robotics, embedded systems, or telecommunications in the curriculum. Other key topics that are included in electronics engineering are control engineering, VLSI design, digital signal processing, and wireless communication systems.
Career Scope
Electrical engineering offers diverse and promising career prospects across various industries, namely, construction, power generation, telecommunication, IT, and others. After graduating, individuals can work as electrical engineers, maintaining power grids, and supervising the research and development of electronic devices. Within electrical engineering, two primary career paths stand out, i.e., power engineers and telecommunication engineers. Power engineers are crucial in the generation and transmission of electricity, especially in the automobile industry. On the other hand, telecommunication engineers focus on cable design and maintenance, as well as the production of receivers and transceivers. Other job profiles within electrical engineering include instrumentation engineers, power electronics engineers, and embedded systems engineers, each contributing to different facets of technology and innovation.
On the other hand, electronics engineering offers a wealth of career opportunities, driven by the rapid scientific advancements around the world. Individuals can explore promising career prospects in laboratories and scientific experiments, government organisations such as DRDO, NASA, and ISRO, healthcare, and life-saving interventions. Alternatively, individuals can work as electronic engineers, checking the quality of electrical components and products. As electronic engineers, individuals will be responsible for designing, analysing, and conducting research to enhance electronic products. For those seeking leadership roles, technical heads in this field are responsible for effective communication and collaboration with their teams. Alternatively, individuals can take on roles such as network planning managers, planning, designing, evaluating, and implementing changes to both existing and new communication networks.
Way Forward
Electrical engineering and electronics engineering, while closely related, are distinct disciplines with diverse career prospects. Electrical engineering focuses on power generation and distribution, while electronics engineering concentrates on electronic devices and components, with applications in areas like automation and healthcare. The curricula for these fields differ, with electrical engineering covering topics such as power systems and electromagnetics, while electronics engineering explores electronic circuits and microelectronics. Career opportunities in electrical engineering span construction, power generation, and telecommunications. On the other hand, electronics engineering offers promising paths in laboratories, government organisations, and healthcare sectors. Both fields of engineering have their own unique contributions to technological advancements, offering individuals a wide range of career possibilities in a rapidly evolving world.

Amidst all the engineering disciplines, civil and structural engineering play a pivotal role in our ever-growing and urbanising world. While civil engineering and structural engineering share the common goal of developing our infrastructure, they possess distinctive roles. Civil engineering encompasses the overall construction and maintenance of the built environment. On the other hand, structural engineering specialises in the specific design and analysis of individual structures, such as buildings and bridges. Today, in this blog, we shall understand the differences between these two engineering specialisations in detail:
Focus and Duration
The undergraduate courses available in civil engineering include a Bachelor of Engineering (B.E) and a Bachelor of Technology (B.Tech) in civil engineering. These UG courses focus on building materials, construction, and planning. Upon successful completion of these programmes, students can plan, design, and construct diverse structures such as buildings, roads, bridges, and canals. The undergraduate courses span four years, organised into eight semesters. Additionally, students have the opportunity to pursue advanced degrees like a Master of Engineering (M.E) or Master of Technology (M.Tech) in this field, which usually lasts for two years, comprising four semesters.
Conversely, structural engineering is a broad specialisation within the field of civil engineering. This field of engineering deals with planning, evaluating, designing, and managing the construction of huge structures like bridges, tunnels, buildings, flyovers, etc. The UG courses offered in this stream are B.E and B.Tech in structural engineering, spanning four years in duration. Furthermore, students can opt for higher education by pursuing post-graduate degrees in relevant fields. The duration of these PG courses is also two years.
Course Curriculum
The civil engineering courses introduce a specialised curriculum that imparts learning on the planning, design, and construction of infrastructure such as roads and buildings. Often considered a conventional engineering discipline, numerous colleges are making efforts to enhance the civil engineering syllabus. Subjects like engineering graphics and design, computer-aided analysis, and design are now integral components of the curriculum. Let us see some of the core subjects covered in this curriculum:
| Functions of Several Variables | Engineering Drawing |
| Intro to Civil Engineering | CE Materials and Construction |
| Series and Matrices | Ecology and Environment |
| Physics I & Physics II | Surveying |
| Physics Lab. 1 | Mechanics of Materials |
| Engineering Mechanics | Geotechnical Engineering |
| Chemistry I & Chemistry II | Transportation Engineering |
| Intro to Programming | Hydraulic Engineering |
The curriculum in structural engineering focuses on the construction, and improvement of structures engineered to endure natural forces and the stresses of daily use. Grounded in the core principles of physics, mathematics, and materials science, students master the art of designing structures that are functional and aesthetically appealing. This engineering discipline covers a wide spectrum of specialisations, including earthquake-resistant structures, aerospace structures, nanoscale structures, and more. Let us see some of the core subjects covered in this curriculum:
| Applied Mathematics for Civil Engineers | Costing & Scheduling Laboratory |
| Advanced Theory & Design of Concrete Structures | Aircraft Systems & Structures |
| Experimental Methods & Model Analysis | Advanced Mechanics of Solids |
| Structural Dynamics | Stability of Structures |
| Theory of Plates & Shells | Design Studio |
| Design of Metal Structures | Engineering Optimisation |
| Finite Element Analysis | Seismic Design of Structures |
| Research Methodology & IPR | Theory of Elasticity & Plasticity |
Career Opportunities
In an era of ongoing global population growth, the demand for civil engineers is paramount. These engineers play a significant role in the planning, construction, and upkeep of essential infrastructure, including structures, roads, water distribution systems, and more. Furthermore, civil engineers are at the forefront of tackling contemporary challenges like sustainability, climate change resilience, and the development of smart cities. Following their graduation, students can work on different projects, spanning from designing towering skyscrapers to developing efficient water treatment facilities. Students can also pursue careers in the public sector with government agencies responsible for maintaining public infrastructure.
The potential for structural engineering in India is huge. LinkedIn data reveals that the prominent sectors actively hiring structural engineers include civil engineering, construction, oil and energy, automotive, and real estate. Within the construction industry, students have the opportunity to engage in the planning and supervision of building, bridge, and other structural projects. However, in the infrastructure sector, students can actively participate in the development of roads, dams, and transportation systems. Aerospace companies also employ structural engineers to design and analyse aircraft components. Moreover, there are ample opportunities in research and academia for students interested in higher education and innovation.
Summing Up
Civil and structural engineering stand as indispensable disciplines in our global world. While these two branches of engineering share a common goal of advancing our built environment, they maintain distinct identities. Civil engineering deals with the comprehensive construction of the built environment and tackles concerns related to sustainability and climate change. In contrast, structural engineering specialises in developing structures engineered to withstand the rigors of natural wear and tear. The civil engineering curriculum covers a spectrum of subjects, including mechanics and materials, while structural engineering offers specialisations in fields like aerospace and earthquake engineering. Furthermore, career opportunities in both of these fields are diverse, robust, and full of potential. In summary, civil and structural engineers stand as the architects of tomorrow's sustainable and resilient infrastructure.

Biotechnology Engineering and Genetic Engineering are two closely related yet distinct biotech pathways that play pivotal roles in shaping the future of science and technology. Both disciplines harness living organisms' power and molecular processes but differ in their scopes, objectives, applications, and methodologies.
Biotechnology Engineering, often referred to simply as Biotechnology, is a broad field that integrates biological principles with engineering practices to develop innovative solutions for several industries. It encompasses multiple applications, including agriculture, medicine, environmental management, and industrial processes.
Genetic Engineering, conversely, is a subset of Biotechnology that focuses explicitly on directly manipulating an organism's genes. It involves altering the genetic material, typically DNA, to introduce desirable traits or eliminate unwanted characteristics. Genetic Engineering has revolutionised various fields, including medicine, agriculture, and industry, by allowing scientists to modify the genetic makeup of organisms. In the realm of medicine, Genetic Engineering has led to the development of gene therapies that hold the potential to treat and cure genetic disorders.
Course duration
The duration of Biotechnology Engineering and Genetic Engineering programmes can vary depending on the level of study. Both fields typically offer a four-year bachelor's degree programme at the undergraduate level. Students pursuing a bachelor's in Biotechnology Engineering or Genetic Engineering undergo a foundational curriculum that includes core courses in biology, chemistry, mathematics, and engineering principles. For those seeking advanced degrees, such as master's or Ph.D., the duration can vary. A master's programme generally takes two years to complete, while a Ph.D. programme can extend for three to five years, focusing on advanced research and specialisation.
Curriculum
Biotechnology Engineering is a broad and multidisciplinary field with a wide range of subjects that provide students with a comprehensive understanding of biotechnological applications. Primary courses in biology, chemistry, and engineering are usually included in the curriculum. Specialised electives including molecular biology, bioinformatics, bioprocess engineering, and bioethics are then studied. Additionally, students enrolled in Biotechnology Engineering programmes may work in practical laboratory work to obtain hands-on experience in bioprocessing, genetic engineering, and protein expression. Additionally, optional courses may allow students to tailor their education based on their specific interests within the field.
Core areas of study include:
The curriculum for Genetic Engineering is more focused and specialised, emphasising molecular biology and genetic manipulation techniques. Students delve into the intricacies of DNA manipulation, gene expression, and the ethical considerations surrounding genetic modifications. Laboratory work is a significant component of Genetic Engineering programmes, where students gain practical skills in gene editing techniques such as recombinant DNA technology and cloning. The focused nature of the curriculum prepares students for precision work in manipulating genetic material.
Core courses often include:
Career opportunities
Biotechnology engineers find diverse opportunities in pharmaceuticals, contributing to drug development and manufacturing. They play pivotal roles in agricultural biotechnology, enhancing crop yields and creating genetically modified organisms. In healthcare, they design medical devices and diagnostic tools, while environmental biotechnology offers roles in waste treatment, pollution control and sustainable resource utilisation. Food technologists work in the food industry to develop and improve processes for food production, preservation, and quality control. Research and development positions allow biotechnology engineers to explore innovative solutions like synthetic biology and bioinformatics.
On the other hand, genetic engineers focus on gene therapy, correcting genetic disorders, and advancing medical treatments. In agriculture, they contribute to genetically modified crops, creating plants with improved traits. Biomedical research offers opportunities to delve into the genetic basis of diseases. The field extends to genomic counselling, guiding individuals through the implications of their genetic information. Stem cell researcher explores the use of stem cells in genetic engineering applications, including regenerative medicine and tissue engineering. Genomic data analyst utilises bioinformatics tools to analyse genomic data, contributing to research in genetics and personalised medicine.
Conclusion
Both Biotechnology Engineering and Genetic Engineering open doors to impactful careers, shaping the future of medicine, agriculture, and biotechnology. While Biotechnology Engineering and Genetic Engineering share common roots and goals, they represent distinct branches with unique focuses and methodologies. Both fields contribute significantly to advancements in science and technology, driving innovation and shaping the future of various industries. Ultimately, the choice between Biotechnology Engineering and Genetic Engineering depends on individual interests and career aspirations within the broader realm of biotechnology and genetic sciences.

Engineers play an important role in refining the raw materials that occur naturally to create useful devices and solutions. Engineering studies hone problem-solving skills, which can be applied in many fields. If you are passionate about protecting the planet and smartly using its limited resources, environmental engineering and materials engineering are two streams to learn about creating sustainable solutions to reduce pollution, minimise waste, recycle and reuse, create efficient waste management systems and so on. Engineering is the process of improving the system, increasing efficiency, and applying design processes to create solutions.
Course Eligibility and Duration: Materials Engineering vs. Environmental Engineering
Engineering courses can be pursued after 10th grade through a Diploma in Engineering. After a Diploma in Engineering, the Bachelor of Engineering programme is of 3 years duration. After 12th grade, the Bachelor of Engineering (BE) or Bachelor of Technology (B.Tech) courses are of 4 years duration.
To be eligible for the programme, in 12th grade, the candidate must score a minimum of 50% with Mathematics, Physics, Chemistry, and Biology as compulsory subjects.
Curriculum and Syllabus: Materials Engineering vs. Environmental Engineering
Materials Engineering, or Material Science Engineering is an interdisciplinary field where one studies properties of matter and its application in various engineering and sciences. Students learn about ceramics, metals, polymers, composites, and semiconductors along with chemistry, physics, and life sciences. Students will understand the science of structures. The syllabus covers Basic Electrical & Electronics Engineering, Mechanical Behaviour of Materials, Chemistry, Engineering Drawing, Materials Characterisation, Phase Equilibrium in Materials, Computer Programming, Engineering Mechanics, Iron and steel-making, Thermodynamics, Kinetics of Materials, Mathematics and Physics, Industrial Economics, Electronic and Optical Materials, Corrosion and Degradation of Materials, Fundamentals of Materials Processing, Principles of Powder Processing, HeatTreatment of Metals, Diffusion in Solids, Manufacturing Processes: Selection and Design and so on.
Environmental engineering is a sub-branch of Chemical Engineering and Civil Engineering courses. It concerns itself with natural resource management, environmental pollution, and water resource management among other things.
The subjects studied in the courses are Engineering Maths, Engineering Physics, Elements of Civil Engineering and Engineering Mechanics, Basic Electrical Engineering, Environmental Chemistry, Environmental Biology, Strength of Materials, Surveying Construction, Elements of Environmental Protection, Municipal Solid Waste Management, Origin and Characterisation of Environmental Pollution, Hydraulics and Hydraulic Machines, Applied Engineering Geology, Wastewater Collection and Drainage System, Water Treatment Engineering, Water Supply and Distribution System, Hydrology and Water Resources Engineering, Geotechnical Engineering, Management and Entrepreneurship and so on.
Career Scope: Materials Engineering vs. Environmental Engineering
As a materials engineer, one can work in technical areas research and development, and manufacturing. One can also enter managerial roles in sales, marketing, consultation, or entrepreneurship. The roles available for Materials Engineer are -
You can work in the transport industry, universities, space research organisations, mining industry, manufacturing industry, or FMCG companies to name a few. They can become an entrepreneur who manufactures clean and environment-friendly substitutes for harmful or expensive materials. Environmental Engineers work in roles such as -
Environmental engineers can work with non-government organisations, international environment conservation organisations and government bodies, they are in demand with the corporate social responsibility teams of multinational companies. They can work with financial institutions and law firms as expert consultants.
Sustainable development, sustainable manufacturing, clean energy sources, and recycling are strong terms and there is ample scope for engineers to contribute towards conservation and sustainability.
Both Materials Engineers and Environmental Engineers provide solutions for responsible development through innovative engineering solutions. If you feel strongly about conservation and environment protection, then merge your passion and talents to create actionable solutions as an engineer.
Engineering is the application of science to amend the problems of real-life world problems that make day-to-day life a smoother process. Software engineering and Data Science engineering are two engineering branches of the new world. Software engineering is the field of science that deals with the systematic approach to the development, maintenance, and innovation of software. The course of B-Tech Software Engineering is designed to equip students to use various programming and software technologies to create scalable and reliable applications for the advancement of the world.
Data Science Engineering is a highly integrated field with a flexible approach to its purpose with respect to the industry chosen to work with. In short, Data Science Engineering helps with meaningful and adequate extraction of data and analysis of metrics with the respective requirement. The curriculum of Data Science Engineering is comprehensive after considering the industry's emerging needs and demand.
Software Engineering vs. Data Science Engineering: Course Duration and Eligibility
Software Engineering and Data Science Engineering are professional courses and the curriculum is designed for a span of 4 years. These four years are inclusive of theoretical classes, practical classes, internships, projects, and industrial visits.
The minimum eligibility criteria for enrolling in Software Engineering is passing Grade 12 or equivalent studies as accepted by the University with a percentage falling under the cut-offs.
The minimum eligibility criteria for enrolling in Data Science Engineering is passing Grade 12 or equivalent studies as accepted by the University with a percentage falling under the cut-offs.
Getting qualified for national engineering entrance exams like JEE is a plus criterion when considering the application for admissions.
Software Engineering vs. Data Science Engineering: Course Curriculum
The course Curriculum for the Bachelor of Technology in Software Engineering and Data Science Engineering is enhanced and extensive.
Below are the subjects learned throughout the course duration:
Software Engineering Course Curriculum:
Semester I
Semester II
Semester III
Semester IV
Semester V
Semester VI
Semester VII
Semester VIII
Data Science Engineering Course Curriculum
Semester I
Semester II
Semester III
Semester IV
Semester V
Semester VI
Semester VII
Semester VIII
Software Engineering vs. Data Science Engineering: Career Opportunities
Software engineering as well as Data Science Engineering, these professional courses are booming and promising multiple career opportunities. Listed below are a few among the numerous career opportunities available:
Software Engineering Career Opportunities:
Data Science Engineering Career Opportunities:
In Short
After having gone through the course curriculum and other details of both subjects, it is understood that software engineering and data science engineering are two distinct in themselves but with certain cross-overs in specific areas. Both these professional courses are career-promising and in high demand in the industry for the pivotal role played by technology in almost all industries these days. The continuous progress and evolution of technology as a science and sector is indeed an insight into the subject’s existence in the world from a future perspective.

Aerospace Engineering and Biomedical Engineering represent two fascinating and distinct branches of engineering that cater to diverse aspects of human life and technological innovation. There are various career opportunities in these fields, which reflect their unique contributions to technological innovation and societal well-being, from aircraft design to healthcare device development.
Aerospace Engineering focuses on designing and developing aircraft and spacecraft, involving aerodynamics, propulsion systems, and flight mechanics. It explores the skies and beyond, contributing to aviation and space exploration. Aerospace Engineering fascinates students with the awe of flight, spacecraft, and cutting-edge technology. On the other hand, Biomedical Engineering merges engineering principles with biology and medicine to address healthcare challenges.
Course duration
Aerospace Engineering programmes typically span four years at the undergraduate level, with students undergoing a comprehensive curriculum covering aerodynamics, propulsion systems, flight mechanics, and spacecraft design. A master's in Aerospace Engineering can take an additional two years, offering specialisation in avionics, aerospace systems, or propulsion, among other options. A doctoral programme in Aerospace Engineering generally requires an additional 3-5 years, emphasising advanced research and the development of expertise in a specialised area.
Biomedical Engineering undergraduate programmes typically also last four years. The curriculum is designed to include engineering, biology and medicine principles with an overview of biomechanics, bioinformatics and medical imaging. A master's in Biomedical Engineering is usually for two more years, which allows the students to gain an increased familiarity with particular areas of health and medical device design or tissue engineering. Doctoral programmes in Biomedical Engineering, similar to Aerospace Engineering, can take 3-5 years, emphasising original research and advancing knowledge in a specialised area.
Curriculum
Aerospace engineers are focused on studying the behaviour of air and gases in motion, essential for designing aircraft and spacecraft with optimum efficiency and performance. They contribute to developing and producing engines and propulsion systems for aircraft and spacecraft to ensure that they comply with relevant performance and safety standards. The study of aerospace engineering also includes analysing flight dynamics, including the control and stability of aircraft and spacecraft during different operation phases. Core subjects of study include:
Biomedical engineers study the mechanics of the human body to figure out how forces and structures interact. This is essential for the design of prosthetic limbs and ophthalmological implants and knowledge of musculoskeletal systems. They use computational tools to analyse biological data and help synthesise genomics, medical imaging and drug discovery. They also study more advanced imaging technologies such as MRI, CT scan and ultrasound, contributing to disease diagnosis and treatment planning. Biomedical engineers also study artificial tissues and organs, merging principles of engineering and biology to address organ transplantation challenges. Core areas of study include:
Career opportunities
Aerospace engineers contribute to the design and manufacture of aircraft, which ensures that the latter meets safety and performance requirements as well as regulatory standards. Opportunities exist in the design and development of spacecraft for exploration missions, satellite systems, and space station components. Electronic systems for aircraft and spacecraft, such as navigation, communication systems or controls, are also worked on by aerospace engineers. Careers in research institutions involve pushing the boundaries of aerospace technology, exploring new materials, and enhancing propulsion systems. Potential career opportunities include:
In contrast, biomedical engineers are crucial in developing and manufacturing medical devices such as diagnostics tools, high-tech prosthetics or implants. They use their expertise in bioinformatics, genetics and tissue engineering to contribute to drug development in the pharmaceutical sector. Opportunities exist in research organisations focused on advances in medical technologies, genomics and regenerative medicine.
In the broader range of engineering, Aerospace Engineering involves designing and developing aircraft and spacecraft that require technical expertise in aeronautics, propulsion systems, and flight mechanics. Those interested in improving patient outcomes and investigating the complex nature of human bodies can choose Biomedical Engineering. Both Aerospace and Biomedical Engineering offer exciting opportunities for exploration and innovation in an evolving engineering landscape, whether one is drawn to the sky and beyond or is passionate about improving healthcare outcomes.

The demand for Engineering graduates has only grown over the years, prompting a drastic increase in students opting to pursue a Bachelor of Engineering (BE), Bachelor of Science (BS), Bachelor of Technology (B.Tech) or similar graduate programmes. If you find science and technology interesting, whether it is working with a screwdriver or mixing chemicals in a laboratory, you must consider Engineering for graduation. We will look at Electronics Engineering and Chemical Engineering in this blog.
Course duration and eligibility: Electronics vs. Chemical Engineering
To join an Engineering graduate programme, you can do a Diploma in Engineering after the 10th grade and then transfer to a graduate programme in the same course. Or, to qualify for an undergraduate engineering programme after high school, you must complete 12th grade with Physics, Chemistry, Mathematics and Biology or Computers as compulsory subjects. The minimum scores are 50% in the 12th board exams and appear for entrance exams such as CET, JEE, or GATE. For international colleges, you must appear for SAT and TOEFL or IELTS.
Available Courses: Electronics Engineering and Chemical Engineering
Depending on a student’s interest and aptitude they can choose either stream or opt for integrated courses with these subjects. Some options are –
|
Electronics Engineering |
Chemical Engineering |
|
Electrical and Electronics Engineering |
Biochemical engineering |
|
Electronics and communication engineering |
Chemical Engineering and Biotechnology |
|
Sound Engineering |
Material Science |
The BE/ B.Tech courses curriculum will include classroom time, lab time, theoretical exams, practical exams, viva voce, and projects. Some institutes also offer internship programmes.
Course Curriculum and Syllabus: Electronics Engineering and Chemical Engineering
Electronics engineering is the study of nonlinear and active electrical components for designing electronic circuits, integrated circuits, devices, and other equipment and systems. It is a branch of electrical engineering that deals with all types of consumer electronic devices, industrial electronics, or research-related electronic equipment. The subjects covered in Electronics engineering are Applied Physics, Mathematics, Electrical Engineering, Electronic Devices and Circuits, Engineering Linear, Engineering Drawing Laboratory, Digital Communication, Digital System, Mechanics of Engineering Design, Circuit and Networks, Control Systems, Instrumentation Systems, Computer organisation, Power Electronics, Micro Electromechanical Systems and Industrial Automation.
Chemical engineering is the study of ideas and techniques for transforming chemicals and raw materials into finished goods. These finished goods can be fuel, paint, textile fabric, or industrial raw materials. Chemical engineers understand the nature of chemicals and naturally occurring materials and how they can be used for solving problems such as developing technology to harness clean energy, increasing food production or making essential goods for society. The subjects studied in a chemical engineering course are Engineering Mathematics, Engineering Physics, Engineering Chemistry, Engineering materials, Fluid mechanics, Mechanical operations, Instrumental methods for analysis, Chemical Engineering, Thermodynamics, Mathematics, Heat Transfer, Optimisation Techniques, Equilibrium, Staged Operations, Polymer Technology, Diffusional Mass Transfer Operations, Statics and Strength of Materials, Process Dynamics and Control, Modelling, Computer simulation & Optimisation, Chemical Technology and Membrane Separation Technology.
Scope after graduation: Electronics Engineering and Chemical Engineering
With graduation in electronics engineering, you can consider a post-graduate course with a specialisation in –
You can consider careers with MNCs, academics, and public sector organisations. You can work in roles such as –
You can look at job opportunities in research and development, consumer electronics manufacturing companies, the telecommunication industry, defence organisations, IT and software companies, space research companies, and other similar companies.
Scope after graduation in Chemical Engineering
After graduation, you can choose a postgraduate course with specialisation in domains such as –
You can work in roles such as -
You can work in industries such as plastic, rubber, textile, chemical manufacturing, petroleum industry, fertiliser, or aerospace industry.
Both electronics and chemicals are interesting fields with incredible scope and interesting opportunities. You can also consider pursuing a management or entrepreneurship programme and building a business in the chemical or electronics fields.
A recent survey claimed that civil engineering witnessed a job growth of 15%, while computer engineering accounted for 16% in the last two years. LinkedIn also mentioned that these two engineering disciplines are one of the top career choices in India and abroad. Civil engineering involves the planning and supervision of infrastructure projects like roads, bridges, airports, and water systems. On the other hand, computer science engineering focuses on designing algorithms and software. Both disciplines involve critical thinking and problem-solving and offer rewarding career opportunities across different fields.
While both disciplines have their own unique benefits and opportunities, civil engineering tends to be more physically demanding than computer science. This means that civil engineers frequently involve themselves in physically demanding tasks such as architectural projects, construction management, land surveying, and transportation engineering. Conversely, the majority of computer science engineers work in areas that are not physically strenuous, such as software developers, database administrators, and web developers. In addition to this contrast, there are other characteristics that set these engineering disciplines apart. Today, we shall explore these two core disciplines and help make an informed career choice!
Civil Engineering vs. Computer Science Engineering: Duration and Eligibility
The undergraduate (UG) programmes offered in civil engineering and computer science engineering include a Bachelor of Engineering (B.E) and a Bachelor of Technology (B.Tech) respectively. The duration of both of these UG degrees is four years, divided into eight semesters. Students can pursue higher education by opting for a Master of Engineering (M.E) or a Master of Technology (M.Tech) in the respective fields. The duration of these post-graduate (PG) programmes is 2 years, split into 4 semesters.
The eligibility criteria to enrol in engineering courses require successful completion of 10+2 from a recognised board with a minimum of 50% marks. Moreover, students are encouraged to focus on subjects like mathematics, physics, and chemistry during their high school education. Admission to prestigious engineering colleges typically necessitates a satisfactory score in national entrance exams like the Joint Entrance Examination (JEE) or state entrance exams such as the Consortium of Medical, Engineering, and Dental Colleges of Karnataka (COMEDK), among others. For admissions in PG programmes, students need to hold 50% of their bachelor degree, followed by scoring cut-off marks in the Graduate Aptitude Test in Engineering (GATE) exam.
Civil Engineering vs. Computer Science Engineering: Curriculum
Civil engineering encompasses the field of planning, constructing, and maintaining critical infrastructure, including highways, bridges, canals, dams, airports, sewage systems, railway systems, and more. Students leverage their expertise in mathematics, science, and engineering to confront challenges and develop durable and efficient structures. Essential components of the curriculum include disciplines like structural engineering, geotechnical engineering, transportation engineering, environmental engineering, and construction management. Beyond theoretical knowledge, students frequently participate in industrial training and on-site projects. The civil engineering curriculum is meticulously crafted to equip students with the knowledge and skills required to tackle a wide range of challenges in the field, from smaller-scale structures to large-scale infrastructure projects.
Computer Science Engineering (CSE) is an academic programme that blends the fields of computer engineering and computer science. The CSE curriculum covers a diverse range of subjects, with a strong focus on computer programming and networking. Throughout the course, students explore various topics, including computation, algorithms, programming languages, programme design, computer software, computer hardware, and more. CSE students engage with various aspects of computing, spanning from the intricate design of microprocessors and supercomputers to circuit design and software development. Students also gain exposure to advanced concepts in artificial intelligence, machine learning, and cybersecurity. The curriculum often integrates experiential learning through coding assignments, projects, and internships.
Civil Engineering vs. Computer Science Engineering: Career Opportunities
Civil engineering plays a significant role in developing a region's infrastructure, rendering it one of the most highly demanded courses in India. Following their graduation, students can work in both the private and public sectors, engaging in construction projects and upholding rigorous safety standards. Students can also specialise in specific domains like geotechnical or design engineering or take on managerial roles within the field. Students can work as surveyors, responsible for measuring and recording property boundaries and locations to establish building site specifications. Additionally, students can explore a career role as a CAD technician, utilising computer-aided design software to plan projects. Building engineering is another prominent career choice where students apply their extensive knowledge of heating and cooling systems to ensure compliance with local fire and building codes. Water hygiene engineers work in water treatment plants, overseeing system operations and treatment protocols. Students can also pursue careers as urban planners, where they collaborate with public officials, developers, and communities to create land development strategies.
In the era of increasing dependence on digital technology, computer science engineers lead the way in innovation and addressing challenges. The rising prevalence of smartphones and the Internet of Things has further increased the demand for computer science engineers. Opting for a profession in CSE equips students with the technology, analytical, and communication skills required to transition to various other tech-related occupations. After graduation, students can work as multimedia programmers, responsible for writing code to ensure video, animation, and graphics work seamlessly. Students can also consider a career as a technical support specialist, where they collaborate closely with end-users to troubleshoot and resolve hardware, software, and technical issues. Web developers are tasked with the design, construction, and maintenance of websites and web applications, employing a variety of technologies and programming languages. Furthermore, students can work as forensic computer analysts, using specialised software and methodologies to investigate and secure data associated with criminal activities. Lastly, students can opt for the position of a computer programmer, responsible for transforming software designs into code and developing operating systems (OS) and software applications.
Way Forward
In summary, the recent job market statistics indicate a strong demand for both civil engineering and computer science engineering. These disciplines are not only highly sought-after in India but also offer promising career opportunities globally. When considering a career in either field, students must assess their preferences, strengths, and aspirations. Both civil engineering and computer science engineering offer undergraduate and postgraduate programmes, with specific eligibility criteria and entrance examinations. The civil engineering curriculum emphasises infrastructure planning and development, while computer science engineering covers a broad spectrum of subjects, including programming, networking, and advanced technologies. The choice between civil engineering and computer science engineering should align with students’ interests and career goals, as both fields provide ample opportunities for personal and professional growth!

According to the U.S. Bureau of Labor Statistics, by 2029, there is an anticipated growth of 11% in the employment opportunities in computer engineering professions. The deployment of 5G networks and the advancement of 5G-compatible devices are causing a huge demand for electronics and telecommunications engineers on a global scale.
The tremendous growth of computer engineering and electronic engineering is inspiring numerous students to pursue a career in these two domains. Computer engineering covers the intricate fusion of hardware and software that powers our computing devices. On the other hand, electronics engineering explores the vast landscape of electronic circuits, components, and systems. Both fields play a crucial role in advancing innovation, however, they specialise in different segments of the technological landscape. In this blog, we will dive deep into each discipline to help identify which course is the ideal choice for you.
Courses, Certification, and Duration
In the field of computer engineering, you can opt for undergraduate (UG) programmes such as Bachelor of Engineering (B.E) and Bachelor of Technology (B.Tech) in computer engineering. Both the UG programmes have a duration of 4 years, organised into 8 semesters. Furthermore, you can pursue a Master's degree in this field, which is a 2-year course divided into 4 semesters.
Conversely, if you are interested in pursuing a career in electronics engineering, there are two undergraduate options available: Bachelor of Engineering (B.E) and Bachelor of Technology (B.Tech) in electronics engineering. Each of these options have a 4-year duration, followed by a 2-year postgraduate degree programme in the respective stream.
Additionally, you can augment your earning potential, expertise, and career opportunities by pursuing further licensure and training. Some companies may require electronic or computer engineers to hold specific certifications or licenses, so it is advisable to review the prerequisites of the company you wish to join. For instance, as an electronic engineer, you can obtain additional certifications through organisations like the International Society of Certified Electronics Technicians (ISCET) or the Electronics Technicians Association (ETA). In the case of computer engineering, you can expand your qualifications through various online certification programmes encompassing hardware, software, networking, and related fields.
Course Curriculum
The curriculum for computer engineering comprises a wide spectrum of subjects that pertain to both computer hardware and software systems. You will dive deep into subjects such as digital logic design, microprocessor systems, computer architecture, and computer organisation. You will also study the programming languages, algorithms, data structures, and software engineering principles. To ensure a well-rounded education, mathematics and physics courses are often included to provide a solid theoretical foundation for the field. Additionally, you may explore specialised areas such as computer networks, embedded systems, and artificial intelligence. Hands-on practical experience is a vital component, involving laboratory work and internships. This comprehensive curriculum equips you with the knowledge and skills required to design, develop, and maintain both hardware and software components of computing systems..
On the other hand, the electronics engineering curriculum is tailored to impart you with the knowledge and skills essential for working with electronic circuits, devices, and systems. The curriculum encompasses fundamental subjects like circuit theory, analog and digital electronics, and semiconductor devices. You will gain insights into electromagnetic fields, signal processing, and control systems, establishing a strong foundation in electrical engineering principles.In addition to these core subjects, you will often study microelectronics, digital signal processing, and embedded systems. The curriculum may also include courses in communication systems, power electronics, and robotics, depending on the programme's specialisation. You will gain practical experience through hands-on laboratory work and projects. This comprehensive curriculum prepares you to design, analyse, and troubleshoot electronic systems, making it essential for today's technology-driven world.
Future Scope
The future scope of computer engineering is incredibly promising and dynamic. With the increasing integration of technology into various aspects of our lives, you will play a crucial role in developing innovative solutions. Areas like artificial intelligence, cybersecurity, data science, and the Internet of Things (IoT) present enticing career prospects for computer engineers. Furthermore, the expansion of cloud computing, mobile technology, and software development guarantees a diverse array of opportunities in both hardware and software fields. As industries become increasingly reliant on automation and digital systems, you will be at the forefront of creating cutting-edge applications. Moreover, the growth of cloud computing, mobile technology, and software development ensures a wide range of options in both hardware and software domains.
The future scope of electronics engineering is marked by a wealth of exciting and evolving career opportunities. Fields like integrated circuit design, renewable energy systems, and telecommunications offer compelling career prospects for electronics engineers. With the increasing emphasis on sustainability, electronics engineers specialising in green technologies and energy-efficient systems are in high demand. The emergence of 5G technology and the proliferation of the Internet of Things (IoT) offer career roles for engineers in the development and enhancement of communication systems. Additionally, progress in the field of medical devices and automation technology has enabled the electronics engineers to pioneer innovations in the healthcare and manufacturing industries.. The role of electronics engineering is integral to developing new electronic components and systems that drive progress in various industries.
Way Forward
The fields of computer engineering and electronics engineering hold promising career avenues in the field of technology. These two disciplines offer unique pathways, each with its own set of opportunities and areas of specialisation. Computer engineering covers both hardware and software systems, while electronics engineering focuses on electronic circuits, semiconductors, and practical applications. Future prospects are bright, with computer engineers driving innovations in AI, cybersecurity, and software development. Conversely, electronics engineers play a key role in the development of integrated circuits, renewable energy solutions, and 5G telecommunications. Irrespective of the path chosen, both of these engineering disciplines provide an opportunity to be at the forefront of innovation, actively shaping the future of technology in distinctive and meaningful ways.
Are you passionate about pursuing a career in designing and construction? If so, both civil engineering and architectural engineering are promising career avenues. These esteemed fields are involved in the creation of diverse structures, ranging from buildings and roads to bridges and dams. However, while their shared focus on construction may seem similar, these two disciplines possess features that sets them apart. If you are curious to know which is the right course, read on!
Course Focus and Duration
Architectural engineering encompasses conceptualisation and arrangement of structures such as buildings, industrial facilities, art galleries, sports arenas, corporate towers, and more. The courses available in this discipline are Bachelor of Engineering (B.E.) and Bachelor of Technology (B.Tech) in architectural engineering. Both of these undergraduate (UG) degrees are four years long, divided into eight semesters. You can also pursue a 2-year Master degree in relevant domains if you are interested in higher education.
Civil engineering is a broader field that deals with the planning, design, construction, and maintenance of various infrastructure projects. These are large-scale projects such as roads, bridges, dams, tunnels, and water supply systems. You can pursue a UG degree in this field by opting for B.E or B.Tech in civil engineering followed by a master degree. The duration of the UG programmes is 4 years, while that of a master degree is 2 years.
Course Curriculum
The curriculum of architectural engineering comprises core subjects such as mathematics, physics, and basic engineering principles. The courses cover the principles of architectural design, including concepts of aesthetics, space planning, and functional design. You will learn about the various building systems, structural systems, HVAC (heating, ventilation, and air conditioning), electrical systems, and plumbing. Environment management is also a crucial component of the curriculum that deals with sustainable design, energy efficiency, and indoor air quality. You may need to participate in internships, industrial visits, and projects as a part of the curriculum’s practical learning experience.
Civil engineering, on the other hand, covers basic engineering concepts and structural engineering. You will learn to design and analyse various structural elements, such as bridges, buildings, and others. Geotechnical engineering and transportation engineering are two important topics covered in a civil engineering curriculum. While the former teaches about soil mechanics and geotechnical principles, the latter focuses on topics like hydrology and water supply systems. Similar to architectural engineering, civil engineering often includes environmental subjects, covering topics like wastewater treatment and environmental impact assessment. Additionally, you need to attend internships and workshops to learn about construction methods, project management, and cost estimation.
Career Opportunities
Architectural engineering offers a range of compelling career opportunities in areas of architectural design and engineering techniques. After graduation in this field, you can work for design firms, construction companies, and public agencies. One primary career path is that of an architectural engineer, where you will work closely with architects to ensure that building designs are both aesthetically pleasing and structurally sound. Architectural engineers are involved in the design and integration of building systems such as HVAC, electrical, and plumbing. Moreover, you will play a significant role in improving energy efficiency and sustainable building practices. Other career options include working in construction management, where you oversee projects from concept to completion, ensuring they meet safety standards and design specifications. With the increasing focus on green building practices, you can also specialise in promoting eco-friendly building solutions.
Civil engineering is a diverse field that presents a wide array of career opportunities after graduation. You can work as a civil engineer, responsible for the planning, design, construction, and maintenance of infrastructure projects. You will be highly sought after by government agencies in the public sector to manage large-scale public works projects. Private consulting firms will also hire you to provide specialised services to a variety of corporate clients. Some civil engineers become structural engineers, focusing on the design and analysis of buildings and other structures. Geotechnical engineers deal with the mechanics of soils and foundations, ensuring the stability of structures. Transportation engineers work on transportation systems, including traffic management and road design. Additionally, you can also work as a water resources engineer, dealing with projects related to water supply, and wastewater treatment.
Which One to Choose?
So far, you have understood the intricacies of each discipline. However, when considering the choice between architectural and civil engineering, it is important to understand that there isn't a definitive "better" option. You should opt for the courses based on your preferences and long-term goals. If your passion lies in the design and planning of traditional structures, architectural engineering is a suitable option. If you are inclined towards an office-based role and prefer not to engage directly in the construction process, you must pursue this engineering!
On the other hand, if you want to engage in every stage of construction, civil engineering is a recommended pathway. Civil engineering offers a dynamic career that combines office work with hands-on field experience. Therefore, you must carefully assess your individual interests and career objectives before making the final call!

The future of mechatronics and robotics in India and around the world appears promising and dynamic. The potential of both these domains is propelled by rapid technological advancements, a constant need for automation, and the call for innovative solutions across various sectors. As manufacturing and production processes become progressively automated, the demand for skilled professionals in industries such as automotive, electronics, and pharmaceuticals is set to continually expand. Recent emphasis by a defense council has underscored the critical role of mechatronics and robotics in India and globally, particularly in operating unmanned aerial vehicles (UAVs), bomb disposal robots, and surveillance drones for both national and international security.
While the term 'robotics' is familiar to many, 'mechatronics' might be less well-known. Mechatronics is an emerging engineering discipline that is gaining traction in response to the growing automation of tasks previously carried out by humans. This engineering discipline focuses on the principles behind creating and producing automated machinery. Robotics is often considered a subset of mechatronics engineering; however, these two are considered separate disciplines in general. Let us delve further into these two engineering fields and understand which is a better career in automation:
Mechatronics vs. Robotics: Course Duration and Eligibility
The undergraduate (UG) courses offered in mechatronics are a Bachelor of Engineering (B.E) and a Bachelor of Technology (B.Tech) in mechatronics. These two specialised UG programmes have a duration of 4 years, divided into 8 semesters. As far as post-graduation (PG) is concerned, students can pursue a Master of Engineering (M.E) and a Master of Technology (M.Tech) in mechatronics. The duration of these PG courses encompasses 2 years, split into 4 semesters. Besides these courses, there are other 1-year diploma courses in mechatronics in India, including automation systems, CAD/CAM, and electrical systems.
Robotics, on the other hand, offers UG courses such as B.E and B.Tech in robotics, respectively, each entailing a duration of 4 years and 8 semesters. Additionally, students can also pursue a Master degree in a relevant field, which consists of a duration of 2 years, divided into 4 semesters. There are other diploma courses in the field of robotics, encompassing a duration of one year. The specialisations offered by these diploma courses include industrial robotics, mobile robotics, and medical robotics.
Admissions to UG mechatronics and robotics programmes are determined after attaining the benchmark score from either of the entrance examinations and merit lists. Entrance exams such as Joint Entrance Examinations (JEE) (Main and Advanced) and JoSAA Counselling are administered to secure admission to IITs, NITs, IIITs, and GFTIs. State-level entrance exams are organised for admission to government engineering colleges or universities at the state level. To gain entry into private engineering courses, students can utilise state-level entrance exams, direct admission, or management quota options. For admission to deemed universities, either JEE Main or university-level entrance exams are conducted. Furthermore, students must have completed their Class XII education at a school affiliated with a recognised board and obtained a minimum of 50% marks in the science stream.
Mechatronics vs. Robotics: Course Curriculum
Mechatronics is a multi-disciplinary domain that combines aspects of mechanical engineering, electronics, and computer science. This engineering field focuses on blending mechanical and electronic systems to produce intelligent and automated products and procedures. Students learn about different topics such as mechanical design, electronics and circuits, microcontroller programming, and control systems. To bridge theory with practice, mechatronics programmes often emphasise internships and practical training. These internships provide students with valuable hands-on experience in real-world engineering settings. Practical training may encompass working with industrial automation systems, electronic components, and integrated control systems.
Conversely, robotics is a specialised branch of mechatronics that primarily focuses on the design, construction, and programming of robots. While robotics is a part of mechatronics, it has a more specific focus on creating robotic systems. The curriculum of a robotics course covers topics such as robot kinematics, dynamics, sensor integration, and robot programming. Students often engage in internships or cooperative experiences with companies or research institutions specialising in robotics. These opportunities expose students to the intricacies of robotic design and operation, and they may involve hands-on work with various types of robots, such as industrial robots, autonomous vehicles, or robotic arms.
Mechatronics vs. Robotics: Career Opportunities
The growth of industrialisation has led to a notable upsurge in the requirement for mechatronics specialists within a broad spectrum of industries. As sectors like automotive, aerospace, consumer electronics, and healthcare consistently expand and embrace automation, employers will perpetually seek out mechatronics professionals. With the growing focus on automation and robotics in manufacturing and logistics, there will be an increased demand for mechatronics engineers capable of developing and deploying automated systems and robots. A career in mechatronics offers abundant job opportunities across various sectors. Upon graduation, students can explore careers as mechatronics engineers, where they design, develop, and maintain complex automated systems, manufacturing processes, and robotic applications. Other roles include control systems engineering, specialising in the creation and management of integrated control systems that regulate machinery and processes. As the Internet of Things (IoT) gains prominence, there is a growing need for mechatronics experts to engage in IoT development, integrating sensors and data analytics into smart devices and industrial applications.
Conversely, the field of robotics also presents substantial career prospects, with a multitude of job openings spanning various industries. With the expanding utilisation of automation and intelligent systems in fields as diverse as manufacturing, healthcare, logistics, and space exploration, the demand for robotics professionals is on a continuous upswing. Robotic engineers and specialists design, build, and programme robotic systems, whether for industrial automation, autonomous vehicles, or medical applications. Upon graduation, students can advance their career as robotics software engineers, responsible for developing the software and algorithms that control and coordinate robotic systems. Another interesting career avenue is that of an autonomous vehicle engineer, designing self-driving vehicles and related technologies, such as sensors and computer vision systems. Students can also pursue a career as robotic process automation (RPA) developers, responsible for creating automated software bots that mimic human actions. Lastly, students can also become human-robot interaction (HRI) designers, developing user-friendly interfaces and interactions between humans and robots in applications like customer service or healthcare.
Mechatronics vs. Robotics: A Way Forward
The oscillating demand for automation and innovative solutions has elevated mechatronics and robotics as appealing career pathways in India and abroad. Mechatronics, a rising discipline, combines mechanical, electronic, and computer engineering, offering multidisciplinary expertise. Meanwhile, robotics focuses on designing, building, and programming robotic systems for various applications. As students explore these fields, they can expect diverse and engaging career opportunities across industries like aerospace, healthcare, and others. The students’ expertise in developing and maintaining automated systems and robotic applications is indispensable in today’s evolving landscape. Therefore, students should align their areas of interest and explore careers in robotics software engineering, autonomous vehicle engineering, and various other disciplines.

A survey by a reputed university found that several students are opting for psychology and computer science majors for their undergraduate degrees in India. Factors such as societal pressures, digital connectivity, and global events like the COVID-19 pandemic have contributed to the demands of psychologists in recent times. Conversely, technological advancements that have revolutionised sectors such as healthcare, finance, transportation, and entertainment have created opportunities for lucrative careers in the field of computer science. If you are contemplating which course aligns best with your aspirations, today we will conduct an in-depth examination of each discipline, shedding light on the distinctions between them!
Psychology vs. Computer Science: Course Duration
In the field of psychology, undergraduate (UG) programmes include Bachelor of Psychology (B.Sc), a specialised 3-year degree programme. You also have the option to pursue higher education with a Master of Science (M.Sc) in the same field, which is a 2-year course. Additionally, there's the opportunity to apply for a Master of Philosophy (M.Phil), a 2-year academic research programme.
As for computer science, UG courses encompass the B.Sc in Computer Science and the Bachelor of Technology (B.Tech) in Computer Science. The former spans 3 years, while the latter covers 4 years, divided into 8 semesters. Furthermore, post-graduation (PG) options in this field include M.Sc. and M.Tech in Computer Science, respectively. The duration of these two PG courses is two years.
Psychology vs. Computer Science: Course Curriculum
The curriculum of psychology explores scientific areas of human behaviour and mental processes. The programme explores various facets of the mind, including emotions, cognition, behaviour, and underlying psychological processes. The syllabus covers fundamental subjects such as an introduction to psychology, research methods in psychology, biological psychology, developmental psychology, cognitive psychology, and social psychology. Additionally, the curriculum covers other essential areas like statistics for psychology, experimental psychology, psychopathology, behavioural neuroscience, and more.
On the contrary, computer science programs concentrate on the study of algorithms, data structures, computation, and the design and evaluation of software and hardware systems. The course also encompasses the theoretical and practical aspects of computer technology. The primary subjects covered in a computer science curriculum include an introduction to computer science, programming fundamentals, data structures and algorithms, computer architecture, operating systems, database management systems, and software engineering. Furthermore, the course delves into topics such as object-oriented programming, web development, networks and data communications, cybersecurity, artificial intelligence, and machine learning.
Psychology vs. Computer Science: Career Opportunities
A career in the field of psychology helps you gain insights into human behaviour, develop therapeutic skills, and cultivate empathy and active listening. Throughout the programme, you will also develop competence in research methodologies, statistical analysis, and ethical principles. Learning these skills will help you forge a rewarding career in both clinical practice and scientific research. Upon completion of your studies, you can pursue roles as clinical psychologists, counsellors, and therapists within settings such as hospitals, clinics, rehabilitation centres, and private practices. There's also the opportunity to serve as educational counsellors in schools, colleges, and universities, aiding in the support of student's academic and emotional well-being. Additionally, you can take on the role of a forensic psychologist, assisting in criminal investigations, working in correctional facilities, and providing expert testimony in legal proceedings. As trained psychologists, you can also pursue research and teaching careers in universities, research institutions, and academic publishing.
As computer science experts, you will develop proficiencies in programming, software development, algorithms, and problem-solving capabilities. In addition to these competencies, you will also gain expertise in domains like cybersecurity, artificial intelligence, and data analytics. Your domain knowledge and experience will pave the way for rewarding career opportunities in the areas of technology solutions and addressing complex computing challenges. Lately, computer scientists and engineers are in demand in the tech industry, working for companies ranging from startups to tech giants. The financial institutions also employ computer scientists for algorithmic trading, risk assessment, and financial software development. Given the rising occurrence of cyber threats, there is a growing demand for cybersecurity experts who can safeguard data and systems across various organisations. Moreover, as businesses transition to cloud-based operations, there will also be a surge in the need for cloud architects and engineers to design and oversee cloud infrastructure.
Conclusion
Psychology and computer science present promising career pathways across diverse industries. While a degree in psychology programmes equips individuals with deep insights into human behaviour, a computer science programme renders expertise in programming algorithms and technology solutions. Upon graduation in psychology, you can utilise your clinical skills and research proficiency to explore careers in clinical practice, counselling, and education. Conversely, the versatility of computer science knowledge will allow you to explore roles in software development, data analytics, and cybersecurity. Although distinct, both fields offer opportunities for personal growth, societal impact, and fulfilling careers in the rapidly evolving landscape of the 21st century.

Engineering has historically been a preferred career choice for many students worldwide due to its features like job stability, and high earning opportunities. The engineering programmes impart practical and skill-focused training that prepares the students for a bright future in the field of technology and innovation. Given the variety of programmes offered within the engineering courses, choosing the appropriate specialisation can often pose a considerable challenge. Our blog aims to delve into All India Council of Technical Education (AICTE) approved engineering specialisations, which can lead to a multitude of career paths.
Mechanical Engineering
Mechanical engineering utilises the principles derived from physics and mathematics to design, analyse, manufacture, and maintain mechanical systems and apparatus. This field of engineering caters to developing solutions for a diverse array of mechanical challenges. Mechanical engineering encompasses various domains of study, including machinery, engines, HVAC (heating, ventilation, and air conditioning) systems, manufacturing machinery, and more.
Civil Engineering
After military engineering, civil engineering is the second-oldest engineering branch in the world. Civil engineering applies physical and scientific principles to plan, construct, and sustain both human-made and natural environments. This field of engineering encompasses infrastructure such as airports, bridges, buildings, canals, power plants, railways, sewage systems, and others. Civil engineers employ scientific and engineering principles to develop secure, efficient, and sustainable infrastructure that fulfils community needs and bolsters economic growth.
Electronics & Communications Engineering
Electronics & Communications Engineering (ECE), commonly known as ECE, represents a specialised engineering branch dedicated to the examination, design, and application of electronic and communication systems. ECE emphasises diverse technologies, such as electronic circuits, microprocessors, telecommunications, and more. ECE graduates contribute to the development of communication devices and systems such as smartphones, satellites, radio and television broadcasting, and internet connectivity.
Electrical & Electronics Engineering
Electrical and Electronics Engineering (EE) constitutes a branch of engineering focused on the study, design, and application of electrical and electronic systems. EE Engineering encompasses a broad spectrum of technologies, covering aspects like electrical power generation, distribution, microelectronics, and digital systems. EE engineers engage in various applications, ranging from electrical grids and power networks to crafting electronic devices and integrated circuits.
Computer Science Engineering
Computer Science Engineering (CSE) specialises in the planning, implementation, and management of both software and hardware components within information systems. Computer science engineers tackle a diverse array of computing systems, encompassing activities such as designing software applications and algorithms, as well as maintaining computer hardware components. These engineers play a crucial role in developing cutting-edge technology in domains like artificial intelligence, cybersecurity, software development, and computer networking.
Information Science Engineering
Information Science Engineering focuses on the study, design, and application of information systems and technology. This engineering discipline focuses on managing and processing data, information retrieval, and the development of software to facilitate efficient information handling. Information Science Engineers work on designing databases, information systems, web applications, and data analytics tools. Information Science engineers play a vital role in managing and optimising the flow of information in various industries, such as healthcare, finance, and e-commerce.
Aerospace Engineering
Aerospace Engineering is an engineering specialisation aimed at developing aircraft and spacecraft. This discipline is bifurcated into two primary categories, aeronautical and astronautical engineering, offering comprehensive training in designing, fabricating, and maintaining aircraft, spacecraft, and missiles. Aerospace engineers engage in diverse aspects of aerospace technology, including aerodynamics, propulsion systems, materials, control systems, and structural design.
Food Technology
Food Technology, on the other hand, falls under the engineering branch and concentrates on aspects like food product manufacturing, preservation, quality assurance, and research and development. Food technologists are dedicated to enhancing and innovating food products, ensuring compliance with safety standards, nutritional requirements, and consumer preferences. These professionals employ a wide array of techniques and technologies to create new food items, refine food processing methodologies, and extend product shelf life while upholding quality and safety standards.
Biotechnology Engineering
Biotechnology combines biology and technology for practical applications to develop innovative products and solutions. This field of engineering is often branched into different specialisations such as genetic engineering, agricultural biotechnology, medical biotechnology, and others. Graduates in biotechnology engineering play a vital role in improving agriculture practices, environmental conservation and waste management. Biotechnology is a dynamic and impactful discipline with applications spanning healthcare, agriculture, industry, and the environment.
Biomedical Engineering
Biomedical Engineering is a multidisciplinary field of study that combines engineering principles in healthcare settings. The application of this field includes creating prosthetic limbs, medical imaging devices, artificial organs, and healthcare software. Biomedical Engineering plays a vital role in advancing medical technology, improving patient outcomes, and enhancing healthcare delivery. Biomedical engineering bridges the gap between engineering and healthcare, fostering innovations that save lives and enhance quality of life.
Chemical Engineering
Chemical Engineering applies principles of chemistry, physics, and mathematics to design and optimise processes for producing chemicals, materials, and energy. This branch of engineering plays a crucial role in various industries, namely, pharmaceuticals, petrochemicals, food, and energy production. Chemical engineers develop processes for manufacturing products like pharmaceutical drugs, plastics, and fuels efficiently and sustainably. These experts work extensively towards environmental protection and safety in handling hazardous materials.
Summing Up
In conclusion, engineering is a promising career choice that offers opportunities across different industries. Engineering programmes provide students with practical, skills-focused training, positioning them for a promising future in technology and innovation. However, the diversity of engineering specialisations can present a significant challenge when it comes to choosing the right path. With AICTE-approved specialisations such as mechanical, civil, electronics & communications, computer science, aerospace, and others, students can remain at the forefront of shaping the future of technology and infrastructure.
A survey by NASSCOM reveals that around 15 lac engineering students graduate every year in India. This data is a testament that engineering has been one of the popular career choices for Indian students for a long time. We can see the impact of engineering around us, starting from the creation of a satellite to the mechanics inside our smartphones. Engineering is one such field that always empowers the development and maintenance of all technological innovations that influence our daily existence. Its ever-increasing popularity in our daily lives makes engineering a great field to explore diverse careers.
Amidst a multitude of specialisations available to pursue in the field of engineering, one may wonder which is the right engineering for them. Most of the time, students might find themselves at a critical juncture trying to choose between two major engineering disciplines, viz., mechanical engineering and electrical engineering. If you are one of them, this article is just for you!
In this article, we shall delve into these two disciplines to help you determine the most suitable career pathway!
Mechanical Engineering vs. Electrical Engineering: Course Duration
The undergraduate (UG) courses offered in mechanical engineering include a Bachelor of Engineering (B.E) in mechanical engineering and a Bachelor of Technology (B.Tech) in mechanical engineering. Both of these UG programmes have a course duration of 4 years, further divided into 8 semesters. You can pursue post-graduation by opting for a Master of Engineering (M.E) or a Master of Technology (M.Tech) in the same field, which is a 2-year course split across 4 semesters.
The UG programmes offered in electrical engineering include a B.E or B.Tech in electrical engineering. Both of these courses span 4 years, further divided into 8 semesters. To pursue higher education, you can opt for an M.E or M.Tech in electrical engineering, which is a 2-year course divided into 4 semesters.
Mechanical Engineering vs. Electrical Engineering: Course Curriculum
Pursuing a mechanical engineering degree provides you with expertise in the intricacies of designing, analysing, producing, and maintaining mechanical systems and components. You also develop an understanding of mechanics, materials, thermodynamics, and fluid dynamics. Besides theoretical exposure, the curriculum also nurtures practical learning through internships, onsite project visits, experiments, and so on. The core subjects included in a mechanical engineering curriculum include:
On the other hand, electrical engineering fosters expertise in circuit design, control systems, digital electronics, and signal processing. You will learn to work with software for simulation and programming microcontrollers for embedded systems. Just like mechanical engineering, this course also exposes you to practical learning through experiments, internships, and projects. The core subjects included in an electrical engineering curriculum include:
Mechanical Engineering vs. Electrical Engineering: Career Opportunities
After completing their mechanical engineering degree, graduates can discover attractive employment prospects in diverse sectors, such as aerospace, automotive, and renewable energy industries. Employers will highly value their abilities and proficiency in designing and creating products like engines, HVAC systems, turbines, and mechanical components for a wide range of applications. Let us see some of these career prospects in the field of mechanical engineering:
Industries today need experts who can design and develop electrical systems and electronic devices in this rapidly evolving business landscape. Therefore, after graduation, you can find rewarding career opportunities in the fields of electronics, telecommunications, computer hardware, and others. Let us see some of these career prospects in this domain:
Mechanical Engineering vs. Electrical Engineering: Final Thoughts
To summarise, both the fields of mechanical and electrical engineering offer ample career advancement opportunities. However, you must choose the path after assessing their area of interest and future aspirations. While electrical engineering demands strong mathematical skills and an interest in computer programmes, mechanical engineering emphasises calculus and trigonometry. Hence, if you have a curiosity to learn about electricity and electronics and better knowledge of physics, a profession in electrical engineering could be the perfect fit. Alternatively, if you are inquisitive about understanding the functioning of vehicles, media devices, or robotics, then embarking on a career in mechanical engineering is the most suitable decision!

One of the most confusing yet important decisions for students is to choose the right engineering stream!
Amidst the multitude of options prevalent, two most common streams emerge, i.e., civil and mechanical engineering. While civil engineering is concerned with the development of infrastructure around us, mechanical engineering explores areas of the design and operation of machinery. Today, in this blog, we shall understand the differences between these two areas of engineering!
Civil vs. Mechanical Engineering: Course Duration
The undergraduate (UG) course offered in civil engineering is a Bachelor of Technology (B.Tech) in civil engineering. This programme has a duration of 4 years, further classified into 8 semesters. Additionally, students can pursue a Master of Technology (M.Tech) in civil engineering. This post-graduate programme with course duration of 2 years, split across 4 semesters. Students can also pursue higher education in the same field by opting for a Doctor of Philosophy (Ph.D).
In mechanical engineering, the UG programme entails a B.Tech. in the same field, which has a duration of 4 years, divided into 8 semesters. Students can also pursue higher education by enrolling on a master's programme, which is a 2-year course. Similarly, students can also pursue a Ph.D. in mechanical engineering, with a total duration of one year.
Civil vs. Mechanical Engineering: Course Curriculum
Civil engineering curriculum imparts knowledge on the design, development, and maintenance of large-scale infrastructure. Besides theoretical exposure, the curriculum also ensures that students gain practical experience through internships, industrial projects and case studies. The core subjects included in a civil engineering curriculum consist of geotechnical engineering, mathematics, civil mechanics, structural analysis and design, hydraulics, transportation engineering, environmental engineering, geomatics, and others.
The curriculum of mechanical engineering is a combination of theoretical and practical exposure. While the theory part focuses on the design, analysis, and manufacturing of mechanical systems and devices, students gain experiential learning through experiments, case studies, and internships. The core subjects included in a mechanical engineering curriculum consist of engineering mathematics, engineering mechanics, thermodynamics, fluid mechanics, heat transfer, material science and engineering, machine design, the dynamics of machinery, manufacturing processes, mechanical vibrations, and others.
Civil vs. Mechanical Engineering: Career Opportunities
Civil engineering offers exciting career advancement opportunities across different industries. Upon graduation, students can work on the construction of buildings, bridges, roads, and infrastructure projects. They can also work in the transportation industry to design and manage transportation systems. Let us see some of the promising career roles in this domain:
Construction engineers oversee construction projects, thereby ensuring that these projects are completed safely, on time, and within budget. Structural engineers design and analyse structures like buildings and bridges for stability and safety. Geotechnical engineers study soil and rock mechanics, which are essential for foundations and underground structures. Transportation engineers plan and design transportation systems, such as roads and public transit. Environmental engineers address environmental challenges such as water and air quality and sustainable development.
Mechanical engineering offers lucrative career opportunities for students across different sectors. After completing the course, students can explore diverse career opportunities in the manufacturing, aerospace and automotive industries. Let us see some of the top career prospects in this domain:
Mechanical engineers design and analyse mechanical components and systems using CAD software and engineering principles. Manufacturing engineers enhance manufacturing processes and ensure that the product maintains optimum quality and efficiency. Aerospace engineers develop aircraft, spacecraft, and related systems, ensuring that they meet safety, performance, and regulatory standards. Automotive engineers conceptualise, design and develop vehicles and their components They design, analyse, and optimise thermal solutions to ensure efficient heat dissipation, temperature control, and thermal performance.
Civil vs. Mechanical Engineering: Final Thoughts
Although both civil and mechanical are two branches of engineering and offer exciting career prospects in their respective domains, they are very different from each other. Expertise in structural analysis, construction management, hydraulics and AutoCAD are some of the key skills that students can learn in a civil engineering course. On the other hand, students will gain valuable knowledge and skills in areas such as mechanical design, thermodynamics and heat transfer, manufacturing processes, and fluid mechanics. Therefore, students must carefully analyse their area of interest and the type of expertise they want to develop before making the final call!

Although computer engineering and electrical engineering are both tech-driven fields that offer rewarding career opportunities, these are two completely distinct disciplines.
The field of computer engineering focuses on both hardware and software aspects of computing and specialises in areas such as microprocessors, embedded systems, and digital circuitry. On the other hand, the field of electrical engineering focuses on areas such as power generation, electronics, control systems, and telecommunications. Today, in this blog, we shall discuss the differences between these two technology titans. Read on to learn more!
Computer Engineering vs. Electrical Engineering: Course Duration and Eligibility
The undergraduate programmes offered in computer engineering include a Bachelor of Engineering (B.E) in computer engineering and a Bachelor of Technology (B.Tech) in computer engineering. The duration of these courses is 4 years each, divided into 8 semesters. The eligibility criteria to enrol for these programmes is to have a minimum of 60% marks (55% for SC/ST) in 12th PUC/ISC/CBSE or equivalent board with physics and mathematics as compulsory subjects with chemistry, electronics, computer science, and biology. Alternatively, students need to have a valid score from entrance exams such as the Joint Entrance Examination (JEE), Under–Graduate Engineering Entrance Exam (Uni-GAUGE), or the Consortium of Medical, Engineering, and Dental Colleges of Karnataka (ComedK). The students can pursue their postgraduation in this field by opting for a Master of Engineering (M.E) in Computer Engineering and a Master of Technology (M.Tech) in Computer Engineering, both of which have a duration of 2 years, split across 4 semesters.
The undergraduate programmes offered in electrical engineering include a B.E in electrical engineering and a B.Tech in electrical engineering. The duration of these courses is 4 years each, divided into 8 semesters. The eligibility criteria to enrol in these programmes is to have a minimum of 60% marks (55% for SC/ST) in 12th PUC/ISC/CBSE or equivalent board with physics and mathematics as compulsory subjects with chemistry, electronics, and computer science. Alternatively, students need to have a valid score from entrance exams such as JEE, Uni-GAUGE, or ComedK. The students can pursue their postgraduation in this field by opting for a Master of Engineering (M.E) in Electrical Engineering or a Master of Technology (M.Tech) in Electrical Engineering, both of which have a duration of 2 years, split across 4 semesters.
Computer Engineering vs. Electrical Engineering: Course Curriculum
The curriculum of computer engineering focuses on the design, development, and integration of computer systems and digital devices. On the other hand, the curriculum of electrical engineering explores a broader range of topics, such as the generation, transmission, and distribution of electrical power, as well as the design of electrical systems and devices. Both courses expose the students to a holistic education approach encompassing theoretical and practical learning experiences.
Core Subjects in Computer Engineering
Core Subjects in Electrical Engineering
Computer Engineering vs. Electrical Engineering: Career Opportunities
Upon graduation, students in computer engineering can find lucrative career opportunities in industries related to computer hardware and software development, embedded systems, networking, and consumer electronics. On the other hand, graduates in electrical engineering can pursue their careers in a wide range of industries, such as power generation and distribution, telecommunications, aerospace, automotive, and automation. Let us see some of the common job opportunities in each field:
Career Prospects in Computer Engineering
As organisations are relying on technological transformation to scale up their business processes, students with computer engineering knowledge and skills are highly valuable. With the rise of artificial intelligence, machine learning, the Internet of Things (IoT), and cybersecurity systems, there is a growing demand for computer engineering specialists across the country. Following are some of the high-demand career roles in computer engineering:
Career Prospects in Electrical Engineering
The rise of electrical appliances and renewable sources of energy has created a demand for specialists who can design and maintain the required systems. Moreover, professionals in this field have a stable demand in industries such as power generation, telecommunications, and electronics manufacturing. Following are some of the high-demand career roles in electrical engineering:
Computer Engineering vs. Electrical Engineering: Final Thoughts
To summarise, computer engineering emphasises programming languages and software design principles, whereas electrical engineering focuses on developing electrical and electronic systems. Both of these fields share distinct features and offer exciting career advancement opportunities for students. If a student is interested in learning programming, software development, and cybersecurity, then a career in computer engineering is recommended. On the other hand, if a student is interested in working on power systems, electrical systems, and renewable sources of energy, then they must pursue a career in electrical engineering. Therefore, a student must carefully assess their career aspirations and interests before making the final decision!
Engineering is one of the top degree choices for most students after completing their 12th pre-university in the science stream. Catering to this demand, there are two popular degree programmes that have emerged in the engineering domain, i.e., a Bachelor of Engineering (B.E) or a Bachelor of Technology (B.Tech).
Although these courses share several common aspects, they are very different educational models. A B.E curriculum is a theoretical model that focuses more on ideas and theories of engineering, whereas a B.Tech is more application-centric and caters to industry trends. Besides this crucial difference, there are several other factors that make both of these courses distinct from each other. Well, this brings us to the main question, ‘Which engineering degree should one choose? Today, we will explore the differences and help our readers make the right career choice!
B.E Vs B.Tech: An Overview
|
Parameters |
B.E |
B.Tech |
|
Focus |
B.E is a theoretical course that focuses on engineering principles and theories. |
B.Tech is a skill-focused course that emphasises hands-on learning and technological advancements. |
|
Industry Exposure |
May excel in research, teaching, or roles that require a strong theoretical background. |
May transition directly into industry roles due to practical training and up-to-date knowledge. |
|
Courses Offered |
B.E in Electrical Engineering, Chemical Engineering, Mechanical Engineering, and others. |
B.Tech in Civil Engineering, Mechanical Engineering, Computer Science and Engineering, Aerospace Engineering, and others. |
|
Eligibility |
60% score in Class 12th Science (with Mathematics as a subject). Additionally, need to clear the Joint Entrance Examinations (JEE) to apply for colleges. |
60% score in Class 12th Science (with Mathematics as a subject). Additionally, need to clear the JEE to apply for colleges. |
B.E vs B.Tech: Course Duration
The course duration for a B.E degree is four years, divided into 8 semesters. A student may also pursue a Master of Engineering (M.E) later, which is again a 2-year course programme.
The course duration for a B.Tech degree is also four years, split across 8 semesters. Individuals may pursue post-graduation by applying for a Master of Technology (M.Tech) in the relevant field. The M.Tech is a 2-year degree programme, divided into 4 semesters.
B.E Vs B.Tech: Curriculum
As already explained, a B.E is a theoretical and data-driven course, while a B.Tech focuses more on real-life applications. The curriculum for a B.Tech degree is regularly updated to align with market demands and trends, whereas the same is not applicable for a B.E degree. Industrial visits and internships are compulsory for a student in a B.Tech programme, whereas these are recommended but not mandatory in a B.E programme. Besides these differences, both have a different curriculum that sets them apart. Let us see some of the core subjects taught in each discipline:
There are different specialisations in a B.E programme such as mechanical, civil, electronic engineering and various others. Although the main curriculum may vary from one specialisation to another, the core subjects in covered in a B.E syllabus consist of Engineering Mathematics, Mechanics, Thermodynamics, Electromagnetism, Fluid Mechanics, Material Science, Structural Analysis, And Electronics, among others. Additionally, students also study Engineering Drawing, Manufacturing Processes, Control Systems, Circuits And Networks, Heat Transfer, and Environmental Engineering.
Similarly, there are various types of specialisations in a B.Tech programme such as computer science, aerospace, chemical, civil, mechanical engineering and many more. Despite the differences in the curriculum in each specialisation, the fundamental subjects covered in a B.Tech degree consist of Mathematics, Physics, And Chemistry. There are different branches of the B.Tech degree, such as Computer Science, Electronics, Electrical Engineering, Mechanical Engineering, Civil Engineering, and others, based on which the curriculum might change and differ.
B.E Vs B.Tech: Career Opportunities
Upon graduation, students can bag lucrative job opportunities across different industries. Let us see some of the common career opportunities in each field:
Career Prospects After B.E
B.E graduates are one of the most sought-after professionals in the technical world because of their ability to research and offer innovative solutions to complex challenges. We have listed some of the common career prospects students can pursue after completion of their B.E programme:
Electrical engineers focus on electrical systems, from power generation to electronics and telecommunications. Computer engineers design and develop computer systems, hardware, and software to meet various technological needs. Structural engineers specialise in designing safe and efficient structures like buildings and bridges. Automotive engineers focus on designing and improving vehicles and automotive systems. Manufacturing engineers optimise production processes to improve manufacturing efficiency.
Career Prospects After B.Tech
B.Tech graduates not only possess the theoretical knowledge but also have the necessary skills to design path breaking technical solutions. They are often at the forefront of digital innovation. We have listed some of the common prospects one can pursue after the completion of their B.Tech programme:
Civil engineers design and oversee the construction of infrastructure projects like buildings, bridges, and roads. Mechanical engineers are responsible for designing, testing, and manufacturing machinery and mechanical systems. Software developers create, test, and maintain computer software and applications. Aerospace engineers design and develop aircraft, spacecraft, and related technologies. Data analysts interpret and analyse data to help organisations make informed decisions.
B.E Vs B.Tech: Which One to Choose?
To summarise, a B.E programme is recommended for students who are looking for theoretical knowledge. For example, if a student wishes to learn theoretical concepts a BE degree is the most appropriate career choice. On the other hand, if an individual wants a more hands-on learning experience, they should opt for a B.Tech degree. For example, if a student wishes to design real-world practical applications for computer applications, then a B.Tech degree in the relevant field will be more appropriate. Both degrees offer similar career advancement opportunities, and thus, one must align their interests and aspirations before making the final decision.

Do you know that civil engineering is one of the sought-after professions in India? As India has been investing immensely in infrastructure projects such as roads, bridges, airports, railways, and other forms of development, civil engineers are in high demand to plan, design, and manage these projects. Moreover, due to urbanisation, there has been increased demand for real estate across the country. Besides these, the initiatives taken by the Government of India, such as the "Smart Cities Mission" and the "Atal Mission for Rejuvenation and Urban Transformation (AMRUT)," have increased the demand for civil engineers.
There is immense scope to pursue a career in the field of civil engineering. The first step is to apply for a Bachelor of Technology (B.Tech.) degree in civil engineering. However, there are many specialisations offered under this programme. It is very important for you to choose the right specialisation, as it will determine your career path. We have come up with this guide to help you understand the different specialisations you can pursue in the future!
Structural Engineering
If you choose structural engineering your curriculum will cover topics such as ways to withstand high winds and natural disasters like floods and earthquakes. You will also study the gravitational features of these buildings to understand how much weight they can handle and develop support mechanisms through beams and columns. Upon graduation, you can pursue further specialisation in bridge design, building, or aircraft engineering. As a structural engineer, you will be capable of undertaking projects such as site inspection, home improvements, skyscraper and vehicle design, and so on.
Environmental Engineering
In this discipline, you will learn how to reduce the overall impact of a man-made system on the natural ecosystem. Moreover, you will also learn to manage natural resources for a construction project. As environmental engineers, you will study the chemical properties of water, soil, and air so that you can design the technical mechanisms that can mitigate pollution issues. After graduating, you can use your knowledge and skills to help organisations improve their sustainability and advise legislators on environmental policies. Upon completing your B.Tech. degree, you can take up projects such as solid waste management, recycling systems, wastewater treatment, drainage systems, crop irrigation, and various others.
Construction Engineering
Under this specialisation, you will gain knowledge of the design principles of construction, building code regulations, and operation steps for a project. You will also learn how to manage the resources and devices used in a project and develop skills to build safe and sustainable buildings. In this speciality, you will master the art of organising each step of the construction process, such as planning the project, setting a deadline, maintaining inventory, and so on. Upon graduation, you can undertake the projects of constructing residential buildings, commercial buildings, roads and bridges, water treatment plants, and others.
Geotechnical Engineering
In geotechnical engineering, you will learn about the importance of rocks, soil systems, and artificial materials that support an engineering process. For example, you may be asked to oversee the construction of an underground mining facility. In order to succeed in this role, you will need to learn about the chemical properties of the earth, as different types of rock may require different building techniques. Upon graduation, you can undertake projects such as designing water tank reservoir systems, sewer tunnel systems, pavements and roads, natural embankments, and so on.
Way Forward
In conclusion, there is an increased demand for civil engineers in India. The dynamic landscape of construction and development allows you to explore a plethora of opportunities in the field of civil engineering. However, choosing the right specialisation can determine your career trajectory. While, you will learn to design safe buildings in structural engineering, on the other hand, you will manage ecological preservation in environmental engineering. Therefore, each specialisation serves a vital role in addressing the complex challenges of modern society. Therefore, the field of civil engineering offers a rewarding career if you wish to contribute to the nation's progress and development in a meaningful way.

According to a recent survey by McKinsey & Company, it has been found out that several organisations are adopting artificial intelligence (AI) in at least one of their business vertical. Additionally, a report by CB Insights also claims that global funding for AI start-ups is expected to rise by $73.3 billion in the next few years.
When corporations are turning to AI and machine learning systems to optimise their business functions, a career in this field is surely the right decision. Pursuing a Bachelor of Technology (B.Tech) in AI and Machine Learning can be a potential career pathway for you. However, before we dive deeper into the topic, let us understand what the course is about!
What is B.Tech in Artificial Intelligence and Machine Learning?
A Bachelor of Technology (B.Tech) in Artificial Intelligence and Machine Learning is an undergraduate degree programme that provides you with knowledge of the concepts of artificial intelligence and machine learning algorithms. The course curriculum helps you build smart machines that can aid in the decision-making process without human intervention. Besides this, the programme also helps you build self-learning computer systems by combining algorithms and statistical models.
Why should you pursue a B.Tech in Artificial Intelligence and Machine Learning?
AI and ML are two important technologies that have taken the world by storm. Several firms are adopting AI-powered predictive analytics to predict market trends, supply chain disruptions, and customer behaviour. In this light, a B.Tech. in AI and ML is a compelling career option because the technology will stay in trend for a long time, will not fade away soon, and will offer multiple career opportunities for you. Let us see some of the reasons that prove that a B.Tech. in AI and ML is a good career move for you:
A Bright and Promising Career Prospect
Since several companies are introducing AI into their ecosystems, studying AI and machine learning opens up lucrative career opportunities for you. You can create cutting-edge technologies in diverse sectors, such as computer protection, image recognition, pharmacy, or face recognition. Your unique skill set and knowledge will make you a desirable candidate for top positions across different industries.
Highly Rewarding Salaries
All the recent surveys prove that AI is one of the fastest-growing technologies in the business world. The data also suggests that AI engineers are the most sought-after professionals around the world these days. In India, the average annual salary for an entry-level AI engineer exceeds the average salary for an engineer in any other discipline. Therefore, opting for a career in AI and ML can bring in handsome salary packages for you upon your graduation.
A Versatile Discipline
AI and ML are two fields that can be applicable across any industry or field such as healthcare, finance, retail, hospitality, manufacturing, and many others. As these two disciplines have a broad spectrum of applications, you can find a plethora of career options to choose from based on your interests and aspirations.
Skill of the Century
AI and ML are often referred to as the skills of the century because of their profound impact on the global market. In the coming days, AI will eventually reduce manual labour while also creating new career options in related fields. As the world is constantly progressing towards an AI-centric world, it is imperative that you have at least some knowledge of AI in order to remain relevant in the industry!
Way Forward
As the world is gravitating towards AI-driven solutions, pursuing a B.Tech in Artificial Intelligence and Machine Learning can be a smart career move for you. The diverse application of AI and ML in our daily lives has successfully underscored the indispensability of AI in modern life. Therefore, a career in AI and ML offers a bright and promising career by offering lucrative opportunities across different industries. Therefore, if you want to be at the forefront of the technological revolution, a B.Tech in AI and ML is the right career option for you!

One of the biggest dilemmas in pursuing a career in the tech industry is to choose between a degree in computer engineering or a degree in software development. Although both fields might be interconnected, there are subtle differences. Moving on to the next question, one would think about which field is more appropriate and best to pursue.
Computer engineering and software development might be the two sides of the same coin, but they are not the same fields. Computer engineering is a discipline that focuses on the design and development of computer systems, that includes both hardware and software components.
On the other hand, software development focuses on building, designing, testing, and maintaining software applications and systems. While computer engineers may work on both hardware and software aspects, software developers primarily focus on writing code and deploying software solutions to meet specific user needs. Let us understand each aspect of these two fields in detail:
Computer Engineering vs. Software Development: Course Duration
A Bachelor of Technology (B.Tech) in Computer Engineering is a 4-year programme. The programme includes both theoretical coursework and practical hands-on experience through laboratory work, projects, and internships. Furthermore, one can also pursue higher education by opting for a Master's degree in the same field, which is again a 2-year degree programme.
A B.Tech in Computer Science is an undergraduate degree that one can pursue in the field of Software Development. This undergraduate programme is a 4-year course split into 8 semesters. They can also pursue a Master’s degree in the same field, which is a 2-year programme. Alternatively, there are different other courses available for students to learn software development, such as Introduction to Programming (4–8 weeks), Web Development Bootcamp (8–12 weeks), Mobile App Development (6–10 weeks), Software Engineering Fundamentals (8–12 weeks), Full Stack Development (12–20 weeks), Object-Oriented Programming (4–8 weeks), Data Structures and Algorithms (8–12 weeks), Python Programming (6–10 weeks), and many others. However, these durations may vary depending from one institution to another.
Computer Engineering vs. Software Development: Course Eligibility
For an undergraduate degree in computer engineering, the candidate must have studied their 10+2 with a PCM (Physics, Chemistry, and Maths) background and must have a minimum percentage between 50 and 60 in their 12th examinations. They must also clear entrance exams, such as JEE Main (Joint Entrance Examination-Main), state-level engineering entrance exams, the Birla Institute of Technology and Science Admission Test (BITSA), and other university-specific entrance exams. Similarly, for the postgraduate degree, the minimum percentage requirement is around 50% to 60% aggregate in the undergraduate degree. Additionally, some institutions may require a valid Graduate Aptitude Test in Engineering (GATE) score or equivalent entrance exam score for an M.Tech degree.
To qualify for the software development courses, one should have a high school diploma or equivalent and possess basic computer literacy and familiarity with programming concepts. Some institutions may require a prerequisite understanding of certain topics in mathematics, computer science, or related subjects if the candidate has completed their undergraduate degree. Furthermore, meeting the admission criteria set by the university or institution, which may include a certain GPA, letters of recommendation, and possibly a relevant work or research background.
Computer Engineering vs. Software Development: Course Curriculum
The course curriculum for degrees and courses in Computer Science and Software Development can vary with institutions. However, let us go through some of the common topics and subjects that are taught in the respective fields.
The subjects that are taught in the Computer Engineering course curriculum are Digital Logic Design, Computer Architecture, Programming Languages and Software Engineering, Data Structures and Algorithms, Operating Systems, Computer Networks, Database Systems, Microprocessors and Microcontrollers, Digital Signal Processing, Computer Graphics and Visualisation, Embedded Systems, Computer Security, Artificial Intelligence and Machine Learning, Electronics and Circuits, Mathematics and Engineering Mathematics, Engineering Ethics and Professionalism.
The subjects that are taught in the Software Development course curriculum include Programming Languages, Software Engineering Principles, Data Structures and Algorithms, Object-Oriented Programming, Database Management, Web Development, Mobile App Development, Version Control Systems, User Interface (UI) and User Experience (UX) Design, Software Testing and Quality Assurance, Agile Development Methodologies, Software Project Management, and Computer Science Fundamentals.
Computer Engineering vs. Software Development: Career Opportunities
As the tech industry is growing rapidly, one can find lucrative career opportunities lurking in both the fields of computer engineering and software development. The individuals must utilise the knowledge and skills gained during these programmes to navigate career opportunities across various industries and sectors. Let’s observe some of the potential career paths one can pursue in each field:
Career Prospects after Computer Engineering
Computer engineering offers a wide range of career opportunities in various sectors. Let us see some of the prominent career options for computer engineering graduates, including:
Software Engineers are responsible for designing, coding, testing, and maintaining software applications and systems for different platforms, industries, and purposes. Hardware Engineers develop and design computer hardware components, including processors, memory systems, and circuit boards. Network Engineers work on designing, implementing, and managing computer networks and communication systems to ensure efficient data exchange. Systems Analysts are responsible for analysing an organisation’s IT needs and designing solutions that address business requirements and improve efficiency. Embedded Systems Engineers create software for embedded systems used in devices like IoT devices, medical equipment, and automotive systems.
Career Opportunities after Software Development
There are ample career advancement possibilities after completing a course in software development. Let us see some of the prominent career paths in the field of software development:
Front-end developers specialise in creating user interfaces and interactive elements for websites and applications. Back-end developers focus on the server-side logic, databases, and application architecture that power software systems. Full-Stack Developers utilise their proficiency in front-end and back-end development to build web applications. Mobile App Developers are responsible for creating applications for smartphones and tablets on platforms such as iOS or Android. Game Developers design and code video games for consoles, PCs, or mobile devices.
Way Forward
In conclusion, a career in computer engineering encompasses involvement in both hardware and software, whereas a career in software development is a subset that concentrates solely on creating software applications. Therefore, the decision to choose a career in any of these fields solely depends on one’s interests and passions. If anyone is passionate about designing and developing computer hardware and software systems, then computer engineering is the right career choice for them. However, if an individual is interested in creating, testing, and designing software applications, then software development is the right career choice for them.

Did you know that the global IT industry is expecting a massive growth projected at around $3.8 trillion? Yes, you heard us right. There has been an increased demand for IT services in the last few years. With the development of new technologies like artificial intelligence, machine learning, and blockchain, the demand for professionals skilled in computer engineering has skyrocketed.
In today's fast-paced world, computer science and software engineering serve as crucial pillars of technological innovation. As our world becomes more interconnected and data-driven, there is an increasing demand for individuals in both these fields. However, we must understand that both these fields are different from each other. In this blog, we shall explore the intricacies of pursuing a career in computer science, versus software engineering. Come, let's navigate the differences between these two domains.
Computer Science vs. Software Engineering: Course Duration
A Bachelor of Technology (B.Tech) in Computer Science typically has a duration of 4 years in most educational institutions. The programme is divided into 8 semesters and includes both theoretical coursework and practical hands-on experience through laboratory work, projects, and internships. Furthermore, one can also pursue a Master's degree in the same field, which is again a 2-year degree programme that is again divided into 4 semesters.
A B.Tech in Software Engineering is a 4-year undergraduate programme across most of the engineering colleges in India. Along with theoretical coursework, the course also exposes the students to practical projects, onsite visits, and internships divided into 8 semesters. After completing their undergraduate, one can also apply for a two-year postgraduate degree in Master of Technology (M. Tech.) in Software Engineering, which is again divided into 4 semesters.
Computer Science vs. Software Engineering: Course Eligibility
For an undergraduate degree in both fields, the candidate must have taken a PCM (Physics, Chemistry, and Maths) combination in their 10+2 and must have a minimum required percentage between 50 and 60. They must also clear their entrance exams, such as JEE Main (Joint Entrance Examination-Main), State-Level Engineering Entrance Exams, the Birla Institute of Technology and Science Admission Test (BITSA), and other university-specific entrance exams.
Similarly, for the postgraduate degree in both fields, the minimum percentage requirement is around 50% to 60% aggregate in the undergraduate degree. Additionally, some institutions may require a valid Graduate Aptitude Test in Engineering (GATE) score or equivalent entrance exam score for an M.Tech degree.
Computer Science vs. Software Engineering: Course Curriculum
Both Computer Science and Software Engineering have similar foundations that intertwine with coding and computation. However, each of the curricula follows distinct trajectories.
The core subjects in the Computer Science curriculum are Programming Fundamentals, Data Structures and Algorithms, Computer Architecture, Operating Systems, Database Management Systems, Discrete Mathematics, Software Engineering, Computer Networks, Artificial Intelligence, Theory of Computation and various others.
The core subjects in the Software Engineering curriculum are Software Development Lifecycle, Requirements Engineering, Software Design, Software Testing and Quality Assurance, Software Project Management, Software Maintenance and Configuration Management, Software Security, User Experience (UX) Design, Software Metrics and Measurement, Agile and DevOps Practices and many others.
Computer Science vs. Software Engineering: Career Opportunities
Both Computer Science and Software Engineering offer a plethora of rewarding career opportunities. While Computer Science equips an individual with the core principles of computation, Software Engineering hones your software development skills. These paths enhance their problem-solving abilities, innovation mindset, and adaptability, thus making them competent candidates. Let us explore some of the high-demand career prospects in each field:
Career Prospects in Computer Science
Individuals pursuing a career in Computer Science are often called the frontiers of technology as they are pioneering breakthroughs in artificial intelligence, machine learning, and cybersecurity systems. Let us see some of the key roles in the Computer Science industry:
Data Analysts are responsible for analysing data in order to extract valuable information and make well-informed business choices. Web developers design and maintain websites, and web applications with the help of programming languages, and other design tools.
Cybersecurity analysts play an important role in safeguarding computer systems and networks against cyber threats. Database administrators manage and maintain databases, ensuring efficient storage, retrieval, and security of data for organisations. Machine learning engineers develop and deploy machine learning models to extract insights and drive data-driven solutions.
Career Prospects in Software Engineering
Individuals who are interested in pursuing a career in software engineering are known as the architects of the virtual world. They use their knowledge and skills to develop codes that breathe life into our devices, applications, and systems. Software engineers can work across borders and industries, thus helping the way we communicate, conduct business, and experience the world around us. Let us see some of the key roles in the Software Engineering:
Software Engineers design, develop, and maintain software applications, translating concepts into functional code. Software Architects create high-level software designs and guide teams in implementing complex systems. Quality Assurance (QA) Engineer ensures software quality through rigorous testing and quality control processes. UI/UX Designers design intuitive user interfaces and seamless user experiences for digital products. DevOps Engineers streamline software development and deployment through automation and collaboration.
What to Choose and the Way Forward
In conclusion, computer science lays emphasis on the design and understanding of computational processes, whereas software engineering focuses on the analysis, design, construction, and testing of software applications. If an individual is eager to learn about AI and machine learning, they should choose computer science, whereas if they wish to pursue a career in understanding software functionalities, they should choose software engineering. Despite their differences, both fields open doors to great career advancement opportunities for tech-savvy professionals. In today’s technological age, both fields are in high demand and never have a shortage of job opportunities. Therefore, one must understand their key strengths and drive their career in such a field that they have an interest in!
As per recent survey reports, the tech industry is expected to have a massive growth of 15% in the coming years. Another research predicts that there will be over 75 billion Internet of Things (IoT) connected devices by 2025 that will drive our homes, cities, and workplaces.
When we come across these astounding figures, we realise that we are soon transforming into a society that will be driven by technology. With that being said, the demand for skilled tech professionals will also increase rapidly. Now that we know that the demand will surge, it brings us to another question: Which one is a better tech career - Computer Engineering or Computer Science? Which course offers better career opportunities and how should one align their interests accordingly?
Today, we shall dive into the nuances of both fields, exploring the educational paths, curriculum, and career trajectories that set Computer Engineering and Computer Science apart. So, whether one is drawn to constructing hardware or possesses a knack for coding, let's navigate the crossroads of tech careers together!
Computer Engineering vs. Computer Science: Course Duration
A Bachelor of Technology (B.Tech) in Computer Engineering typically is of 4 years. The programme includes both theoretical coursework and practical hands-on experience through laboratory work, projects, and internships. Furthermore, one can also pursue a Master's degree in the same field, which is again a 2-year degree programme.
A B.Tech in Computer Science is a 4-year undergraduate programme across most of the engineering colleges in India. Along with theoretical coursework, the curriculum also exposes the students to practical projects, onsite visits, and internships. After completing their undergraduate programme, students can apply for a two-year postgraduate degree in Master of Technology (M. Tech) in Computer Science.
Computer Engineering vs. Computer Science: Course Eligibility
For an undergraduate degree in both fields, the candidate must have studied their 10+2 with PCM (Physics, Chemistry, and Maths) background and must bear a minimum percentage between 50 and 60 in their 12th examinations. They must also clear entrance exams, such as JEE Main (Joint Entrance Examination-Main), State-Level Engineering Entrance Exams, the Birla Institute of Technology and Science Admission Test (BITSA), and other university-specific entrance exams.
Similarly, for the postgraduate degree in both fields, the minimum percentage requirement is around 50% to 60% aggregate in the undergraduate degree. Additionally, some institutions may require a valid Graduate Aptitude Test in Engineering (GATE) score or equivalent entrance exam score for an M.Tech degree.
Computer Engineering vs. Computer Science: Course Curriculum
The course curriculum for B.Tech and M.Tech in Computer Science and Computer Engineering can be different across various institutions of the country. However, let’s see a general overview of the subjects and topics that are commonly covered in each of the undergraduate and post-graduate programmes.
| Core Subjects in B.Tech in Computer Science | Core Subjects in B.Tech in Computer Engineering |
| Data Structures | Data Structures |
| Computer Organisation and Architecture | Digital Logic Design |
| Digital Logic Design | Computer Organisation and Architecture |
| Object-Oriented Programming | Object-Oriented Programming |
| Microprocessors and Microcontrollers | Microprocessors and Microcontrollers |
| Database Management Systems | Database Management Systems |
| Operating Systems | Operating Systems |
| Algorithms | Algorithms |
| Computer Networks | Computer Networks |
| Software Engineering | Software Engineering |
| Web Technologies | Web Technologies |
| Artificial Intelligence and Machine Learning | Artificial Intelligence |
| Core Subjects in M.Tech in Computer Science | Core Subjects in M.Tech in Computer Engineering |
| Advanced Algorithms | Advanced Computer Architecture |
| Machine Learning | VLSI Design and Testing |
| Artificial Intelligence | Advanced Digital Signal Processing |
| Data Mining and Warehousing | Embedded Systems |
| Advanced Computer Networks | High-Performance Computing |
| Distributed Systems | Network Protocols and Security |
| Advanced Operating Systems | Advanced Algorithms |
| Software Engineering | Cloud Computing and Virtualisation |
| Cloud Computing | Internet of Things (IoT) |
| Natural Language Processing | Cybersecurity and Privacy |
| Cryptography and Network Security | Internet of Things (IoT) |
| Advanced Database Management Systems | Advanced Artificial Intelligence |
Computer Engineering vs. Computer Science: Career Opportunities
There are ample opportunities in both the fields of computer science and computer engineering. One can utilise the knowledge and skills gained during undergraduate and postgraduate programmes to navigate career opportunities across various industries and sectors. Let’s observe some of the potential career paths one can pursue after completing a degree in computer science or computer engineering!
Career Prospects after Computer Engineering
Machine Learning Engineers use their strong programming skills and knowledge of data science to design and develop machine learning systems, implement appropriate ML algorithms, and conduct experiments. An artificial intelligence engineer creates algorithms that are capable of learning, assessing, and forecasting future events. Network engineers are expert professionals who establish and maintain networks within an organisation or between organisations. Mobile app developers build applications for mobile devices, working on platforms like iOS and Android, using programming languages and tools. UI/UX designers create user interfaces and experiences that enhance the usability and visual appeal of software applications and websites.
Career Prospects after Computer Science
Software Developers build and design computer programmes that power desktop computers, smartphones, and even cars. Web developers create and maintain websites, and web applications with the help of programming languages, and design tools. Data analysts analyse and interpret complex data to extract important information. Database Administrators manage and maintain databases, ensuring efficient storage, retrieval, and security of data for organisations. Cybersecurity Analysts protect computer systems and networks from cyber threats by implementing security measures and monitoring for vulnerabilities.
Way Forward
Both computer science and computer engineering are technology-driven domains centred around computer and information systems. While we learn about the development of computer systems in computer engineering, on the other hand, we build innovative solutions with the help of computer science. For individuals who like delving into hardware intricacies or envisioning user interfaces, computer engineering might resonate more deeply. However, if an individual likes data analysis and computer networks, computer science might hold greater appeal.

A recent survey observed that more than 20 million mobile application developers will be needed in India alone by 2030. The research conducted by NASDAQ suggests that investments in cloud technology are projected to surpass $40 million in the coming years.
All of these statistics point out a common result, i.e., there is an increasing demand for professionals with expertise in cloud technology and mobile applications. As technology continues to reshape the landscape of industries around the world, the demand for skilled professionals in cloud technology and mobile application development has increased significantly.
In response to this evolving landscape, if you pursue a Bachelor of Technology (B.Tech) in Cloud Technology and Mobile Application, you will be exposed to a myriad of advantages in your career. Let us understand the benefits of this specialised B.Tech programme and uncover the degree’s potential in shaping your careers in this digital era!
Relevance in the Tech Industry
The IBM statistics show that about 85% of new applications are being developed around cloud computing. The industry is expected to grow tremendously, driven mainly by the services that allow users to back up their files including photos and music. As the industry is rapidly evolving, enrolling in a B.Tech programme focused on these areas can help you stay relevant and aligned with industry trends. This increases your chances of finding employment in technology-driven organisations.
Culminates a Diverse Skill Set
The curriculum of a B.Tech programme in Cloud Technology and Mobile Application covers a wide range of subjects. The curriculum covers topics in cloud infrastructure management, mobile app development, user experience (UX) design, coding languages, frameworks, and many more. This variety of subject exposure helps you to gain proficiency in multiple areas and excel in different types of career roles.
High-demand Career Scope
Due to globalisation, cloud computing and mobile app development have become fundamental components for businesses across industries. According to IDC, worldwide spending on public cloud services and infrastructure is projected to reach $210 billion in the coming years. This prediction is a testament that more firms will be turning to skilled professionals in the cloud domain to steer their organisations toward success. Therefore, if you are skilled in cloud computing, you will become a potential candidate for several industries seeking expertise to deliver seamless user experiences.
Options for Flexibility and Scalability
The programme teaches you concepts like designing cloud-based systems, auto-scaling and load balancing, which can scale up your demand in the changing business landscape. Moreover, understanding cloud resource management helps you optimise usage and costs which can turn out to be handy during a company crisis. So, by understanding how to manage cloud resources, contribute to the operations of an organisation in the best way and help it to adapt to changes efficiently.
Expertise in Mobile App Development
In the next few years, it is expected that billions of devices like home appliances, LED bulb lights, power sockets, etc. can be integrated and controlled by mobile applications. There will be an increased demand for mobile applications. That is why a B.Tech degree in Cloud Technology and mobile application development can help you learn about user interface (UI), user experience (UX) design, coding languages, and frameworks.
Way Forward
In conclusion, the rising demand for professionals skilled in cloud technology and mobile application development is evident from various statistics and industry trends. Through a B.Tech degree in Cloud Technology and Mobile Application, you'll learn about the latest trends in today's digital world. The different subjects you'll study will help you gain skills to do well in jobs like cloud engineers or mobile app developers. Therefore, a B.Tech degree in Cloud Technology and Mobile Application empowers you to embrace the evolving landscape of technology and pursue a successful career in a digital ecosystem.

Do you have a burning desire to explore the world of innovation and technology? If your answer is yes, then we highly recommend you apply for a Bachelor of Technology (B.Tech) in Cloud Technology and Information Security. This undergraduate programme is well-designed to equip you with the knowledge and skills to thrive in the ever-evolving cloud industry. In today's digital age, businesses rely heavily on technology and information security to safeguard their data and operations. As organisations tend to search for highly skilled professionals and manage their data on a daily basis, you will stay in demand for your extensive skills and knowledge. Let us help you understand the benefits of studying B.Tech in Cloud Technology and Information Security:
Diverse Career Scope
The programme equips you with relevant skills and knowledge that are aligned with the current trends in the IT security sectors. You will possess a comprehensive understanding of network security, cryptography, ethical hacking, and many more crucial areas. Having knowledge on such holistic topics will help you gain a competitive edge over others. You can pursue diverse career roles such as information security analyst, network security specialist, information security consultant, and so on. You can also progress into leadership roles, such as security managers or cloud architects, as you gain experience and expertise in the field over the years.
Great Remuneration
Information technology and information security are integral to the smooth functioning of modern businesses. The companies recognise the importance of safeguarding their sensitive data and ensuring seamless business operations. As a result, they are willing to invest in skilled professionals who can handle these critical responsibilities. Therefore, as cloud technology and information security professionals, you will be able to draw competitive salaries that are the best in the industry. However, you must bear in mind that the earning potential can vary based on the skill set, industry and size of the company.
Exposure to Continuous Learning
Cloud technology and information security are dynamic domains that witness frequent updates and innovations. As new services, tools, and best practices emerge regularly, you need to keep pace with these changes to remain relevant in your field. During your course, you will have several opportunities for continuous learning through certifications and workshops. You can obtain certifications like Certified Cloud Security Professional (CCSP) or Certified Ethical Hacker (CEH) that will help you demonstrate your expertise in specific areas, and increase your overall marketability.
Contribution Towards Innovations
As businesses adopt cloud services, there will be an increased demand for robust data security measures. Therefore, as cloud technology professionals, you will be responsible for developing and implementing advanced security protocols to protect data. You will also explore new encryption algorithms, authentication methods, and access controls to fortify the security posture of cloud systems. Additionally, you will explore innovative Multi-Factor Authentication (MFA) methods, such as biometrics, and adaptive authentication, to enhance security while maintaining user privacy.
Way Forward
In conclusion, pursuing a B.Tech. in Cloud Technology and Information Security is a highly recommended career path if you aspire to be at the forefront of innovation. This undergraduate programme is meticulously designed to equip you with the knowledge and skills necessary to excel in the rapidly evolving cloud industry. The diverse career scope offers you abundant opportunities for growth and specialisation across different industries. Moreover, the field presents great earning prospects as businesses understand the significance of safeguarding data and seamless operations. The continuous learning aspect is equally crucial, and the programme encourages you to pursue additional certifications to enhance your skill and knowledge levels. As a B.Tech graduate in this field, you will be well-prepared to make a significant impact, protect vital data, and drive progress in this rapidly evolving and impactful domain.

According to a recent survey, India produces more than a million Computer Science Engineers (CSE) every year!
The staggering number indicates the rising demand for CSEs in the country to fill the talent gap in today's digitised business landscape. The field is in high demand due to the myriad of exciting opportunities it offers students. The young graduates are equipped with essential technical skills like programming and operating systems, along with the ability for creative problem-solving and leadership. With relevant knowledge and skills, the CSEs have been able to penetrate across various industries, such as hospitals and financial institutions.
With an impressive 72% employment rate and the highest placement records, the computer science industry is poised for continuous expansion in the coming decades. As nearly every business embraces digital technology, the importance of computer science will only increase. This rising popularity will make it a promising and rewarding career choice for aspiring students. Let’s understand in detail how pursuing a Bachelor of Technology (B.Tech) in Computer Science and Engineering can be a smart career choice for youngsters these days!
Booming Tech Industry
The tech industry is witnessing explosive growth with innovations in artificial intelligence, data science, cybersecurity, and more. As a result, there is a soaring demand for skilled professionals in the fields of computer science and engineering. The CSEs’ expertise in programming languages, algorithms, software development, and system design makes them invaluable assets for businesses seeking to implement and optimise technology solutions.
Diverse Career Pathways
A B. Tech in computer science and engineering offers diverse career pathways for graduates to work across various sectors. For example, they can work in software development, where they will be involved in the design, coding, and testing of software applications and systems. Alternatively, they can also work as IT consultants, where they will help businesses optimise their technology infrastructure and strategise IT initiatives.
High Earning Potential
CSE professionals are known for their high earning potential, making it one of the most financially rewarding fields in the market. In today's digital age, nearly every business relies on technology, and therefore they need to rely on CSEs to design, develop, and implement innovative solutions for them. As a result, companies are willing to pay lucrative remuneration to attract and retain top talent in the field. Alternatively, professionals can also embark on entrepreneurial journeys and earn well from their profits.
Global Opportunities
The tech industry is widespread across countries, so there are a plethora of global opportunities for CSE graduates. Several multinationals and tech start-ups have a global presence and are constantly seeking top tech talent to drive innovation for their companies. These professionals can collaborate with teams worldwide and enrich their knowledge and skills. Furthermore, international conferences, seminars, and workshops provide platforms for CSE professionals to showcase their expertise and network with global leaders and researchers in the field.
Flexibility at Work
The tech industry often offers flexible work arrangements, including remote and hybrid work options. Many companies in the tech sector recognise the importance of work-life balance and provide flexible working hours. By having this arrangement, it enables CSE professionals to manage their time efficiently, thus catering to personal commitments without compromising their professional responsibilities.
Way Forward
In conclusion, the increasing number of Computer Science Engineers (CSE) produced annually in India highlights the growing demand for skilled professionals in the tech sector. With an impressive employment rate, a bachelor’s in Computer Science and Engineering offers a promising and rewarding career choice for aspiring students. The booming tech industry presents a plethora of opportunities for CSE professionals to implement and optimise technology solutions. The high earning potential in the tech industry further reinforces its appeal, as companies are willing to invest generously in attracting top CSE talent. Additionally, CSE professionals have the flexibility to work remotely or in a hybrid model, thereby having a balanced work-life balance. With a dynamic and promising career outlook, a B.Tech in Computer Science and Engineering remains a smart and forward-thinking career move for young talents.

Are you looking for the right B.Tech College to elevate your engineering aspirations to the next level?
Selecting the right college is a crucial task as it lays the groundwork for your career. With numerous factors to consider, the process can be daunting. Your choice directly influences the quality of education you receive. A well-designed curriculum, experienced faculty, and modern infrastructure can enrich your learning journey and provide a strong foundation in your chosen field.
Moreover, top-tier colleges often have strong industry connections and a robust placement cell. A reputable college can increase your chances of landing internships and job placements easily. Well, if you are wondering how to choose the right B.Tech college, we have come up with a comprehensive guide that will aid you in your admissions:
Accreditation
Accreditation plays an important role in choosing the right B.Tech college. Accredited colleges ensure that they meet the academic standards. Accreditation ensures that the college has undergone evaluations by recognised accrediting bodies that verify the quality of education they offer. Therefore, you must choose the B.Tech colleges that are accredited by regulatory bodies such as the National Board of Accreditation (NBA) or the All India Council for Technical Education (AICTE).
Reputation and Ranking
A college's reputation and ranking play a significant role in shaping your academic and professional journey. A college with a strong reputation automatically earns you respect from employers. Possessing a reputable educational background enhances your likelihood of securing excellent internships and job placements. Therefore, choose B.Tech colleges that are ranked under 100 by the National Institutional Ranking Framework (NIRF).
Faculty and Infrastructure
The faculty members are the first point of contact for your engineering curriculum. Therefore, the expertise and experience of faculty members will directly impact your learning experience. You must choose those colleges with highly qualified and experienced professors, as they can provide valuable insights and guidance during your engineering journey. Besides this, a college with well-equipped infrastructure, modern facilities, laboratories, and libraries can enhance your learning and research opportunities.
Course Curriculum
It is very important to consider your course curriculum before applying to any B. Tech college as your curriculum should align with your academic and career goals. Different colleges might offer variations in the B.Tech programmes, with some focusing on specific specialisations or industries. You must ensure that the college you choose offers a curriculum that matches your interests and aspirations. A well-designed curriculum should cover a wide range of topics relevant to your field of study, including both theoretical knowledge and practical applications.
Internship and Placement Support
The college's tie-ups with industries and its track record of internships and placements are vital factors to consider before choosing a B.Tech college. A college that emphasises internships helps you bridge the gap between theoretical knowledge and practical application, making you job-ready. Secondly, a college with a dedicated and effective placement cell can assist you in finding suitable job opportunities. Placement cells organise placement drives, connect with companies, and help match your skills with potential employers. You must look for colleges that can provide internship opportunities, have active placement cells, conduct placement drives, and have a history of successful placements.
Way Forward
To put it in a nutshell, choosing the right B.Tech college is a critical decision that lays the foundation for your engineering career. It can significantly impact the quality of education you receive, your exposure to the industry, and your job prospects after graduation. By considering factors such as accreditation, reputation, faculty expertise, and course curriculum, you are bound to receive a comprehensive and industry-relevant education. Besides this, the availability of internships and robust placement support can open doors to practical experiences, industry connections, and diverse career opportunities. So, you must invest your time and effort appropriately to find the best B.Tech college that is the right fit for your aspirations and ambitions.

Congratulations on passing your engineering entrance exams with flying colours! You must be appreciated for putting in a lot of hard work and dedication for your entrance examinations. The long hours of study and hard work have enabled you to enrol for your dream degree, i.e., Bachelor of Technology (B. Tech)!
Although you must be elated now, you must bear in mind that your B. Tech journey will require utmost dedication and hard work. If you think that the hassle of studying has ended after clearing your entrance, then you are wrong. The programme is considered prestigious because of its academic rigour and the long-term career opportunities it brings. Engineering is recorded as one such discipline that offers the highest number of career opportunities. You can start earning well and your salary can also increase over the years based on your skill, knowledge, expertise, and experience.
However, if you don’t score well in your semester examinations, then you might have to face tough competition during your job search. You need to follow some clever tips that will help you prepare for your semesters successfully. Read on to know more!
In-depth Understanding of the Concepts
Your journey towards scoring better than your peers becomes easier when you have a better understanding of engineering concepts. If you choose to mug up your answers without any comprehension, it makes the learning process tedious, clumsy, and difficult to grasp. If you try to mug up answers, you may not be able to retain the information longer. Because of this, you might not be able to answer your questions accurately and may underperform during the actual examinations. Therefore, it is always advised to read the chapters, understand the concepts, make notes, and seek clarity from professors wherever you are struggling.
Set Clear Goals
You must be pursuing your degree with a certain vision in mind. It's crucial to back up any long-term objectives you establish for yourself with more compact, doable objectives. For example, you have a B. Tech in computer science engineering and wish to pursue a career in that area. You might make a plan with reachable milestones instead of concentrating just on your long-term objective. However, you can achieve this by setting smaller, more attainable goals. These can be scoring well in internal examinations, fetching the highest marks in practical assignments, or performing well during your internships. You can create a well-structured schedule that balances classes, study time, and extracurricular activities. This will help you achieve your goal effortlessly.
Smart Answering Approach in Examinations
Writing answers in a presentable manner is crucial for scoring well in exams. When answers are organized, neat, and easy to read, it creates a positive impression on the examiner. Clear and legible handwriting, proper spacing, and logical structure make it easier for the examiner to understand your thoughts and ideas. This helps the evaluator concentrate on the keywords in the answer and provides better clarity about the flow of your solutions. Additionally, if you can combine your answers with relevant, neatly labelled diagrams, it shows that you have a better understanding of the concept. This move can create a lasting impression on the examiner, and you may end up scoring more than your peers!
Regular Attendance and Time Management
Regular attendance ensures that you stay engaged with the course material. You must participate actively in discussions, ask questions, and take detailed notes. Moreover, if you learn to master time management, you will be able to prioritise your tasks and assignments. You will never miss a deadline and can score well at the end of the semester examinations. You can do this by planning your deliverables ahead of time and setting a deadline for each task. This will help you complete your assignment on time, and you might also get some time to improvise or review it later.
Maintain a Healthy Lifestyle
As an engineering student, you may dedicate extensive hours to studying or working on projects. Consequently, this often entails prolonged periods of sitting without much physical activity. Furthermore, the ongoing stress and pressure to excel can have a significant impact on your mental well-being. However, maintaining a proper and healthy lifestyle, such as eating balanced and nutritious food and exercising or yoga, can help you stay physically and mentally fit. You can also take breaks during your studies to engage in your hobbies or recreational activities to maintain a balance between your studies and personal life. This will help you rejuvenate your mind and enable you to give your best during your examinations.
Way Forward
Although the B. Tech journey can be exciting for you, you need to be ready for what lies next. It is important to remember that your journey is fueled by dedication and hard work. To prepare successfully for your semesters, consider practising writing your answers concisely and in a visually appealing manner. You must also focus on understanding concepts deeply and setting clear goals aligned with your long-term aspirations. By attending classes regularly and prioritising your physical and mental well-being, you will move a step closer to your goal. By following these tips, you can excel academically and pave the way for a successful engineering career.
Essential Advice for First-Year Engineering Students
Are you a first-year engineering student looking for a guide to help you through your engineering journey?
If yes, this blog is for you. You must have heard that all your ordeals might end after your 12th, but this is a myth. The real struggle starts from the time you enrol in a college, especially if you are in a technical field like engineering. We all know that engineering is one of the most sought-after degrees in the world today.
Passing the strict entrance examinations and going through all the preparation to be where you are today is definitely something to be proud of. However, one must not think that the journey ends here because this is where the race for the future begins. With rapid globalisation and increased competition in the sector, securing a career is no longer easy.
We understand the gravity of the situation because, at JAIN’s (Deemed-to-be-University) Faculty of Engineering and Technology, we help our engineering students navigate through this journey seamlessly. From our experience and expertise throughout the years, we have come up with some valuable advice to help first-year engineering students like you! Read on.
Become Organised
Staying organised helps you streamline your priorities and stay on track. For example, keeping a weekly or monthly planner helps you plan the days prior so that you are well-prepared for an exam or assignment or project submission. Also, by creating a well-planned study schedule, you can cover your syllabus, prepare for mock tests, and score well on your assessments. Besides this, you can also break down larger tasks, such as projects or assignments, into smaller, manageable tasks. This will make them less overwhelming and easier to tackle. You can do this by creating a to-do list and prioritising tasks based on urgency and importance.
Keep Your Base Strong
Many of you might skip revising the fundamental concepts once you join the engineering college. Revisiting the important topic you studied earlier is recommended because these concepts set the foundation for the next four years of your engineering programme. You need to concentrate on the fundamentals of physics, mathematics, and chemistry to be prepared for future subjects and topics. It’s never a bad idea to polish your knowledge as this will enhance your basic engineering skills.
Engage in Hands-on Learning
As an engineering student, it's crucial to understand that engineering goes beyond memorization. Remember, it involves both theoretical knowledge and practical application. These will allow you to implement practical learning in real-world settings during your internship or job in the future. Therefore, you must grab every opportunity that comes your way, allowing you to access hands-on learning practices. You can participate in laboratory sessions, workshops, or projects that allow you to apply theoretical knowledge to real-world scenarios. This will enhance your understanding and make the learning experience more enjoyable.
Build a Strong Network of People
Engineering, once perceived as purely technical, now incorporates a corporate aspect. In today's competitive market, networking with specialists is vital for seizing timely opportunities. For instance, maintaining a positive relationship with mentors or trainers during internships can lead to job opportunities through referrals. You must make connections with professors, alumni, mentors, industry professionals, guest lecturers, and anyone else you come across during your journey who can add value. You can do this by participating in engineering conferences, seminars, workshops, and career fairs. These events provide opportunities to connect with professionals, learn about industry trends, and explore potential job opportunities.
Practise a Healthy Lifestyle
An engineering programme can be physically and mentally cumbersome for any young adult like you. Long hours of project work, assignments, and critical assessments can often lead to physical and mental exhaustion. By maintaining a healthy lifestyle, you allow your body and mind to free itself from unnecessary stress and pressure. You can prioritise tasks, set realistic goals, and avoid excessive procrastination to create a well-balanced routine and avoid last-minute stress. Engage in moderate physical activities such as swimming, cycling, jogging, or yoga for at least 30 minutes every day to keep yourself physically fit. You must eat a balanced diet and maintain a proper sleep schedule for your overall well-being.
Way Forward
As exciting as your engineering journey can be, it can also be challenging and demanding at times. However, by implementing the tips mentioned above, you can navigate through your engineering journey more smoothly. While staying organised helps you manage your time effectively, exposing yourself to hands-on learning opportunities allows you to stay prepared for real-world scenarios. Most importantly, building a strong network of connections with professors, mentors, and industry professionals opens doors to potential opportunities in the future. Lastly, practising a healthy lifestyle will help you manage stress. By following these guidelines, we are sure that you can make the most of your engineering journey and lay a strong foundation for your future career.
Has anyone wondered how technology can change the dynamics of engineering education?
Yes, we are talking about engineering students. We all know that engineers are the driving force behind the immense technological advancements around us. This modern world is propelled by engineers who have made our lives better and more convenient with the development of new products and services. So, is it possible that these creators of technological advancements can also be recipients of this significant global impact?
Of course, the answer is yes. Engineers implement the skills of critical thinking, innovation, and curiosity to prepare for what lies ahead. They utilise their knowledge of mathematics and science to bring revolutionary answers that can solve the pressing technical questions of our world today. Being the flag-bearers of technological transformation, we can definitely say that engineering students too shall not be exempted from the impact of technology when it comes to education. In the era of automation, and digitalisation, engineering students shall be equipped with the modern technology and skills necessary to succeed in the ever-changing academic and professional landscape.
Let us understand in depth how the future of engineering education is immensely dependent on adapting to technological developments.
Growing digital space
We are all well aware of the evolving digital advancements that are transforming our lives. Almost everything around us has become digital in the past few years. These digital spaces can create opportunities for remote collaborations among engineering students, enabling them to work together on projects, share ideas and solve problems. The digital space also contains repositories of open educational resources that can help students access them anywhere and at any time. The intervention of Augmented Reality (AR) can help engineering students indulge in immersive learning experiences. For example, they can overlay virtual objects onto the real world, thereby allowing them to visualise complex engineering concepts. The usage of online design and collaborative tools like computer-aided design (CAD) allows students to co-create 3D models on a cloud-based platform. The real-time feature of editing and designing the files enhances teamwork and streamlines the design processes seamlessly.
Introduction to Gamification
Education has evolved completely in the past few years. It is no longer restricted to just blackboards or whiteboards alone. With the introduction of digital or smart classes, we are witnessing a rise in the implementation of virtual reality in the engineering education sphere. Gamified simulations can be used in engineering courses to learn engineering principles in an interactive way. For example, civil engineers can use these simulations to create a virtual environment to construct and analyse the structural integrity of bridges. Besides this, the students can also present engineering challenges in the form of game-like scenarios. This can be done by students designing a fictional city to check how they can implement the concepts of resource sustainability in virtual reality.
Rise of Education 4.0
Education 4.0 is the concept of integrating advanced technologies and innovative teaching and learning methods in the field of education. It represents a shift from traditional educational approaches to more personalised, flexible, and technology-driven models of education. In India, Education 4.0 aims to disrupt the disparities in the education realm by empowering the youth to learn beyond the four walls of a classroom. This form of education aspires to prepare students for the challenges and opportunities of the digital age and the Fourth Industrial Revolution. Education 4.0 shall leverage powerful computational tools and software packages that can benefit engineering students. They can use these tools for finite element analysis or circuit simulations to solve complex engineering problems, analyse big data and gain insights. With the help of this technology, we can see engineering students adapt to intelligent learning and tutoring systems that can deliver customised content, assessments, and feedback to students, enabling them to learn at their own pace and in their preferred style.
Way Forward
We can therefore conclude that, as an education segment, engineering is all set to witness a big change, and this will influence the way courses are designed in the future. The rapid expansion and popularity of the digital space will facilitate promising job opportunities for engineers in fields such as computers, IT, analytics, big data, and electronics. Furthermore, we are all set to observe the introduction of gamification in education, which will transform the way students comprehend their lessons and adapt to interactive learning experiences. The introduction of Education 4.0 will also inculcate personalised and immersive learning environments for engineering students in the future.

Did you know that there are currently 80,000+ computer engineering jobs in India?
Yes, you heard us right, and all of these jobs are ready to pay handsome salaries; but to efficient engineers! However, the next question that will come to your mind is, "How do I become one of those potential engineers who can come under the radar of potential employers?
Well, a master’s degree like M.Tech in computer science from any top-reputed engineering college in India can help solidify your career prospects! This is because most Fortune companies in India or abroad prefer candidates who have advanced degrees and skills in their respective fields.
So, if you are looking for an answer about what could be your potential career opportunities after an M.Tech in computer science, we have listed down the different options. Read on.
Big Data Engineer
As the name suggests, “big data engineers” are individuals who work primarily with big data ecosystems, tools, and technologies. You will be responsible for upgrading, troubleshooting, and optimising big data systems and software to improve the efficiency of the databases. You will work collaboratively with data scientists, data architects, and data analysts to help organisations acquire meaningful insights from big and complex datasets that can be transformed into actionable business decisions.
Machine learning engineer
Being one of the most in-demand professions these days, machine learning engineers are experts who specialise in building and designing intelligent machines and systems. You will be responsible for creating advanced ML algorithms that can teach computers how to perform specific tasks without being programmed for them.
Data Scientist
Data scientists are the talk of the town these days. You will be referred to as the maestro of the data science domain. You will work extensively to derive value from complex data, followed by cleaning, organising, and processing this data to further analyse it and extract the hidden patterns within it. Moreover, you will also work closely with data analysts to uncover meaningful insights from data and provide real-world business solutions to organisations.
Data Analyst
Data analysts are the missing piece of the link that bridges the gaps between the two worlds of data science and business. As a data analyst, you will munge, process, visualise, and optimise data to ensure its quality and accuracy. You will create algorithms and modify them to extract information from large databases without corrupting the data stored within.
Blockchain Developer/Engineer
Going by the name, "blockchain developer/engineer" refers to individuals who are experts in the field of blockchain technology. In other words, you will be responsible for the entire life cycle of blockchain applications. You shall also utilize different programming languages (Simplicity, Solidity, Rholang, JavaScript, C++) to create advanced interfaces, features, and architecture to protect the systems from cyber-attacks.
Software Developer
If you love coding and programming, software development is the ideal career option for you! That’s because you will specialise in multiple programming languages like C, C++, C#, Java, Python, etc. and develop innovative software programmes and applications with unique use cases and functionalities that cater to specific customer needs. Software developers are always in high demand in the IT/ITES sector and are one of the preferred career options after computer engineering.
Computer Network Architect
Referred to as "network architects" or "network engineers”, computer network architects are professionals who design, implement, and maintain computer networks for organisations. You will be tasked to develop efficient and secure network infrastructures to support the communication needs of businesses. As a network engineer, you will also research new networking technologies to analyse current data traffic and estimate how growth in traffic might affect the network.
Wrapping it Up!
As far as career prospects are concerned for M.Tech graduates in computer science, it is safe to say that the sky's the limit for you! Pursuing an M.Tech (Master of Technology) in Computer Science opens up many new avenues to explore different career opportunities in the field of technology and computer science. Getting an M.Tech degree helps you possess advanced knowledge and specialised skills that make you highly sought-after in the industry. You will have the opportunity to work on cutting-edge technologies and contribute to fields such as artificial intelligence, machine learning, data science, computer vision, and robotics.

Are you looking for renowned colleges in Bangalore to pursue your B.Tech degree? If your answer is yes, then you have landed at the right place because our blog covers the important things that you must consider before choosing the right college for your B.Tech journey in Bangalore!
It is undeniable that the scope of an engineering degree is immense, as it offers you great placements with lucrative salary packages. Moreover, if you have aspirations to establish a career in a bustling tech hub like Bangalore, the endeavour becomes even more rewarding. The first step is to find a good college because that’s where you will build the foundation for your career.
We understand that choosing the right college can be a tricky and challenging task, as you might be overwhelmed with too many options at hand. However, we have made it easy for you by narrowing down the points that you must consider before choosing a B.Tech. college in Bangalore.
Accreditation and NIRF ranking
The first thing that you must always consider before choosing any engineering college is whether it is accredited by recognised bodies like the NBA (National Board of Accreditation), the National Assessment and Accreditation Council (NAAC), and the AICTE (All India Council for Technical Education). These accreditations are a reflection of the quality of education offered by engineering institutions. Besides this, you must also look out for the National Institutional Ranking Framework (NIRF) ranking published by the Government of India. NIRF promotes excellence amongst the educational centres and institutions of the country with respect to ‘teaching, learning, and resources.’
Scope of your specialisation
The next thing on your list should be specialisation options. Look out for colleges that offer diverse options for your B.Tech degree. You can choose the area of specialisation based on your interest, such as mechanical, civil, computer science, electronics, communication engineering, and so on. A diverse range of specialisations gives you a broader perspective to make the best choice rather than being restricted to limited options.
Internships and placements
Internships are an important part of the B.Tech course as these programmes provide practical exposure, industry insights, skill development, networking opportunities, industry-ready skills, and self-exploration. You should also look for colleges that offer good placement opportunities in big companies like IBM, Genpact, Dell, Infosys, and so on.
Financial Assistance
Pursuing a B.Tech degree can be financially challenging for many students like you and your families. However, scholarships can provide financial assistance to students and help reduce the burden of tuition fees and other educational expenses. Students who have been awarded scholarships also create a meaningful impact on employers as it demonstrates their dedication, hard work, and commitment to excellence, which are highly valued in the job market.
Industry-Relevant Curriculum
It is advisable to evaluate the curriculum of the B.Tech programme offered by the college so that you can stay industry-oriented, up-to-date, and aligned with current trends and advancements in the engineering field. A curriculum aligned with industry requirements enhances your employability prospects. Employers often seek candidates with practical skills and relevant knowledge, and a curriculum that incorporates industry-relevant topics and technologies can give you a competitive edge in the job market.
Alumni Network
The significance of an alumni network in college selection cannot be overstated. It serves as a testament to the educational excellence upheld by the institutions through their notable achievements. You must consider the strength and involvement of the college's alumni network because it provides valuable support, mentorship, and networking opportunities for you during and after your studies.
Campus life and extracurricular activities
Since you will be spending a couple of years at the college, it is very important that you assess the overall campus life and extracurricular activities offered by the college. You can look out for opportunities to engage in clubs, volunteering activities, community programmes, cultural festivals, and technical events. Engaging and vibrant campus life can contribute to your personal development and provide a well-rounded educational experience.
Wrapping it up!
Pursuing an undergraduate degree is one of the most important decisions of your life, and therefore we advise you to thoroughly research the colleges, attend open houses, interact with alumni, current students, and faculty, and gather as much information as possible before making a decision. This will help you make an informed decision and select the right B.Tech college in Bangalore that best suits your academic and career aspirations.

Have you always been interested in building machines or understanding how they work? If you are someone who is passionate about designing and developing machines that are of industrial grade, mechanical engineering can be the captain of your ship!
Yes, a Bachelor’s degree in Mechanical Engineering, also known as a B.Tech. in Engineering, can help you get a step closer to your affinity for machines. Mechanical engineers are responsible for making cost-effective designs, followed by testing and implementing them for construction. Their technical expertise allows them to plan, design, build, and implement innovative technologies with the help of technical reasoning.
They are also known as technical doctors, who can solve any problem related to machines and are credited with making human life more simple and efficient with their innovations. Therefore, because of the diverse range of skills and expertise they have, they can enjoy lucrative career options after mechanical engineering.
Although challenging and demanding, a degree in mechanical engineering can open bright paths for your future. If you are considering getting a degree or have recently graduated, this article will help you understand what the best career opportunities are out there waiting for you once you are done with your graduation in mechanical engineering!
Mechanical Engineer
How often have we heard this term in our day-to-day lives? As common and generic as it may soundou mechanical engineers shoulder immense responsibilities for designing, developing, operating, and maintaining machinery across different industries. Mechanical engineers are generally hired to test or install new machinery or can work as technical consultants to guide on structural engineering or machine maintenance questions.
Automotive Engineers
Automotive engineers are responsible for researching, designing, and developing the mechanical components and machines related to trains, cars, and other automated vehicles. India’s automotive industry is one of the largest in the world, so one can understand the diverse scope of career opportunities that are available for pursuers of mechanical engineering.
Maintenance Engineers
Maintenance engineering applies engineering concepts to optimise the existing equipment, procedures, and departmental budgets to achieve better sustainability, maintenance, reliability, and availability of the equipment.
Aerospace Engineer
Mechanical engineers are often hired to implement their domain knowledge and expertise to design aircraft and allied machinery that are compatible with airports and other production needs. They can work along with aerospace engineers in this field and can also assist in national defence projects like working with spacecraft, satellites, or missiles.
Control and Instrumentation Engineer
Control and instrumentation engineers, or C&I engineers, apply the concepts of mechanical engineering to design, develop, install, maintain, and manage the equipment responsible for monitoring and controlling other machines and systems. C&I engineers are tasked with measuring and controlling process variables like pressure, pH levels, speed, force, etc. to ensure that all the other machines and processes are running safely and efficiently.
Research and Development Supervisors
A B.Tech. in Engineering allows you to become research and development supervisors, where you oversee processes related to designing new systems, improving existing technology, analysing customer reactions to prototypes, and researching new advances in the field.
Construction Engineer
Construction engineers supervise big construction projects where they are responsible for servicing and maintaining the machines. They also advise on the installation of heavy equipment, suggest device optimisation, and perform cost calculations. Mechanical engineers are often hired by construction companies as consultants to advise on commercial building layout and design.
Nuclear Engineer
Mechanical engineers assist the nuclear engineers for technical support at nuclear power stations. They are responsible for designing, creating, maintaining, and disassembling different parts of machines related to operating a nuclear power station. You can take on the roles of process engineers, quality engineers, reactor operators, C&I engineers, and other managerial roles.
Manufacturing engineer
Manufacturing engineers apply the technical aspects of mechanical engineering to design and develop integrated systems used in the manufacturing industry. They help produce high-quality products that are in high demand in the marketplace.
Gearing up for Future!
Looking at how the world is moving at a fast pace, we can realise that humans will bring more innovations and inventions to the table to make their lives hassle-free and less complicated. To do that, they would require skilled professionals who know how efficient machines can be designed, upgraded, operated, and maintained. Therefore, it is safe to say that mechanical engineers will have ample opportunities and a futuristic career waiting for them.
If you are someone who loves machines and is keen to develop them, a B.Tech. in Engineering is the ideal path for a promising future ahead. So, grab the opportunity and get enrolled now!

Are you into gadgets and love them way too much? Are you the person who always searches for new technological developments on YouTube and Google? In other words, are you a futurist?
If your answer is yes to any of these questions, then let me tell you – you have landed at the right place! Technology has developed and transformed humongous in the past few decades; the fun part is that it’s still evolving. Have we ever thought that from a stereo recorder, we could transcend to AirPods or Bluetooth earbuds, from talking on a landline phone to owning a multi-purpose smartphone that can do anything you name? We have come a long way – thanks to technology, and there is still a long way to go.
So, to feed your increasing curiosity, today, we will discuss the trending technologies set to conquer 2023!
The AI Dominance
In 2023, artificial intelligence will become the real deal in organizations. No-code AI, with its easy drag-and-drop interfaces, will help businesses to leverage its power to create more intelligent products and services. It will change the dynamics of the e-commerce business as contactless autonomous shopping and delivery will take over the market. Several retailers will use AI to manage and automate the complex inventory management processes that will set the bar high for other industries and verticals.
Parts of the Metaverse Will Become Real
Virtual reality (VR) and augmented reality (AR) will continue to advance, and collaborative platforms will emerge for digital projects. Metaverse will revolutionise the internet by creating learning spaces where one can work, play, and socialise on a persistent platform. A leading corporate company has already created its metaverse to virtually carry out HR-related tasks, such as onboarding, training, etc.
Progress in Web3
As organisations focus on making more decentralised products and services, blockchain technology will also advance significantly in 2023. Non-fungible tokens (NFTs) will become more usable and practical, giving you access to backstage experiences for your concert tickets. This will also help us decentralise data storage and encrypt that data using blockchain technology.
The Unification of the Digital and Physical World
We will be witnessing an emerging bridge between the digital and physical worlds in 2023. There are two components of this unification, i.e., digital twin technology and 3D printing. Digital twins are virtual simulations of real-world processes, products, or operations that can be used to test new ideas in a safe digital environment. After testing in the virtual world, engineers can modify and edit components, then create them in the real world using 3D printing technology.
Quantum Progress
Quantum computing is the concept of using subatomic particles to create new ways of processing and storing information. Currently, the trend around us is to develop quantum computing at a large scale. This step is expected to bring us computers capable of operating a trillion times faster than the fastest traditional processors available today. Although there is a drawback that quantum computing at scale has the potential to break the encryption of other nations, businesses, security systems, and more, still several countries are investing billions of dollars into this idea.
Adoption of Green Technology
Despite all forms of progress and growth, we are facing a climate crisis due to increased carbon emissions in the past few decades. 2023 can bring hope for the planet as we develop green hydrogen, a new clean-burning energy source that produces close to zero greenhouse gas emissions. We will also see progress in developing decentralised power grids that distribute power worldwide with reduced carbon emissions.
Robots Will Become More Human
In 2023, we will see robots becoming more human-like in appearance and capability. These robots will be used in the real world as event greeters, bartenders, concierges, and companions for older adults. They will also perform complex tasks in factories and warehouses as they work alongside humans in manufacturing and logistics.
Wrapping it Up
We have heard that time and tide wait for none, and it will not wait for us to cope with the emerging new technology. With so much AI and machine learning penetrating the environment around us, we must stay updated with the current trends to utilise the services to the optimum potential and secure the best future for us in the coming days.

Engineering is a significant field of study that has revolutionised our Earth since immemorial. With so many great things built because of engineering, many of us also want to contribute towards this journey. Engineering is a field with curiosity and an inclination toward creating something new and innovative for humanity.
So, if you are a student with questions about why you should take engineering, you are at the right place! Today, we will answer your questions and help you understand how engineering is the stepping stone to a well-organised and educated 'next-generation' of the country and the world.
Question 1: Why am I taking up Engineering?
Often youngsters take up a field of study due to parental or peer pressure and have no personal interest in it. As a student, you must know your academic strengths and weaknesses and channel your career in that direction. There is no better judge than yourself.
So, if you want to ask yourself why you want to take up engineering, you can look at the following pointers that can help you decide.
If you are unclear about the answers and feel this is solely because you want to score a great job and make your parents happy, then engineering is not for you. None of it will help you because your passion drives engineering to learn and live the subject wholeheartedly and not treat it as a trophy degree.
Question 2: Do I possess the required skill set to complete engineering?
Passion alone cannot be everything. Of course, you need an inner drive to propel you in this, but apart from this, you also need to develop a certain skill set to become an engineer. It would help if you were a good problem solver, as you will encounter several critical problems and obstacles during your experiments. You need to focus and be a detailed person. You should also be able to work in a team and exhibit good communication skills. You can also lead a team of engineers in the future, so you should possess the leadership skills to lead everyone around you.
Question 3: Can I stay motivated throughout the journey?
You can be motivated when you have a fixed goal. Once you define your goal, it will become easier for you to conquer the obstacles standing in your way.
Like any other field of study, engineering to requires effort, dedication, and hard work. However, during your journey, you may encounter subjects or projects that may not guarantee success or the upper hand. In such situations, you have to keep moving forward without getting demotivated.
Question 4: Am I ready to invest my four years?
Most youngsters take up their degree courses to get a good and stable job that can help them achieve their goals. So, if you are interested in pursuing engineering, you must make clear that in these four years, you must maintain your grade card consistently.
Engineering invests multiple years in learning and improving their skills. The journey is of 8 semesters and 4 years, wherein you will come across several projects, assignments, exams, etc. Therefore, if you want to be an engineer, you must ask yourself if you are ready to invest four years dedicatedly.
Therefore, engineering may be an attractive field of study if we look at its returns, but it also demands dedication and determination to make it through. Your love for machines should drive your desire to become an engineer. Sometimes, you may feel demotivated, but you must never regret your choice and accept all the challenges as a lesson.
Congratulations on passing your entrance examinations! You are just a few steps away from becoming an engineer.
Or wait…. Are you?
Getting through the entrance exams is very stressful and challenging but being able to continue and be consistent in your academic performance demands a lot of commitment and dedication. But, hey, don't get worked up. It is easy to create goals and a roadmap to achieve them. As an engineer, you need to identify these career goals and take the necessary actions to reach them.
Setting your career goals can help you achieve your desired accomplishments and advance your career. In this article, we help you understand how to achieve long-term career goals at engineering colleges.
Identify your long-term career goals
Whatever you want to achieve, the most important step is determining your desired long-term outcome. For a career, this goal can consist of your skillset, positions, and accomplishments that you want. When you list your goals with a roadmap, you can move towards them to achieve your ultimate career goal.
Integrate your professional and personal goals
After you are done with writing your long-term professional and personal goals, you can identify the common intersection factors that can either benefit or create conflict. For example, if your career goal is to become an engineer and you personally like building things, then you can be a civil engineer.
Determine long-term personal goals
There is no point in having such goals that do not align with your thinking or lifestyle. You must identify your personal goals and check if they can fit well with the career goals that you have set for yourself. Your personal goals should include character traits, habits, and mental synergy that you hope to develop and practice. These elements are important for you to have a healthy work-life balance. If your personal goals conflict with your long-term career goals, then you may re-evaluate the ones more important to you and come to a mutual understanding about your priorities.
Create short-term goals
You must have heard this saying that little drops of water make up an ocean one day. It is often advised to divide your big goals into smaller fragments so that you can achieve small things, and in the end, they will accumulate and bring you bigger success. Short-term goals can help you plan your long-term career or personal goals and make the process more manageable. You can do this by setting short-term goals that you are sure you can achieve within a day, week, month, or year. Once you accomplish this, it will give you a sense of encouragement and motivation to move ahead faster in your life. For example, if your long-term goal is to improve your efficiency at engineering drawing by 50%, you may set a short-term goal of improving by 2% per month until you reach the end of the semester.
Adjust your goals as needed
You may not always succeed, and that is why you should accept that your goals can also change with time and circumstances. This should not affect your progress. Keeping your goals flexible allows you to take the time to accomplish each goal. This will also help decrease stress and motivate you to work toward your desired outcome.
Wrapping Up
Therefore, there could be multiple goals for engineers, but the main goal is to learn the appropriate skill to be good at what they do. Refining talent and skills are vital to achieving your dreams. So, if you want to accomplish something that you have dreamed of for a very long time, you must set your goals in the right direction and follow the tips mentioned above!

Engineering is a well-known field of study offering education and training on designing and improving several organisations' systems, products, and processes. The right engineering program allows exploring and grabs exciting opportunities to help you achieve your personal and professional goals in life.
An engineering program covers a wide range of subjects, from Physics, Mathematics, Chemistry, Biology, and Computer Science. The curriculum covers design theory, advanced mathematics, core engineering principles, diagrammatic representations, etc.
A student who receives the right direction will become a good engineer. Therefore, it is important to ponder certain points before opting for an undergraduate engineering programme. Even if you are meticulous and dedicated, the right engineering program will propel your career toward excellence.
How to Choose the Right Undergraduate Engineering Program?
Accreditation
Go for engineering programs only if they come with certified accreditation. The presence of an accreditation implies that the institute or university meets the global or national standards of that particular academic field. For example, if you are looking for jobs in the field of mechanical engineering, many employers consider this a point while recruiting candidates only from NBA (National Board of Accreditations). Besides this, if you are applying for an education loan for your mechanical engineering degree, a NBA accreditation makes the process seamless and effective.
Specializations and Sub-Specializations
Studying the various specializations and sub-specializations that the engineering colleges/universities around you offer is crucial. Students can now pursue engineering programmes in varied specializations – thanks to the new National Education Policy (NEP 2020) in force in various states of the country!
Curriculum
Every student interested in engineering must research the curriculum of any prospective school or institute before applying. As the curricula for engineering programme is diverse concerning the range of topics, electives, and practical elements, one must ensure that the programme they are opting for covers the topics of their interest and need.
Growth Opportunities
Every student studies any course to fulfill their goals in the end. Be it a good job, higher studies, or any entrepreneurial venture, your engineering programme should provide you with potential growth opportunities post the completion of the degree.
Reputation
One must consider the reputation of any engineering program that one opts for. You can do this by researching the professional reputations of the professors teaching the program. Quality engineering professors are always more than just ‘graduates’ and possess great years of experience. Researching notable alums can also testify to the programme’s reputation and quality.
Internships
An engineering programme without internships is like a boat without a sailor. It would be best if you had practical training and exposure from industry experts to sharpen your technical skills and help you score a good post-graduation job. Always opt for schools or institutes with tie-ups with prominent corporations or organisations willing to provide internships to undergraduate engineers.
Affordability
An expensive undergraduate programme can often lead to long-term debts even after graduation. Therefore, it is very important to compare and contrast the cost of the affordable and cost-effective curriculum. No programme should have opted that can create a hole in your pocket for the next ten years. Even if you are going for an engineering programme with higher fees, the quality and outcome of the programme should compensate for the same.
Infrastructure and Ancillary Support
A good engineering institute or school provides students with infrastructural support to help them excel in their studies. This includes access to the well-equipped library, laboratory, practical rooms, sports room for extra-curricular activities, a medical room for emergency first-aid, and financial aid such as scholarships to help the students during their financial crunch.
Location
Location is important in determining the programme you are opting for (unless it is an online course). Spending hours in travel will affect the productivity of the students and can also impact your networking initiatives post-study hours. A student must opt for programmes close to their residence or easily accessible, whichever is earlier.
As engineering is a domain area with lucrative career opportunities, it is advised that one research a college or institute properly and consider the pointers mentioned above before selecting their undergraduate engineering programme.

Do you wonder why engineers make extraordinary entrepreneurs? You are not alone, as many people have the same question in their minds when they witness more and more engineers translating their innovative ideas into successful business ventures. Therefore, it can be concluded that engineering graduates have a certain advantage over candidates from other disciplines.
We all know that today’s age is witnessing a revolution, called start-up culture. And engineering graduates are contributing a lot to keep this culture going with immense success and outstanding popularity.
Moreover, engineering students and graduates have been coming up with diverse competitive and innovative ideas for quite some time to start their entrepreneurial journey. Today’s majority of well-known start-up brands are the brainchildren of engineering students as well as graduates.
Why do Engineers make Excellent Entrepreneurs in today’s world?
It is time to check out some key reasons why engineers are making the majority of successful entrepreneurs in almost every industry in today’s world:
Engineers have proved themselves as Excellent Innovators:
Needless to say, innovation is among the prime skills that can transform an idea into a successful business venture. And engineers come with adequate skills and expertise to brainstorm innovative ideas and strategies to turn their dreams into reality. In other words, innovation is one of the main reasons why more and more engineers are managing to prove themselves as outstanding entrepreneurs.
Engineers can scan opportunities with ease:
Needless to say, engineers can find opportunities even in difficult situations and leave no stone unturned to come up with an innovative and effective solution to ease the situation. Needless to say, engineers study, acquire knowledge, and prove themselves in a too much competitive environment throughout their academic years.
As a result, they become capable of extracting opportunities from almost every situation and work accordingly to get success. In other words, the skill of scanning opportunities and brainstorming innovative ideas is another prime reason for engineers becoming great entrepreneurs.
Engineers have Commendable Perseverance:
Engineers, who aspire to become successful entrepreneurs, do not give up on their dreams despite difficulties and challenges. In other words, engineers hold the power to face and survive hardships to make their dream come true.
That is why they can overcome failures with ease and start scanning for alternative ways to find an effective solution to the current problem in no time. In other words, engineers have immense emotional strength that motivates them to keep going and become excellent entrepreneurs.
Engineers are Outstanding Planners:
No one can dream to become an entrepreneur without solid planning. And engineers have excelled in this department as well. The reason is that engineering students work on diverse assignments and projects throughout their academic years. Thus, they become excellent planners and come up as top-class entrepreneurs as a result.
Moreover, when it comes to turning their dreams into reality, engineers have backup plans as well. That is how more and more engineers are getting success in their entrepreneurial journey.
Moreover, engineers know how to be excellent team players and accomplish a task by working together.

Are you interested in pursuing a career in engineering? If yes, then you have to complete a B.Tech degree in your chosen stream as a first step. In short, engineering is one of the most preferred and evergreen courses available after 10+2 when it comes to having a fulfilling, soul-satisfying, and sustainable life.
Nonetheless, the course has been witnessing many changes with time as newer specializations are getting introduced to keep pace with the latest trend and technology. Needless to say, you have to prove your worth and competency while enrolling in an engineering course by cracking the applicable entrance exam (s). Note that only students with PCM (Physics/Chemistry/Mathematics) or PCMB (Physics/ Chemistry/ Mathematics/ Biology) can choose to study engineering.
Different Specializations under B.Tech Courses
Nowadays, diverse specializations are available to make students industry-ready and future-proof. However, it might seem to be a cumbersome and confusing task for some students to select their specializations in the B.Tech curriculum. Don’t worry! The following options help you choose your B.Tech specialization based on your passion and interests:
B.Tech in Computer Science & Engineering:
You can choose to achieve your B.Tech degree in computer science and engineering if you are passionate about making your career in this domain. Needless to say, the degree attracts an abundance of job opportunities in various industries (such as the IT industry) for competent candidates.
Once you complete your course, you can make your career as a software developer, software engineer, test engineer, content developer, or programmer analyst.
B.Tech in Aerospace Engineering:
If you aspire to become an aerospace engineer, then you should go for aerospace engineering. The demand and popularity of competent aerospace engineers are on the rise, so you can expect to have many golden opportunities throughout your career.
Once you obtain the degree, you can start your career as an Aerospace Engineer, Welding Engineer, Aircraft Technician, or Researcher in a top-notch organization.
B.Tech in Civil Engineering:
The demand for competent civil engineers is evergreen due to the growth and development of industrial projects, real estate projects, Smart City projects, and so on. Eligible candidates after completing a B.Tech degree in Civil Engineering can start working as a Civil Engineer, Executive Engineer, Site Engineer, or Structural Engineer.
B.Tech in Cloud Technology & Information Security:
A B.Tech degree in Cloud Technology & Information Security comes with a curriculum in ethical hacking, cloud security, and computer forensics to name a few. If you choose to complete your degree in this specialization, you can expect to work as a Cloud Project Manager, Cloud Security Specialist, Cloud Support Engineer, and so on in the upcoming years.
B.Tech in Cyber Security & Forensic:
Since the inclination toward online financial transactions is on the rise, the demand for competent cybersecurity and forensic candidates has also increased. That means if you would like to contribute to securing online transactions against cyber criminals, you can opt for B.Tech in Cyber Security & Forensic.
As a qualified candidate in this regard, you can embark on the roles of an Ethical Hacker, Information Security Manager, and Malware Analyzer among others.
Some other popular specializations for the B.Tech course include Artificial Intelligence & Machine Learning, Computer Science in Full Stack Development, and Mechanical Engineering.

Have you already obtained a B.Tech degree in Mechanical Engineering? If yes, then it is high time to consider a myriad of career options for your future. You already know that mechanical engineering revolves around researching, designing, and production of versatile machines.
In short, the applications of mechanical engineering can be seen everywhere in the world. That means the demand for competent mechanical engineers is evergreen. Moreover, today’s mechanical engineering field leverages the power of more and more advanced technologies. Therefore, as a mechanical engineering graduate, you need to stay updated with the latest tools and technologies to broaden your horizon.
Some Popular Career Options after B.Tech Mechanical Engineering
Mechanical engineers play crucial roles in society. Whether it is about leveraging technical expertise or catering to client’s requirements, mechanical engineers leave no stone unturned to prove their competence and expertise. Let us discuss some of the most popular career options for mechanical engineering graduates:
Post Graduation or M.Tech in Mechanical Engineering:
One of the most popular career opportunities for mechanical engineering graduates is to obtain an M.Tech degree. Postgraduate students get to obtain in-depth knowledge of various subjects in mechanical engineering.
Thus, they can make sure of better job opportunities in the upcoming years. Also, if you want to broaden your horizon in the research field of mechanical engineering, then you have to enroll in a postgraduation course followed by Ph.D.
Government Jobs:
Do you want to start working as an employee after completing a B.Tech degree in mechanical engineering? If yes, then there are diverse government jobs available for competent candidates in organizations, such as DRDO, national research laboratories, and so on.
You can apply for jobs based on the required criteria. Note that you need to prove your worth to start working in a government job in a reputed organization.
Internships:
Would you like to acquire real-life industry knowledge, expertise, and experience after your graduation? Then, you can apply for internships in prestigious organizations. Although you can take up an internship during your last semester, applying for one after graduation can do wonders for your career. Thus, you can get ready for various job responsibilities that you would apply for once you obtain your internship completion certificate.
Teaching Jobs:
As an engineering graduate, you must have excellent expertise in physics and mathematics. Hence, if you are interested in teaching students, you can apply for teaching jobs in high schools. If you wish to advance your career further in the teaching profession, you can opt for professional courses, such as B.Ed.
Private Technical Jobs:
The majority of engineering graduates opt for private technical jobs via campus placements or walk-in interviews. If you succeed to show your worth and competence in front of employers, you can expect to land a high-paying job in a top-notch company. Did you know engineering is one of the professions, which is highly promising as well as beneficial?
Hence, what are you waiting for? Choose your career option today and soar high in your profession.

Are you an electrical engineering graduate? Then, you must have been dedicating a significant time a day to consider your career options. As an electrical engineer, you have already gained basic knowledge of the field.
Now, it is high time to opt for the most suitable career option for you to reach your goals and achieve something great in your life. Knowing about the available career opportunities in electrical engineering helps you decide whether you would like to advance your career in the same field or switch to a different path.
Some Best-in-Class Career Opportunities for Electrical Engineering Graduates
As an electrical engineering graduate, you have a myriad of career options from which you can choose your preference based on your passion, interest, and skill sets. Every industry calls for competent electrical engineers to cater to various responsibilities. That is why it is a must for you to know about the responsibilities for a specific job role in advance so that you can make an informed decision. It is time to check out some of the popular career options for electrical engineering graduates below:
Micro Electrical Engineer:
One of the most popular fields for electrical engineers is microelectronics. And as a micro electrical engineer, you would have to design small electronic parts, such as microchips, circuit boards, semiconductors, and so on, which contribute to designing diverse electronic, biomedical, aerospace, and IT devices.
Did you know that the demand for micro electrical engineers has increased by approx 26%? Hence, if you are interested in microelectronics, many golden opportunities are awaiting you.
Electrical Engineering:
You can also opt to work in the core electrical engineering jobs. Your job responsibilities would revolve around large-scale electrical systems, including motor control, transmitting energy, power transmission, and so on. You need to contribute to designing and developing test equipment, and electrical systems and solve day-to-day challenges in the company you are going to work for.
As an electrical engineer, you can choose to work on an array of technologies ranging from household appliances, electrical power stations, satellite communications, telecommunication systems, and so on.
In short, the demand for electrical engineers to design and maintain electrical control systems and other day-to-day equipment is evergreen. Hence, if you would like to work in a core electrical engineering job, there won’t be any dearth of opportunities for you.
Instrumentation Engineer:
As an instrumentation engineer, you would be contributing to working on automated processes to boost reliability, safety, optimization, stability, and productivity.
Did you know instrumentation engineering is considered among the best career options for electrical engineering graduates? Hence, if you have unique thinking abilities, required skill sets, and adequate problem-solving skills, you can opt to be an instrumentation engineer.
As a competent instrumentation engineer, you can choose to work in one of the diverse fields, including machinery, automation, manufacturing, construction & railways, and so on.
Wrapping Up
Electrical engineering graduates have many scopes to make a bright career and reach their professional goals. Hence, what are you waiting for? Choose your career path today and start gaining experience for your future.

Contemplated as one of the most lucrative career choices, engineering can certainly be observed as a dream career for millions of candidates. Nonetheless, cracking the engineering entrance exam is not child’s play! From JEE to many more engineering entrance exams, the aspirants need to work hard, stay devoted and follow the right strategy to taste success in these much popular and highly competitive entrance exams.
If you are determined to clear your engineering entrance exam, no one can stop you from achieving your dream. Here, we have mentioned five significant tips that will help you put your best foot forward and crack engineering entrance exams with flying colours.
Most Efficient Tips to Crack Engineering Entrance Exam
Always think positively. Leave no stone unturned. Stay confident and follow all the above tips that ensure your success in engineering entrance exams. Good luck.
Are you an engineering student and getting nervous about your upcoming semester exam? Do not worry! There are some key strategies through which you can expect to do well in your semesters. Since you have many aspirations and goals associated with a career in engineering, it is time to set all worries and anxieties aside and gear you up for the battle to prove your worth and excellence.
Key Strategies to get prepared for Upcoming Semester Exams in Engineering
Set a Schedule to Study:
The first step is to give cues to your brain to get ready for a study session. Having a customized study schedule makes you punctual and keeps your inspiration to study intact throughout the session.
You can tweak the schedule from time to time to accommodate other priorities, such as extra classes or group study sessions with friends. However, you should dedicate most of the time in a day to preparing for your semester exams, especially when the exam dates are out.
Revise & Practice as much as possible:
Collect the question papers of the last few years and go through them carefully. You would certainly find some topics to be more important than the rest by the number of questions asked from the same. Note down those topics and prepare separate strategies to cover them with the ace.
Revision is a crucial part of the preparation for every exam, and the semester exams are no exception. Revise the concepts you have already covered as much as possible. Never start learning concepts before a couple of days of the semester. Dedicate the time to revise and practice.
One of the best ways to brush up on the concepts and check your proficiency level is to take as many mock tests as possible. Thus, you can also get a scope to get a taste of the actual semester exam, as you would have to complete writing within the same time as the actual test.
Seek help whenever needed:
You might get stuck on tricky concepts in your syllabus once in a while. Do not hesitate to seek support in such situations. Reach out to your professors to get your queries resolved to get a clear idea about the complex topics.
The initiative on your part would help you draw the attention of your faculty members. As a result, you can expect some extra guidance or tips from them for your semester preparation. Do not forget to take small notes during your doubt-clearing sessions with professors to recall the concepts later.
Make plans for Group Study:
One of the best ways to prepare for exams is to exchange knowledge with like-minded people. Make schedules for group studies to clear doubts on various concepts together with your friends.
Helping others in clearing concepts also helps you brush up on the concepts you already learned. Take the help of your friends to get a better grasp of difficult concepts in your semester’s syllabus.
What are you waiting for? It is time to start a solid preparation for your upcoming exams and give it your best shot. Never panic, keep your motivation intact instead!

The advancements in cybercrimes around the world made it mandatory to hire more and more cyber security experts in organizations across different industries. Needless to say, it is the key reason why India is experiencing the surge in demand and popularity of competent cyber security experts. However, if you are interested in building your career in this niche, you need to be familiar with the latest trends and future career prospects in cyber security.
In essence, the graph of the future career opportunities in cyber security is upward, as the IT sector in India has witnessed potential job growth in cyber security over the last couple of years. Even a majority of businesses have already started their journey in cyberspace.
Businesses worldwide cannot keep running their operations without leveraging the power of the Internet. It marks the importance of cyberspace in organizations across diverse industries although the level of dependency may vary. Needless to say, the circumstance has taken the necessity of cyber security to the next level, which has further brightened the current and future career prospects in this industry.
Why is the demand for cyber security professionals on the rise?
All of us have been witnessing advancements in the IT industry over a few years. And it has come with the potential of various cyber security threats, which have been evident from different hacking incidents.
Whether it is a data breach, scam, or exploitation of sensitive information, the figures of cyber attacks are showing the severity of the situation. That is why more and more organizations have started hiring competent cyber security experts to secure their security and privacy online. And the upcoming years would also witness the growth of cyberspace and the importance of cyber security professionals.
Future Career Prospects in Cyber Security
Many colleges in India have already collaborated with cyber security experts to gear students up with the necessary knowledge, skills, and expertise to help them build successful careers in the industry. Thus, next-generation professionals can grasp all the latest information and be familiar with the current industry trends in cyber security to address all the concerns in this regard.
Today’s industry experts are leaving examples in terms of their analytical skills to enable future professionals to address cyber security issues regardless of complexity. The key goal is to counterattack cyber criminals and take preventive measures on time to check or minimize the potential risks.
You already know the demand for cyber security professionals won’t go down anytime soon. And when it comes to the top career opportunities in cyber security in India, ethical hacking secures one of the top ranks.
Ethical hackers are competent cyber security professionals with a rigorous understanding of the mindset of a hacker to spot vulnerabilities in the security network and applications of a company. It is one of the high-demand career opportunities in cyber security to ensure a secure cyber security network of an organization.
On the other hand, cyber security analyst and security architect are two other sought-after job roles for cyber security experts.

Would you envision yourself being a successful engineer in the future? Have you already enrolled in an engineering course? Whether you are currently an engineering student or about to become one, you need to know how to become a good engineering student. In other words, you need to be familiar with how to make the best of the 4-year of your college life.
Needless to say, some of the best brains can only get the opportunity to pursue an engineering career. That means you have to step up your game to stay ahead in the competition while maintaining an excellent relationship with your peers.
A Few Easy Strategies to become a top-class Engineering Student
Work on Your Goals & Dreams from the Beginning:
Pursuing higher studies is all about expanding one’s horizon and gearing up for a professional career. Some students do not emphasize their first-year study and get lost in their newfound freedom of adult life.
However, if you have big dreams in your life and envision yourself being a successful professional, pay heed to your courses straight from the beginning. The first-year study creates momentum for the remaining years.
Moreover, your final CGPA (Cumulative Grade Point Average) would be calculated based on your every semester’s performance. And you know very well how high CGPA can give you an edge over your peers in the placement drives later.
Emphasize the Importance of Networking & Expand Your Horizon:
An engineering student should work on networking right from the beginning of the academic session. That is why you need to be familiar with your peers, alumni, and faculty members to attract opportunities and become a popular face on campus. Thus, you can take your confidence to the next level and do wonders in campus interviews.
You can start your journey to expanding your network by forming a small study group. Exchange ideas, knowledge, and concept with your friends in your close-knit group. As a result, you can keep your motivation and positive energy intact while away from your home (if you are living in the college hostel) and face challenges without getting frustrated.
In addition, being in touch with your professors and alumni helps you stay updated with the latest trends in the world of engineering. Having an in-depth conversation with your faculty members would not only help you with academics but also with your job preparation.
Ask as many questions as you want:
Do not be a student, who hides behind others throughout the lectures. It is high time to come out of your shell and leverage the power of exposure that the engineering course brings to you.
Be a proactive student and ask as many questions as you want to resolve all your queries. It is time to acquire new knowledge and upgrade yourself. Take your learning curve to the next level by covering concepts in advance. You may ask permission from your professors to help you with your queries during office hours to acquire more clarity in the subjects.
Do not forget to keep working on your resume by adding new milestones as you achieve them.

A Brief Introduction
Do you want to pursue engineering in your higher studies? If yes, then you must be familiar with various branches of engineering to opt for your preference. Do not go for others’ opinions or perspectives if you do not want to end up getting disinterested or disappointed in the final year of your course.
The selection of an engineering branch depends on your interest and preference while the future job prospects or business opportunities should also be considered. Having a degree no longer gives an edge to a candidate- it is the expertise, knowledge, and skills that make all the difference. And choosing a branch you are not passionate about won’t work in your favour in the long run.
Opt for the Best Engineering Branch: Some easy-to-follow tips
Whether you are going for a core engineering branch or a non-core engineering branch depends on your preference and future goals. While Civil Engineering, Mechanical Engineering, and Electrical Engineering are considered core engineering branches, Computer Science Engineering, Information Technology (IT), and Electronics and Telecommunication Engineering are regarded as the most popular non-core engineering branches.
Based on all the above-mentioned considerations, choose an engineering branch that serves well to your expectations as well as dreams!

A Short Introduction
Did you know Construction Engineering Technology comes as a vast field with tremendous career opportunities? Competent engineers leverage the power of construction technology to convert ideas into reality when it comes to building roads, airports, bridges, buildings, railroads, and so on.
In short, construction technology contributes a lot to the development, advancement, and welfare of a nation. Hence, needless to say, today, construction technology is the most sought-after career choice of students considering the job opportunities and job growth potential ensured by Construction Engineering Technology.
Students in this field get familiar with all the latest aspects of architectural engineering, civil engineering, construction management, and so on. Thus, pursuing your career in Construction Engineering Technology helps you stand out in the crowd with your knowledge, skills, and expertise as a construction manager and an engineer alike.
Career Prospects in Construction Technology
In essence, the building and construction industry is growing leaps and bounds and creating loads of golden career opportunities for competent candidates. Do you wonder what potential opportunities you can expect once you have achieved a Construction Engineering Technology degree? Let us discuss it below:
Upon completing the Construction Engineering Technology degree with flying colors, you can join a construction company as a site engineer or a construction planning engineer. The projects you would be working on include commercial buildings, residential buildings, hospitals, cooperatives, railways, roads, and so on.
You can also opt to join a construction company as a chief engineer (based on your experience) and collaborate with an architect to complete vast construction projects. Do you want to take your career to the next level in construction technology? Then, you can opt to specialize in a preferred yet demanding field of construction. For instance, if you want to build a promising career in railways, then you can choose to be a tunnel engineer.
Note that Construction Engineering Technology familiarizes you with all the requisites of construction, so you can start your career as a project supervisor or supply chain manager.
What is the Expected Salary of a Beginner Construction Technology Professional?
Note that the potential and prospects of employment in construction technology are immense. However, the entry-level salary of a professional depends on several factors, such as the organization itself, academic qualifications, experience (such as internships), job roles, and so on.
On the other hand, professionals aspiring to work as specialists in construction technology (like tunnel engineers) can expect huge salaries. Although a site engineer can expect to earn a decent salary, the prospects of growth and increment are abundant.
Wrapping Up
Construction technology is one of the well-known branches of civil engineering that lets students get familiar with non-technical as well as technical aspects of building roads, railways, private or public buildings, and so on.
Since the latest economy is witnessing rapid growth and advancement in the construction domain, construction technology professionals can expect immense opportunities to build their dream careers.
Are you a detail-oriented individual? Are you ready to face day-to-day challenges revolving around construction projects? Would you like to stay updated with the latest trends in the construction industry? Then, construction technology can be an ideal career option for you.
Over time, there has been an overpowering surge of a few individuals wandering into the world of information science and utilizing artificial intelligence (AI) and machine learning (ML) strategies to test measurable regularities and construct immaculate data-driven items. In any case, it's found that a few need the vital numerical instinct and system to urge valuable results. Recently, there has been an upsurge in the accessibility of numerous easy-to-use machines and profound learning bundles such as sci-kit-learn, Weka, TensorFlow etc.
Artificial intelligence and machine learning hypothesis may be a field that converges factual, probabilistic, computer science and algorithmic angles, emerging from learning iteratively from information and finding covered-up bits of knowledge which can be utilized to construct smart applications. Despite the huge conceivable outcomes of the machine and profound learning, an intensive scientific understanding of several methods is essential for the internal workings of the calculations and getting great results. Whatever your objective is, whether it’s to be an Information Researcher, Information Examiner, or Machine Learning Design, your essential range of centre ought to be on Mathematics.
Mathematics is the essential building piece to fathom all the business and information-driven applications within the real-world situation. From analyzing company exchanges to understanding how to develop within the day-to-day advertising, making future stock expectations of the company to anticipating future deals, mathematics is used in nearly every zone of trade. The applications of mathematics are utilized in diverse businesses like retail, fabricating, and IT to bring out the company diagram in terms of deals, generation, merchandise, admissions, the wage paid, forecast of their level within the show advertise and much more.
What level of Mathematics do you need?
The primary address when attempting to get into intriguing fields such as artificial intelligence and machine learning, the sum of arithmetic vital and the level of science is required to get these strategies. The reply to this address is multidimensional and depends on the level and interest of an individual. Research about scientific details and hypothetical progression of machine learning is continuous and a few analysts are working on more progressed procedures. The least level of arithmetic is required to be a machine learning scientist/engineer and the significance of each scientific concept.
Mechanization and machine learning has changed our lives. From the foremost mechanically smart individual working in driving advanced stage companies like Google or Facebook to somebody who is a fair smartphone client, there are exceptionally few who have not been affected by manufactured insights or machine learning in a few shapes or the other; through social media, savvy keeping money, healthcare or indeed uber. From self–driving cars, robots, picture acknowledgement, demonstrative evaluations, suggestion motors, photo labelling, fraud detection and more, the long-standing time for machine learning and AI is shining and full of undiscovered possibilities.
With the guarantee of so much advancement and path-breaking thoughts, any individual will be inquisitive about cutting-edge innovation and may aim to create a career in machine learning. But how can you learn about the latest technologies and the different areas that contribute to them? You would have heard about numerous cool-sounding work profiles like Information Researcher, Information Examiner, Information Build, Machine Learning Build etc., they are not only monetarily fulfilling but also allow one to develop as an engineer and work at some of the foremost productive innovative companies. Now the question is, how do you start to set a career in machine learning? What instruction foundation ought you seek after and what aptitudes will be required? Machine learning may be a field that includes, insights, computer science and calculations that are used to make shrewdly applications. These applications can gather valuable and smart data from information that is valuable to reach trade bits of knowledge. Since machine learning revolves around the consideration and application of calculations, it is crucial to have a foundation in mathematics.
Today, data is a vital aspect of any business. Companies use and construct various data structures to build customer relationships and respond to business queries. A wide range of technologies is applied to the data to understand customers and their requirements. Managed by distinct technologies and stocked up in several structures data analysis becomes a challenging task. However, the tools owned for analysis accept that the data is from a single technology and stored in an identical structure. Data engineering eases the process of providing reliable and secure data to scientists, data analysts, and other professionals who work with data regularly.
The importance of data engineering and its scope as a career choice has been growing exponentially in recent years as companies of varied sizes rely heavily on data. Some of the points that support the above statement are:
Data engineering organizes and manages suitable data for different systems and various data consumers, such as system architects, business leaders, data analysts, and data scientists. Some vital areas of data engineering are:
The above responsibilities are well addressed by data engineers through data acquisition, cleansing, conversion, disambiguation, and de-duplication. Hence, data engineers should possess the ability to work on different technologies using specialized tools.
Programming and math/statistics are two of the most critical technical abilities for a data engineer to acquire.
Programming: Software developers transitioning to an AI role or those with a computer science degree are likely to be familiar with a few programming languages. Python and R are two of the most widely used languages in AI, particularly machine learning. Every aspiring data and AI engineer must be well-versed in these two languages, as well as their most often used libraries and packages.
Math / Statistics: More than merely coding, data and AI engineering require math and statistics. Machine learning algorithms are based on statistical and probability notions. When verifying the authenticity and integrity of your data, you will also require a good grasp of terms like statistical significance.
Artificial intelligence and data engineering provide a reliable artificial intelligence solution that can work at scale by providing usable products to clients. Artificial intelligence and machine learning possess high demand for data that is impossible to scale by human engineers. To incorporate artificial intelligence capabilities and feed the data-hungry models many transformative technologies must be implemented for the analysis and storing of data. If the role of a data engineer lies in preparing the data, then the data scientist's responsibility is to use the data for the promotion of business decisions. To summarise, a career in data engineering is both challenging and rewarding because providing artificial intelligence assistance to a wide range of companies in industries such as healthcare, retail, finance, etc. becomes unrealistic without structured data and the technical resources to mine the data. Data engineering experts with technologies to mine the forthcoming zettabytes of data will be the need of the hour in the coming future.

Electronics and Communication Engineering have evolved as the spine of the technological innovations of modern times. From satellites to telecommunication to robotics to 3D gaming ECE graduates are in high demand in the labor market. Below we have listed some out-of-the-box careers for WCE pursuers.

Dhivya S and Madhulekha Rakshit
Industry 4.0, which is referred to as the fourth industrial revolution, emphasizes automation as the key to production. 3D food printing has become a fundamental and automated aspect of food production and processing. Therefore, the issues such as printed food safety and the process of food printing will initially be confronted by customers. Let us discuss how 3D printing has revolutionized the food industry in a nutshell.
In general 3D printing is the additive process where a product is designed, coded, and then printed in three-dimensional form. In the 3D food printing manufacturing process, the ingredients are taken in the correct proportion and added to the cartridges, which are then extruded through the syringe in the coded ratio layer by layer. These filling ingredients are pre-heated for smooth flow and processing and maintained in the proper viscosity needed for shape retention. So, this type of manufacturing is the end of the fantasy.
3D printing was invented by a Japanese scientist in the 1980s. His design used a photosensitive resin whose polymerization was triggered by UV light. The technology was initially used by astronauts for space missions and later, products in puree or paste form were extruded and printed. So, the bakery and confectionary products come to the list first for 3D printing.
Companies like REM3DY Health, Natural Machines, etc., use 3D printers for their products. These are confectionery products that are flawless in terms of shape and color ratio, resulting in increased market share. All upcoming R&D ideas are keeping 3D printers as part of their novel product plans. Nutritionists use this technique to create and manufacture their products so they can maintain the right amount and healthier alternatives of raw material.
From the consumer’s point of view, 3D printed food products will be more attractive as they are customizable, artful, and intriguing. Bakers, for example, can produce their goods in less than 5 minutes with robots in the printers, allowing them to work faster and increase the value of their products. Extrusion-based printing (low viscous products), binder jetting (powdered form ingredients), and inkjet printing (surface decorating) are some of the types of printers available to producers. Depending on their needs, producers can choose one of these.
While discussing the advantages of 3D printing, their ability to design products that are complex, sophisticated, and difficult for a human to design is considered. Additionally, it offers the potential to completely automate food production processes, with substantial reductions in food waste. Some of these advantages are accompanied by disadvantages, such as it is not possible to print meat, fruit, vegetables, or rice by nature, so additives, such as hydrocolloids, are required to enable them to be extruded. Continual heating and cooling promote the growth of bacteria and fungi in food. However, the eco-friendly, sustainable and low waste generation characteristics of the 3D printed foods will make this technique successful in the future.

Engineering still features high on the list when it comes to graduate programmes in India, as this profession has shown flexibility and ability to adapt to changes in requirements, as well as providing students with the necessary knowledge and skills for a successful career. The disciplines of engineering teach students concepts of mechanics, civil engineering, urbanization technology, electronics and telecommunications, and other associated disciplines due to the high demand and comprehensive prospect of engineering as a career. Civil is one of the mother trades of engineering is one of the strongest and perennial disciplines of this technical academic course.
In the next ten years, given our cities and villages facing infrastructure problems, it is likely to become repetitive. While every industry is critical to economic development, infrastructure is a significant growth engine worldwide in the 21st century. In India, we need more highways, more airports, more houses, and more to meet the city’s mass urbanization pressures and collapse. Substantial progress can be achieved in all fields and major human-related improvements, civil engineers are expected to face many obstacles, including environmental infrastructure construction.
The career prospect of civil engineers had been slummy in India for some time back, however, since 2020 this trade has regained its stature with a boom in infrastructural domains due to the following factors
Career prospect of Civil Engineers in India
Once you have graduated in Civil Engineering from any of the accredited technical colleges or universities of India you can aspect a prosperous career in the following fields.

In today's information technology world, data mining and cloud computing are emerging trends. The process of extracting information from raw data is known as data mining, and cloud computing provides scalable and flexible computing.
Cloud Computing concept
Cloud computing has emerged as one of the most popular and trending courses among IT enthusiasts in recent years. Cloud computing is now accepted by both small and large multinational corporate houses and not just IT professionals. This new technology has significantly aided individuals and businesses in storing data at a lower cost. Businesses are increasingly seeking professionals who have completed Cloud Computing courses like DevOps training.
Career Advantages of Cloud Computing
Cloud computing provides benefits to modern businesses, such as allowing multiple users to view data in real time and easily share projects. Working as a synchronized team is now easier and more accessible than ever thanks to cloud software and SaaS applications (Software as a Service). Simply put, cloud computing is internet-based computing, and moving to the cloud is the best way to keep your business current and competitive. And on the other hand, we can use data mining to make smart market decisions, run accurate campaigns, make predictions, and more; we can also use data mining to analyze customer behaviors and insights. This leads to enormous success and data-driven business. Hence, we conclude that cloud computing and data mining is one of the best courses one should opt for which helps one to grow in the business and the one who opts for this course will get their business analytics and technology skill upgrade.
Undoubtedly there are multiple career advantages of studying cloud computing and data mining and hence it is a great choice if you are choosing this course for your undergraduate or post graduate studies evidently you will enjoy a rewarding career.

From lightening up rural areas to powering up high voltage power manufacturing units, electrical engineers are required in every organization that deals in construction projects or deals with real estate or manufacturing or making human life easier. If you are keen on pursuing a career in the field of electrical engineering, there are some “must-have” skills that you must essentially possess, to build an outstanding career.
Below we have discussed some of the most essential qualities an electrical engineer must unfailingly have:
Formal technical training
The foundation of any engineering career rests on understanding the principle of science involved in it. Like in mechanical engineering you must have a fair knowledge of machines, similarly, in electrical engineering, you must have a strong grasp on circuits, conductors and others which you can attain only with a formal degree. You can pursue B. Tech in electrical engineering if you have dreams of making a successful electrical engineering career. It is a six-semester formal technical training in electrical engineering that is awarded by all the reputed colleges and universities.
An analytical and rational mind
The projects in which electrical engineers are involved, they have to contribute in every stage from planning to procuring to design and execution. For completing all these procedures, he will come across many roadblocks. He must hence have a critical and analytical mind that will help him to anticipate problems and solve them at an initial stage. Prospective electrical engineers must be rational enough to provide innovative, cost-effective, and secured solutions for problems.
Flexible speaking and writing capabilities
Electrical Engineers have to work and coordinate with a diverse category of people. Right from communicating with the management for approval, to getting work done with the workmen, to dealing with raw materials suppliers, a lot of responsibility rests with electrical engineers. The mode of communicating with a construction worker is completely different from that of speaking with the management. Hence a to be a successful civil engineer, you must develop versatile communication skills.
Acumen in Physics and Mathematics
An electrical engineer is responsible for various calculations on the construction site. The design involves using a lot of calculations and theories which as an engineer he is responsible for. He must be efficient in calculating the ratio and proportions or voltage, quality of electrical equipment and raw materials along with acumen in physics and engineering principles which is essential for successful completion of construction.
A sporting team player
Every profession demands good team playing skills and electrical engineers are no exception. An electrical engineer has to work in liaison with different departments, so he /she must have the natural team spirit of working together with all. A project is easily and successfully done if all the teams act in cohesion especially when the work is very challenging and comprehensive.
Adaptableness
Every organization has multiple projects going on at the same time as an electrical engineer you might have to handle multiple projects at the same time. You will have to handle diverse teams with different, ethnicity and different values. Adjusting to different geographic and cultural conditions is also a challenge for prospective electrical engineers. Adaptableness to any terse situation is hence an essential condition for all would-be engineers.

Today, B.Tech Aerospace Engineering is one of the most highly sought after courses among young people. Aviation and spacecraft are the topics covered in the course, including their study, design, and development, whether automated, power-driven, or operated manually. It additionally includes the study of diverse Aviation and spacecraft procedures and theories. If you are studying aerospace engineering or planning to choose it after your 10+2, you must know the future career opportunities to make a successful career. In the following part of the article, we will suggest some career options to aid you to choose the right career path for yourself.
Aerospace Engineer
Aerospace engineering is a prospective career option for mechanical engineering students. The primary responsibility of aerospace engineers includes designing.
In addition, aerospace engineers are also responsible for devising new technologies for aviation and other associated industry. If you are going to pursue this career opportunity, you will be able to design, assemble and test aerospace products and aircrafts.
Public sector Job opportunities
The public sector offers exciting career prospects for B.Tech graduates in Aerospace Engineering. The government's research organizations and aircraft manufacturers have many vacancies for Aerospace Engineers. Listed below are some of these institutions.
Flight Technicians
There are a number of fields in India that you can choose from if you wish to work as a flight technician. You can become an aircraft mechanic, an aerospace technician, or an avionics technician. Your main tasks will be to maintain, construct, and regularly troubleshoot and test the operating systems of the aircraft so that they work properly.
Rocket Scientists
Even though rocket science may seem exciting, there is a lot of hard work involved. The job requires you to design and test propelling systems used in rockets, which is a high-pressure job. In addition, you will be required to conduct regular and intensive research into space technologies and understand, operate and maintain the hardware used in space missions expertly
Spacecraft Crew Members
A career in aerospace engineering is the perfect career choice if you have always dreamed of traveling through space. To stand out against the fierce competition you are bound to encounter, you must possess extensive knowledge about spacecraft engineering. B. Tech Aerospace Engineering provides you an extensive understanding of space technology so that you can have a prosperous career.
Technical Communicators
Having exceptional communication skills can help you become a technical communicator. This will require you to act as a link between the crew of the spacecraft and control room technicians on the ground. It is critical that you have a thorough understanding of the complex technical terms and scientific jargon used in space technology.
Nuclear Engineer
As the job title suggests, a nuclear engineer is responsible for ideating, designing, and manufacturing machines and technology that can reap the benefits of nuclear energy and radiation.
Robotics and Automation Engineer
Last but not least, this is the most futuristic career opportunity for mechanical engineers. From building futuristic automated intelligent machines to human look-alike robots, robotics and automation engineers will have huge career opportunities in the coming years.

Mechanical Engineering is all about machines, their study, designing, and development, operated either by automation or power-driven or by manual interference. It additionally includes the study of diverse mechanical procedures and theories. If you are studying mechanical engineering or planning to choose it after your 10+2, you must know the future career opportunities to make a successful career. In the following part of the article, we will suggest some career options to aid you to choose the right career path for yourself.
In addition, aerospace engineers are also responsible for devising new technologies for aviation and other associated industry. If you are going to pursue this career opportunity, you will be able to design, assemble and test aerospace products and aircrafts
Automotive Engineer -The automobile industry can provide endless opportunities to mechanical engineers, as they can use their formal education knowledge to design manufacture, and test automobiles and their parts. As an automobile engineer, you will be responsible for end to end fabrication of an automobile right from its design ideation to production.
CAD Technician - ‘Draughtsman’ is a well-known term in the construction, manufacturing, and engineering industries. A draughtsman is responsible for preparing technical plans and drawings, though earlier it was done manually, all the designing activities are done with the help of CAD software, and hence draughtsman is now synonymously known as CAD technician. Mechanical Engineers have a good career scope as CAD technicians.
Consultants in Construction Sites - Construction sites no doubt require a civil engineer, there is a requirement of mechanical engineers as well. Every construction sites have heavy machines and vehicles required in various construction procedures. A mechanical engineer hence is required in construction sites for the maintenance of those heavy pieces of machinery.
Control and Instrumentation Engineer- Also known as C&I engineers, they are responsible for manufacturing, installation, management, and maintenance of types of equipment that are used for supervising the engineering systems, heavy machines, and mechanical processes. The job responsibility of C&I engineers is to look after that machines and operating processes are working effectively, efficiently, and safely.
Maintenance Engineer - Mechanical engineers in this job role will be responsible for looking after the prevention and maintenance of heavy types of machinery in plants and manufacturing units. They will be responsible for supervising any machinery break down, looking after if the machines are working properly and if they need any repairs. They are also responsible for procuring the manpower and raw materials required for the healthy operation of the machines.
Nuclear Engineer - As the job title suggests, a nuclear engineer is responsible for ideating, designing, and manufacturing machines and technology that can reap the benefits of nuclear energy and radiation.
Medical Equipment Engineer - Mechanical Engineers willing to make a career in the field of bio-medical will be responsible for designing machines and tool that makes surgeries and medical treatments minimally invasive.
Robotics and Automation Engineer - Last but not least, this is the most futuristic career opportunity for mechanical engineers. From building futuristic automated intelligent machines to human look-alike robots, robotics and automation engineers will have huge career opportunities in the coming years.

Rightly said by Isaac Asimov an American writer, professor of biochemistry
“Science can amuse and fascinate us all, but it is engineering that changes the world.”
Engineers are the shapers of the modern world. They are the makers of machines and systems and constructions that makes human life easier. However, to become an engineer one must have a creative attitude and out of the box thinking. There are many challenges that an engineer faces from constraints of science to limitation of modern technology, to availability of materials and resources to health and safety. Hence to become an engineer one must have an innovative outlook and certain inherent skills. So to know if you are ready to be an engineer, here are few things you must ask yourself.
Do you have a rational mind and analytical thinking?
The projects in which engineers are involved, they have to contribute in every stage from planning to procuring to design and execution. For completing all these procedures, he will come across many roadblocks. Hem must hence have a critical and analytical mind that will help him to anticipate problems and solve them at an initial stage. Prospective engineers must be rational enough to provide innovative, cost-effective, and secured solutions for problems.
Are you well versed with laws of Physics and Calculation?
An engineer is responsible for various calculations on his/her projects. Designing be it a machine or a structure or a code, it involves using a lot of calculations and theories which as an engineer must have dexterity. He must be efficient in calculating the ratio and proportions of raw materials used in the project along with acumen in physics and engineering principles which is essential for successful completion of a project.
Do you have the Formal Training?
The foundation of any engineering career rests on understanding the principle of science involved in it. Like in mechanical engineering you must have a fair knowledge of machines, similarly, in civil engineering, you must have a strong grasp on design and construction which you can attain only with a formal degree. You can pursue B. Tech in any engineering trade you have knack for. Engineering is typically a six-semester formal technical training that is awarded by all the reputed colleges and universities.
Do you have flexible communication skills?
Engineers have to work and coordinate with a diverse category of people. Right from communicating with the management for approval, to getting work done with the available resources, to dealing with raw materials suppliers, a lot of responsibility rests with civil engineers. The mode of communicating with a construction worker is completely different from that of speaking with the management. Hence a to be a successful engineer, you must have versatile communication skills.
Are you a team player?
Every profession demands good team playing skills and engineering is no exception. An engineer has to work in liaison with different departments, so he /she must have the natural team spirit of working together with all. A project is easily and successfully done if all the teams act in cohesion especially when the work is something very challenging and comprehensive like creating something new.
Can you adapt in adverse situation?
Every organization has multiple projects going on at the same time and as an engineer you might have to handle multiple projects at the same time. You will have to handle diverse teams with different, ethnicity and different values. Adjusting to different geographic and cultural conditions is also a challenge for prospective engineers. Adaptableness to adverse situation is hence an essential condition for all would-be engineers.

What to Do After Engineering in Computer Science?
Computer Engineering has been the most sought-after course, especially for those who want to pursue a technical career. Computer engineering opens up numerous career options and higher study opportunities for young aspirants. So here we have listed out some career options that you can pursue after you complete your graduation in computer science.
A career in Computer Application Development
Upon passing out engineering in computer science you can choose to work on the primary areas of computer science like algorithm development, structure, and administration of computers, application development using multiple programming languages, information managing, and handling, etc. Foraying in such skills will help you to explore career opportunities like Network Administrator, Web Designer, Web Developer, Database administrator, System Manager, Research Analyst, Computer Programmer, Software Developer, and Software Tester.
A career in Cloud Technology and Information Security
Aspirants who want to work in this field will have the opportunity to work on fundamentals of operating systems and programming languages, provide hands-on experience in Java programming, key aspects of android, data structures, and Linus. You will also have exposure to extensive knowledge about computer networks, mobile architecture, and app development. Concepts like the configuration of server and database management are also a part of the course. You can expect to work for job titles like Cyber Security Consultant, Security Analyst, Security Architect, Security Engineer, Risk Analyst.
A career in Artificial Intelligence
With the concept of Industry 4.0 emerging along with the rise of exponential technologies, artificial intelligence is the most sought-after sector. Students interested in this field of technology can explore careers as Software Engineers, Software Developers, AI / Machine Learning software developers, AI / Machine Learning Specialist, Data Analyst, Data Engineer, NLP (Natural Language Processing) Engineer, Automation Engineer, Technical Support Engineer, Digital Transformation Consultant and lots more.
A career in Gaming Industry
This is another offbeat choice for students who want to pursue a technical career after computer engineering. You can explore the following career opportunities in the gaming industry
A creative career in Graphics & VFX
Graphics and VFX Course is another exciting career where students with computer engineering can foray into. Spirants can work in graphic designing, visual effects, fundamentals and techniques of VFX, Animation both two dimensional (2D) and three dimensional (3D), digital filmmaking, FX, Dynamics, and Simulation. If you are capable of thinking out of the box and yet utilizing your technical skills, graphics and VFX can be a great career choice for you.
A career in Cybersecurity
This career opportunity is also suitable for students of computer engineering where they will get the scope of working on the technologies of cyber security, application security for java/application security for .net, cyber-threat intelligence, cyber security incident handling, fundamentals of information security.

Indispensable Skills of a successful Civil Engineer
The world around us is changing; to pace up with the evolving technologies and growing needs of the society, skilled civil engineers are the need of the hour to meet the infrastructure challenges of the society. From bridges to high-rise condominiums, from the high-end irrigation system to the sewage treatment plant, civil engineers are shapers of modern society.
As a career choice, civil engineering provides immense opportunities to wanna-be engineers with a good salary and international exposure. However, to be a successful engineer you must possess some indispensable skills which are as follows:
Dexter in Math and physics
A major part of civil engineering jobs involves understanding, calculating, and designing infrastructure specifications. He has to identify and solve all the construction issues for which he must be adept in formulas of math and physics.
Technical Acumen
To become a civil engineer, you must have a complete understanding of the design techniques, construction development models, and charts. Civil engineers who have hands-on experience in Auto CAD, quantity surveying, project billing, estimation, and bar bending schedule required for planning and designing infrastructures get a priority in recruitment.
Project Management Skills
A civil engineer, most of the time given end-to-end responsibility for the whole construction project. He has to work with architects, interior designers, material suppliers, contractors, junior engineers, and other construction workers to ensure the timely completion of the project. He will have to coordinate with different teams associated with the construction, hence he must have impeccable project management skills for successful completion of the project.
Adaptableness
Every real estate organization has multiple projects going on at the same time as a civil engineer you might have to handle multiple projects at the same time. You will have to handle diverse teams with different, ethnicity and different values. Adjusting to different geographic and cultural conditions is also a challenge for prospective civil engineers. Adaptableness to any terse situation is hence an essential condition for all would-be engineers.
Excellent Communication, Documentation and Reporting Skills
A civil engineer might have to work on a variety of projects both private and the public interest which needs them to communicate with a wide variety of people from a layman to a political figure. He must also have to consult with architects and experts and have a discussion with urban planners. Additionally, he must be able to compose reports concisely and comprehensively that can be understood even by people who do not have a technical understanding. Hence, an indispensable skill for a flourishing career in civil engineering is impeccable communication skills.
An analytical and rational mind
The projects in which civil engineers are involved, they have to contribute in every stage from planning to procuring to design and execution. For completing all these procedures, he will come across many roadblocks. Hem must hence have a critical and analytical mind that will help him to anticipate problems and solve them at an initial stage. Prospective civil engineers must be rational enough to provide innovative, cost-effective, and secured solutions for problems.

From designing new construction to maintenance of the existing or old structures, Civil engineers are required in every organization that deals in construction projects or deals with real estate. If you are keen on pursuing a career in the field of civil engineering, there are some “must-have” skills that you must essentially possess, to build an outstanding career.
Below we have discussed some of the most essential qualities a civil engineer must unfailingly have:
Formal technical training
The foundation of any engineering career rests on understanding the principle of science involved in it. Like in mechanical engineering you must have a fair knowledge of machines, similarly, in civil engineering, you must have a strong grasp on design and construction which you can attain only with a formal degree. You can pursue B. Tech in civil engineering if you have dreams of making exemplar structural designs. It is a six-semester formal technical training on civil engineering that is awarded by all the reputed colleges and universities.
An analytical and rational mind
The projects in which civil engineers are involved, they have to contribute in every stage from planning to procuring to design and execution. For completing all these procedures, he will come across many roadblocks. Hem must hence have a critical and analytical mind that will help him to anticipate problems and solve them at an initial stage. Prospective civil engineers must be rational enough to provide innovative, cost-effective, and secured solutions for problems.
Flexible speaking and writing capabilities
Civil engineers have to work and coordinate with a diverse category of people. Right from communicating with the management for approval, to getting work done with the workmen, to dealing with raw materials suppliers, a lot of responsibility rests with civil engineers. The mode of communicating with a construction worker is completely different from that of speaking with the management. Hence a to be a successful civil engineer, you must develop versatile communication skills.
Acumen in Physics and Mathematics
A civil engineer is responsible for various calculations on the construction site. The design involves using a lot of calculations and theories which as an engineer he is responsible for. He must be efficient in calculating the ratio and proportions of construction materials used in the building process along with acumen in physics and engineering principles which is essential for successful completion of construction.
A sporting team player
Every profession demands good team playing skills and civil engineering is no exception. A civil engineer has to work in liaison with different departments, so he /she must have the natural team spirit of working together with all. A project is easily and successfully done if all the teams act in cohesion especially when the work is something very challenging and comprehensive like construction.
Adaptableness
Every real estate organization has multiple projects going on at the same time as a civil engineer you might have to handle multiple projects at the same time. You will have to handle diverse teams with different, ethnicity and different values. Adjusting to different geographic and cultural conditions is also a challenge for prospective civil engineers. Adaptableness to any terse situation is hence an essential condition for all would-be engineers.

“You are not a job-ready professional until you complete your program.” Now, bid adieu to this myth forever. While JAIN (Deemed-to-be University), in association with Futurense Technologies, is here to offer you multiple guaranteed paid internships along with assured placements during your B.Tech provided you meet the eligibility criteria.
The sky-rising demand of Data Engineering and Artificial Intelligence solutions in the industry have opened the eyes of aspiring engineers. Since 2019, these two technologies have been the frontrunners of the ongoing technological revolution. To give students the right exposure and bridge the talent gap in the industry, JAIN (Deemed-to-be University), in association with Futurense Technologies, has remodelled their B.Tech CSE degree with specialization in Artificial Intelligence & Data Engineering, where the students will get:
Experienced Learning = Learn^3 x Earn^2
This formula encompasses the following—
Remodeling Of B.Tech CSE by JAIN (Deemed-to-be University) And Futurense Technologies
JAIN (Deemed-to-be University) and Futurense Technologies have spinned the wheel and remodelled the program with 16 terms across 4 years. You will be taught conventional subjects in unconventional ways. You will get the facility of ClassLabs (Classrooms integrated with labs). The students will be trained in a way where they will get the competency of data engineers by the end of their 2nd year, machine learning engineers by the 3rd year, and an industry-ready AI engineer by the time you graduate.
Experience Speaks the Final Words
Well, you know “Who pays the piper, calls the tune.” Nowadays every company is looking for candidates who will be ready to work for them without wasting time on the training period. “Need of experience to get a job and vice versa” is a never-ending paradox. To get out of this, JAIN (Deemed-to-be University) and Futurense Technologies have designed their AI & DE program where you get multiple guaranteed paid internships at Futurense Technologies from the 2nd year of the program along with guaranteed placements given that you meet the eligibility criteria for the same.
While your soft skills are being cultivated at the university, the internship strengthens your hard skills. So, you don’t get a “fresher” tag with your name when you graduate. You complete your B.Tech degree with 12+ months of relevant work experience.
Global Exposure
University has tied up with global top cloud providers like AWS and Microsoft Azure to provide you with an opportunity to work on their proprietary cloud platforms. Besides designing their program in an out-of-the-box way, in this program you will be mentored by global faculty. You will be taught by global professors of practice and will also get to interact with CxOs and industry thought leaders on a regular basis. The perfect icing on the cake is added with an opportunity to study abroad at the University of California Riverside along with the complete assistance provided for GMAT/GRE test preparation. (Conditions apply)
If you want to become an expert in these emerging technologies, enroll now for the newly launched B.Tech CSE program with a specialization in Artificial Intelligence & Data Engineering by JAIN (Deemed-to-be University) and Futurense Technologies.
To know more about the program, visit »

Organisations have been utilising sensors for a long time, but the Internet of Things (IoT) has pushed sensor technology to a whole new level. Nevertheless, this new connectivity revolution has already begun, with more than 50 billion linked gadgets. When used with a range of sensors, IoT systems work and offer several types of information and data. A network of connected devices can use IoT sensors and devices to gather, push, and share data. As a result of all the acquired data, gadgets can function independently, making the entire ecosystem grow 'smarter' every day.
Here is a catch!
Because of IoT, physical sensors can immediately communicate their data onto virtual dashboards without human intervention. IoT sensors come in various shapes and sizes, and there are countless applications of sensors in everyday life.
Let us first understand what an IoT sensor is.
What is an IoT Sensor?
The market remained in saturation with measuring devices, such as thermometers, magnetometers (for example, compass), altimeters, and many others until the Internet of Things existed.
One real-world variable is what these sensors are designed to detect, measure, and report to the users in layman's terms. Ultimately, they are designed to help us understand the world around us in a quantifiable, universal way that anybody can grasp.
According to the theory behind this technology, using IoT modules, next-generation IoT sensors may combine and transfer their data straight to an IoT dashboard, making it faster and easier to make crucial choices.
Role of IoT Sensors
Sensors play a crucial part in the development of IoT systems. When external information is detected, sensors convert it into a signal that people and machines can recognise.
It is now feasible to collect data in almost any circumstance, thanks to IoT sensors and devices. The world uses them in a wide range of areas, including medical care, nursing care, industrial applications, and logistics and transportation.
The market for sensors continues to develop with the rise of sectors in which sensors play a significant role.
Applications of IoT Sensors in Real-World
Many leading firms are turning to the Internet of Things to acquire a competitive edge. Besides, increasing operational efficiency through real-time data management and automation of operations is a top priority for companies worldwide.
Organisations can also create and deploy more comprehensive risk-management strategies with new IoT applications.
Moreover, the technology is helping companies upgrade their operational performance. As a result of IoT, enhanced features such as task automation and remote control are possible. Hence, companies can achieve a better balance between energy use and conservation.
Furthermore, we can say that companies will be able to minimise their carbon footprint impact by becoming more energy efficient.
Common Types of Sensors in IoT
Here's a list of some of the most commons types of sensors in IoT:
1. Temperature Sensors
2. Humidity Sensors
3. Pressure Sensors
4. Proximity Sensors
5. Level Sensors
6. Accelerometers
7. Gas Sensors
8. Gyroscope
9. Optical Sensors
10. Infrared Sensors
11. Water Quality Sensors
12. Air Quality Sensors
13. Chemical Sensors
14. Smoke Sensors
15. Motion Detection Sensors
16. Image Sensors
17. Light Sensors
18. Sound Sensors
19. Magnetic Sensors
20. Metering Sensors
IoT Sensors Functionality
Generally, sensors are functionally simple devices that transform physical variables into electrical impulses. In addition to this essential capability, sensors must also have the following characteristics to serve as IoT components:
Conclusion
The world will widely use IoT sensors and devices in multiple sectors to meet social requirements in the future. Sensors will always play an essential role in our daily lives and work settings.
The Internet of Things (IoT) opens up a world of possibilities for companies. Moreover, many sectors have already been influenced by IoT technology, steadily altering the corporate environment. Additionally, IoT sensors will significantly contribute to work-style changes because of their exceptional ability to monitor without human involvement.
Cloud Technology refers to the distribution of various services through the internet using the cloud computing model. Tools and applications such as data storage, servers, database, networking and software, are examples of these resources.
Information Technology (IT) is delivered through the internet or a specialised network in the cloud, with on-demand distribution and payment, depending on consumption. Applications, development platforms, servers and virtual desktops are all cloud-based services.
Various application and infrastructure demands, such as Customer Relationship Management- CRM, database, computing and data storage, are met by cloud-based services in both the private and public sectors. Compared to a typical IT system, where software and hardware are financed upfront by departments and installed for months, cloud-based services offer IT resources in minutes to hours and align prices with actual usage.
As a result, firms become more flexible and can better control their expenditures. Customers use cloud-based services for similar purposes, such as simplifying application usage, archiving, sharing, protecting material and allowing access from any web-connected device.
In addition to cost savings and greater productivity, cloud computing is popular among individuals and organisations for various reasons, including performance enhancement, speed and efficiency, and safety.
Cloud computing services include various possibilities, from storage and networking to artificial intelligence and typical office programs. Services that do not require one to be physically present at computer hardware can now be offered via cloud computing services.
Cloud Computing Example
As a result of cloud computing, a wide range of services are available. Services like Gmail and cloud backups of smartphone pictures are examples, as are services that allow significant companies to host all their data and operate all their apps in the cloud. Moreover, several movie/video apps use cloud computing to manage their streaming service and other business processes.
What is Cloud Storage?
Cloud storage refers to a service paradigm where data is sent and stored on remote storage systems. It is managed and backed up before being made available to users through a network, generally the internet. Most often, users pay a monthly fee for their cloud data storage based on consumption.
Besides, cloud storage relies on a virtualised infrastructure with readily available interfaces, near-instant elasticity and scalability, multi-tenancy and metering of resource usage. A third-party cloud provider manages a data centre where cloud-based data is kept in logical pools across different commodity storage systems.
Types of Cloud Storage
There are three types of cloud data storage: Public Cloud, Private Cloud and Hybrid Cloud.
1. Public Cloud : Public cloud is a subscription-based storage service that provides a multi-tenant storage environment best suited for unstructured data. Data is kept in a data centre and dispersed over many countries or continents as a service provider in the public cloud.
2. Private Cloud: A private cloud service is an internal storage resource protected behind a firewall. Users, who want customisation, more control over their data, and have a great requirement for regulatory or data security benefit from private clouds.
3. Hybrid Cloud: Hybrid cloud is a blend of private and public cloud storage services from third parties, with a layer of orchestration management to connect the platforms.
Types of Cloud Services
1. Infrastructure as a Service (IaaS): It is an entry-level cloud computing service where IT infrastructure can be rented from a cloud service provider on a pay-per-use basis, including servers and virtual machines (VMs), storage, networks, and operating systems.
2. Platform as a Service (PaaS): Platform as a Service provides a development, test, delivery and management environment for software applications. Web and mobile app developers may create apps faster using PaaS since they do not have to set up or manage the servers, storage, network and databases required for the development.
3. Serverless Computing: Serverless computing, which overlaps with PaaS, focuses on creating app functionality without constantly managing servers and infrastructure necessary to do so. Setup, capacity planning, and server administration are all taken care of by the cloud service provider. Besides, event-driven and scalable serverless systems use resources just when a specified function or trigger happens.
4. Software as a Service (SaaS): Software as a Service allows users to access software programs using the internet on-demand basis and generally through subscription. In most cases, users use a web browser on their phone, tablet, or PC to access the program. A cloud service provider hosts and maintains the software application and infrastructure. It provides any necessary maintenance such as software upgrades and security patches for SaaS applications.
The Future of Cloud Computing
Although cloud computing has been around for a long time, it is still at an early adoption stage. Many organisations are on the verge of deciding which apps to migrate and when to do so. However, as companies are getting more comfortable with the concept of having their data stored in someplace other than a server in the basement, usage of cloud computing is rapidly increasing.
Some firms state that moving data, applications, software etc., to the cloud may help organisations rethink business processes and speed up transformation by breaking down data and organisational silos.

Mechatronics combines the multi-faceted aspects from the field of computer, electric, and mechanical engineering aimed at building smarter and simpler systems.
Though originally conceived as an acronym for the words "Mechanical Engineering" and "Electronics" dating back to the 1960s, Mechatronics has been developing and growing ever since. Modern-day mechatronics carries a lot of real-world impacts and can also integrate elements such as artificial intelligence, network security, telecommunications, optical engineering, systems, and control.
What is Mechatronics used for?
Mechatronics can be integrated into various industries and be applied to support applications. Although it is more common in the production of manufacturing including consumer goods, industrial products, automobiles, electronic products, etc., mechatronics has become an integral part of healthcare, transportation, and many other domains.
Listed are some common mechatronics applications:
Mechatronics is applied in many different industries and applications. The discipline lends itself to vast applicability in diverse career paths.
Mechatronics and the Fourth Industrial Revolution
The fourth industrial revolution—also called industry 4.0 and Mechatronics is a key component of Industry 4.0.
It is a term widely used to describe the digital transformation of all industries. It is usually characterized by the combination of physical and mechanical systems with digital and even biological worlds. Cloud computing, artificial intelligence (AI), blockchain, robotics, advanced wireless technology, and the Internet of Things (IoT) are all signs of this revolution, and we are still in it today. The fourth industrial revolution employs something called cyber-physical systems. This system involves multiple sensors and connected devices that converse or communicate, exchange data, and make sound decisions with other devices.
Although Industry 4.0 can transform many industries, occupations, those who understand the field of Mechatronics may be better able to withstand this disruption and excel. With this growth comes many possibilities. There is a range of opportunities to explore in private and public sector units. You can work in the automation sector, equipment building and maintenance factories, and so on. Depending upon the industry that one joins, the responsibilities or the job role will differ. As a mechatronics engineer, get the chance to leverage your expertise and be a part of a workforce that develops smart technologies.
While in the past, it was a common practice to move into the mechatronics field without a degree, these days employers prefer candidates who have specialized education in this domain. With the evolution in technology and innovations that come up each day, it is vital to stay ahead of the competition. A degree in Mechatronics will equip you with the required skill-sets, relevant knowledge, and trends.

It is often seen that students end up choosing engineering due to a lack of awareness about other career options and streams. Another scenario involves students who do not know the right attributes required to be an engineer end up getting confused and choosing the wrong career option.
Students who wish to pursue engineering as a stream often choose Bachelor of Technology (B. Tech) with specialization in a particular field. B. Tech is a four-year degree program with minimum eligibility of 10+2 or an equivalent qualification. Many students appear for entrance exams like JEE Advanced, JEE Main, JET, etc. for various engineering courses and colleges in India. With so many options available, students often find it difficult to choose one relevant specialization to suit their requirements.
The field of engineering is an ever-developing field that includes understanding and studying the theories of science and technology along with their practical applications. The knowledge that students attain is not just limited to the classrooms. The main objective is to drive future engineers towards innovation, research, and development for a bright, better, and functional society.
Popular engineering specializations include:
The framework of a B. Tech program is designed keeping in mind the specialized fields of engineering, wherein students pursue both theoretical as well as practical knowledge. The course includes classroom lectures, practical classes, industry visits, and an internship program. In most engineering colleges, students have a common set of subjects like physics, chemistry, manufacturing science and technology, applied mathematics, engineering design, etc. In the second year of Bachelor of Technology, students are exposed to specialized courses associated with their respective streams. Engineering students need to have adequate experience in fieldwork and internships, as these experiences make them industry-ready and efficient.
Below are some of the questions which students need to answer honestly to decide whether they are suited for engineering or not.
If your answer to most of the above questions was a yes, then it is safe to assume that you are suited for engineering. A carefully planned decision must be taken after considering individual interests, strengths, and opportunities.

Computer science is the study of what computers can do and applications of computations i.e., both theoretical and practical.
Computer Engineering is a combination of electrical engineering and computer science and is about the study of computer hardware and software.
Computer Science and Engineering is a broad domain of computer science and computer engineering
At the Postgraduate level, the graduates are expected to be industry-ready and solve real-world problems through innovation and research. At the entry level, applied computing engineers will have the experience and skills required for leadership positions in the industry and ready to solve day-to-day organizational problems using technology. The curriculum should blend the practical and business skills required for graduates to be multidisciplinary and ready for future technology demands of the industry. If we want the learners to equipped with skills to learn, then the learner's focus should be shifted from listening and behaving to
Engagement in learning is a significant achievement in jobs and outcomes. Students should be kept engaged to develop lifelong learning skills, to guide them to explore and achieve their career goals. The curriculum should focus on meaning and has relevance to each learner and allow them to contribute to the local and global community around them. what will be more important is faculties to research their content, delivery, and assessment and continuously improve teaching practice to meet the needs of changing learners.
Applied Computing
It is a broad domain of computer science where the learner is allowed to explore all possible topics in achieving his carrier goals. Applied computing prepares the learners to be innovative, competent, and industry-ready by the ability to think critically about how to best use their technical skills in solving problems and create a positive impact within the organization. Applied computing is a combination of applied and theoretical computer science and learners focus on developing analytical thinking and applied skills by blending theoretical and practical aspects to solve day-to-day business problems by applying technology. by applying the computing and business skills.
Theoretical Computer Science
Theoretical Computer Science focuses on problem-solving everyday computation using Mathematical Logic, Programming Language Theory, Machine Learning, data structures and algorithms, Automata Theory, Graph Theory, Number Theory, Computability theory, cryptography, Quantum Computation, Parallel and Distributed Computation, Information and Coding Theory, Formal Methods.
Applied Computer Science
Applied computer science focuses on the Internet of Things, Artificial Intelligence, Cloud Computing, Blockchain, Big data and data mining, Software Engineering, Computer Vision, Natural Language Processing, Computer Networks, Parallel and Distributed Systems, Database Administrator.
Business Skills
Business skills are essential skills required to connect, communicate, cooperate and succeed. Business skills along with technical skills are required for success. It is possible by embedding courses that are goal-directed, building leadership qualities, building organizational strategy, decision making, communication skills, project management, interpersonal skills, Analytical and Problem Solving as multiple core disciplines and electives offered. Business skills will help the organization to achieve its goals.
Innovative Learning Environments
Cooperative Learning:here students work together and are responsible for one another’s learning as well as their own. Emphasizing thinking and increasing higher-order learning. It has a range of educational benefits, including an alternative to ability grouping and as a way to prepare students for an increasingly collaborative workforce.
Service Learning: education engages students in community services that are integrated with the learning objectives of core academic curricula. This experiential approach is premised on providing students with contextualized learning experiences based on authentic, real-world situations in their communities.
Learning with technology: learner-centered approaches to technology-enabled learning can empower learners and leverage good learning experiences that would not otherwise have been possible. Technology also often offers valuable tools for other building blocks in effective learning environments, including personalization, cooperative learning, managing formative assessments, and many inquiry-based methods.
Formative assessment: formative evaluation guides learners to better outcomes by providing feedback that continually informs the learner, the teacher, and the learning itself.it is targeted towards three key questions
Inquiry-based learning: students need opportunities to develop higher-order cognitive skills. One important context does this is through inquiry-based approaches in complex, meaningful projects that require sustained engagement, collaboration, research, management of resources, and development of an ambitious performance or product. Relevant approaches include
Future Perspectives for Employability
Todays, goal-oriented applied computing majors become leaders and key assets in the workplace. Applied computing graduates will take up leadership roles in the organization as they are specialized in technologies required in the market and future demands. With changing technology and skills required by industry, students should continuously learn and prepare for future challenges.

The campus placements offered by an educational institution have now become a modern parameter to evaluate its success and reputation. In addition to maintaining goodwill, campus placements also help an educational institution display an image that its students are its utmost priority. It enables students and their families to establish their trust in a particular college or university.
In the last few years, over 200 prospective recruiters have hired more than 4,000 students from our various campuses, which has been an outcome of a very precise placement process adopted by the Student Career Advisory and Placement Support at JAIN (Deemed-to-be University). The dedicated placement team has always kept itself ahead of its peers by constantly evolving the hiring process, thereby creating a niche for itself. The 7-step placement process designed by us helps students land opportunities that they have always sought, for it is unique, well-planned, and designed to provide assurance and confidence to students.
The 7-step placement program includes:
Orientation: This step includes sharing information about the placement process, guidelines, major recruiters, and previous years' statistics with the students. The orientation session is conducted by the Director – Placements or the Chief Placement Officer accompanied by the Dean, Director, and faculties.
Data Capture: Data capture across various parameters is carried out for all the students and this plays a crucial role in the recruitment process. A consolidated Data Capture Format is used by the Student Career Advisory and Placement Support Team for classifying students as per the requirements of various companies.
Student Mapping: This step involves interacting with the students and then mapping them to the job opportunities. Based on the mapping, the Career Advisory and Placement Services Team analyzes the interests of the students and invites the recruiters accordingly.
Placement Training: Every student who has applied for campus placements will have to undergo the Campus Recruitment Leadership Training Program in association with the Institute of Skills (IOS). It includes in-house training (aptitude, group discussions, mock interviews, etc.), guest lectures, workshops, and alumni interaction.
Recruitment Process: The recruitment process is subject to change based on the request from the recruiters. If the applications for a particular job requirement are less in number, the company can conduct the process at their campus or a different venue, based on their convenience.
Final Selection: Once the companies are over with the recruitment process, the recruiters have to provide the names of selected students. After confirmation from the recruiters, successful students are informed about their selection.
In addition to the above-mentioned placement process, the Student Career Advisory and Placement Support Team invites thought-leaders, entrepreneurs, executives, and policymakers for interaction with the students. It involves guest lecture series, conferences, seminars, workshops, industry visits, industry-recognized certifications, summer internships, and a Memorandum of Understandings (MOU) with the industry. To be successful, we forge on both host recruiters and students.
The requirements of recruiters:
The approach of students:
The Student Career Advisory and Placement Support Team at JAIN (Deemed-to-be University) works in tandem with recruiters to provide both the students and recruiters a hassle-free and smooth process that serves their requirements.

As winter comes, Karnataka gets enveloped by the avarekai fever - the omnipresent ingredient that makes its path into our breakfast, lunch, and dinner. The local nomenclature for Hyacinth Beans, Avarekai, or AvareKalu, would fairly depict as the aroma of Bengaluru. During November and February, it is not at all surprising to see our moms and grandmas holding a small handful of beans up to their noses, sensing through the olfactory for purchasing average. It is highly sought after based on size, aroma, and flavor and is usually harvested in December after the 15th or 20th day. Sodagu, the signature aroma of the hyacinth beans is profoundly entwined with the bliss of eating avarekai. Sogadu Avarekai is that one expression that a true Bangalorean will relate to.
The hyacinth bean is full of nutrients that enhance health and prevent disease.
Hyacinth beans (dry) are one of the finest sources of several B-complex vitamins like thiamin, pyridoxine, riboflavin, pantothenic acid, folates, and niacin. Most of these work as co-factors for the enzymes in carbohydrate, protein, and fat metabolism in the body. Hyacinth bean is very low in saturated fat, cholesterol, and sodium. These beans are gluten-free and a very good source of protein, dietary fiber, phosphorus, potassium, zinc, and copper.
Traditionally, it was used to treat diverse illnesses such as heart ailments to nose bleeds. It is the staple eating regimen of nursing mothers in Africa due to its high nutritional and functional aspects: minerals, nutrients, lipid content, and antifungal, antimicrobial, anti-inflammatory properties. This magical bean is great for gut, heart, and brain health, and cancer prevention as well.
Today Avarekai is making its way into modern restaurants, and chefs are wholeheartedly embracing the ingredient in a variety of dishes such as it is widely available in the winter months, and served with fresh salad or soups. It has a beautiful yellowish-green colour, easy to prepare and gives a subtle nutty flavour and texture. Avarekai is high in fibre and protein, which makes it very popular among the health conscious urban population and it makes addition to the menu.
Besides this salad, modern resturants use Avarekai to make falafel, as a puree with buckwheat batter crepes and in flatbreads as well as a side or accompaniment that cohesively mixes with proteins like prawn and lamb in bespoke and tasting menus. Many chefs of popular urban joints want to explore the varirty of items that can be prepared using Avarekai such as the Avarekai Biriyani that can be prepared by cooking the rice using the water in which the avarekai is boiled, which lends a subtle flavour to the dish. The halwa was also made for the element of surprise; most people do not expect avarekai to be the base of a sweet dish, and when the paste is mixed with jaggery, it takes the dish to a different level.
It is fascinating to see how Avarekai has its own tales to tell from the traditional household of southern Indian kitchen to modern eateries, whether it is breakfast, lunch and the afternoon tea snack, the aromatic avarekai will dominate the delicacies of upma, rasam, sambar, akki roti, ragi roti and bisibele bath, pongal and many more.

Covid-19 has now become a part of our daily lives and it is quite evident that we have to live with it, at least for a while. By now everyone has already realized that our chances of catching the Coronavirus are very high, whether it is symptomatic or asymptomatic. Many might already be the carriers of the coronavirus without even knowing or showing any symptoms. Our first line of safety action to refrain from contracting Covid-19 is by preventive measures such as washing hands, sanitizing, wearing a mask, social distancing, staying home, and maintaining hygiene. However, one must have a healthy immune system to fight the virus as it directly affects the immunity of an individual.
The word “Immunity” has been on trend since the initial time when we were hit by the pandemic Covid-19. Never in history was immunity discussed to such an extent which is a defensive mechanism in the body built naturally as well as acquired over time with exposure to diseases or infections. The immune system performs at its best when the body functions in optimal condition. For this, balanced nutrition is very essential as a healthy immune system needs good and regular nourishment. Hence, there is a clear connection between immunity and nutrition.
Loads of content are available on the web, recommending the best way to boost your immunity. Valuable recommendations are like - vitamin supplements, immunity-boosting foods, and drinks, physical fitness, enough sleep, reduce stress, enough sunlight, etc.
We must understand that building a strong immune system is a process and not possible to acquire overnight. Our body needs both macronutrients – carbohydrates, protein, healthy fats as well as micronutrients – vitamins A, B, C, D, E and minerals - Zinc, Iron, Magnesium, and Potassium, etc. These are the basic building blocks of our bodies. Therefore, nutrient deficiency or malnourishment have a direct impact on our body functioning and make us more vulnerable to infectious diseases. In the current lifestyle, many are facing this micronutrient malnourishment without even knowing about it.
Adequate nutrition and hydration are the most important factors because people who follow a well-balanced diet tend to be healthier with stronger and better immune systems which reduce the health risks through infections like Covid-19 to a great extent. So, the body needs to intake a variety of new and natural foods consistently to get an adequate amount of nutrients, minerals, dietary fiber, protein, and antioxidants. Popular immunity boosters like zinc, vitamin C, vitamin A, iron, vitamin E present in various foods, supplements, drinks/teas are recommended in this regard however these boosters alone will not be enough to battle against infections like Covid-19. Therefore, all we need is balanced adequate nutrition and stable metabolism along with and mental wellbeing that is fundamental for good health.

Over the past several years the number of connected devices (mobile, laptops, and IT systems) are increasing at a very high spike, and it is also estimated that the number of such numerous connected systems in coming years will be in billions within a few years. These connected devices generate a huge amount of data in abundance (Big Data). Due to digitalization, most of our critical systems are interconnected and driven by computers and in the future, this connection among various devices will be even more compressed. Automation will take place and most of the decisions will be automated only.
IoT (Internet of Things) will be all over from smartwatches to smart cars that will make our life easy but at the same time our data will also reside in cloud computing, where we don’t fully control the dataflow and access to information. More of our personal lives and business activities are being conducted online than ever. As a result, the complexity and connectivity of these systems would directly impact their level of vulnerability and thereby causing the need for Cybersecurity.
As per the reports of Cybersecurity ventures, it is predicted that the number of internet users will add up to triple in an amount from the year 2015 to 2022 and it will reach the number by 6 billion users approximately and in the future by the year 2030, this number will rise to 7.5 billion Internet users. This rise in Internet usage is directing towards the great need for security on the Internet and ultimately Cybersecurity professionals. As per the Cybersecurity Market Size & Share Report by Grand View Research, the global Cybersecurity market was valued at USD 156.5 billion in 2019 and is predicted to grow at a CAGR of 10 % from 2020 to 2027 as shown in Figure 1. The Government/Defense sector led the Cybersecurity market in 2019 and was accounted for 24.4% of the total revenue.
Figure 1: Increased Market Size of Cybersecurity
According to the reports of NASSCOM, there would be a large requirement for Cybersecurity professionals by 2020 (around 1 million) in India alone. In a recent survey /study, it is found that there is an exponential hike in cybersecurity around 150 percent. The current ratio has shown many big giant companies such as KPMG have almost doubled the size of their Cybersecurity teams, although the jobs for Cybersecurity professionals are fewer in number yet they are increasing at an exponential rate when compared to the other jobs such as IT, network administrator, software developers, etc. As far as our global economy is concerned, it is? directed more towards Internet-based computing and integration the whole world over. Subsequently, many organizations have shown tremendous growth? and now are more vulnerable to hacking and various cyber-attacks.
These organizations have started hiring cybersecurity staff rather than the local police force. It has become a rudimentary job of an organization to protect their confidential data along with the user’s information they are privy to. Many organizations along with the industry such as government, banks, retail, and BFSI sectors are now actively recruiting numerous Cybersecurity professionals and the demand for such professionals will shoot up in the upcoming years. According to a report of PwC and Data Security Council of India (DSCI) the cybersecurity market in India is expected to rise from $1.97 billion in 2019 to $3.05 billion by 2022, a CAGR of 15.6 percent, almost 1.5 times the global rate and shown in Figure 2.
Figure 2: Growth of Cybersecurity Products Market in India
Having a Cybersecurity is degree is worth investment and to support this there are countless reasons apart from mentioned above. B. Tech- Computer Science and Engineering (Cyber Security) will enable you to start up your career while M. Tech Computer Science and Engineering (Cyber Security) will help you to earn more, expand the career opportunities, and have a rich experience in both research and academic. Pursuing your career in Cybersecurity after graduation is considered as one of the best decisions nowadays. This will certainly lead you to not only a very lucrative salary package over time but also help you work in a highly challenging environment evolving continually.
At the School of Computer Science and Engineering, Faculty of Engineering and Technology,
JAIN (Deemed-to-be University), B. Tech - Computer Science and Engineering (Cyber Security) will enable you to be ready for Industry 4.0 emerging and exponential technologies.

India is being charged with being a major hotspot for electric mobility. Electricity is a domestic resource that can turn the transport market through the usage of electricity grid networks. Technology exists to help mobility applications that transfer both people and goods using electricity as a power. When cities and neighborhoods explore smart, affordable transportation options, electric transport is becoming a central component. This latest wave of electric transport would help the country reach an age of sustainable transport. It would minimize emissions and reduce dependency on imported fossil fuels. The economy would flourish, providing a dynamic range of entrepreneurship prospects and rising specialized skills and employment. India is in a unique place to harness electric mobility by leveraging the historic transformation of personal mobility and seeking alignment with strategic imperatives for energy stability, green development and urban decongestion. Electric mobility holds an immense potential for India. However, this shift to e-mobility is a traditional "poor idea" issue where there are multiple players and a great deal of uncertainty in the e-mobility arena.
In the New Budget, Karnataka Emphasizes On Electric Mobility
In a current Government budget statement, “Karnataka Chief Minister BS Yediyurappa” declared a total of Rs 100 million (~ $13.56 million) will be dedicated to the development of a state-owned electric vehicle and energy storage cluster. As a result, “Karnataka” has been the leading nation towards electrical car and energy stowage strategy in the country. The strategy would be established in the 5th step of the “Karnataka Industrial Land Development Board (KIADB)” manufacturing zone in “Harohalli, Ramanagara District”.
Throughout the appearance of the budget for 2020-21 at the “State Assembly”, the Chief Minister announced that, under the FAME India-II (Faster Adoption and Manufacturing of Electric Vehicles in India) scheme, 300 cooled electrical busses were introduced to the “Bengaluru Metropolitan Transport Corporation fleet (BMTC)”.
On parallel lines, the state government is offering a grant of Rs. 1 billion (~ $13.56 million) to introduce 500 ordinary electric busses to the corporation's fleet. Last year, Bangalore Electricity Supply Company (BESCOM) announced a proposal to set up 678 charging stations for electric vehicles throughout Karnataka. BESCOM proposed to set up charging stations for a distance of 50 km on either side of the road along the Bangalore-Tumkur highway every 20-25 km and a distance of 100 km along the Bangalore-Mysore highway. Many of the charging stations will be set up in the grounds of government buildings. Karnataka was one of the first Indian states to launch a clear EV policy. The FAME software was revealed in January 2018. In order to boost last mile connectivity in public transport in Bengaluru, the budget also recommended the introduction of the "Electric Bike Taxi" scheme.

Certain traditional practices have been carried out down the ages, to identify and improve the educational practices. Traditional practice is the total sum of knowledge, creativity, skills, and some practices being practice based on theories, beliefs, and most importantly experiences that are indigenous to different teachings, cultures, and traditions. Education is vital to the pace of the individual, social, and growth of the country and teaching methodologies has changed drastically over the years. The traditional approach in education has successfully been delivered through recitation and memorization of concepts and theories and effective teaching plays a crucial role in helping the children grow from one level to another in a more socialistic way to approach life. In education, effectiveness does not mean being right, perfect, or giving good service to society or family, but bringing the best in students.
Traditional Education System
The traditional or conventional methods are the most common practice in schools and colleges. The old-fashioned way of teaching-learning is all about class period like students would sit silently in class and this practice takes one student after another as it turns to recite the lesson. Generally, the teacher observes each student recitation how they are learning and memorizing the lessons. At the end of the lesson, the teacher will go for the written or oral test to examine the student which is known as an assignment or study recitation test. This is common practice that we have in education, which allows us to know the way traditional methods were taught and it ensures that students were rewarded for their continuous efforts. Such practices were based on well-established customs that had been used successfully over many years in schools and colleges. The teachers communicated the knowledge and tried to enforce the standards of behaviors among the students.
In education, teaching techniques are best formulated by answering the questions i.e. what is the purpose of education and what are the best ways to achieve these purposes. In this context, a traditional education practice is much prehistoric, where teaching methods are largely informal and consist of student’s imitation or modeling the learning behavior that of elders, learning through observation and play. Traditional teaching practice is when a teacher directs students to learn through memorization and recitation techniques which restrict the development of critical thinking, approach to problem-solving, and decision-making skills.
Whereas modern teaching techniques involve more interesting interactions, a student-based form of teaching, and group participation to develop skills.
Technical or modern approach in education
Technical or modern approach in education means, teaching and learning is delivered from a completely different angle. Progressive teaching practices in education delivery and focus on the needs of individual students rather than considering all students are the equal or same level of understanding. In simple words, the modern way of teaching is more realistic, activity-based which uses questioning, explaining, demonstrations, and collaborative techniques.
In modern teaching, the teacher can teach by using different pedagogy. For a teacher it is an art, generally addressing strategies of instructions or style of instructions. Several resources will help teachers to teach in a better way, a lesson plan, or practical skill involving learning, thinking, and applying skills. A teacher sets a curriculum that is often set by the government under precise standards and these standards are not constant they change frequently based on government status. By referring to the Sonia Jackson blog written on modern teaching methods for getting smart, the traditional chalk and talk method of teaching that continued for hundreds of years is now getting inferior results when compared to the modern teaching techniques. This means more advanced modern techniques are now available for students which bring revolutionary teaching methods in schools and colleges today.
Modern education techniques focus on student interaction, encouragement, the boundaries of authority are being broken down, and focus on enjoyment with satisfactory grades.
The modern education techniques allow spaced learning opportunities for the students and when students being encouraged to quickly switch to many activities they learn a lot more things rather than a traditional practice.
The spaced learning is to achieve better grades by providing opportunities for students to present through PowerPoint presentations or other activities in a classroom. It works more effectively than traditional practice in teaching for few hours. This allows brain cells to create connections that students need to remember, memorize, enhance their knowledge and helps students to get relax. Next-generation teaching techniques require a complete rethinking of how students and teachers interact in the classroom. This allows students to develop their higher order of thinking, creating, evaluating, and analyzing skills.
Future with traditional and advanced techniques
As traditional practice use repetition and memorization of information to educate the children which restricts critical thinking, problem-solving ability, and decision-making skills. Meanwhile, the modern teaching approach encourages students to collaborate and interactive ways of learning and therefore be more productive. But one cannot give a statement that modern teaching techniques not effective, both modern and traditional practices are effective and useful in today’s life as it’s all about if balance.
One needs to differentiate between critical thinking when a traditional and modern works best and when it’s right to try new and innovative approaches. A teacher is no longer knowledgeable or experienced on the stage, instead, he can be a skillful coach, who tries to strengthen the connections between the students and skills. He can curate an adoptive and supportive environment in which students' skills are nurtured effectively and support for those skills are dynamic and challenging.

Recycling means converting waste materials into usable materials and items. Recycling focuses on environmental sustainability by infusing the raw materials brought back from the waste products, thus sustaining the economic system. To mitigate the ill effects of climate changes, it becomes the responsibility of every one of us to recycle as much as we can that can very well start from home itself.
You can start with a simple attempt to discover what can be reused at home and giving a new life to old things.
We consider recycling a process of decluttering for shipping unwanted or waste items to a recycling plant to transform them into usable products to reduce environmental pollution. However, something still needs to be done about things that cannot be put in a recycle bin?
Reusing more at home needs a framework that begins with having spots to store your reused materials in the house, regardless of whether this is a case, canister, or pack. Keep the recycling compartment close to the garbage bin to remind everybody to reuse however much as could reasonably be expected.
Following are some of the examples to implement recycling at home.
Let’s start with the most frequently used item-plastic bags. It can be used to line your bins instead of buying new plastic bin liners. It can be used to pack objects for storage or shipment and also can be recycled a few times while buying daily groceries. Aluminum foils can be recycled as temporary containers for cleaning jewels with hot water and a bit of detergent powder. Old CDs can be recycled for homemade arts and crafts or can be used to make a collage of reflective CDs for decorating walls or ceiling.
Books can be gifted, donated, or even swapped at new book purchases. Old cardboard boxes can also be reused to dispatch things or for some creative craftworks. Even minor items like envelopes can be reused for covering up ‘to’ and ‘from’ addresses with the new ones. In rare cases, all the paper items can be used as organic mulch in the garden. The idea of considering recycling is one of the chief steps towards creating a sustainable environment.
Why study Mechatronics?
Mechatronics is a technology combining electronics and mechanical engineering. The word was coined by TetsuraMpro in 1969 to describe the systems which embrace electrical control systems and machines controlled by them. It comprises more than one discipline of scientific studies that collaborates with many branches of engineering. The main application of the mechatronic system is to transform output signals which are obtained by processing the input data gathered from the surroundings and then turning them into useful energy, locomotions, and decisions.
The importance of mechatronics can be understood by the fact that about 25-50% of components in today's vehicles are contributing to control the decisions and driving. Today almost all mechanical systems have become smarter, smaller, and efficient. The outcome is that skilled professionals are required to design, operate, and repair such systems.
AICTE committee for studying the short & medium-term perspectives in India has recommended that the focus on conventional disciplines is decreasing day by day because the great focus is given to the multi-disciplinary engineering courses, especially aerospace, forming, engineering in the environment, and mechatronics. Even the enrolment for an interdisciplinary course is on the rise as depicted by the fact that the admissions for mechatronics and biomedical fields are 65% and 69% respectively has been reported in the year 2017-2018. The mechatronics field in the future can be in more demand and can oppose the traditional fields of engineering in the coming days.
Though robotics and automation picked up familiarity some time back, the most up to date expansion to the family are Mechatronics. Right now, mechatronics is growing very fast and every system of today is made of electromechanical systems with computer science and programming like PLC, HMI, Microcontroller, CNC, Robotics systems. India has a big market in manufacturing and machine tools applications where mostly mechatronics systems are employed, in every sector of industries like Food, Oil gas, Pharma, Manufacturing, and Automotive.
The automation of almost everything, small or large systems has brought an improvement in the demand for the manufacturing of mechatronic products, increasing the need for a technological workforce which makes the subject even more sought after among students. The human intellect and inclination towards all mechanical things are now becoming the future of Mechatronics in India. It is also closely associated with the Internet of Things (IoT), which is driving the learning curve for how Mechatronic systems are being designed, perceived, and manufactured, for a smarter, better tomorrow.
The increase in robotics that can coordinate with humans and also act alone without human assistance with accuracy and smartness is molding the future of Mechatronics in India. It is additionally firmly connected with the Internet of Things (IoT), which is driving the expectation to absorb information for how Mechatronic frameworks are being planned, seen, and designed for a more brilliant, better tomorrow.
Since mechatronics applications are vital in many industries such as automotive, aviation, plant cultivation, etc., the study of this emerging technology can be an advantage in empowerment in the future. These days Mechatronics is in demand, and one can make a brighter future by pursuing this program.

There is a proverb, “Tomorrow never comes”, but in the perspectives of modern computing, more closely with respect to Data Science, it seems little incorrect. It can be said that Tomorrow has come and it is today only and it is creating a new Tomorrow with help of Yesterday.
Modern computing makes an effort to mimic most of the human activities in machines only. In this regard it sees everything as data exclusively. It perceives yesterday and today as data, analyses it, and predicts for Tomorrow.
Earlier data would be processed with the disciplines of Statistics. But due to lack or very less computing power, it was not that much effective. So Data Science came into the existence with high computing power blended with Statistical techniques.
Let’s understand the application of data science with some contemporary projects for which it is being implemented.
Let’s now put some lights on the origin of data science.
Before data science, the term data mining was coined and had got publicized in 1996 form the research paper entitled, “From Data Mining to Knowledge Discovery in databases.”
Later in 2001, William S. Cleveland had put forward the term data mining to a new horizon by blending computer science and data mining. Merely, he had incorporated statistics with computing power and called this composition as “Data Science”.
Nearly this time only the Internet had also emerged with the new version “Web 2.0”, assimilating social media welfares such as MySpace in 2003, Facebook in 2004, YouTube in 2005, Twitter in 2006, WhatsApp in 2009 etc., where people also became huge stakeholders for generating huge data by creating texts, uploading images, audio and videos, like and share, and leaving their footprints in the digital landscape. These undertakings were to sow the seeds of a pile of data from so much to too much and beyond, which was termed as “Big Data” that came across a world of opportunities in discovering insights using the data.
So, the rising of Big Data in 2010, forged ahead the existence of Data Science to throw its weight behind the need of the business to extract insights from their massive unstructured datasets. The Journal of Data Science narrates the data science as, “... almost everything that has something to do with data: collecting, analysing, modelling, yet the most important part of its applications ... all sorts of applications”, like machine learning, deep learning, etc.
In the year 2010, with the new horizons of the data, it became a trend to train a machine learning model with the approach of data orientation rather a knowledge orientation approach. Machine Learning and Artificial Intelligence pushed around the media transcending every other features of data science such as exploratory data Analysis, experimentation, etc., and as a whole termed as Business Intelligence. Some more terms and understandings can be outlined from this adjacent figure.
IT+IT=IT, that is Information Technology + Indian(/International) Talent = India(/International) Tomorrow) is a famous quote in the computer world few years back, but now its redefined as DS+DS=DS that is Data Science + Digital System = Developed Society
Let us now see the application of data science to solve a business problem.
Suppose Ms. Leena works for a multinational company as a data analyst and she has been assigned a business problem. So she would be considering the following steps for solving it.
Following figure can explain these steps in some extent.
Figure Source: Internet (https://www.omnisci.com/learn/data-science
There may be different job titles in the aspect of data science such as:
Future with Data Science
This is the era of the Data Science which needs only data as input to create magic. So many insights it can extract from the data which may be quite astonishing. Experts say the scope of the data science is eternal and there are a lot more to appear in these perspectives. New rules need to be set, new algorithms and more advanced computing languages are aligned along with more advanced computing power.
So there is a big rival among human and computer also, if we don’t update ourselves parallel or ahead of computers, we may lose our jobs and it’s also utterly possible that we may be kept on a tight rein by machines only.

There is always an unanswered question in many young minds on how weather forecasts and cyclones alerts are announced before their occurrence. However, thanks to the technology of remote sensing, which is a concept of satellites monitoring the Earth’s surface at high altitude to collect vital information of the Earth. The expansion of ozone rupture, the increase in the level of co2 in the atmosphere, and the melting rate of glaciers in the Polar Regions due to global warming are estimated with the help of this technology. Within a few minutes of forest fire incidents, scientists forecast an estimate of wildlife and vegetation loss without manually visiting the location.
Recently, the whole world is very cautious about carbon emission levels and is switching to eco-friendly, environment-friendly technologies, and sustainable energy resources. The RS technology enables the switch over to alternative sources and creates awareness for the environment.
The Remote sensing technology is the fuel behind giving all necessary estimates for urban planning and infrastructure development to agriculture monitoring and estimating the yield from the data collected by remote observation of Earth’s surface. RS technology has gone beyond estimating the groundwater level using microwave remote sensing. The skilled scientist in this area owns expertise to transform data into information for the betterment of the society and scientific community.
It is not uncommon to get lost in an unknown place, however, the navigation app in mobile handset would have come to your rescue, thanks to the navigation system which has become an integral part of the communication world, be it a mobile handset, a wearable gadget or a toy, navigation chips makes its presence. With the development of navigation technology, the area of utility has expanded from precision framing to autonomous driving and safety wearable gadgets to intelligent robots.
The aforementioned, Remote sensing and Navigation technology are emerging areas in the field of Electronics and Communication Engineering. Till recently, related studies in this field were handled by Govt. The Research organizations such as ISRO and LRDE, under national education policy, aim to trap the potential of young minds in this area by collaborating academia with research institute to promote exposure to such emerging fields.
Remote sensing and navigation research lab, set up at academia in collaborations with world-renowned research institute will not only encourage the students to research but pursue higher studies in this field.

Soon the way we live will be changed by The technology called IoT! Various parts of the world have started adopting this technology already, and the impact it is creating is tremendous.
Presently, we connect our desktops, laptops, and other mobile gadgets to the internet to perform various tasks. The Internet of Things (IoT) refers to a system of interrelated, internet-connected objects that can collect and transfer data over a wireless network without human intervention, creating endless possibilities for business and personal. One example that we can see take here is before the Internet of Things, patients’ interaction with doctors remained mainly to visits, telephone, and text communications but now, the doctors or hospitals could monitor patients' health continuously and make recommendations accordingly even by being at a different location.
Similarly, an executive can connect to the computer and printer at his office to send printouts for an emergency meeting even when he is traveling. A farmer living in another country can monitor the health of his crops and initiate appropriate actions. He can also physically safeguard his crops from trespassing by installing CCTV cameras in the field. Other industries like manufacturing, building, automation, defense, and space science are also turning towards IoT.
There are various enablers for IoT, but the sensor technology, which has shown tremendous growth in recent years, is one of the main element. High-speed internet connectivity (4G and 5G) and cloud technologies are also prominent contributors to the development of IoT. With the rapid growth of technology, the job potential IoT offers is going to be vast and enormous.
The so-called Smart cities and smart villages are possible only with the support of IoT. The government of India's dream project to create Smart Cities, which launched in 2015, is now becoming possible through the platform of IoT.
No doubt that IoT is going to revolutionize the entire world, but how we learn to adapt to this change is a big question. Engineering students should be aware of this rapid global change and master these technologies to be competitive in the job market. Many universities have already included courses on IoT in the curriculum in all branches of study. This will enable students to understand the importance of this growing technology and sharpen the required skills for brighter career prospects.

We are set out to grow into an engineer, one of the most fruitful and preferred career choices worldwide. The next 4 years are of both educational and financial importance. These are the years that decide what makes us a unique decision-maker and which professional features define us the best. And the very next step is to select the most suitable/best engineering college. Top engineering colleges present a set of criteria. India has become a home to some of the renowned Engineering colleges.
What should we begin our search with?
Appropriate knowledge deployment, approaches of learning, methods of teaching and assessment modules are the four most important constituents of an educational institution. Nonetheless, we must start our search solely after selecting the stream of engineering that suits our academic and career objectives. We can shortlist 2 or 3 additional streams apart from our favourite stream.
Distance and outreach:
How far does it matter to us? It matters the most in miscellaneous scenarios. If the area our college is located in is broadly and comfortably connected to various modes of transport, we are already on the right path. Our first step towards the most crucial decision of our life succeeds. Distance isn’t a hurdle if we are comfortable travelling to and from college.
Setting the colleges categorically:
We must prefer dividing the colleges into three main categories. The first category should include the colleges we prefer the most but are hard getting into. The second category should include the colleges nearing average quality and we can get enrolled into without any serious hurdles. The third category can feature the colleges welcoming us readily and we can count on in the face of uncertainty. Affordability also plays an equally important role in making our academic journey both easy and enjoyable.
Institutional Infrastructure:
Infrastructure has become a common word nowadays. And a good infrastructure means a lot beyond a campus sprawling across lush vegetation and hygienic environment. We should check how sensible the support staff is. We should check the internet speed in college. A library must be voluminous apart from sourcing the best journals and books. We should consider paying a visit to the hostel (If we prefer institutional accommodation).
Academic environment:
An atmosphere conducive to the academics and extracurricular activities is vital to the corrective development of a student. We are here to spend four of the most qualitative years of our life. The academic environment prepares us today to face a future enlightened with professional and personal milestones. Our academic knowledge is our backbone. And the way we integrate our academics with our analytical approaches defines our individuality. We should study the research opportunities our college provides us with. The industries are constantly on the lookout for problem solvers with a modernistic outlook. And if we zero our search on a college fostering every relevant research opportunity, the well begun is half done.
Innovations and unexplored arenas:
Needs shape inventions and inventions are followed by innovations. Dozens of specializations are offbeat and still underexplored. Once upon a time, the list of specializations was confined to civil and mechanical. Contrary to the past, the domains like Aerospace Engineering allow the modern-day intellects to experiment and transform in many fronts. We should consider diversifying our interests and widen them following our preferences. The nation is growing today with a plethora of opportunities. The demand for the offbeat specializations and their pursuers continues to rise. Moreover, the current manpower is too scant to satiate the offbeat demands growing across industries. We too can grow in our endeavours as we explore the underexplored domains.
Scholarships:
Engineering is a program that involves a significant investment in India. We must carefully look into our latest financial aspects as we proceed to get enrolled in our favourite program. Dozens of engineers lose out on the most suitable training prospects due to abysmal funds. The college that thrives on its sensitivity would reward the right candidature that can make a difference to the realm of education. Many institutions offer scholarships or financial aids to the right students in need.
Research facilities:
Engineering colleges are increasing in India. And, so does the number of engineers they export every year to miscellaneous industries. Organizations and MNCs are facing a shortage of time auditing the right candidate whose profile matches their criteria. Most companies, at such junctures, close their recruitment drive on the candidates with an exemplary or a proven track record. We should scan the colleges based on the research facilities or opportunities they offer. An ideal college would prosper every year as it offers both in-house and third-party projects where students can experiment and learn their core competencies. We can further extend our search on the interdisciplinary research opportunities a college offers. These facilities amp up a potential profile. And we are all set for a fruitful beginning.
What exactly is the right institution all about?
Knowledge on the academics, knowledge about the ways to design a curriculum, knowledge about the subject matter and key concepts, resources and technologies available, styles of teaching available are some of the key attributes of an ideal engineering college in India. JGI has been consistently ranked as one of the best institutions nationwide. JGI maintains its connectivity with some of the best companies across the globe. JGI actively contributes to meritorious placements and manpower provision.

The Covid-19 pandemic triggered the entire globe into an economic crisis affecting all industries into loss and stagnant growth, however, one of the sectors worst affected in the crisis of the coronavirus storm is aerospace & manufacturing.
Aerospace & Aviation sectors during the pandemic have seen a serious impact on their sustainability as global air traffic has been brought to a complete standstill from the inception of the Covid-19 outbreak. Meanwhile, the debate is wide open on how the traffic will recover following the current crisis and what this will mean for the civil aircraft manufacturing industry, the supply chain, and the aftermarket support businesses.
Post-Covid, Maintenance repair overhaul, or the MROs have observed serious demand from the airlines especially for the maintenance and the recovery time of the flights will be needed as they were grounded for a period beyond its operational time. Repair and overhauling is a mandate post lockdown to re-energize the use of flights.
With cancellations and depleting older aircraft, demand for new fleet orders incorporated with technology can boost the aerospace & aviation sectors. OEMs of a wider fleet range from smaller sized aircraft to larger carriers can revisit the possible minor design changes in technology, especially in navigation, communication, and control. New orders, can enrich the manufacturing sector with a fresh requirement of components and spare parts. The possible way of recovery would be recycling, rejuvenate as per new fleet requirements. Since aviation has already shown recovery, operating flights based on demand can ensure a steep recovery from the economic crisis. Predicting the second wave of Coronavirus, airlines & allied sectors must be prepared for all possible consequences, and ensure that flight restrictions might not be extended to larger periods.
Vamsi Krishna Chowduru, Asst. Prof. IIAEM – JAIN (Deemed to be University)

Cybersecurity is the defense of hardware, software, and data from unauthorized persons, also known as bad actors. This kind of security is applied by users such as individuals or businesses to protect their servers and computerized systems from malware, phishing, and other cyber threats.
The Threats
The objective to implement cybersecurity is to supply the user with a proper security posture that will help him/her predict, prevent, and respond to cyber-attacks. The aim of bad actors is varied and includes theft of data, identities, money, etc, and theft of IT assets. Bad actors are smart, skilled, and often get paid well to extract and hack important information and data. They are extremely persistent hackers using their stealth controlling systems until their target is reached. This situation is known as an advanced persistent threat (APT).
APT can come from data that is stored by attackers on devices, like mobiles, computers, tablets, servers. This threatening data is installed for malicious use namely extracting critical information about individuals and businesses, stealing money from personal or company accounts, etc. Malware is colloquially spoken of in different terminologies as viruses, spyware, worms, trojan. Blocking these bad actors and their devious threats involves effective cybersecurity.
How to Protect
Cybersecurity is ever-changing. It is always being updated to face the fast-changing threats that evolve together with new technologies. Although we read about cyber-attacks on large companies, we must not think that attackers would not be interested in small businesses or single users. Even these small entities and single users should have cybersecurity firewalls in their devices and servers that will protect their systems from threats and attacks.
Staff and management of a company, whether large or small, should be trained; the staff will need to learn how to use and apply the necessary tools to protect the systems. Since technology is continuously changing and evolving, so will the cybersecurity tool, thus to protect data on the virtual world one must be updated with the latest security tools.
Current Scenarios
A very recent scenario that happened on the 7th of May in England which was published by BBC News, entitled “ Coronavirus: Scam sites selling masks and fake cures taken down” The article highlighted how the National Cyber Security Centre of the UK (NSCS) received over 10k reports that scammers were sending emails worldwide selling face masks, COVID-19 tests, and vaccines. The reports arrived in a day and this triggered a national alarm in the country.
Other emails even cloned the English government websites that were asking for payment information from readers such that these claim their refunds.
The Chief of the NSCS stated that it was also thanks to the help of the public that over 300 websites were shut down. The NSCS set up The Suspicious Email Reporting Service two weeks before the deal with the reports that were starting to arrive.
On April 13th US News published an article relating to how cyber-attacks were on the increase. And states how hackers are taking advantage of the Corona Virus pandemic to attack the Pentagon because most of the employees at the Defense Department are communicating only through online tools.
We all recall the Yahoo! data theft that affected over three billion users. This was a sensational attack on the user’s details that affected an immense number of people and computer systems. It will always be known as this company’s largest security and network breach.
During this cyber- attack, hackers got access to numerous passwords, dates of birth, personal details, account details, identification numbers that were protected, encrypted by a security system that was easy to crack. Also giving them access to government servers and accounts. This incident brings out the vulnerability of our data in the cyber world.
A Future Perspective
It is no news that the internet is an integral part of our lives. We do everything through the internet, from online reading, cooking, dancing to shopping, chatting, meeting friends, new or old. If all this was tangible not just virtual, in a home, we would have the strongest alarm and security system installed in every room. We would do everything in our power to protect our belongings. This is what cybersecurity is. It blocks thieves from entering our virtual but private life.
What is happening in the present should lead us to have a glimpse of the future. We should learn from what we are doing to improve and strengthen the future of cybersecurity. One can anticipate that since the number of online users is always on the increase, the number of cyber investigators will grow too, thus self-alertness such as securing personal data like identification data, account data, passwords, is always necessary, along with stringent laws to curb these cyber crimes.

The fourth industrial revolution, commonly known as Industry 4.0 is not only changing the way we manufacture but also the way we live. New emerging technologies are making us more productive and are bringing about ease of operation. We, humans, are getting relieved from spending hours on many unproductive tasks that are taken care of by the machines equipped with these fast-emerging technologies. The future belongs to these technologies and to be future-ready and competitive, The blog focuses on emerging technologies and how they are impacting and changing the world.
Industry 4.0 The Gradual Evolution
The first industrial revolution took place when water and steam power were used to mechanize the production processes. And the second one was when the industry started using electricity for mass-scale production and assembly lines.
The technological gains made during the third industrial revolution are being taken forward now in the manufacturing processes with the introduction of many emerging and exponential technologies like the Internet of Things (IoT), Internet of Systems (IOS), Robotic Process Automation (RPA), Artificial Intelligence (AI), and Machine Learning (ML), etc. These technologies have revolutionized the way we manufacture products with machines being interconnected, analyzing data, and making decisions without help from humans. This is what is being termed as the fourth industrial revolution or Industry 4.0.
Let us see few important emerging and exponential technologies are making a big difference to industrial processes and systems and are changing the world.
1. Artificial Intelligence (AI) and Machine Learning (ML) - Artificial intelligence and Machine Learning are the terms coined to describe machines that can use their own experience to make corrections, understand new inputs and adjust accordingly, and perform tasks that would normally require human intelligence. AI and ML do not necessarily apply to the manufacturing industry only. These technologies are used to train computers to use a large amount of data to understand a pattern in it and work accordingly. Machine Learning makes computers learn automatically without any human assistance.
Any equipment working on AI and ML has the capacity to store more data than a human mind. Almost all fields of human activity have started using these technologies.
2. Robotic Process Automation (RPA) - There are a lot of business processes that are done manually and are repetitive in nature. Robotic Process Automation makes use of computer software or programs to partially or fully automate these processes.
Robot Process Automation technology can do many tedious tasks that humans may find boring. Another benefit of RPA is that it can complete the work faster than humans because it can retrieve the necessary data from the background more easily and quickly.
Cybersecurity - Every organization wants to protect its systems, networks, and data from any kind of digital attack. This is so because these digital attacks may access, change, or destroy sensitive information. Cybersecurity is the practice of protecting an organization's data and business processes. It consists of technologies and processes which are designed to avert digital attacks.
Cybersecurity is more relevant and essential in today’s digital age as cyber attackers are becoming more active. The number of data breaches is rising continuously. Many organizations have highly sensitive information. For example, armed forces, government departments, medical services, etc. Cyber attackers are always on the lookout for such information and invent new methods to access this information.
In the course of doing their business, organizations are required to transmit a lot of data that may include personal information, financial data, or even strategic plans and their misuse could have a gravely negative impact on the business of the organization. Hence, the importance of cybersecurity has become even more important.
Cognitive Systems - As we all know, cognitive means related to thinking or reasoning, so the term Cognitive System refers to any solution, software, or hardware that can replicate human intelligence such as learning and problem-solving. These systems interact with humans naturally. They are not just programmed. On the contrary, they learn from their interactions with humans and their own experiences.
Today, organizations deal with huge volumes of business information but they don't know how to take full advantage of it. This is where Cognitive Systems come into play. They help organizations to process this data explosion in a structured manner and make effective decisions.
Data Science - Until now, the data available used to be structured and was not so voluminous. It could be easily detected and analyzed by using simple business tools. But nowadays, the data available is not only huge in volume but is also either unstructured or semi-structured. Expert studies show that currently, more than 80% of the available data is unstructured.
This is where Data Science comes in. Data Science is a field that uses a blend of scientific methods, processes, and advanced algorithms to get useful insights into all kinds of data, be it structured or unstructured. It is a high level of technical skill that enables data professionals to build complex algorithms that help in organizing and analyzing a large amount of data and provide solutions that drive the strategy of their organization. Data Science enables companies to uncover many hidden insights like trends, consumer behavior, etc., which helps them in making smarter business decisions.
Be Future Ready
Industry 4.0 is more skill-intensive rather than labor-intensive. These technologies are evolving as the most promising career paths for professionals. So, if you are planning to study Engineering, you should focus on these technologies that employers are looking for in Industry 4.0. Jain (Deemed-to-be University), Faculty of Engineering & Technology is pioneering academic hub of India providing all the new- age programs and technologies of industry 4.0 that fulfil all your quest to be future-read.
Introduction
In 1955 John McCarthy announced Artificial Intelligence for the first time. The term, ‘Artificial Intelligence’ is derived from two words, artificial- a thing which is not natural, and intelligence- a capacity to understand and collect information about events, a particular group, etc.
After combining these two words into a single frame, ‘Artificial Intelligence’ means a computer programming code in a machine like a computer exhibiting traits of human beings like learning, problem-solving, scanning, storing information like memory, thinking, etc. Just like mimicking someone, a system of Artificial Intelligence does the same as human beings perceive things by performing various tasks from their environment.
The system is very quick in recognizing the impulses, and with advanced deep learning, it processes the tasks using natural language processing (NLP) technology. Being a natural branch of artificial intelligence, NLP fulfills the gap of communication between a machine and a human being through many principles and disciplines like computer science, and computational linguistics. NLL helps the machine to understand the human language by turning into their language. The technology saves valuable time and energy by performing its operation in less time than expected.NLP assists artificial intelligence to do multiple tasks like reading a text, following the instructions given in the text, checking records simultaneously, etc. In short, artificial intelligence enables the machine to learn languages to perform tasks. Now,
Difference between Artificial Intelligence and Machine Learning
Artificial Intelligence simulates and trains the machine to mimic human actions like speaking a particular dialect, recognizing colors, shapes, etc. whereas machine learning is a subset of artificial intelligence that are developed to interpret human actions. Machine learning searches for data and tries to reach to a conclusion just like us using certain algorithms. Like a car has a laser-like device on its top, giving signals for the in-between objects while parking in a parking area, and also informing about all the cars that are surrounding it. But both need large volumes of data, granular data, and extremely diversified data.
Current Scenarios
In today’s world, since its inception, Artificial Intelligence has become an integral part of every person’s life due to this, our life has become very fast. AI has led to cut short time and multitasking at once. Artificial Intelligence repetitively learns and discovers through diversified data. Without human involvement, it clarifies high volume of data without fatigue and analyses deep data, hidden into deep layers of neural networks. It is capable of identifying and performing human tasks, deep neural networks achieve incredible accuracy by interacting with humans like a person who uses Google Search, Alexa,. Siri, Macbook, Tablets etc.,
How does it work?
Before learning the working structure of artificial intelligence, we need to research and have deep knowledge about its basic components. Here they are:
Uses:
Artificial intelligence has made our life error-free with superb advanced high-technology. From self-driving and parking vehicles, to digital assistance thanks to Artificial Intelligence in assisting our homes, offices, our objects like mobile phones, washing machines, etc. installing biometric machines in offices, has made it easy to track the attendance of employees. Google assistant, Siri, and Alexa to speech and face recognition have made our gadgets safe and secure. Even applications like Uber, RedBus, Ola use artificial intelligence that allows us to share route details along with the driver and cab information to our dear ones.
Many high-profile industries demand Artificial Intelligence for security, risk recognition, legal assistance, etc. For example, such as health care industry need AI for X-rays and diagnosis treatment of patients. The retail sector uses AI in collecting and possessing multiple customer data online, and offline and also in online shopping and multiple payment options like COD, internet banking, debit, or credit cards. The manufacturing industry also needs AI to analyses IoT (Internet of Things), and for calculating demand and supply of the products in the market. The banking sector uses AI to identify any fraudulent activity, risk measurement, fast and smooth transactions, credit scoring, etc.
What are the future perspectives of Artificial Intelligence?
The future of Artificial Intelligence will be vast and more extensive than the present time. From deep learning, the networking system to driverless cars, it will make the world a digital place. It is influencing everyone’s life making it very simple, optimized, and fulfilling the purpose of life and understanding the mechanics behind Artificial Intelligence. Hence, humans will successfully merge with it completely to do autonomous work.
School of Engineering & Technology Jain (Deemed-to-be- University) is a pioneering school of engineering that offers wide variety of new- age courses. The institute offers both B.Tech and M.Tech programs in Artificial Intelligence that opens a wide gateway for job opportunities for the students even at a global platform. The course gives hands on experience and make the students ready to face the industry demands, with advance knowledge of artificial intelligence.
It allows you to make financial transactions in a secure and reliable way. One of the main advantages of Blockchain is that it allows financial transactions between two participants safely and reliably. There are no more intermediaries involved, but the users themselves have control over their information and the entire transaction. This information is distributed in multiple nodes that are independent of each other. These register and validate it without having to know the other participants.
It is transparent and at the same time private
With this technology transaction are more reliable for two reasons: they are transparent and also private. The movements, although they cannot be modified, are integrated into the network as a whole and are public, i.e. they can be viewed without problems by each of the parties. At the same time, data from transactions between the parties are private. The information flow does not exist since the design is based on a block of chained codes.
The data are impossible to falsify
Another great advantage, which makes it even more reliable, is that once the transaction data has been recorded, it is impossible to falsify it. They are immutable, that is, they cannot be modified or deleted. This is possible because it works with different forms of data verification, so the alteration of transactions by third parties is practically impossible. Besides, the database has a history of each transaction since the technology was created.
It is an immediate process
With banks, you have to wait a while for a transaction to be completed. With Blockchain, since there are no intermediaries, the process is immediate. The computer system used for operations works 24 hours a day, every day. Since the information is transmitted and saved automatically, there is no need to wait.
Information is never lost
Because many nodes are involved in its validation, the information is secure. Even if the network were to go down, the service would never be lost and would continue to function. Why? Only one of the nodes needs to be active. This is achieved thanks to the decentralized networks, which also makes it more resistant to malicious attacks since it does not have a central point of failure.
There are no errors
Banks can make mistakes in transactions, but Blockchain cannot. The data recorded in a Blockchain is always correct because it is constantly checked by a network of people. The information that is recorded is agreed upon by all participants and therefore there are no errors.
The transaction cost is low
One of the big problems for banks and currency exchange platforms like PayPal is the high fees they charge. These are imposed and there is nothing users can do against that if they want to use the service. Blockchain users can free themselves from high commissions since the exchange of assets with this technology usually has a lower cost.
Encourages globalization
With Blockchain, globalization takes another step. With this technology, there will no longer be any borders for transactions. You can avoid the tedious paperwork and even export procedures, regardless of the currency, you will be able to trade goods and services in another country without involving so many intermediaries.
Jain (Deemed-to-be University) offers a B-Tech degree in Distributed Computing and Blockchain. With Industry-standard Infrastructure and staff, get in-depth knowledge of how Blockchain works and lead a bright future! Apply Now!
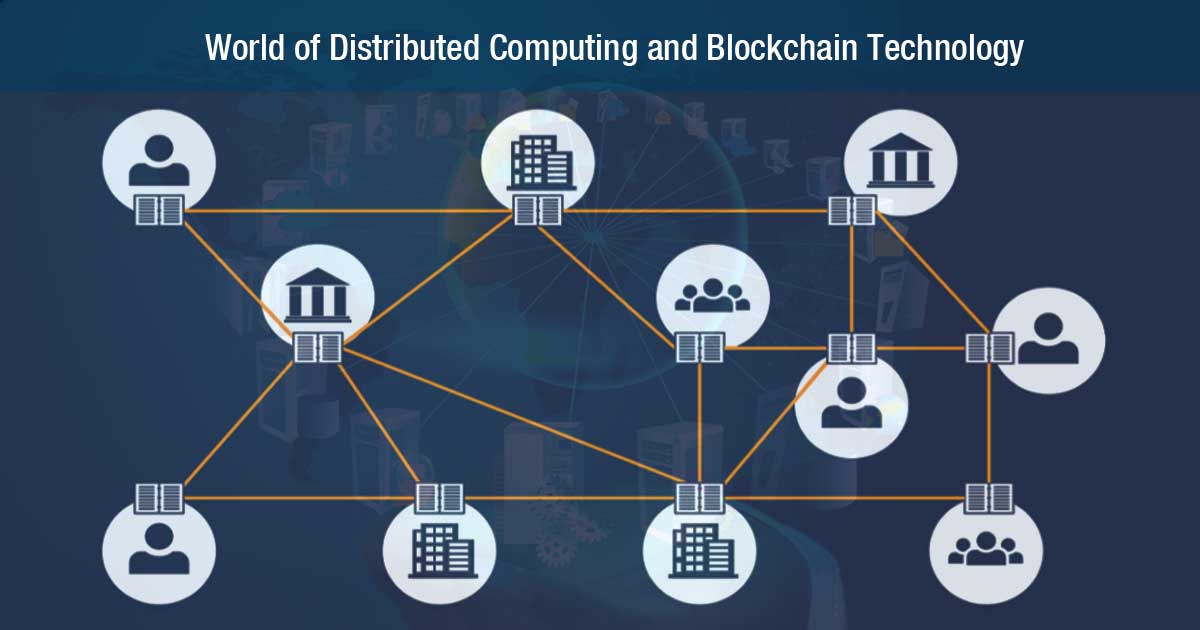
Distributed computing is one of the fundamental computing principles that drive the Blockchain technology. In the simplest terms possible, Distributed Computing is merely a network where different computers come together to form one system. The systems can be physically connected to form a local network or they can be geographically dispersed and connected online. It is an old principle that has been fine-tuned over the years to suit the requirements.
Computers within distributed networks don’t need to be in any specific format or hardware configuration. This could be laptops or mainframes, PCs or Macs.
Blockchain was invented by a person (or group of people) using the name Satoshi Nakamoto in 2008 to serve as the public transaction books. It is a type of payment trail which is curated in digital blocks.
A Blockchain can be termed as a peer-to-peer network and there are no institutions or corporations that are in charge of these Blockchain. They are maintained by a group of highly skilled engineers who are known as the Miners. Blockchain technology has changed the concept of placing our trust from one centralized organization to a distributed trust as this ensures privacy, prevention from frauds and 100% secured transactions.
Course Benefits
Employability
As per LinkedIn's annual Emerging Jobs 2018 report, Blockchain Developer is one of the most coveted jobs among all occupations. Alternatively, you have the option of becoming a technopreneur. You will have an option to incubate your startup even before the end of the course at the JUiNCUBATOR (an event of Jain Deemed-to-be-University).
Some of the employment options are as follows:
In the End…
This course is uniquely curated so that when the students graduate in 2024, they are a step ahead of the emerging technologies and are equipped with the necessary proficiency.
Why Choose Jain (Deemed-to-be University)
B. Tech program in “Computer Science and Engineering (Distributed Computing and Blockchain)” will enable an individual to be ready for Industry 4.0 emerging and exponential technologies. This course is industry-integrated with Wiley Industry 4.0 certifications in Blockchain and will be delivered using project-based learning leading to internships and career opportunities with startups and MNC’s in India and abroad.
As per LinkedIn's annual Emerging Jobs 2018 report, Blockchain Developer is the top emerging job among all occupations. So, with a degree from Jain (Deemed-to-be University) School of Engineering and Technology, a student stands to gain the unique advantage of being positioned to keep pace with the emerging skill-sets and be industry-ready.

The financial sector and the world of crypto-currencies are not the only ones who can benefit from Blockchain technology. Many sectors are seeing the potential that this technology has, which added to others, can be very useful.
In fact, according to a study conducted by IBM's Institute for Business Value in 2017, by that time 33% of companies were already using Blockchain or were planning to use it soon. In addition, 78 percent of respondents said they were exploring its use to develop new business models or in response to changes in their industry.
With regard to the financial sector, the World Economic Forum has stated that “In the coming years, we will witness the Blockchain revolution, as it will eventually become the "heart" of the global financial system”.
Banks are already using this technology to speed up payments, transfers, and remittances, and to lower the costs associated with these processes. Stock markets such as Nasdaq also use it.
But as we have said, Blockchain's applications are not limited to the financial system. These are the areas in which this technology is also being used.
Distributed cloud storage
Blockchain allows distributing data storage. That is, instead of depending on services such as Google Drive or Dropbox, which are centralized cloud storage, files can be saved in a P2P (peer-to-peer) network, which means that they will be saved by several users.
In this way, since the information is not stored in the same space, it is more difficult, if not impossible, for it to be attacked by hackers or to be lost due to technical problems or natural disasters, for example. An identical copy of the data will be stored in each node of the network, which makes the system more secure.
Decentralizing the Internet of Things (IoT)
Most Internet platforms of things are based on centralized models, meaning that a single company controls the connected devices. However, this system is not very functional, since as the popularity of this technology increases, it becomes more necessary for the teams to be able to exchange data with each other quickly and autonomously.
The solution is in the development of decentralized IoT platforms and Blockchain allows it. With the Blockchain the data exchange is done in a safe and reliable way and in addition, an unalterable record is created of all the messages that have been exchanged by the different connected intelligent devices.
Some companies are already opting for this solution, such as IBM, which has created the ADEPT (Autonomous Decentralized Peer to Peer Telemetry) platform in collaboration with Samsung. Using the Blockchain technology, this system is capable of generating a distributed device network.
Identity Management
Another great application of Blockchain is in identity management. With this technology, users can create their own digital identity, which is secure and reliable because it is tamper-proof. Experts assure that this kind of ID based on Blockchain could replace the increasingly vulnerable user names and passwords online in the near future.
People will be able to use their Blockchain identity for many things, from simple actions such as accessing websites and applications to signing digital documents. In fact, there are already companies that have such services such as Keybase, Onename or ShoCard.
Registration and Data Verification
Not only can this technology be used to store financial transactions securely and immutably. It can also be used to store any other type of information, thus generating an incorruptible distributed record, which also stands out for being more secure than traditional databases.
This application can be used in several sectors. In clinics and hospitals, for example, it can be used to create a record with the medical history of patients. It can also be useful for the protection of intellectual property and creative digital products such as e-books, music, photos, etc. It can also be used for the registration of vehicles or property.
Jain (Deemed-to-be University) offers a B-Tech degree in Distributed Computing and Blockchain. With Industry-standard Infrastructure and staff, Get in-depth knowledge of how Blockchain works and lead a bright future! Apply Now!

Vehicles that can be driven on their own, assistants who are capable of translating from one language to another, or personalized purchasing suggestions. Complex tasks that used to be seen as a fantasy, today can be possible due to 'Machine Learning', a quality that allows computers to learn by themselves to perform functions without having to be programmed to do so.
What is Machine Learning?
It is nothing more than an artificial intelligence discipline that provides computers with the ability to see massive patterns through data and thus be able to make their predictions. This is what allows those computers to be able to perform functions autonomously, that is, without being programmed by anyone.
Although this term has been heard since 1959, it has only become relevant in recent years due to the constant increase in the power of computing and data. The techniques used in automatic learning are a fundamental pillar in the process of Big Data.
Three categories divide the Machine Learning algorithms, although the most common are the first two.
Supervised learning: this algorithm has the support of a previous learning that is based on labels and data that allow you to make your decision or make a prediction.
Unsupervised learning: This type of learning is totally lacking in previous experience or knowledge. It takes care of shaping a whole set of data in order to get a pattern to organize the data correctly.
Learning by reinforcement: The algorithm must learn and gain knowledge through their own experiences. This implies that it must take the decisions it considers correct before different situations and all this is achieved through trial and error.
Automatic or autonomous learning
It can produce behaviour through algorithms, and these at the same time are supplied by a large amount of data. The algorithm with all this will know what decision to make. From there the machine will be able to automate the tasks and functions.
Today's technologies are increasingly robotic. Some time ago was launched Autonomous Database, this automates the data using machine learning algorithms.
Deep learning
Also known as Deep Learning, it tries to capture concepts more efficiently by analyzing data in an abstract way. It does this by applying compression of the non-linear. It works in a similar way to the brain. Each neuron can accumulate layers of data in order to learn the concepts.
In order to have an idea about the functioning of DL, let's suppose that the neuron network wants to recognize faces by forming the face through layers that will give one by one the contour of the face until being able to distinguish specific faces.
Some applications of Machine Learning
Social networks: Facebook, Instagram, and Twitter use learning algorithms, Twitter to detect existing spam, and Facebook to detect false or disallowed news in broadcasts and live.

The surface of our mother earth is partially covered with approximately 70% of water, a life giving universal solvent referred as ‘Earth’s Blood in India and its fate’ flowing through gullies and tributaries as arteries and veins in a human body. One of the essential objectives of WHO is “It is necessary to save the water sources from the pollutants which contaminate the water making it unfit for drinking”. Nowadays, there is much concern about the current-use of pesticides (CUPs) which is used in farming/agriculture and these pesticides are percolating into the groundwater sources or through runoff and are moving towards different water sources, causing an alarming threat to the humans.
Since legacy pesticides such as DDT began to be regulated in the 1970s and 80s, there has been a massive increase in the use of replacement chemicals that serve similar purposes (i.e., reducing exposure to insect-borne diseases, protecting crops, and maintaining agricultural yields). In theory, these CUPs can be licensed for use if it does not cause harmful persistence in the environment long after the period of its use and if the chemicals have low bioaccumulation potentials. Thus CUPs should have a less environmental impact than the legacy pesticides they are replacing, but the inordinate utilization of synthetic substances utilized in pesticides and insecticides presents a risk to nature, as well as human beings.
Many parts of the world have fallen prey to pesticides and insecticides that have affected a lot of humans, animals and the environment. In India, it was the insecticide Endosulfan which lead to hazardous outcomes. Thus the Supreme Court of India passed a request on May 13, 2011, to prohibit Endosulfan, after a large number of casualties were reported from Kasargod (Kerela). The creation, conveyance, and utilization of Endosulfan were restricted as any contact with humans may lead to fatal consequences. Endosulfan has been utilized to control creepy crawlies which harm vegetables like the potato scarab, bug, cabbageworm, etc. It has also been utilized in nations all through the world to control bugs on organic products, vegetables, tea and other non-nourishment yields for example, tobacco and cotton.
Endosulfan was a commonly used insecticide until its ill effects came to light in the Kasaragod district of Kerala. As a result, it was banned in Kerala in 2005 after the Centre issued a notification, based on the reports of the National Institute of Occupational Health and other committees. But that ban has been ineffective and describing the effects of Endosulfan as ‘DEVASTATING’ the Supreme Court directed the Kerala government to release compensation for over 5000 victims and newborns.
The insecticide was mainly used to get rid of insects in cashew plantations but its vulnerable exposure brought the insecticide in contact with the humans causing severe health hazards for them. Although there is a complete ban on its use, authorities allow its use for some cases such as to take care of bollworm infestation in cotton fields, in the absence of any alternative till today. In such a scenario, it is important to develop strategies to stop excessive use of Endosulfan and other similar harmful pesticides and insecticides in soil and environment preventing its reach to water bodies and ultimately humans.
Due to its abundant usage and potential transport, Endosulfan contamination is still frequently found in the environment. It has been detected in the atmosphere, soils, sediments, surface and rain waters, and foodstuffs. The revelation of new reports for the first time, from researchers in India, have found that mice and rats exposed to this insecticide are suffering from DNA damage, genomic instability, and impaired DNA damage. This puts the welfare of humans in further danger and calls for an immediate solution and alternative to replace these harmful chemicals.

When we read the word "cyber security" we tend to think of dangerous cyber-attacks capable of destabilizing an entire nation. And we are not saying there isn't some of that. In the depth of the Internet, there is a constant war to protect the classified information of each country as global macro-corporations.
But that's a bit of a big picture for you and us, isn't it?
That's why in today's article we want to focus on cyber security at the user level, which affects us. And to that end, we are going to explain:
This way you can protect all your data and prevent possible threats.
Are you ready? Let's get started.
What Computer Security all About?
The rapid advancement of technology allows everyone to be permanently connected to the Internet. This makes it easier for us to search for information, but it also puts our personal data in a box so that anyone skilled enough can access it.
So the more we depend on the Internet, the more necessary cyber security becomes. Some say that the only possible solution to this scenario is to abandon technology and live in the mountains like a hermit, and well, it's an option. But, since you and we are in the business of researching (and the Internet is one of our key tools), we would better explain to you the most common threats we face. That way, you can get a clear idea of how useful (and necessary) this practice is.
What are the Most Common Threats?
Here's a devastating fact: the threats to cyber security are endless.
This does not mean that nothing can be done to protect our information, but it is necessary to take this into account to put all possible barriers to those who try to violate it. New ways of circumventing computer security defenses are emerging every day, and we need to be vigilant.
But don't panic, we’ll explain later how you can improve your cyber security. For now, let's focus on the most common online threats:
Cybercrime: This threat occurs when criminals with sufficient skills access protected computer systems in order to make a clear profit, such as financial gain or information kidnapping.
Cyberterrorism: this is a more complex concept than the previous ones and also more dangerous. It aims to foster a state of terror and panic among a particular population, threatening their stability and way of life. For example, if one of these attacks succeeded in disabling the computer systems used by a country, the damage would be tremendous (yes, we know it sounds very movie-like, but believe us, it is being attempted every minute).
As you can see, there are different levels of threats and for all of them there must be a contingency strategy. It is clear that the information a company can store is not the same as the information we can store as basic users. Even so, it is in your best interest to protect your data, as there will always be those who want to infringe on the privacy of others or hijack valuable information (such as bank access details or compromised photographs).
Jain (Deemed-to-be University) offers B.Tech course in Cyber Security and Digital Forensics! But you will know how to tackle those threats; you can work for Cyber defense companies, for government protecting the beautiful Internet from these bad guys!

The process of how Blockchain works is not complicated, but it involves more people. It is no longer the bank that must certify transactions, but a group of users.
Everything starts when A wants to make a transaction for B. In the network this transaction is represented as blocks. This is transmitted to all the parts of the network, that is, to the nodes that are connected, so that they approve its validity. Once this is done, the block can be added to the chain, becoming a transparent and indelible record. Finally, the money moves from A to B.
In this process, the nodes confirm that the person who wants to make the transfer has sufficient funds to do so. If this is the case, everyone 'writes down' the transaction and certifies that it can become part of the transaction block. This block will grow to the point where it will no longer support transactions.
The capacity of the block will depend on the structure of the block chain and the size of each transaction. Once it has reached its limit, it will be time to validate it, which is the process that takes place when users are mining. This work consists of performing a series of quite complex calculations that in addition to time require a lot of electricity.
Once this is done, the blocks will be permanently registered in the block chain. This means that they cannot be modified without altering the other blocks that are linked to it, something that is practically impossible because to carry out an operation like this would require most of the nodes to validate it.
The capacity of the block will depend on the structure of the block chain and the size of each transaction. Once it has reached its limit, it will be time to validate it, which is the process that takes place when users are mining. This work consists of performing a series of quite complex calculations that in addition to time require a lot of electricity.
Once this is done, the blocks will be permanently registered in the block chain. This means that they cannot be modified without altering the other blocks that are linked to it, something that is practically impossible because to carry out an operation like this would require most of the nodes to validate it.
Jain (Deemed-to-be University) offers B-tech Degree in Distributed Computing and Blockchain. With Industry standard- Infrastructure and academia, to give students in–depth knowledge of how Blockchain works and lead a bright future! Apply Now!

While technology is one of the major drivers of transformation, it is critical that the human elements are on the same level of learning so as to use the said technology to its fullest potential.
What is Data Engineering?
Even before a model is built and the data is cleaned and made ready for exploration, the role of a data scientist begins. Every data-driven business needs to have a framework for the data science pipeline; otherwise, it leads to failure of the set up. Most people enter this field intending to become data scientist, without ever realizing what a data engineer is, or what that role entails. These data engineers are a significant part of any data science project and their demand in the industry is growing exponentially in the current data-rich environment.
Who is a Data Engineer?
Data engineers bridge the gap between software engineering and data science and transforms data into a useful format for analysis.
Let’s take an example; a data scientist wants to analyze Uber and one of its competitor by checking a user’s action history as compared to the competition and see what actions correlate with users who spend more.
In order to enable them to create this, you’ll need to combine information from the server access logs and the app event logs. It is obvious that both Uber and its competition are generating huge amounts of data from their mobile app (from riders and drivers).
For the data scientist to analyze this information, she/he will need the following:
A data engineer will create a pipeline that will read the mobile app logs and server logs in real-time, parse them, and attaches them to a specific user. The parsed logs will then be stored in a database, so they can easily be queried by the API. The pipeline should be an auto scaling one so that it can accommodate a large number of users.
Tasks of a Data Engineer
How will the students benefit from this?
Course Details
Career Opportunities
The demand for data engineers is massive and growing as we speak. Speaking in general capacity, the common areas of a data engineer happens to be the finance, automotive, health, retail and telecom sectors.
As per a study by Stitch (read here for more), the following are the probable roles of a data engineer in an organization
Become an expert in Data Engineering and Informatics and get added opportunities to study abroad and get a Wiley Industry 4.0 certification, visit us at https://set.jainuniversity.ac.in/

Digital forensics consists of identification, recovery, validation, and presentation of facts regarding digital evidence found in the virtual world such as computers and similar digital storage media devices. The study aims is to preserve any evidence in its most original form and perform investigations that helps to uncover and interpret any electronic data to reconstruct the past events. The findings are often used in courts of law which is why the data has to be thoroughly interpreted without contaminating it even a bit.
We all are aware that Cybersecurity refers to the process of protecting all internet based apps, data, hardware, and software from various types of attacks. The main aim of cybersecurity is to limit risk and protect IT assets from attackers.
Why Cyber Security is of Paramount Importance?
For any enterprise, the protection of their data (both financial and personal) is of utmost importance. Any cyber-attack can end up having a catastrophic impact on the company in terms of finance and reputation. Cyber Security is necessary because it prevents data breaches, identity theft and ransomware attacks, and aids in risk management.
Course Benefits
This comprehensive 3 years Bachelor’s degree enables the student to conduct a digital forensics investigation admissible to a court, and be proficient in the practice of cybersecurity skills in real-world scenarios.
What’s in it for the Students?
Job Options
Become an expert of Cybersecurity and Digital Forensics and get added opportunities to study abroad and get a Wiley Industry 4.0 Certification, visit us at https://set.jainuniversity.ac.in/

Robotic Process Automation (RPA) is emerging as the most vital technology for streamlining business processes in the enterprise. RPA can be considered as the next logical step towards automating the basic functions of an organization. It is a natural progression for an organization’s digital transformation.
As organizations increasingly adopt RPA, which relies on software robots to automate tedious tasks, expertise with RPA tools and implementations will become more important part for business analysts, business intelligence developers, data or solutions architects, and system integrators or administrators, whether it is banking, medical, tourism, defense RPA is emerging as a significant element.
Point to remember – RPA is not an inherent part of the organization’s IT infrastructure. It is added software that enables the existing tech to work more efficiently without altering any parts of the infrastructure. Since machine learning and AI are involved in it, the can adapt to changing circumstances, exceptions and new situations.
Course Details & Benefits
Wiley has partnered with Automation Anywhere to prepare the future workforce for more than 300,000 automation jobs. The Wiley-Automation Anywhere Official RPA Study Guide and Courseware Series will include a competency-based curriculum for specific job roles, study guides and digital courseware including videos, online assessments and lab work.
These official study sources will pool expertise from both Wiley and Automation Anywhere to create a successful learning path for students seeking RPA career opportunities. This collaboration has the potential to build a robust ecosystem with the core competencies required in the future job roles and readies candidates for these in-demand jobs.
How will the students benefit from this?
Job Opportunities
Types of Employers Recruiting Automation Experts
Become an expert in Robotic Process Automation and get added opportunities to study abroad and get a Wiley Industry 4.0 certification.

Considered as a part of the 4th industrial revolution, Industry 4.0 is a trend towards automation and data exchange in manufacturing technologies and processes which include Cyber-Physical Systems (CPS), Internet of Things (IoT), Industrial Internet of Things (IIOT), Cloud Computing, Cognitive Computing, and Artificial Intelligence.
History
Technological Advancement has come a long way, the first Industrial Revolution began around the 18th century, through the use of steam power. By the time third Industrial Revolution, which began around the 20th century there has been drastic transformation to partial automation using memory programmable controls and computers. As the industry 4.0 unfolds remarkable changes have occurred in the field of technology. In the era of Industry 4.0 computers are connected and communicate with one another to make decisions without human involvement. It has built a foundation where machines are able to manage themselves and the production process functions independently without the intervening of manpower.
Germany a nation with an unmatched reputation in manufacturing has played the pioneering role in revolutionizing technology by bringing Industrial Revolution 4.0. The name was first proposed in Hanover Fair in 2011 and was soon followed by a report in 2013, which eventually lead to the adoption of the term by the German Government. The concept of Industry 4.0 emphasizes on bringing intelligence, connectivity, and much broader applications of computerization to manufacturing.
The Aim
The aim of Industry 4.0 is to explore and exploit the huge potential of new technologies like
Data has become the center of most business models. Companies that are born in the digital era have a higher understanding of this point as compared to legacy companies.
For example: Enterprises like Facebook, Netflix, Amazon and Google began by investing largely into these “Futuristic” technologies. They have designed their products in a manner wherein they capture the user data in a far superior way than the traditional companies with hybrid digitization.
Benefits of Adopting the Industry 4.0 Concept
Also, we must keep in mind that when it comes to the decreasing costs of industrial production, Industry 4.0 is looking good. According to some sources, Industry 4.0 factory could lower the costs of the following:
Some useful information regarding industry 4.0
Industry 4.0 and India
India is very much keen on adopting Industry 4.0 and has taken several initiatives one such initiative is Smart Advanced Manufacturing and Rapid Transformation Hub (SAMARTH) - Udyog Bharat 4.0. This is an initiative of the Government of India under the department of heavy industry. The aim of this scheme was to enhance competitiveness in the Indian capital good sector and awareness about industry 4.0 among Indian manufacturing industries through demonstration centers.
Our Collaboration and Courses
Keeping in mind this concept and its impact on the industries, Jain (Deemed-to-be University) in collaboration with Wiley has curated 5 courses in the new age exponential technologies. These will be made available from 2020.
About Wiley – The Global Leader in Learning Solutions
With over 200 years of experience and excellence, Wiley has been helping people and organizations develop the skills and knowledge they need to succeed.
They empower researchers, learners, universities, and corporations to achieve their goals in an ever-changing world. Wiley believes that any new technology or concept is bound to create a talent deficit in the initial run. The aim is to overcome the challenge of this deficit by helping, supporting and guiding employers to tap, identify and retain the top talents. Assess employees’ skills, strengths, and weaknesses in order to transform the company culture.
About Career Graph – Project-based learning
B.Tech – Computer Science and Engineering with below specializations:
Machine Learning - Integrated with:
Robotic Process Automation - integrated with:
Data Engineering and Informatics - integrated with:
Distributed Computing and Blockchain - integrated with:
Cybersecurity and Digital Forensics - integrated with:
In a world where everything is becoming technology driven, it is essential that students are equipped with the knowledge of these emerging technologies alongside their traditional courses. This is what makes these B.Tech courses so imperative. No matter what industry you decide to be a part of, a basic proficiency of these future-ready courses will help build a robust foundation for your careers.
To know more and get details for these courses, please visit our website here.

A subset of AI (Artificial Intelligence), Machine Learning provides learning of scientific algorithms and statistical models, which enables the computer systems to learn, improve and perform a task effectively without being explicitly programmed. ML learn from experience and are programmed to understand Natural Learning Processes to understand human interaction.
Machine Learning algorithms work on a mathematical model based on all the training data and experience it has collated to form predictions/decisions. The tasks are classified into three broad categories.
The core objective of Machine Learning is to come up with generalized prediction from its gathered experience/knowledge. It is one of the most exciting technologies of Industry 4.0 revolution. Although still in its neonatal stage, in future, Machine Learning in network and service management is expected to become a common occurrence.
A joint venture between Jain University and the experts at Wiley, this B.Tech (Computer Science & Engineering) in Machine Learning course is a part of Jain University’s gamut of new technology driven courses.
What’s in it for the students?
Course Benefits
The course is structured as a global B.Tech program where the students will have a study abroad option* in Semesters 4, 7 and 8 at the University of California Riverside (which is ranked amongst the top universities in the USA).
The program also awards additional credits for the Micromasters Certificate in Artificial Intelligence from Columbia University. Students who successfully complete these Micromasters will be eligible for exemption in 7.5 credits out of 30 credits required for a Masters in Computer Science from Columbia University.
Furthermore, in line with the vision of Jain (Deemed-to-be-University), the course integrates certifications from Harvard Business Publishing, and combines the power of technology with the spirit of entrepreneurship to get you on the right track to become a new-age “Technopreneur”.
Author - Neeti Mehta Shukla
Co-Founder, Senior Vice President – Automation Anywhere
Civil engineering is concerned with planning, designing, and supervising the construction and maintenance of building and infrastructure projects. Civil engineers are responsible for every man-made infrastructure development, including roads, dams, bridges, buildings, airports and seaports. Geotechnical engineering is a branch of civil engineering that studies the properties of soil and rock to recommend foundation design. This article will look into the various courses and opportunities in the two fields.
The various courses available in Civil Engineering are -
| Course | Name | Duration | Eligibility |
| Diploma | Civil Engineering | 3 years | Completed 10th grade |
| B.Tech/ B.E. | Civil Engineering | 4 years | Completed 12h grade with Physics, Chemistry and Maths as primary subjects and entrance exam |
| M.Tech/M.E. | Civil Engineering | 2 years | B.E./B.Tech and GATE |
| PhD. | 3-6 years | MTech |
Since it is a branch of civil engineering, Geotechnical engineering is offered as a specialisation in M. Tech. Learners can study it further as a super-specialisation by pursuing a Ph.D. To qualify for the M. Tech programme, a candidate must complete B. Tech/ B.E. from a recognised institute in any relevant field with a 50% aggregate score. They have to take an entrance exam.
The syllabus for Civil Engineering will cover subjects such as -
| Course | Syllabus |
| B.E./ B.Tech | Chemistry, Mechanics, Electronics, Engineering Drawing and Graphics, Programming and Data Structure, Hydraulics, Water and Waste Water Engineering, Solid Mechanics, Foundation Engineering, Design of RC structures, Design of Steel Structures, Construction Management, Environmental Engineering, Reinforced Concrete Design, Reinforced Cement Concrete |
| M.E./ M.Tech (Specialisations) | Construction Engineering, Coastal and Ocean Engineering, Geotechnical Engineering, Fire Protection Engineering, Structural Engineering, General Engineering, Bridge Engineering, Irrigation Engineering, Land Development, Materials Engineering, Transportation Engineering, Urban Engineering, Hydraulic Engineering, Water Resources Engineering, Environmental Engineering |
The Civil Engineering course has classroom lectures, laboratory experiments, field visits, and workshop time. Learners have to take written exams, viva voce, and do projects, and internships in the programme.
The syllabus for the Geotechnical Engineering programme includes topics such as -
| Main Course | Electives |
| Engineering Behaviour of Soils, Earthquake Engineering and Soil Dynamics, Design of Foundations, Embankments and Earth Structures, Geotechnical Foundation Design, Rock Mechanics and Tunnelling, Soil and Site Improvement, Introduction to Geographic Information Systems, Construction Equipment Management, Advanced Soil Mechanics, Theory of Plasticity, Physio-Chemical Behaviour of Soils, Ground Water Hydrology and Sampling |
|
The course will involve classroom lectures, laboratory work, and fieldwork. Students will take semester exams and submit projects and one internship for the duration of the course. They also have to write a mandatory dissertation.
Depending on the specialisation they choose, on course completion a civil engineer will work on real estate development projects, and large construction companies for roads, bridges, dams, or tunnels. They can find roles with the public works department or with the sanitation department in government or non-government organisations. Civil engineers also collaborate with architecture and interior design firms, waste management businesses, designing transportation systems, irrigation methods, and space research and exploration projects. They will be hired in roles such as -
Geotechnical engineers study geology, geomechanics (rock mechanics and soil mechanics), the design of foundations, the stabilisation of slopes, the improvement of ground conditions, the excavation of tunnels and underground openings, the analysis of ground behaviour, and the assessment of ground movements. The roles they generally work in are -
There are ample opportunities for Civil and Geotechnical engineering graduates to work with top organisations in the public and private sectors which will involve exciting fieldwork, research, and application of their learning in infrastructure projects. Civil engineers can build a super-specialist role with their Geotechnical engineering Master’s to become expert consultants and work across industries on various projects.